SentinelOne Reports Surge in Identity-Based Cyber Attacks Targeting Enterprises at Industrial Scale
Published on: 2026-03-25
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Hackers Exploit Compromised Enterprise Identities at Industrial Scale Warns SentinelOne
1. BLUF (Bottom Line Up Front)
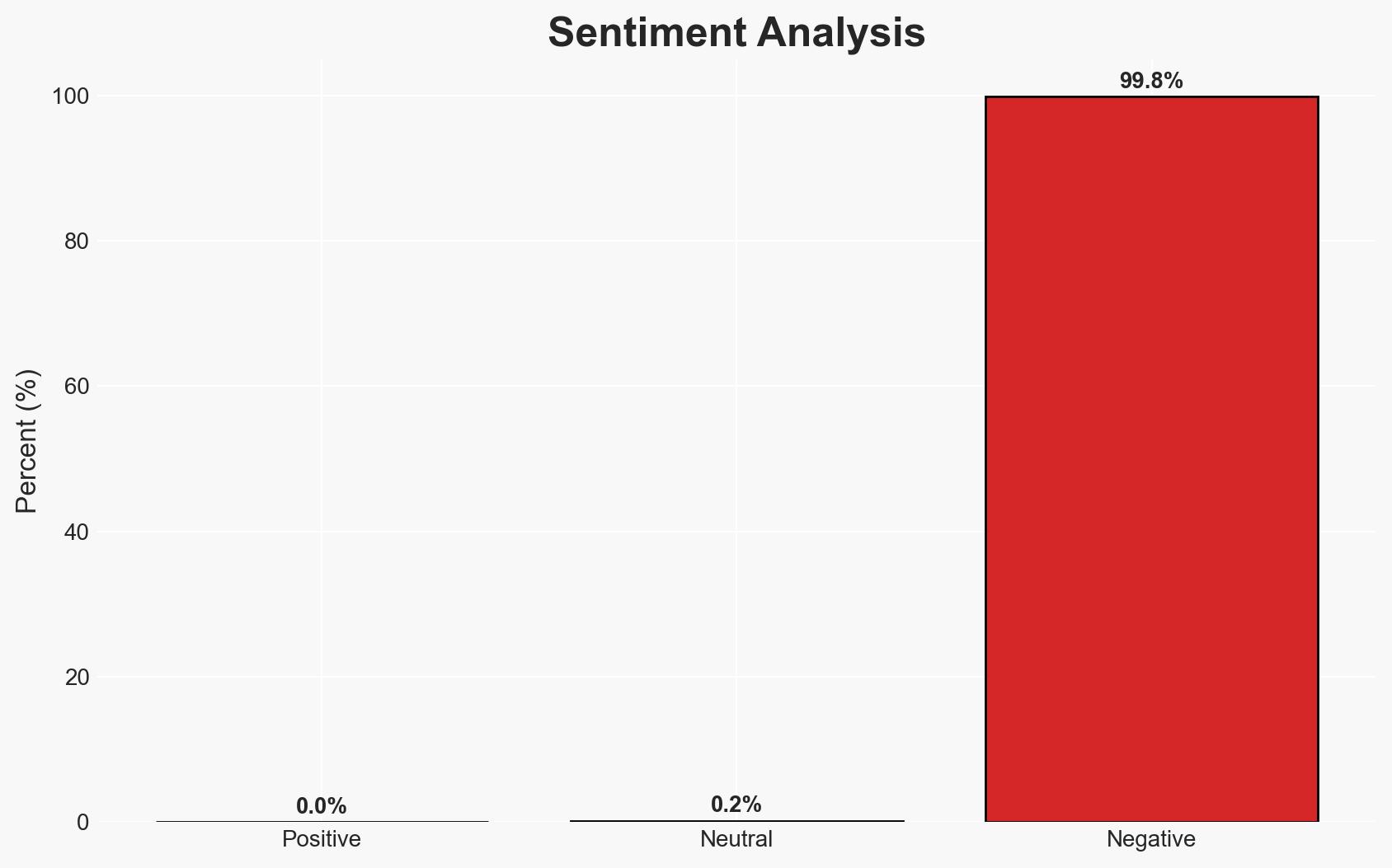
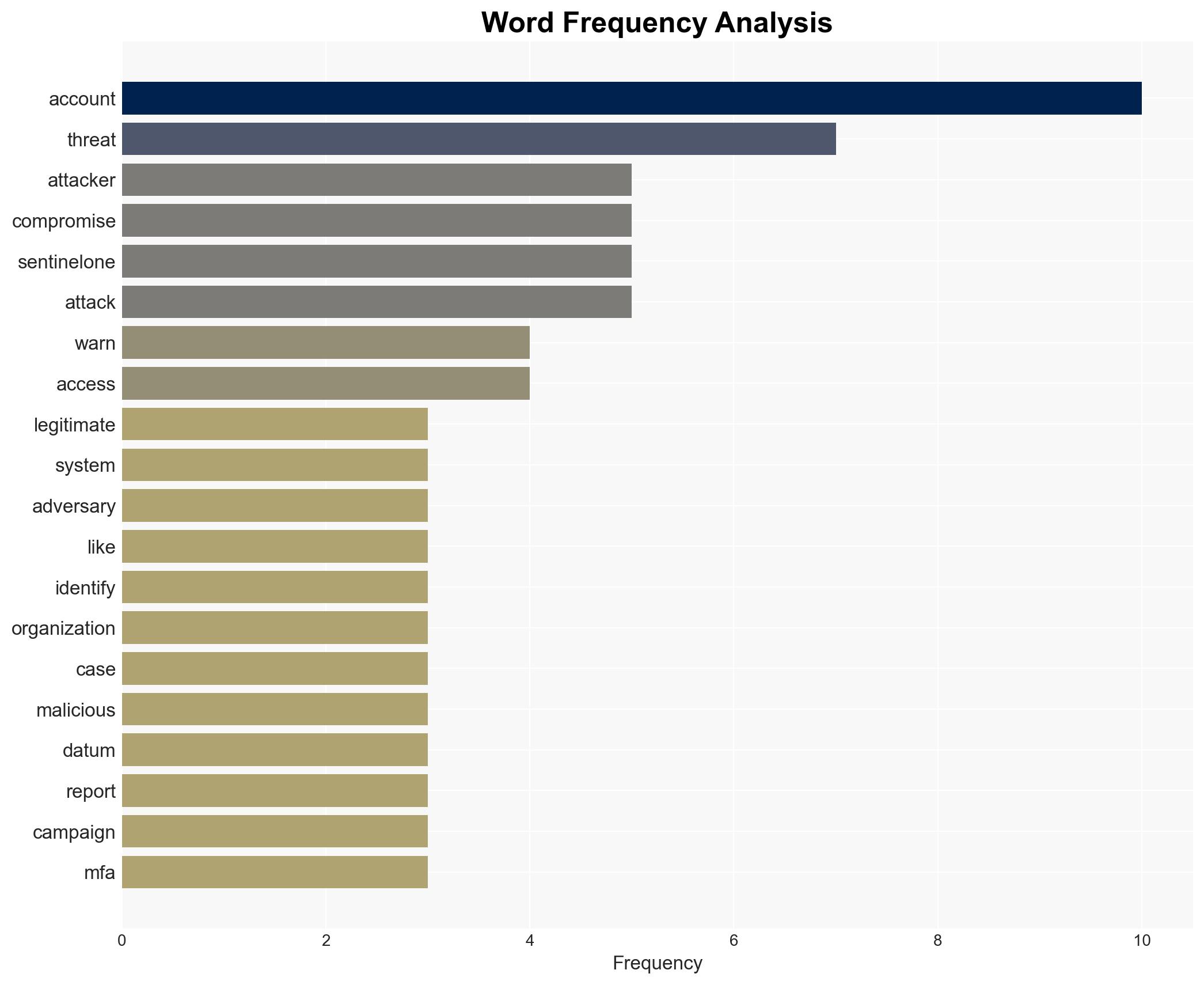
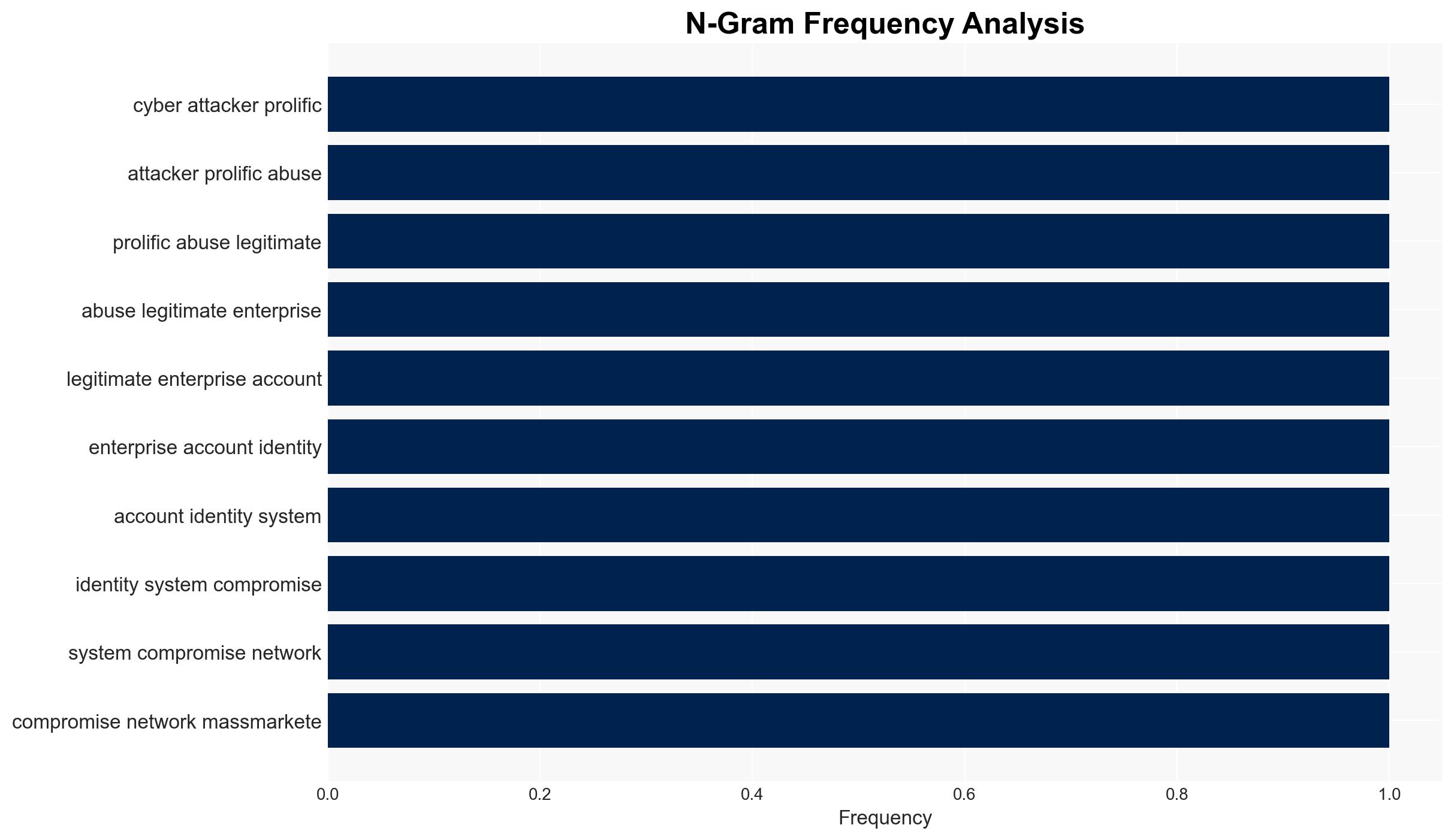
Cyber attackers are increasingly exploiting legitimate enterprise identities at an industrial scale, posing a significant threat to organizational security. The use of compromised credentials allows adversaries to bypass traditional cybersecurity measures, leading to potential data breaches and system compromises. This trend is particularly concerning for organizations with high-value intellectual property or sensitive data. Overall confidence in this assessment is moderate, given the reliance on SentinelOne’s report and the potential for undisclosed vulnerabilities.
2. Competing Hypotheses
- Hypothesis A: The increase in identity-based attacks is primarily driven by advanced persistent threat (APT) groups leveraging sophisticated social engineering and technical exploits. This is supported by the documented use of MFA bypass techniques and the involvement of state-backed actors like North Korea. However, the scale and diversity of the threat actors remain uncertain.
- Hypothesis B: The rise in these attacks is largely due to the proliferation of cybercrime tools and services, making it easier for less sophisticated actors to conduct such operations. The availability of MFA bypass kits and the use of brute force tactics support this hypothesis, though it does not fully account for the strategic targeting of high-level accounts.
- Assessment: Hypothesis A is currently better supported due to the involvement of state-backed actors and the strategic nature of the attacks. Key indicators that could shift this judgment include evidence of widespread use of these techniques by non-state actors or a significant increase in the availability of these tools on the dark web.
3. Key Assumptions and Red Flags
- Assumptions: Organizations are not fully aware of the vulnerabilities in their identity management systems; MFA provides a significant barrier to unauthorized access; State-backed actors have the resources to develop advanced bypass techniques.
- Information Gaps: The exact number and identity of organizations affected; the full range of techniques used to bypass MFA; the role of insider threats in facilitating these attacks.
- Bias & Deception Risks: Potential bias in SentinelOne’s reporting due to commercial interests; risk of deception by threat actors using false flags to obscure their true identity or intentions.
4. Implications and Strategic Risks
The industrial-scale exploitation of enterprise identities could lead to increased geopolitical tensions, particularly if state-backed actors are implicated. Organizations may face heightened security risks, necessitating a reevaluation of identity management protocols.
- Political / Geopolitical: Potential for increased tensions between states accused of sponsoring cyber operations and their targets.
- Security / Counter-Terrorism: Enhanced threat environment requiring updated security measures and threat intelligence sharing.
- Cyber / Information Space: Increased focus on identity management and MFA security; potential for new cyber defense technologies and protocols.
- Economic / Social: Potential economic impact from data breaches and loss of intellectual property; increased demand for cybersecurity professionals.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct comprehensive audits of identity management systems; enhance MFA protocols; increase monitoring for suspicious account activity.
- Medium-Term Posture (1–12 months): Develop partnerships for threat intelligence sharing; invest in advanced identity verification technologies; implement regular security training for employees.
- Scenario Outlook:
- Best: Organizations successfully implement enhanced security measures, reducing the incidence of identity-based attacks.
- Worst: Attackers continue to evolve techniques, leading to widespread breaches and significant economic damage.
- Most-Likely: Continued adaptation by both attackers and defenders, with periodic breaches prompting incremental security improvements.
6. Key Individuals and Entities
- SentinelOne (security analysts)
- State-backed North Korean hackers
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
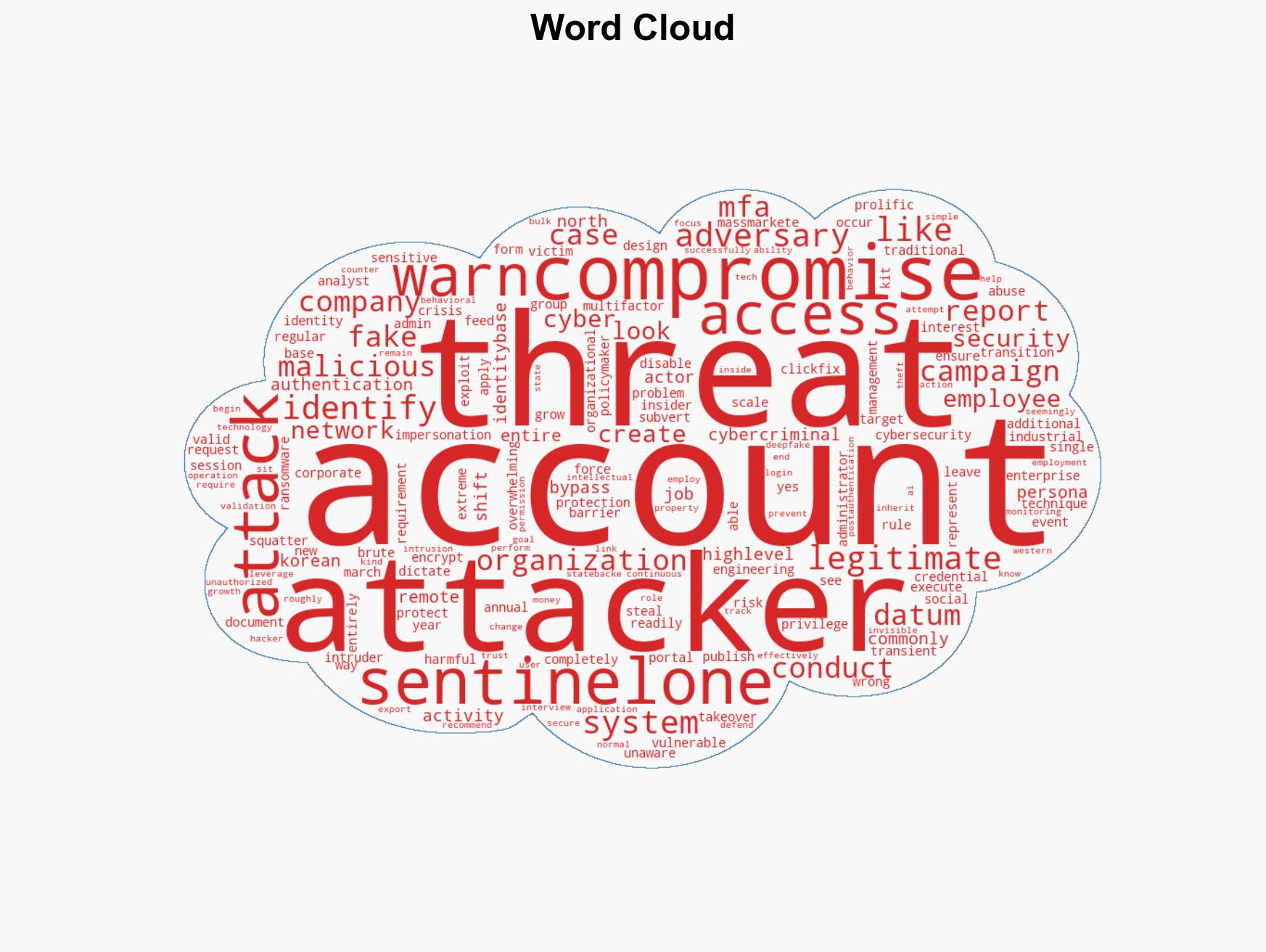
cybersecurity, identity theft, MFA bypass, state-sponsored cyber operations, insider threats, social engineering, cybercrime
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us