Russia-linked Gamaredon targets Ukraine with Remcos RAT – Securityaffairs.com
Published on: 2025-03-31
Intelligence Report: Russia-linked Gamaredon targets Ukraine with Remcos RAT – Securityaffairs.com
1. BLUF (Bottom Line Up Front)
The Russia-linked group, Gamaredon, has been actively targeting Ukraine through a sophisticated cyber espionage campaign utilizing the Remcos RAT. This campaign involves spear-phishing attacks designed to infiltrate Ukrainian entities by disguising malicious files as legitimate documents. The strategic objective appears to be the extraction of sensitive information, potentially impacting national security and regional stability. Immediate countermeasures are recommended to mitigate these threats.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
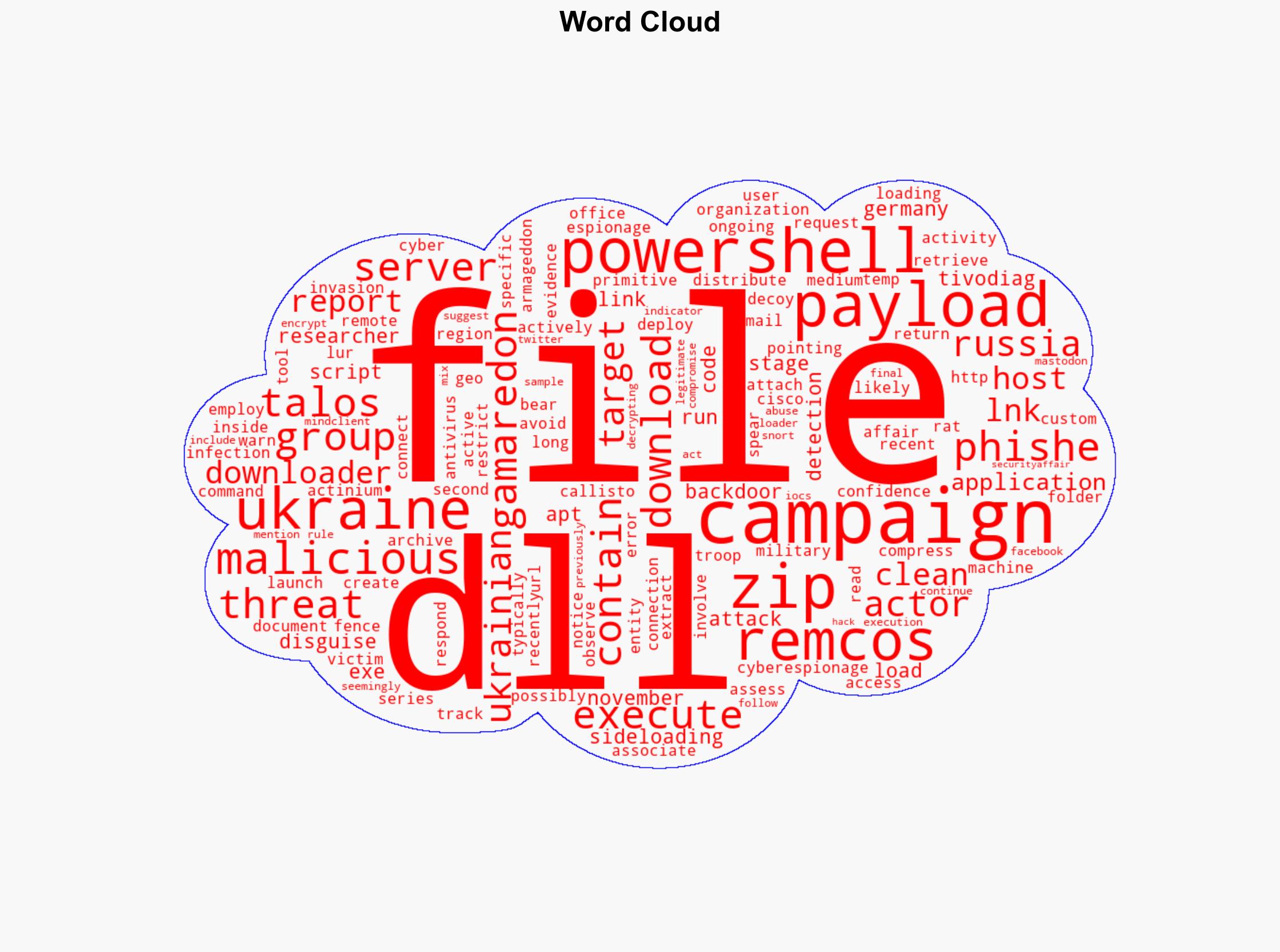
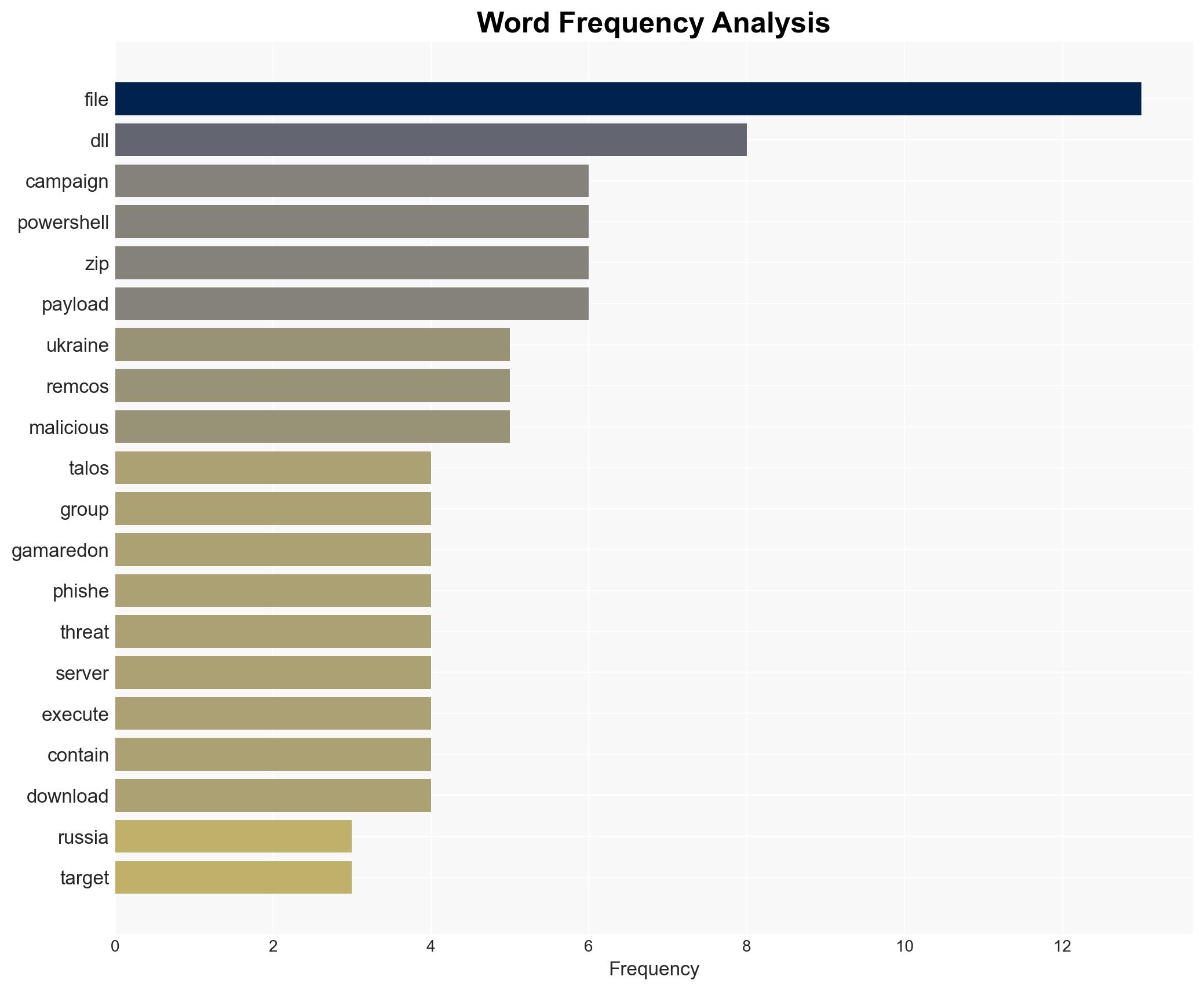
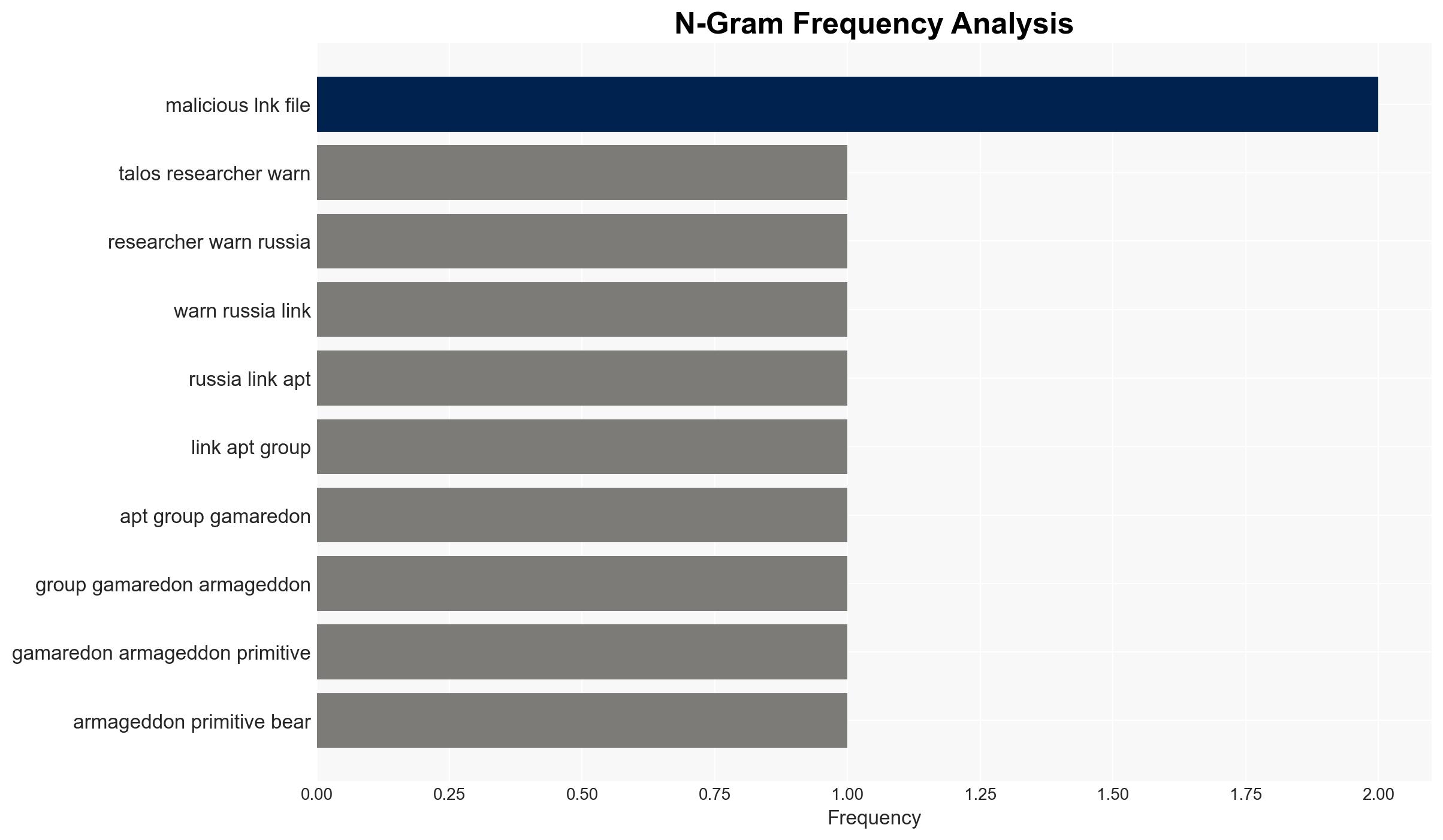
Gamaredon, also known by aliases such as Armageddon and Primitive Bear, has launched a series of cyber espionage campaigns against Ukraine. The group employs spear-phishing tactics, distributing malicious LNK files compressed within ZIP archives. These files are often disguised as office documents with names referencing military invasions, aiming to deceive the recipients into executing them.
The campaign’s technical execution involves a PowerShell downloader that connects to geo-fenced servers in Russia and Germany to retrieve the Remcos backdoor. The attack chain includes DLL sideloading techniques to evade antivirus detection, leveraging legitimate applications to execute the malicious payload.
3. Implications and Strategic Risks
The ongoing cyber operations by Gamaredon pose significant risks to Ukraine’s national security and regional stability. The potential compromise of sensitive information could lead to strategic disadvantages. Additionally, the use of geo-fenced servers suggests a targeted approach, potentially limiting the scope of detection and response efforts. The economic impact could be substantial if critical infrastructure or governmental operations are disrupted.
4. Recommendations and Outlook
Recommendations:
- Enhance cybersecurity measures across Ukrainian entities, focusing on email security and endpoint protection.
- Implement regular training programs for employees to recognize and respond to phishing attempts.
- Strengthen international cooperation for intelligence sharing and coordinated response efforts.
Outlook:
In the best-case scenario, increased vigilance and improved cybersecurity measures will mitigate the impact of Gamaredon’s activities. In the worst-case scenario, continued successful infiltration could lead to significant data breaches and operational disruptions. The most likely outcome involves ongoing attempts by Gamaredon, necessitating sustained defensive efforts.
5. Key Individuals and Entities
The report mentions the following significant entities: Gamaredon, Armageddon, Primitive Bear, Actinium, Callisto. These entities are involved in the cyber espionage activities targeting Ukraine.