Rising Insider Threats Linked to AI Misuse Pose Significant Risk to Businesses, Reports Mimecast
Published on: 2026-03-05
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: AI-Driven Insider Risk Now a Critical Business Threat Report Warns
1. BLUF (Bottom Line Up Front)
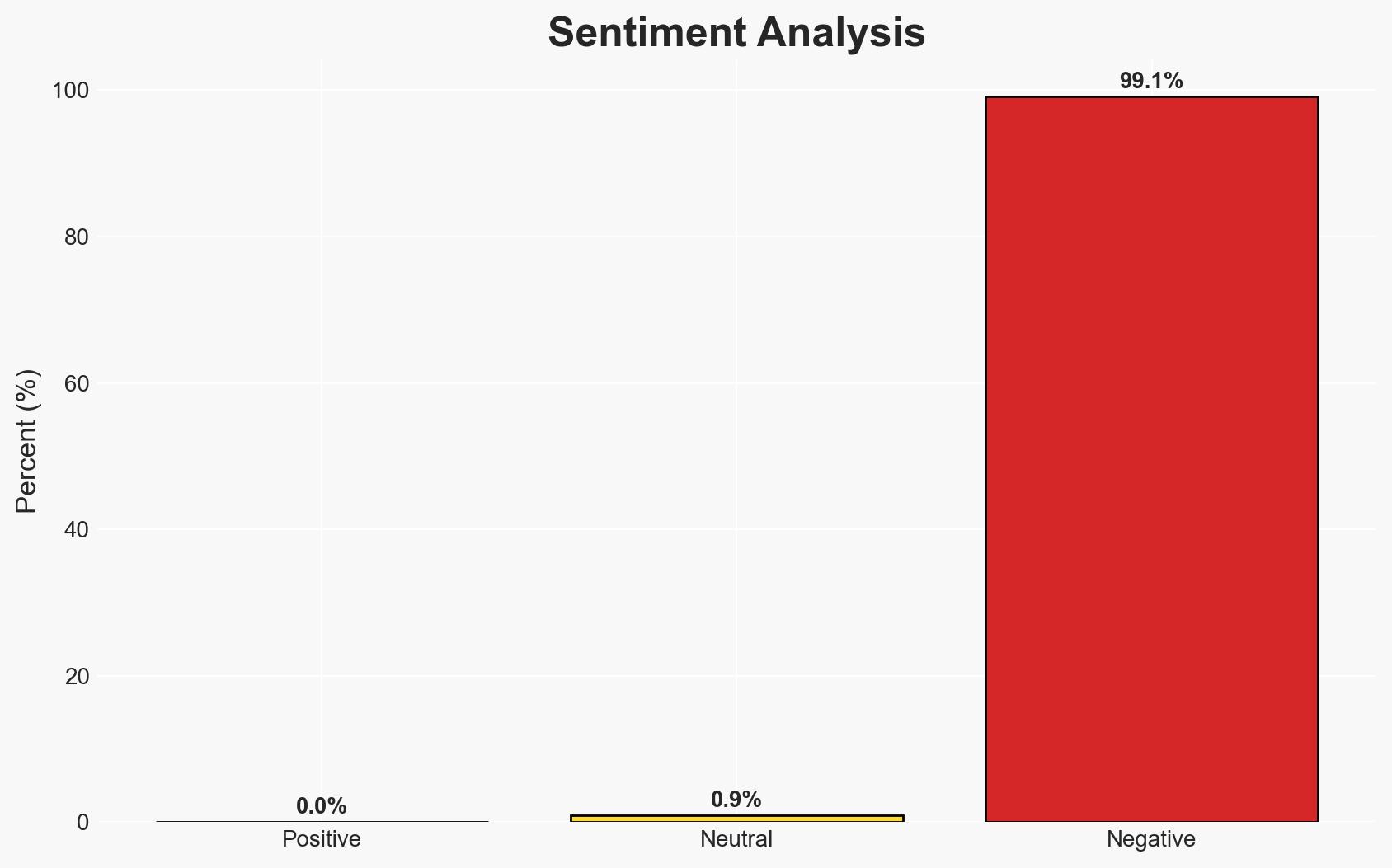
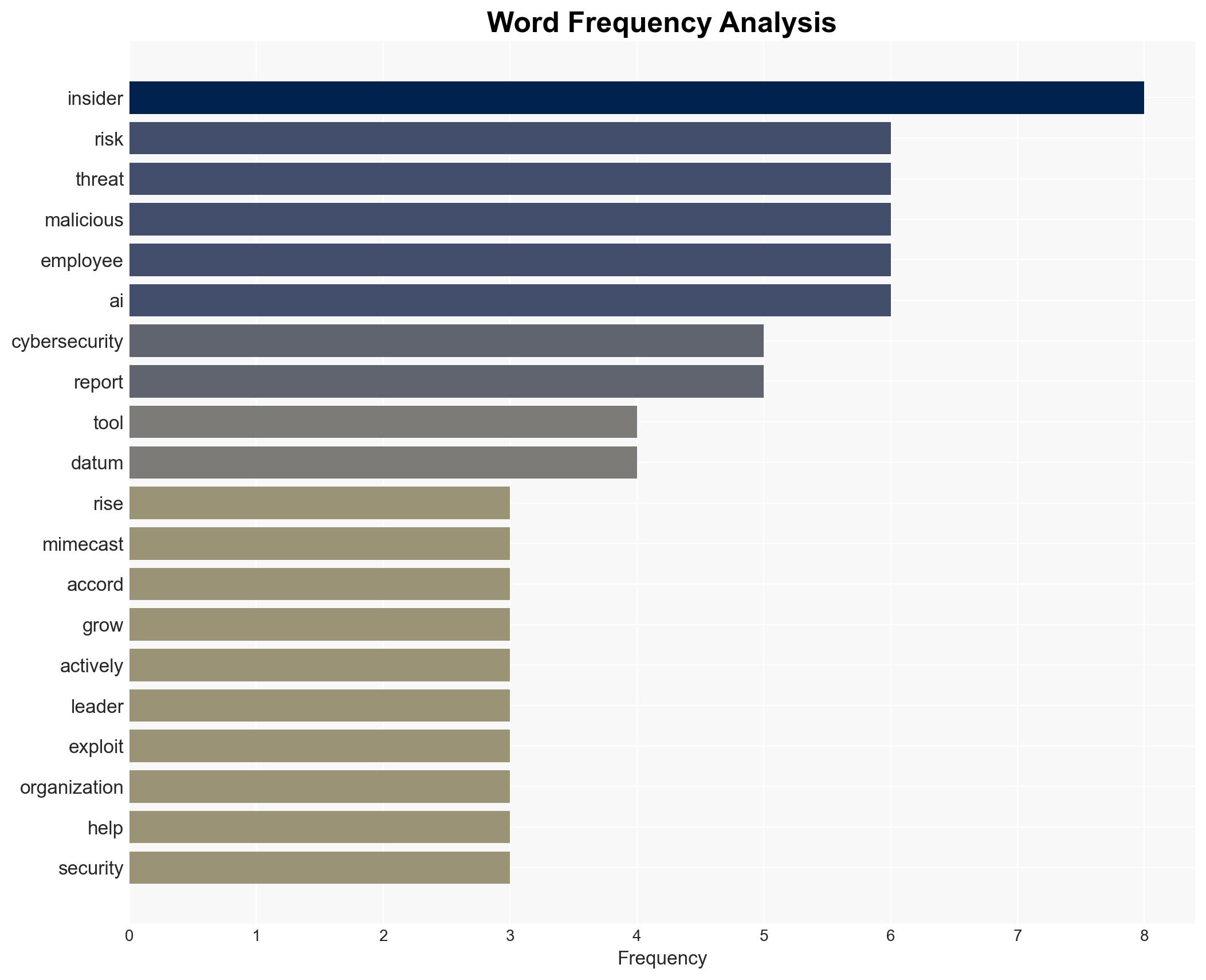
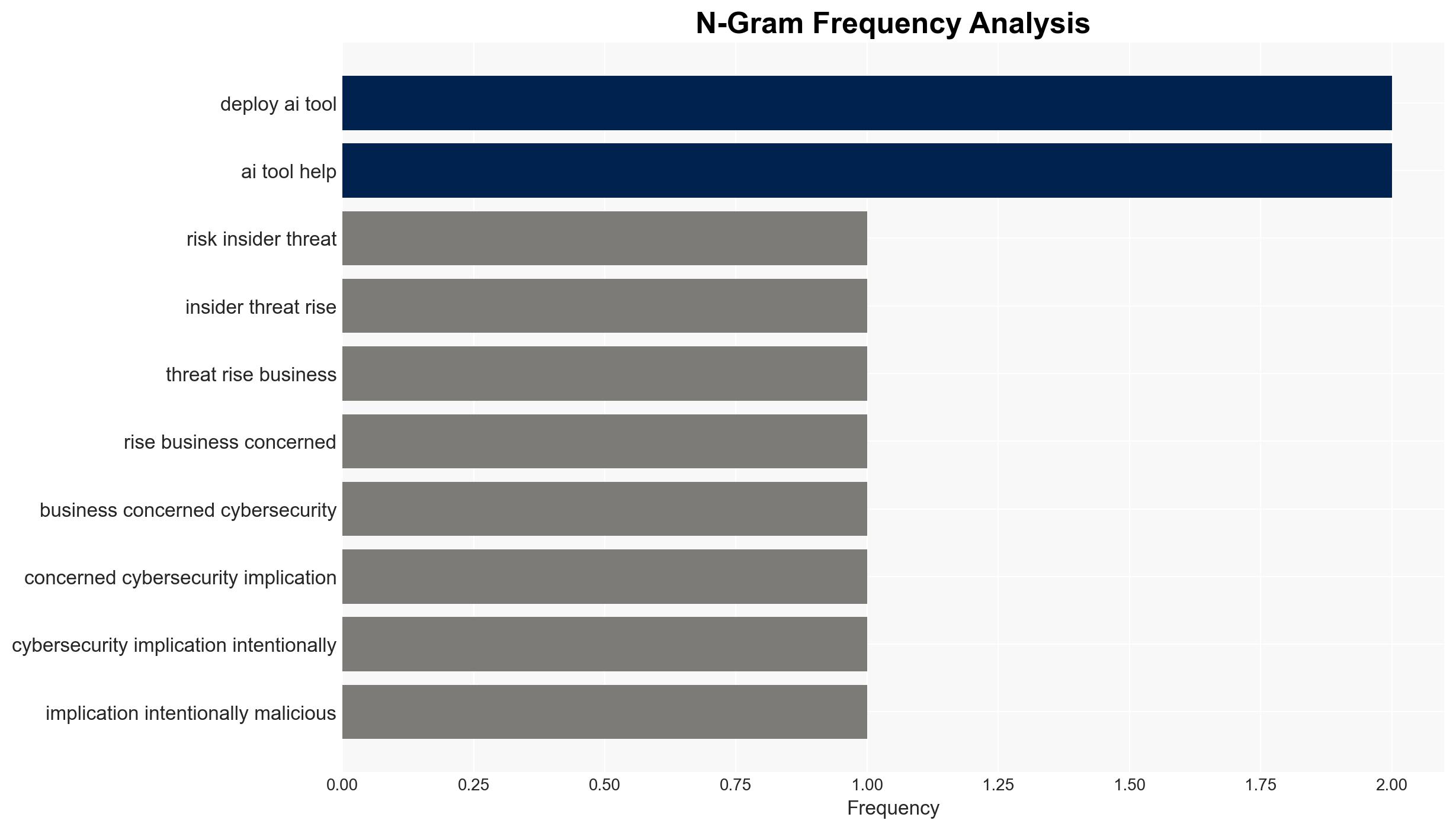
The rise of AI tools in the workplace has significantly increased insider threats, both malicious and negligent, posing a critical business threat. Organizations are experiencing a notable increase in cybersecurity incidents linked to insider actions, with AI tools exacerbating these risks. This trend affects global businesses across various sectors, with moderate confidence in the assessment due to the reliance on a single report and potential biases.
2. Competing Hypotheses
- Hypothesis A: The increase in insider threats is primarily due to the misuse of AI tools by employees, both intentionally and negligently. Supporting evidence includes the reported rise in incidents and the specific mention of AI tools expanding the attack surface. Key uncertainties involve the extent to which AI tools are directly responsible versus other factors.
- Hypothesis B: The rise in insider threats is largely due to broader cybersecurity challenges, with AI tools being a secondary factor. This hypothesis is supported by the general increase in cybersecurity threats and the potential for other systemic issues, such as inadequate security training or policies. Contradicting evidence includes the specific focus on AI in the report.
- Assessment: Hypothesis A is currently better supported due to the explicit linkage between AI tool misuse and insider threats in the report. Future indicators that could shift this judgment include data showing a broader range of contributing factors beyond AI.
3. Key Assumptions and Red Flags
- Assumptions: Organizations have adequate reporting mechanisms for insider threats; AI tools are being widely adopted across sectors; insider threats are being accurately attributed to AI misuse.
- Information Gaps: Detailed breakdown of incidents directly linked to AI misuse versus other causes; comparative data from other cybersecurity reports; insights into the effectiveness of current mitigation strategies.
- Bias & Deception Risks: Potential bias from Mimecast as a cybersecurity vendor; reliance on survey data which may not capture all nuances; risk of overemphasizing AI due to current technological trends.
4. Implications and Strategic Risks
The development of AI-driven insider threats could lead to increased regulatory scrutiny and demand for enhanced cybersecurity measures. The evolving threat landscape may require organizations to adapt quickly to mitigate risks.
- Political / Geopolitical: Potential for increased international collaboration on cybersecurity standards and AI regulation.
- Security / Counter-Terrorism: Heightened risk of data breaches and espionage activities exploiting insider vulnerabilities.
- Cyber / Information Space: Expansion of attack surfaces and complexity in threat detection and response mechanisms.
- Economic / Social: Possible economic impacts due to data loss or breaches; increased pressure on IT budgets and resources.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of AI tool usage within organizations; conduct risk assessments focusing on insider threats; increase employee training on cybersecurity best practices.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms for advanced threat intelligence; invest in AI-driven security solutions; review and update insider threat policies.
- Scenario Outlook: Best: Improved AI governance reduces insider threats; Worst: Insider threats lead to significant breaches and financial losses; Most-Likely: Continued rise in threats with gradual adaptation of security measures.
6. Key Individuals and Entities
- Mimecast, Leslie Nielsen (Mimecast CISO), Vanson Bourne
7. Thematic Tags
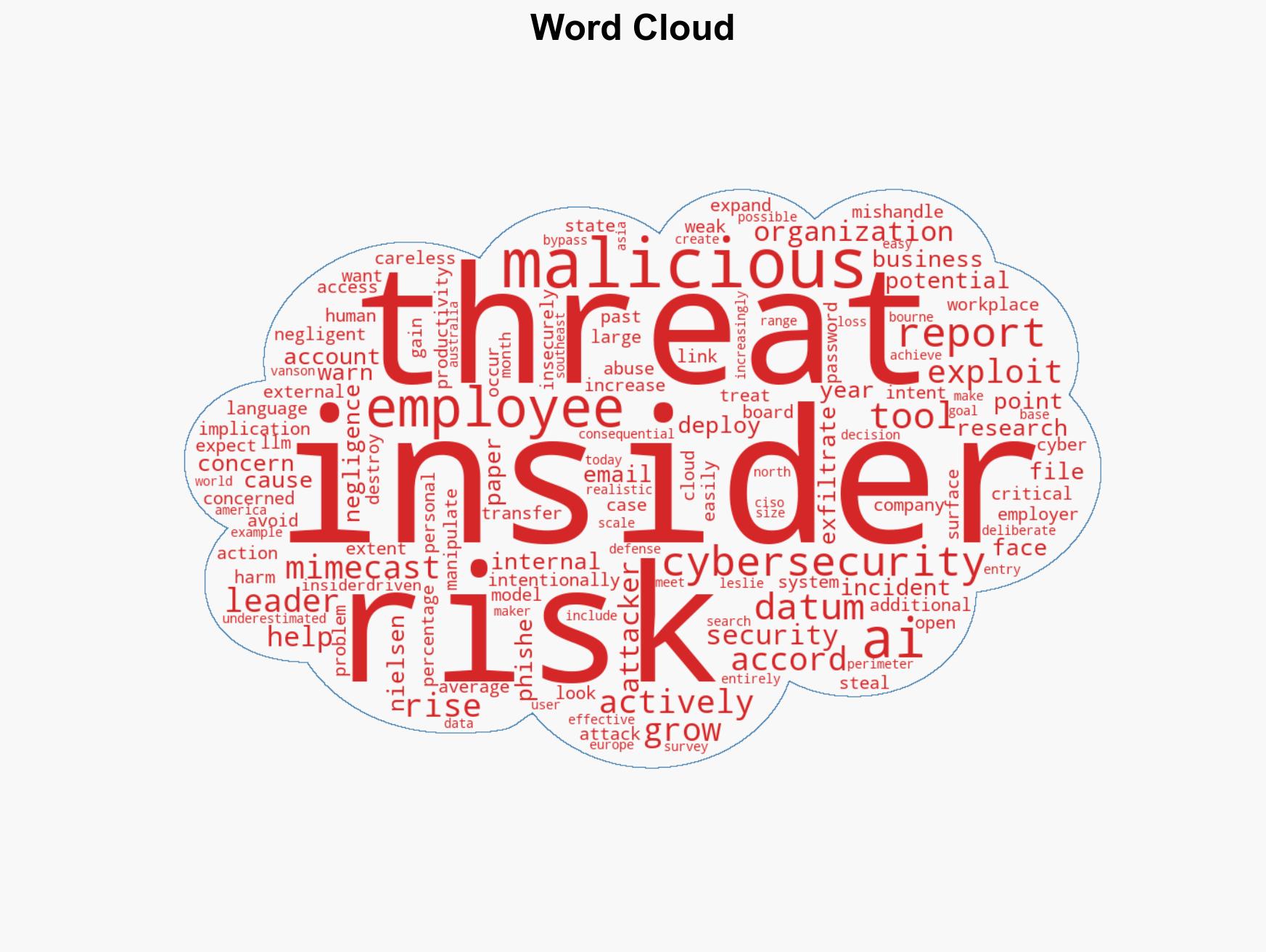
cybersecurity, insider threats, AI misuse, data breaches, organizational risk, threat mitigation, IT security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us