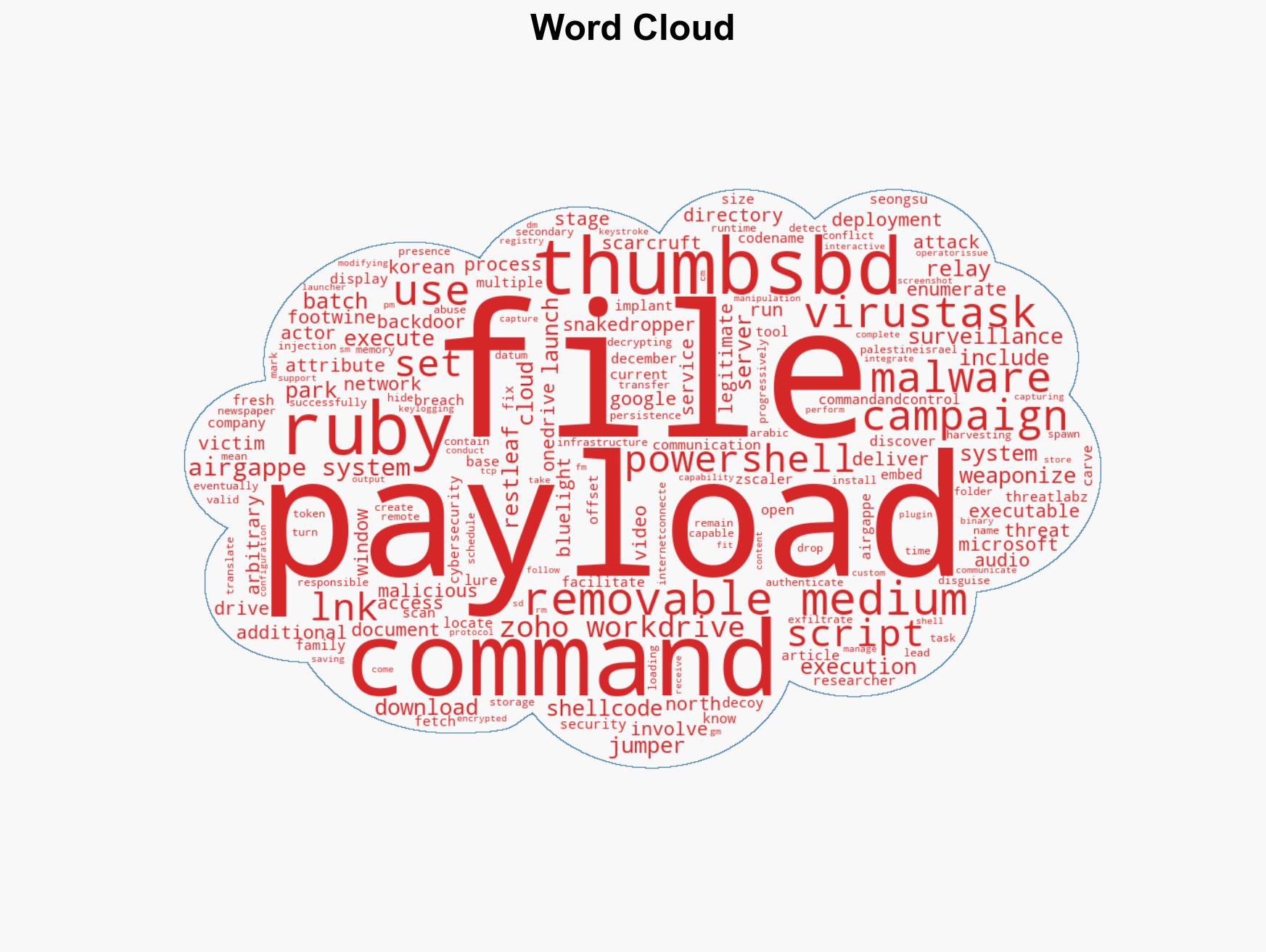
ScarCruft Exploits Zoho WorkDrive and USB Malware for Infiltration of Air-Gapped Systems
Published on: 2026-02-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: ScarCruft Uses Zoho WorkDrive and USB Malware to Breach Air-Gapped Networks
1. BLUF (Bottom Line Up Front)
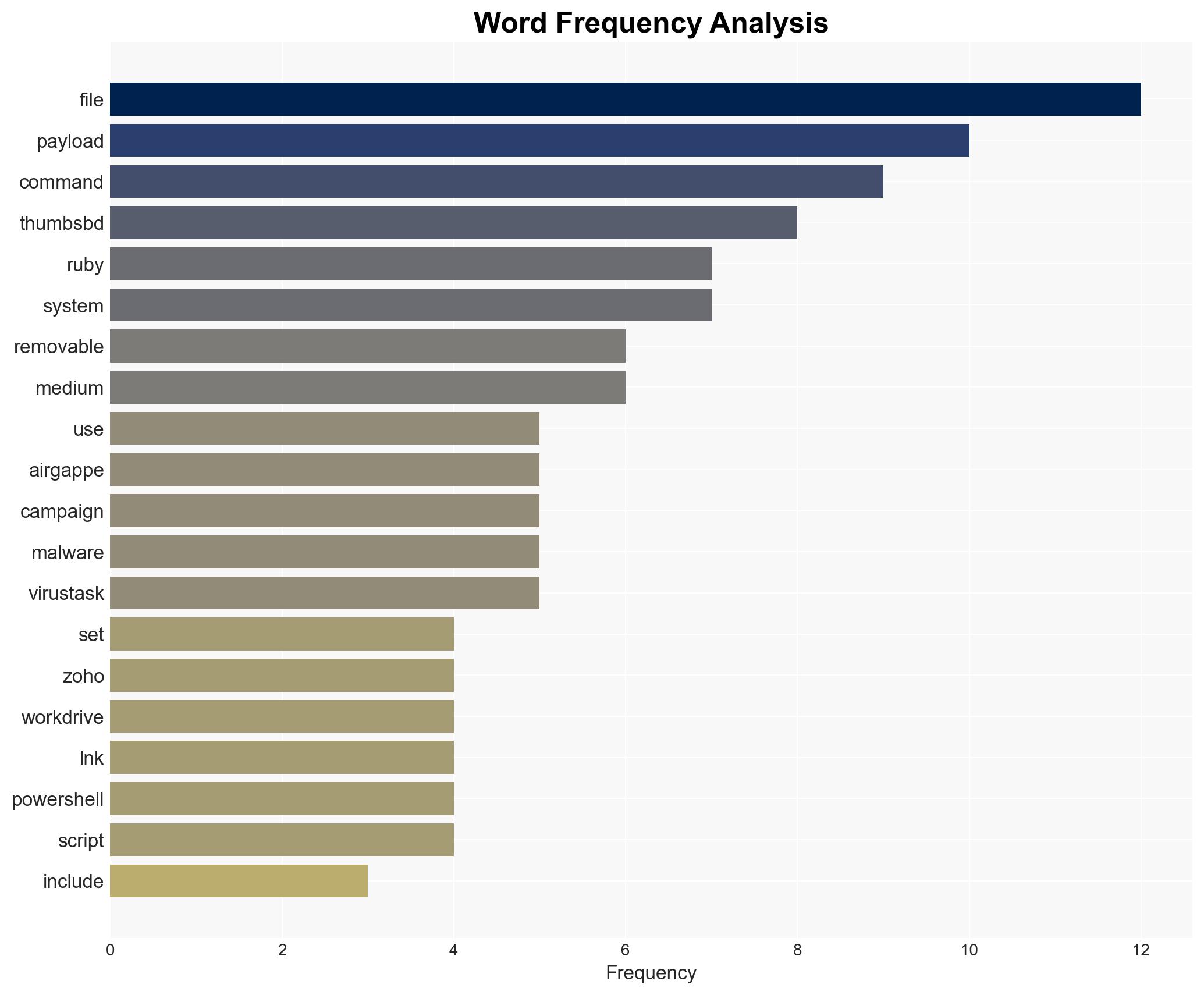
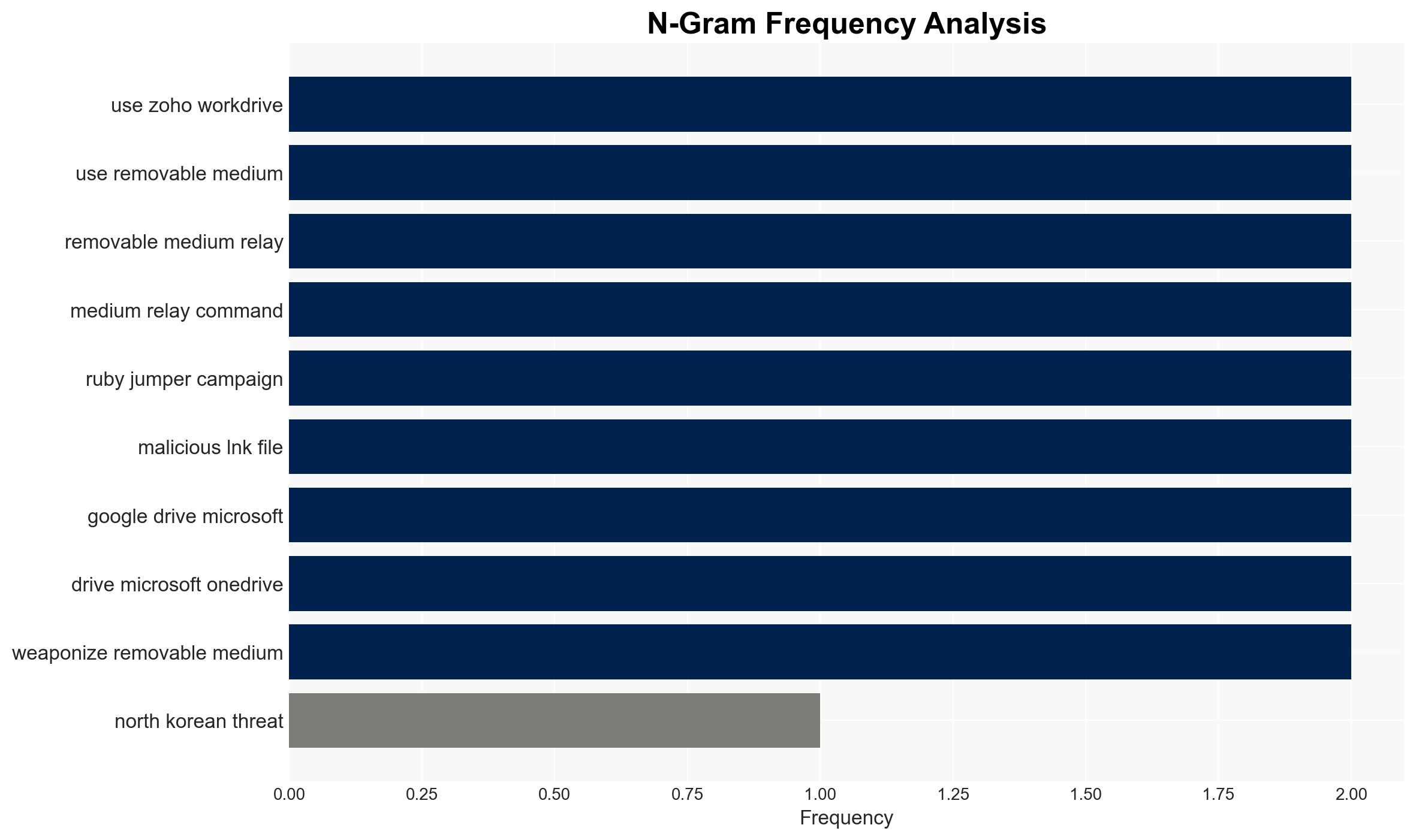
The North Korean threat actor ScarCruft has developed a sophisticated campaign, codenamed Ruby Jumper, utilizing Zoho WorkDrive and USB malware to breach air-gapped networks. This campaign poses a significant threat to targeted entities, leveraging advanced malware families for surveillance and data exfiltration. The assessment is made with moderate confidence due to the complexity of the operation and the involvement of multiple malware components.
2. Competing Hypotheses
- Hypothesis A: ScarCruft is primarily targeting government and military networks to gather intelligence. This is supported by the use of air-gap breaching techniques and sophisticated malware, which are typically employed in high-value intelligence operations. However, the specific targets remain unidentified, creating uncertainty.
- Hypothesis B: ScarCruft’s campaign is aimed at commercial entities to disrupt operations or steal intellectual property. The use of cloud services like Zoho WorkDrive could facilitate broader access beyond government networks. Contradicting this is the focus on air-gapped systems, which are more common in sensitive government environments.
- Assessment: Hypothesis A is currently better supported due to the technical sophistication and targeting methods indicative of state-sponsored espionage. Indicators such as the use of air-gap breaching and complex malware families suggest a focus on high-value intelligence targets.
3. Key Assumptions and Red Flags
- Assumptions: ScarCruft has the capability to maintain and evolve its toolset; the campaign is state-sponsored; the primary targets are high-value intelligence networks.
- Information Gaps: Specific targets and the full scope of the campaign remain unclear; the extent of data exfiltrated is unknown.
- Bias & Deception Risks: Potential bias in attributing the campaign solely to North Korea without considering other actors; reliance on a single cybersecurity source may limit perspective.
4. Implications and Strategic Risks
This development could lead to increased tensions and a potential cyber arms race, as nations seek to protect sensitive networks. The sophistication of the campaign highlights vulnerabilities in air-gapped systems and cloud services.
- Political / Geopolitical: Potential escalation in cyber conflict between North Korea and targeted nations, impacting diplomatic relations.
- Security / Counter-Terrorism: Increased threat to national security infrastructure, necessitating enhanced cyber defense measures.
- Cyber / Information Space: Highlights the need for improved security protocols for cloud services and air-gapped networks.
- Economic / Social: Potential economic impact if commercial entities are targeted, leading to loss of intellectual property or operational disruptions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of Zoho WorkDrive and similar services for unusual activity; conduct security audits on air-gapped networks.
- Medium-Term Posture (1–12 months): Develop partnerships for intelligence sharing; invest in advanced threat detection and response capabilities.
- Scenario Outlook: Best: Improved defenses deter further attacks; Worst: Successful breaches lead to significant data loss; Most-Likely: Ongoing attempts with limited success due to increased vigilance.
6. Key Individuals and Entities
- ScarCruft (North Korean threat actor)
- Zoho WorkDrive (Cloud service provider)
- Zscaler ThreatLabz (Cybersecurity company)
- Seongsu Park (Security researcher)
7. Thematic Tags
cybersecurity, cyber-espionage, North Korea, air-gapped networks, cloud security, malware, state-sponsored threats, intelligence gathering
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us