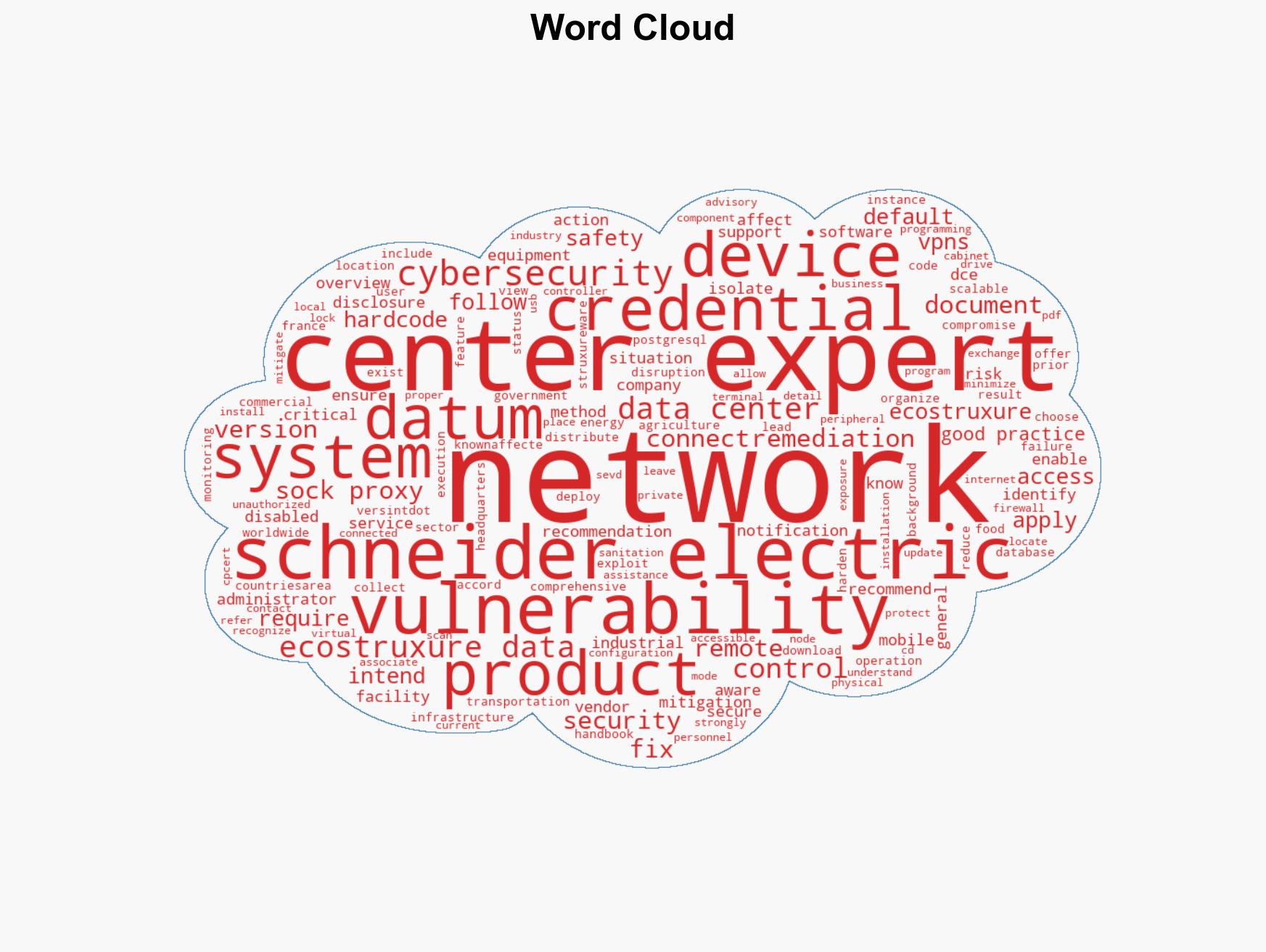
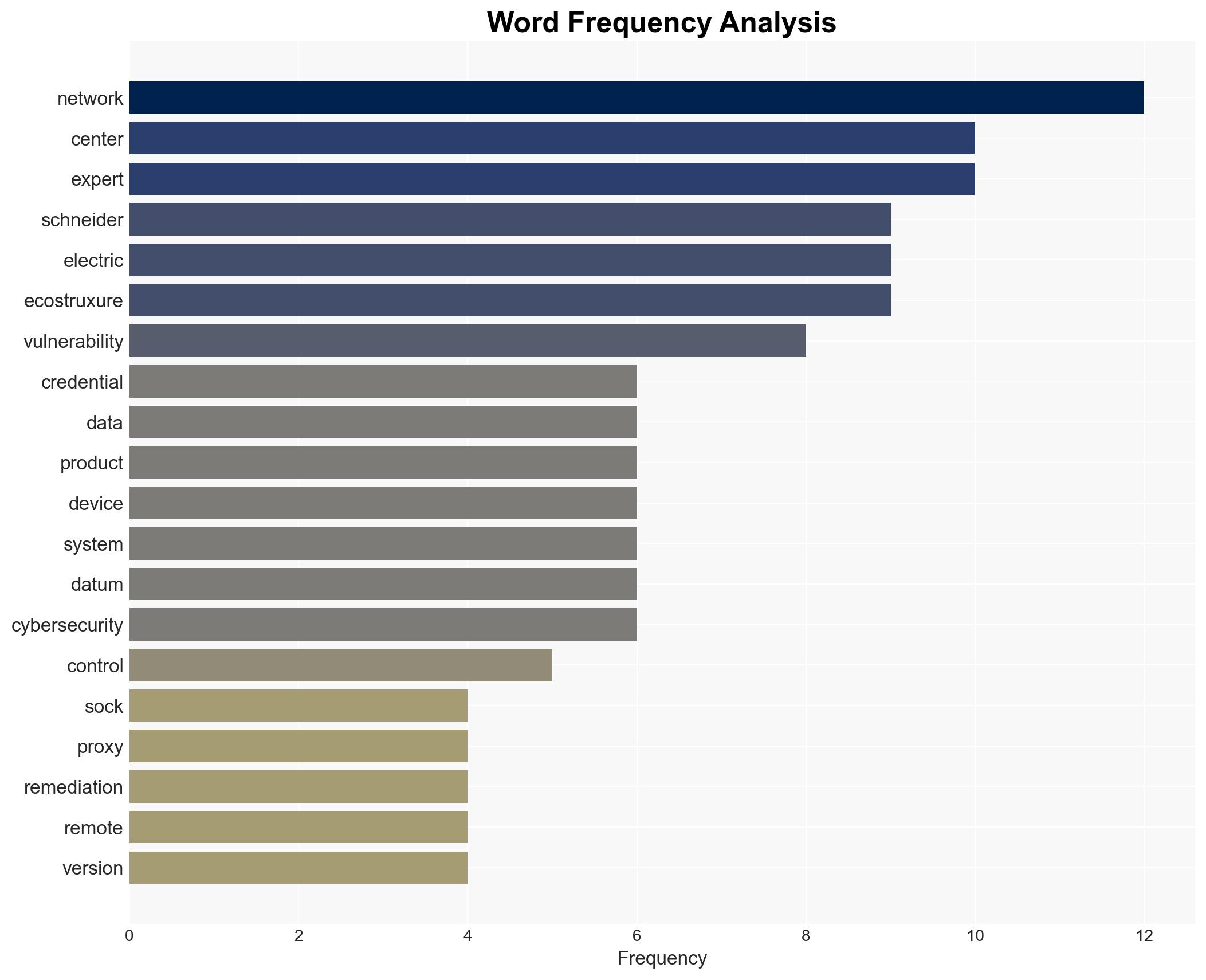
Schneider Electric Warns of Hard-Coded Credentials Vulnerability in EcoStruxure Data Center Expert Software
Published on: 2026-03-17
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Schneider Electric EcoStruxure Data Center Expert
1. BLUF (Bottom Line Up Front)
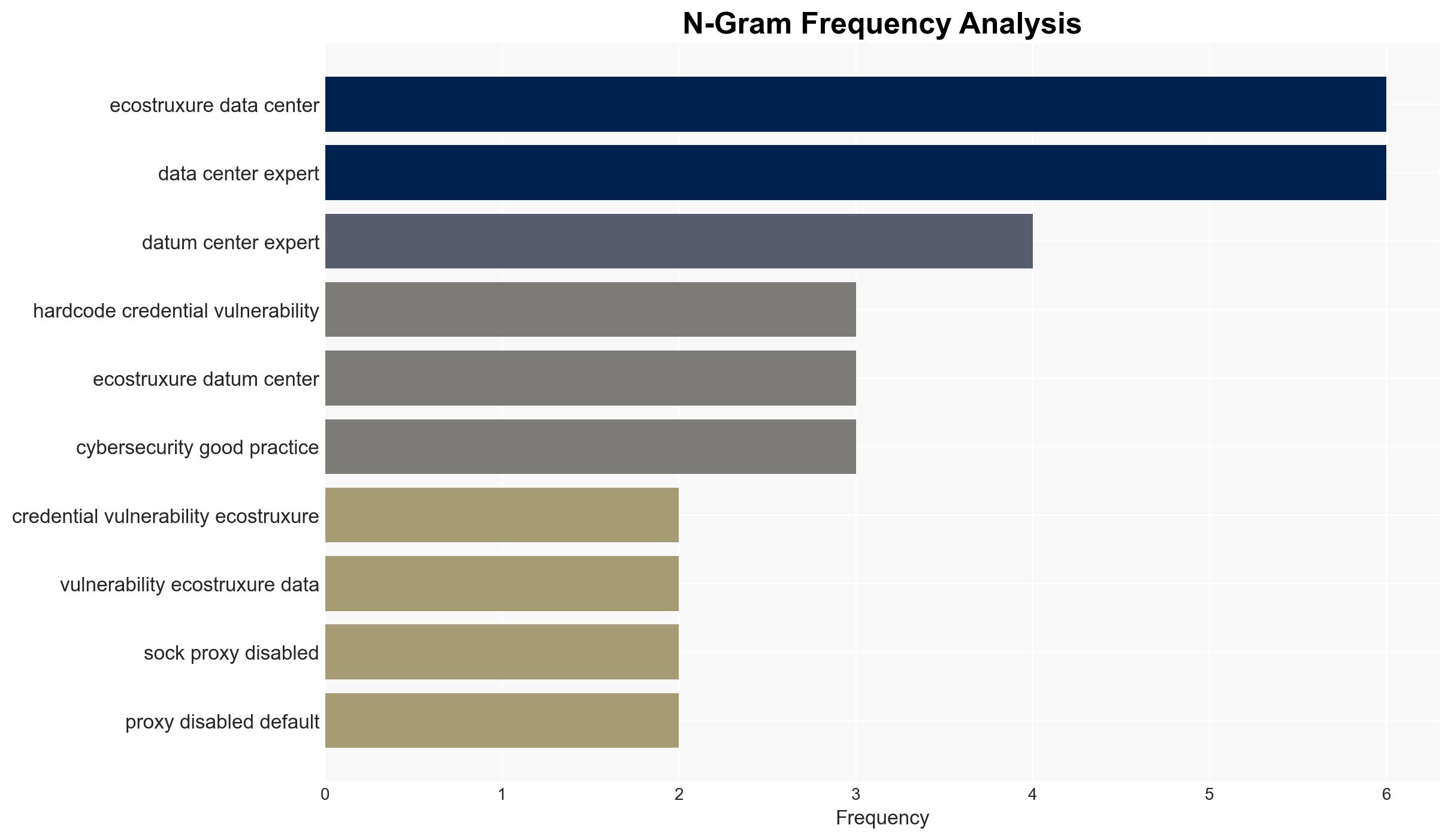
The Schneider Electric EcoStruxure Data Center Expert product has a vulnerability involving hard-coded credentials that could lead to information disclosure and remote compromise if not remediated. This issue affects critical infrastructure sectors globally. The most likely hypothesis is that the vulnerability, if exploited, could result in significant operational disruptions. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
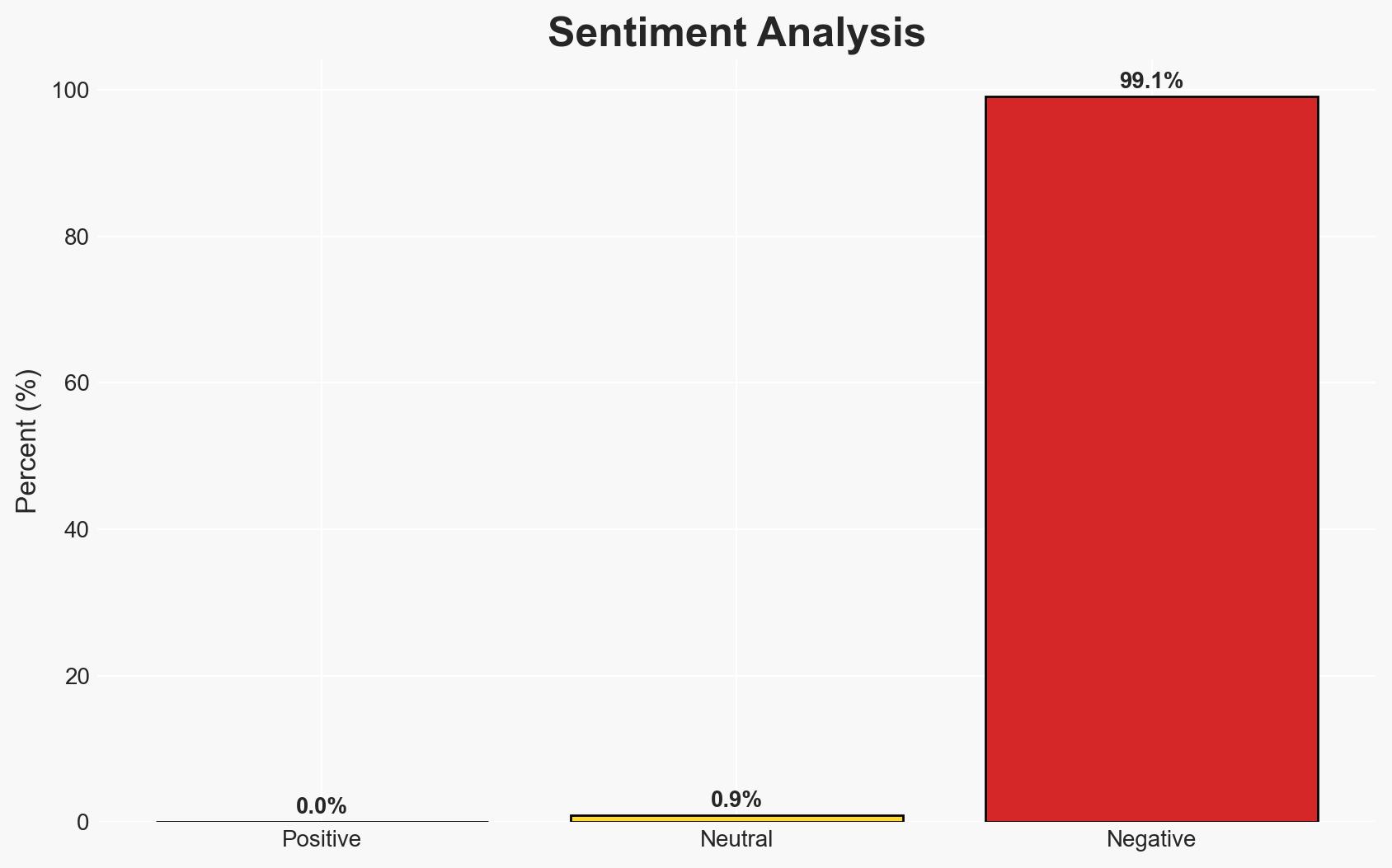
- Hypothesis A: The vulnerability will be exploited by malicious actors leading to significant disruptions in affected sectors. Supporting evidence includes the potential for remote code execution and information disclosure. However, the requirement for specific conditions (enabled SOCKS Proxy and known credentials) introduces uncertainty.
- Hypothesis B: The vulnerability will not be widely exploited due to the default disabled state of the SOCKS Proxy and the availability of a vendor fix. This is supported by the fact that remediation measures are in place and awareness has been raised through advisories.
- Assessment: Hypothesis B is currently better supported due to the proactive measures taken by Schneider Electric and the default security settings. Key indicators that could shift this judgment include reports of active exploitation or failure of organizations to apply the necessary patches.
3. Key Assumptions and Red Flags
- Assumptions: Organizations will apply the available patch; SOCKS Proxy remains disabled by default; attackers require specific knowledge to exploit the vulnerability.
- Information Gaps: Lack of data on the number of systems that have not applied the patch; unclear extent of awareness among all affected sectors.
- Bias & Deception Risks: Potential underestimation of the vulnerability’s impact due to reliance on vendor-provided information; risk of complacency in affected sectors.
4. Implications and Strategic Risks
This vulnerability could lead to operational disruptions if exploited, affecting critical infrastructure sectors globally. The situation could evolve based on the patch application rate and potential exploitation attempts.
- Political / Geopolitical: Potential for increased scrutiny on cybersecurity practices in critical infrastructure sectors.
- Security / Counter-Terrorism: Possible targeting by state or non-state actors aiming to disrupt critical services.
- Cyber / Information Space: Increased focus on securing industrial control systems and awareness of software vulnerabilities.
- Economic / Social: Disruptions could lead to economic impacts, particularly in sectors like energy and transportation.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Ensure all affected systems apply the vendor fix; monitor for signs of exploitation; reinforce cybersecurity awareness among stakeholders.
- Medium-Term Posture (1–12 months): Develop partnerships for information sharing on vulnerabilities; enhance incident response capabilities.
- Scenario Outlook:
- Best Case: Widespread patch application prevents exploitation.
- Worst Case: Significant exploitation leads to major disruptions.
- Most Likely: Limited exploitation due to effective mitigation measures.
6. Key Individuals and Entities
- Schneider Electric (Vendor)
- Critical Infrastructure Operators (Affected Entities)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, critical infrastructure, vulnerability management, industrial control systems, information disclosure, remote code execution, operational disruption
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us