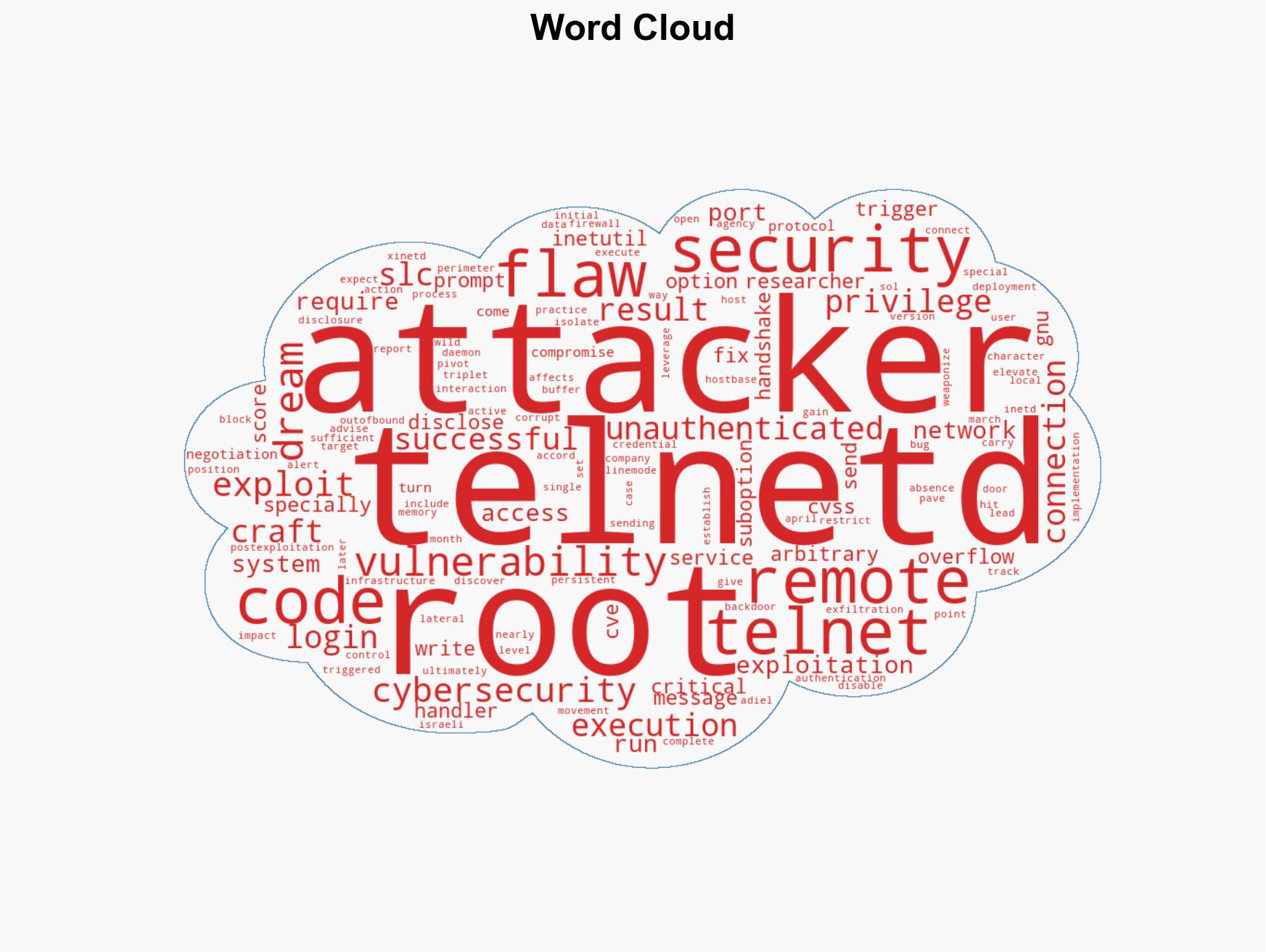
Severe Telnetd Vulnerability CVE-2026-32746 Allows Remote Code Execution via Port 23 Without Authentication
Published on: 2026-03-18
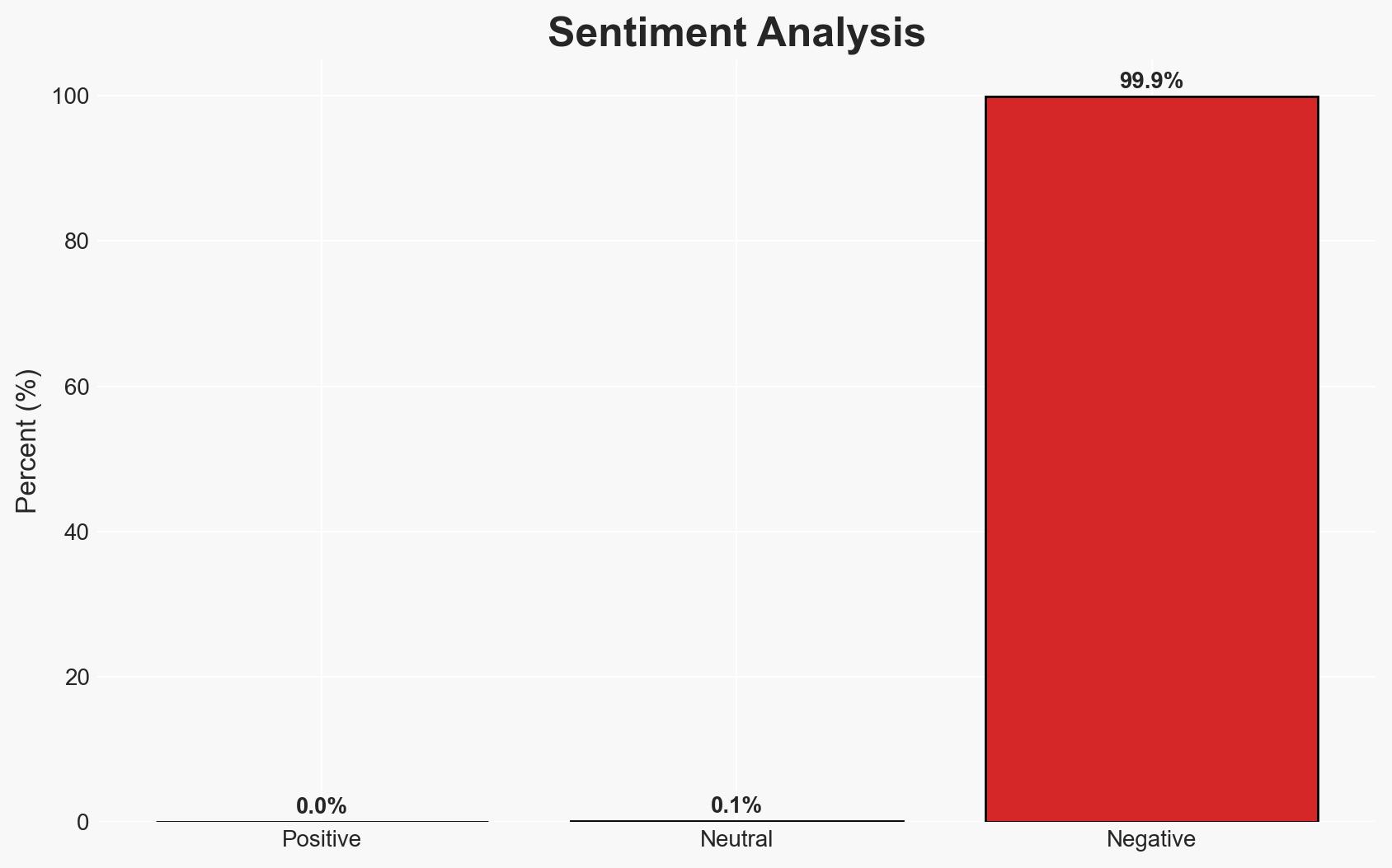
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Critical Unpatched Telnetd Flaw CVE-2026-32746 Enables Unauthenticated Root RCE via Port 23
1. BLUF (Bottom Line Up Front)
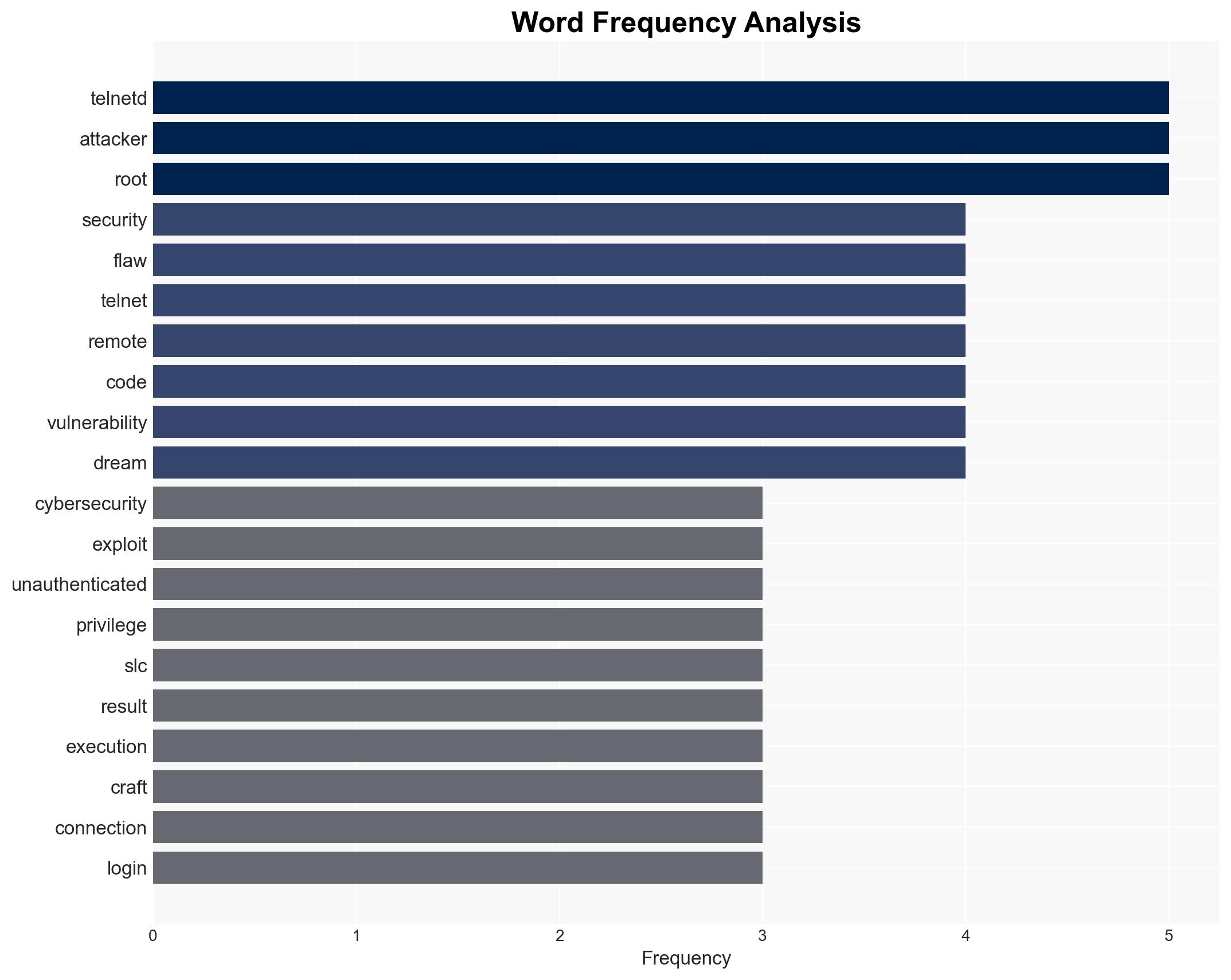
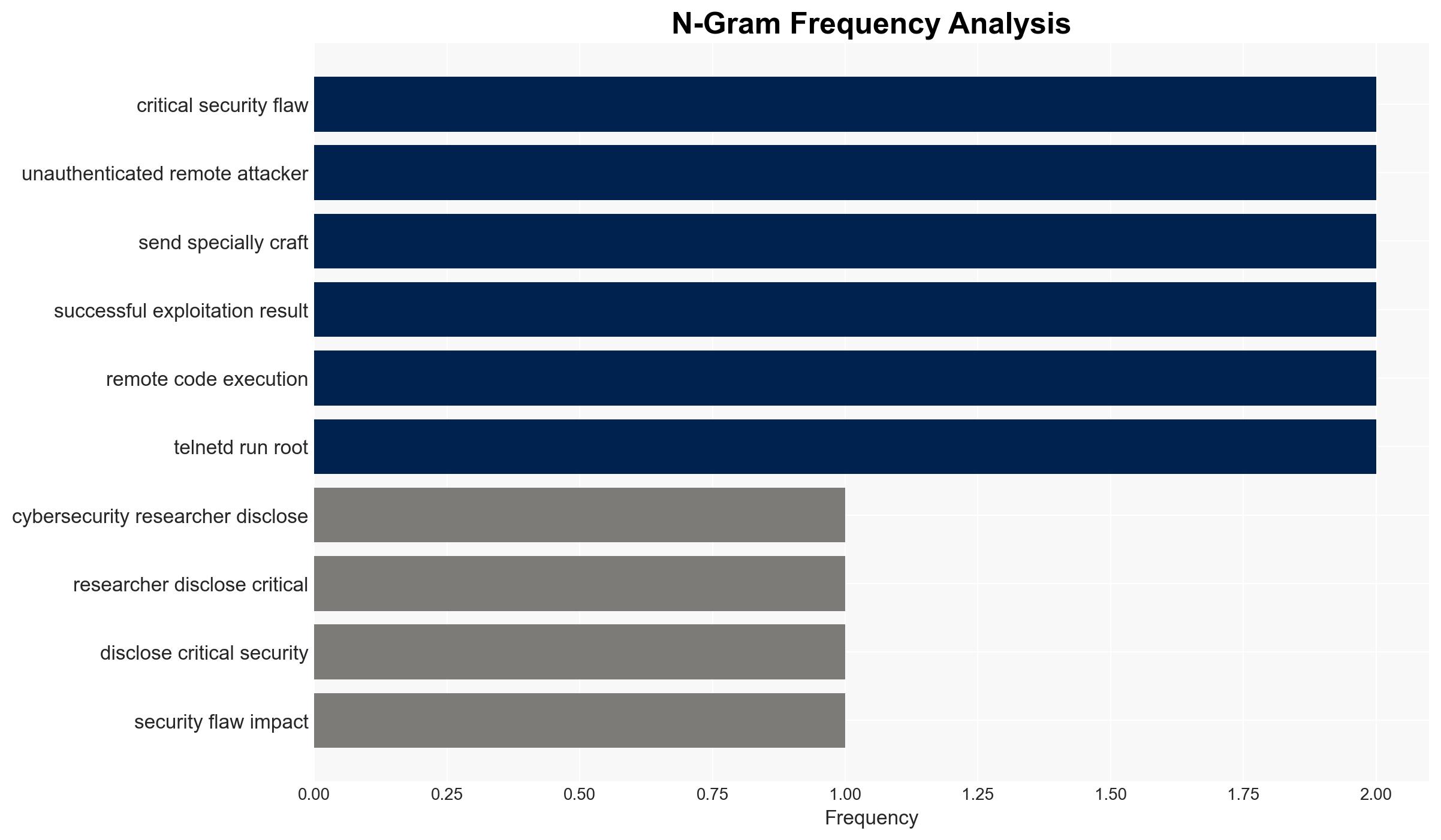
The CVE-2026-32746 vulnerability in the GNU InetUtils telnet daemon (telnetd) poses a significant security risk, allowing unauthenticated remote code execution with root privileges. This affects systems running telnetd versions up to 2.7. The most likely hypothesis is that this vulnerability will be actively exploited in the wild before a patch is released, given its critical nature and ease of exploitation. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The vulnerability will be actively exploited by cybercriminals and state-sponsored actors before a patch is released. This is supported by the high CVSS score, the ease of exploitation, and historical patterns of similar vulnerabilities being exploited quickly.
- Hypothesis B: The vulnerability will not see widespread exploitation due to proactive defensive measures by network administrators, such as disabling telnetd or blocking port 23. This is contradicted by the fact that telnetd is often run with root privileges and may not be easily disabled in all environments.
- Assessment: Hypothesis A is currently better supported due to the critical nature of the flaw and the lack of immediate mitigation options. Indicators that could shift this judgment include rapid deployment of patches or widespread adoption of mitigation strategies.
3. Key Assumptions and Red Flags
- Assumptions: The vulnerability is present in all systems running affected telnetd versions; network administrators may not immediately disable telnetd or block port 23; attackers have the capability to exploit the flaw quickly.
- Information Gaps: Specific details on the number of vulnerable systems and the speed of patch deployment are unknown.
- Bias & Deception Risks: The source of the vulnerability disclosure, Dream, may have an interest in promoting the severity of the flaw; potential underreporting of exploitation attempts.
4. Implications and Strategic Risks
This vulnerability could lead to significant security breaches if exploited, affecting critical infrastructure and sensitive data. Over time, it may interact with broader cybersecurity dynamics, such as increased regulatory scrutiny and demand for secure communication protocols.
- Political / Geopolitical: Potential for increased tensions if state-sponsored actors are implicated in exploiting the vulnerability.
- Security / Counter-Terrorism: Heightened risk of cyber-attacks on critical infrastructure, potentially impacting national security.
- Cyber / Information Space: Increased focus on securing legacy systems and protocols; potential for misinformation campaigns exploiting fear of the vulnerability.
- Economic / Social: Potential economic impact from data breaches and increased cybersecurity spending; social unrest if critical services are disrupted.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Encourage organizations to disable telnetd or block port 23 immediately; monitor for signs of exploitation; prepare incident response teams for potential breaches.
- Medium-Term Posture (1–12 months): Develop and disseminate patches; invest in secure communication alternatives; strengthen public-private partnerships for cybersecurity resilience.
- Scenario Outlook:
- Best: Rapid patch deployment prevents widespread exploitation.
- Worst: Major breaches occur, leading to significant economic and security impacts.
- Most-Likely: Some exploitation occurs before patches are widely applied, but major impacts are mitigated by defensive measures.
6. Key Individuals and Entities
- Dream (Israeli cybersecurity company)
- Adiel Sol (Dream security researcher)
- GNU InetUtils project
- U.S. Cybersecurity and Infrastructure Security Agency (CISA)
7. Thematic Tags
cybersecurity, vulnerability management, remote code execution, critical infrastructure, network security, patch management, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us