Secret Service Agents Fatally Shoot Armed Intruder at Mar-a-Lago During Security Breach Attempt
Published on: 2026-02-22
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: US Secret Service Killed Armed Man Attempting To Breach Mar-a-Lago
1. BLUF (Bottom Line Up Front)
The U.S. Secret Service neutralized an armed individual attempting to breach Mar-a-Lago, raising concerns about security protocols at high-profile residences. The incident appears to be an isolated act by an individual with unclear motives. Moderate confidence in the assessment due to limited information on the suspect’s intentions and background.
2. Competing Hypotheses
- Hypothesis A: The incident was an isolated act by an individual with mental health issues or personal grievances. Supporting evidence includes the suspect’s lone actions and lack of coordination. However, the absence of a clear motive introduces uncertainty.
- Hypothesis B: The incident was a targeted attack with potential political motivations. This is less supported due to the lack of evidence indicating political affiliations or statements by the suspect. The presence of a gas can and shotgun could suggest intent for harm, but without further context, this remains speculative.
- Assessment: Hypothesis A is currently better supported given the lack of evidence for coordinated or politically motivated actions. Key indicators that could shift this judgment include discovery of communications or affiliations suggesting broader intent.
3. Key Assumptions and Red Flags
- Assumptions: The suspect acted alone; there is no immediate threat to other high-profile locations; the incident is not part of a larger coordinated effort.
- Information Gaps: The suspect’s motive and background, potential connections to extremist groups, and any prior indications of intent.
- Bias & Deception Risks: Potential bias in initial reports focusing on security response effectiveness; risk of underestimating the threat if broader connections are later uncovered.
4. Implications and Strategic Risks
This incident may prompt a reevaluation of security measures at high-profile residences and could influence public perception of safety and security protocols.
- Political / Geopolitical: Potential for increased scrutiny on security measures for political figures, influencing public and political discourse.
- Security / Counter-Terrorism: May lead to heightened security alerts and reviews of protective measures at similar venues.
- Cyber / Information Space: Potential for misinformation or disinformation campaigns exploiting the incident to sow distrust in security capabilities.
- Economic / Social: Limited immediate economic impact, but potential for increased security costs and public anxiety.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a thorough investigation into the suspect’s background and motives; enhance security protocols at similar high-profile locations.
- Medium-Term Posture (1–12 months): Develop resilience measures and training for security personnel; establish partnerships with local law enforcement for rapid response.
- Scenario Outlook:
- Best: Incident remains isolated, leading to improved security measures.
- Worst: Discovery of broader network or intent, necessitating widespread security overhauls.
- Most-Likely: Isolated incident with increased security awareness and minor procedural adjustments.
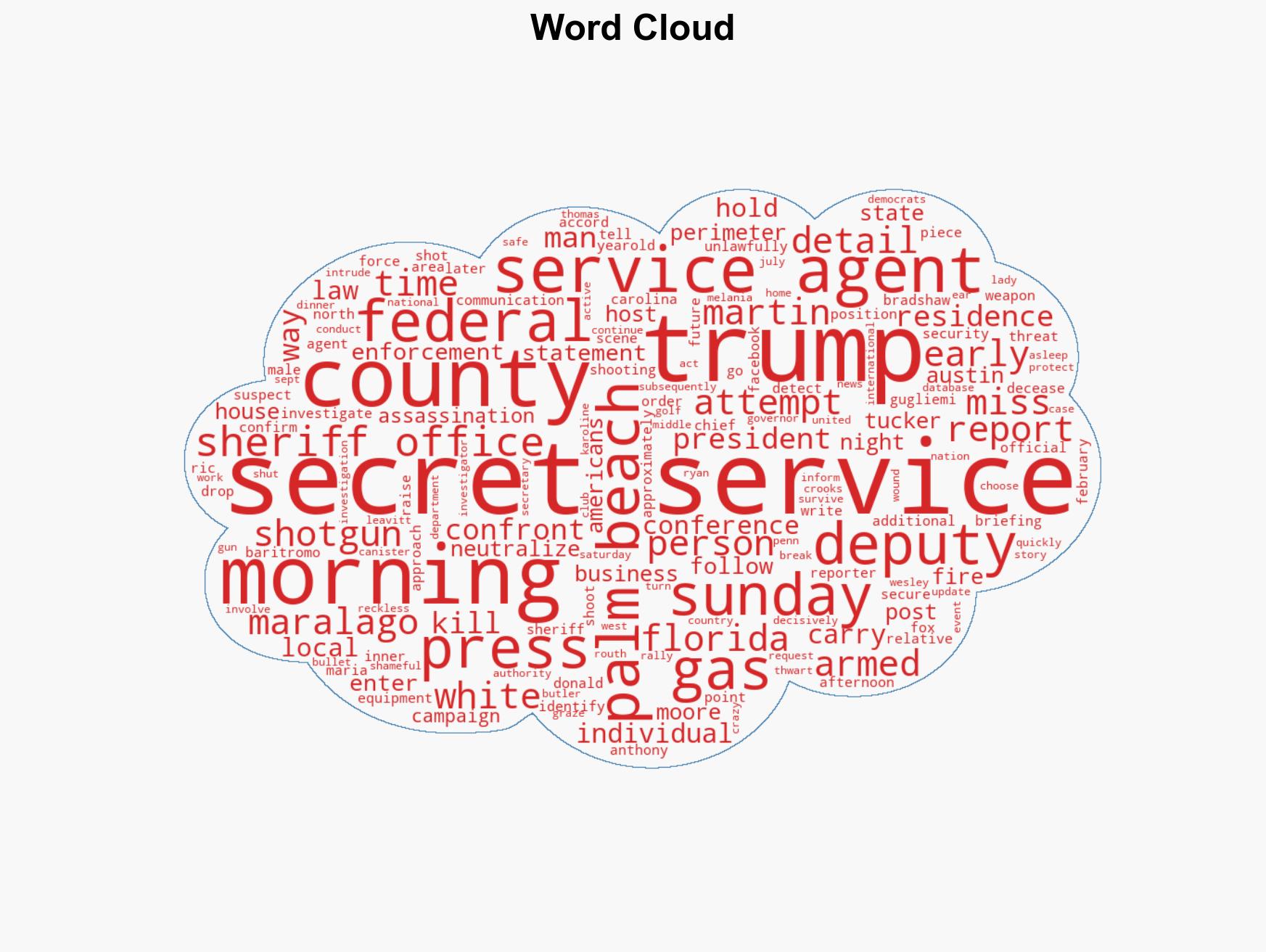
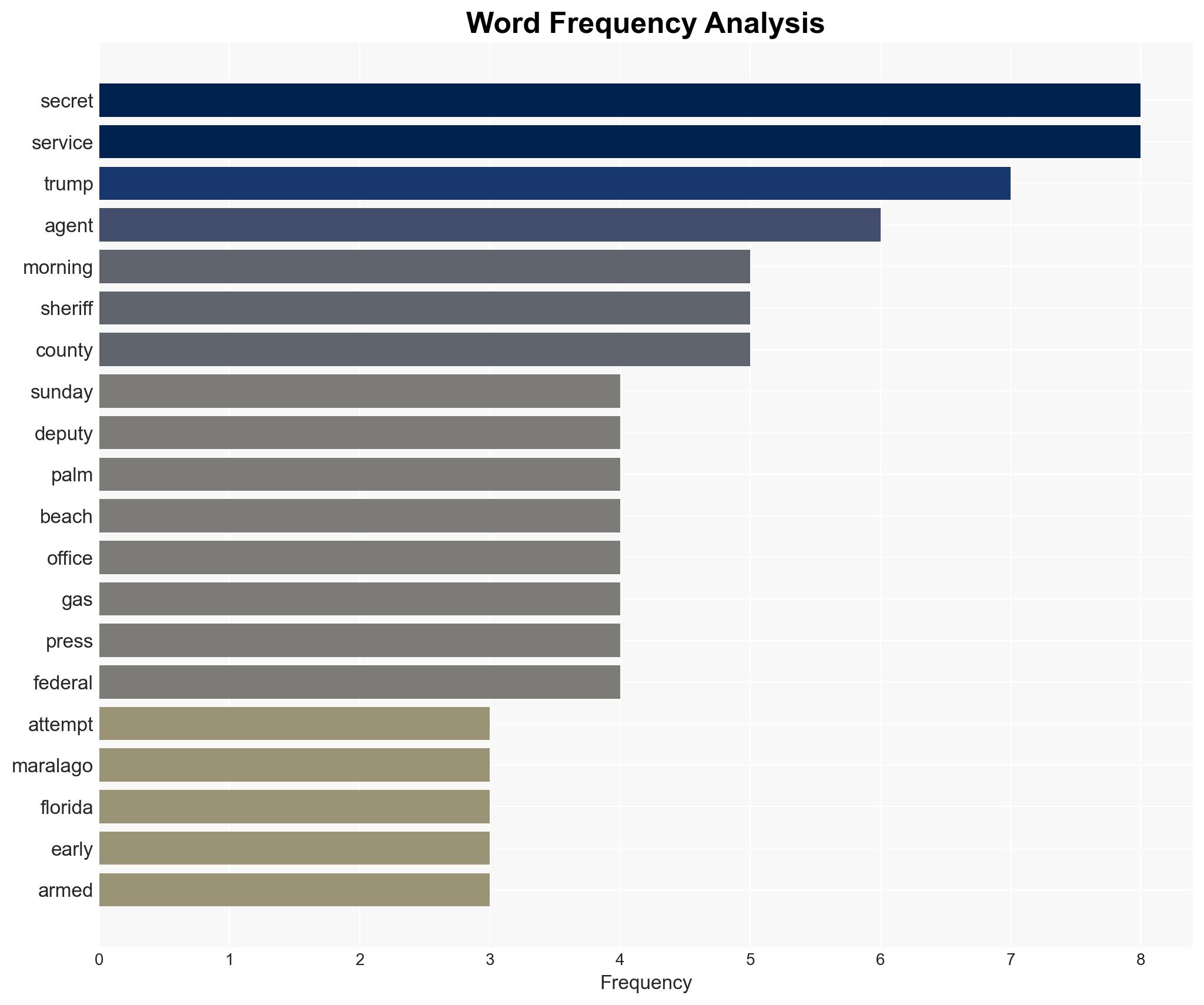
6. Key Individuals and Entities
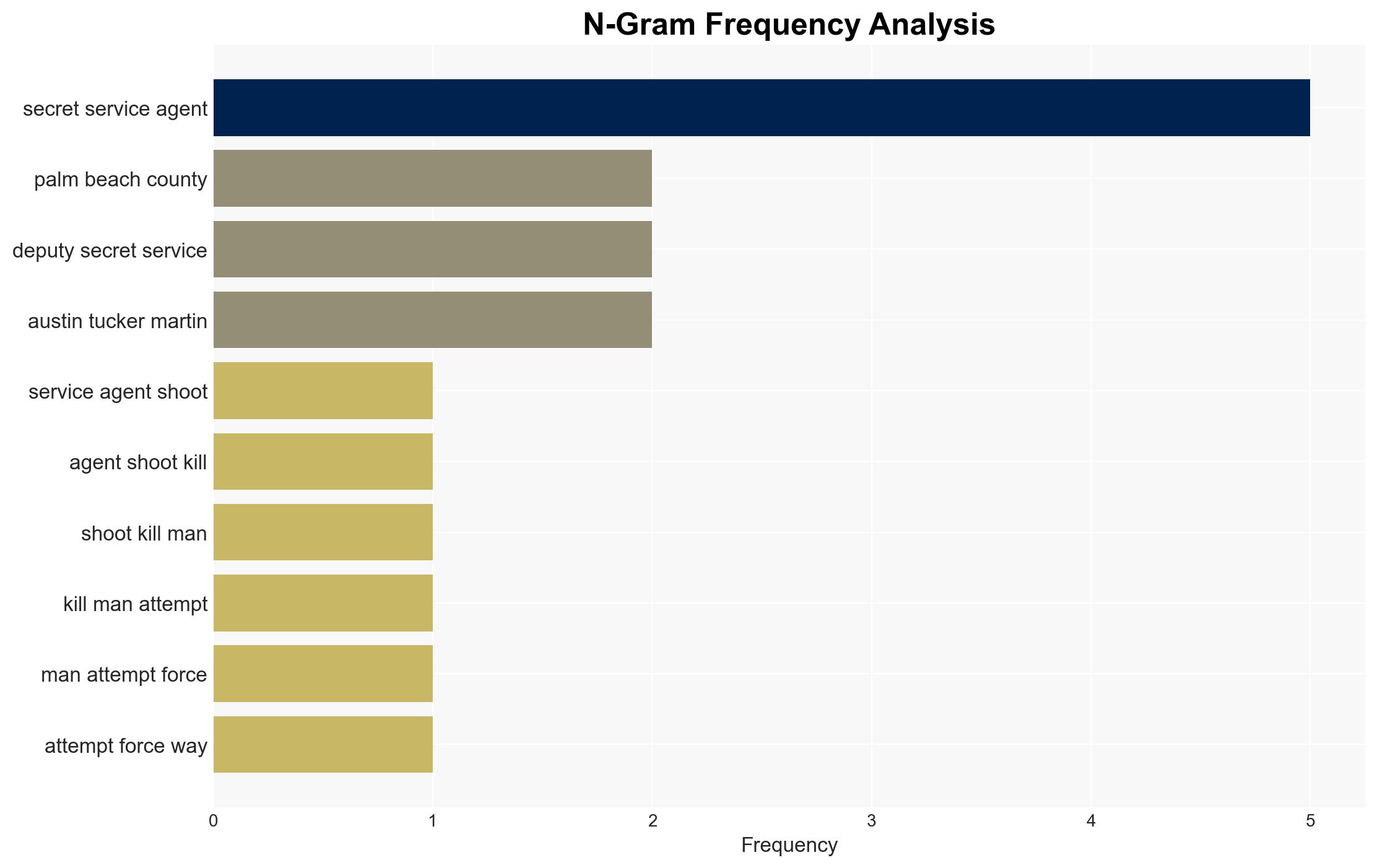
- Austin Tucker Martin (suspect)
- U.S. Secret Service
- Palm Beach County Sheriff’s Office
- Donald Trump (former President)
- Karoline Leavitt (White House Press Secretary)
7. Thematic Tags
national security threats, counter-terrorism, security protocols, political security, law enforcement, threat assessment, public safety, intelligence analysis
Structured Analytic Techniques Applied
- Cognitive Bias Stress Test: Expose and correct potential biases in assessments through red-teaming and structured challenge.
- Bayesian Scenario Modeling: Use probabilistic forecasting for conflict trajectories or escalation likelihood.
- Network Influence Mapping: Map relationships between state and non-state actors for impact estimation.
Explore more:
National Security Threats Briefs ·
Daily Summary ·
Support us