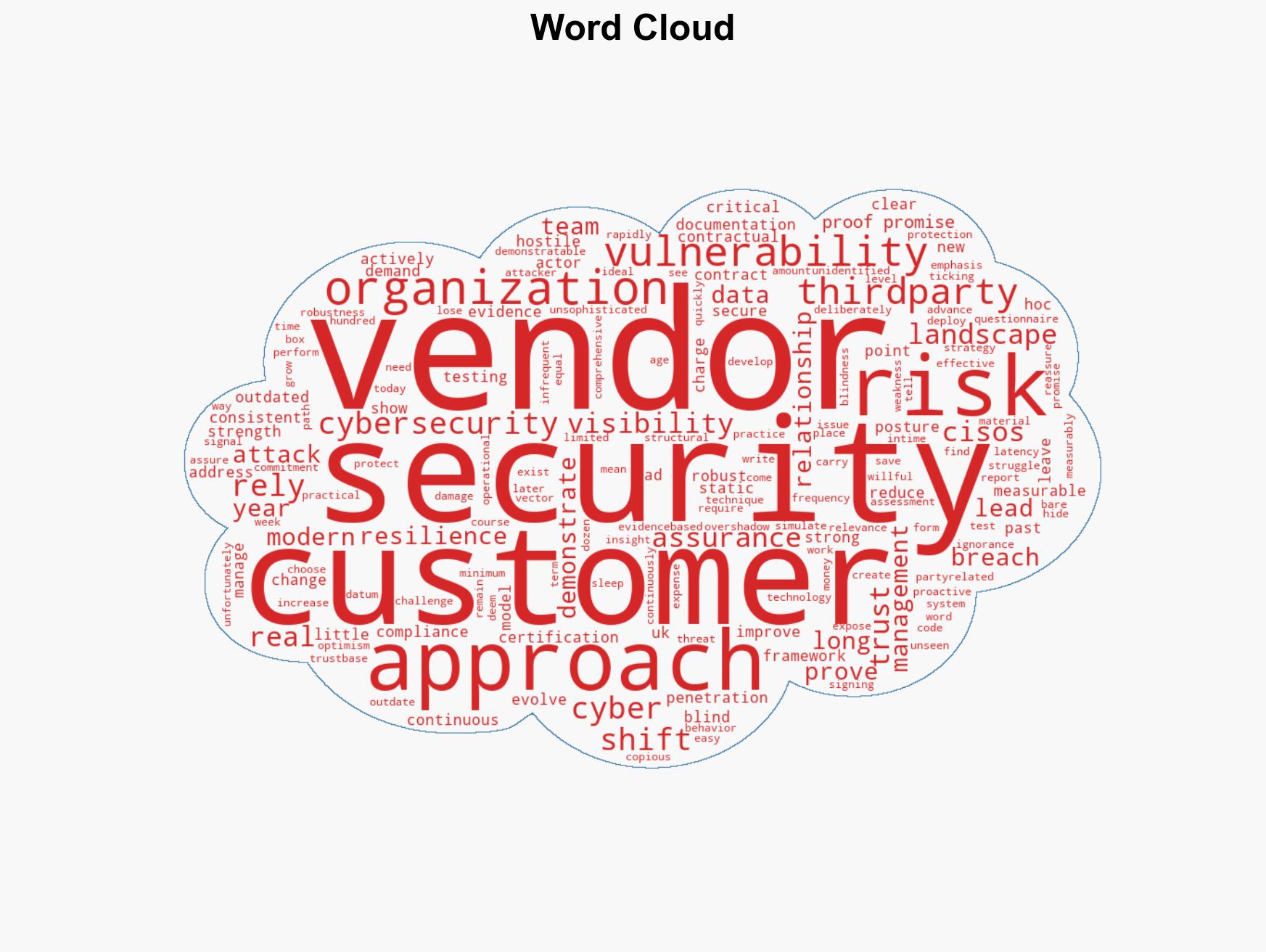
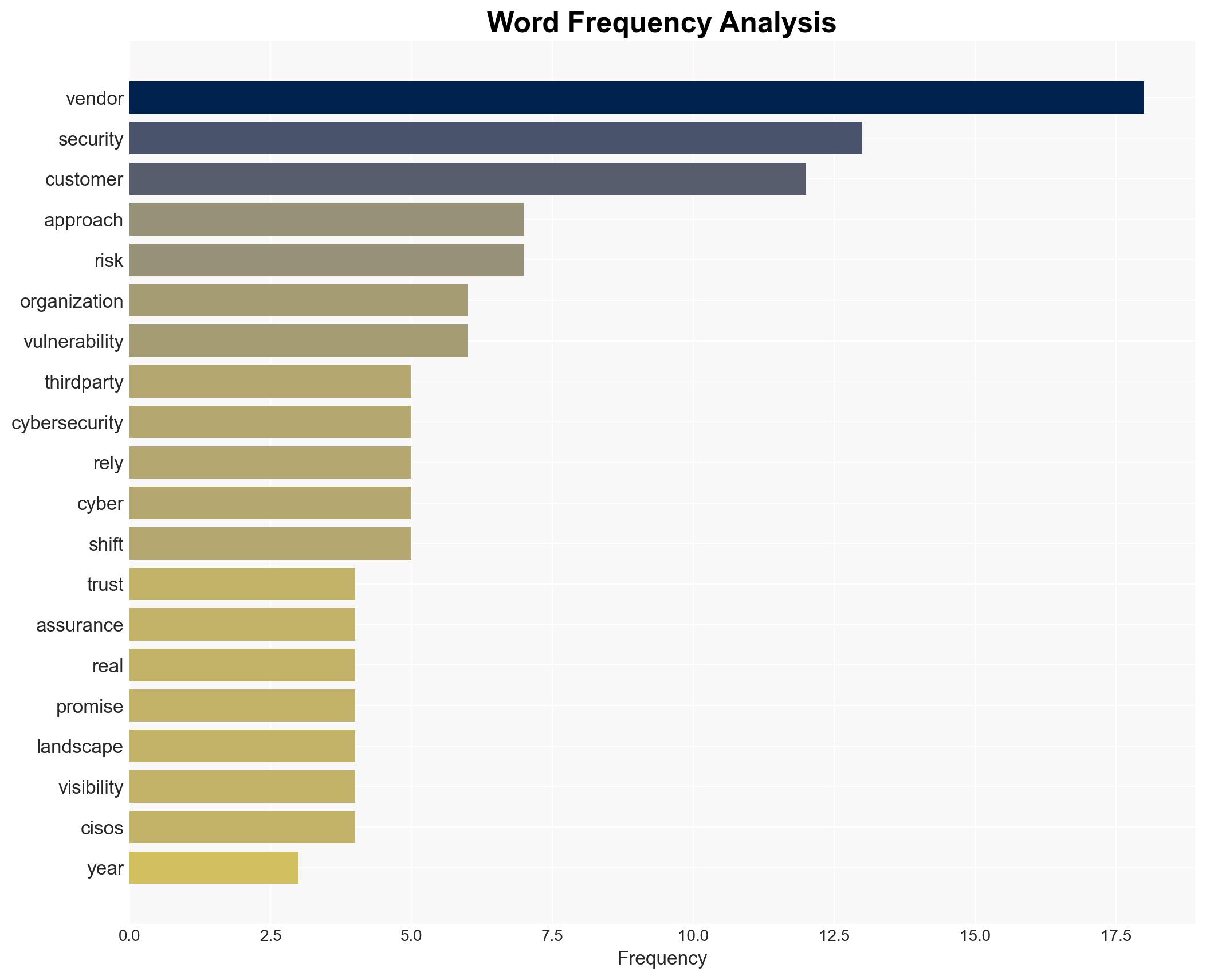
Shifting Cybersecurity Paradigm: Evidence-Based Assurance Replaces Trust in Vendor Relationships
Published on: 2026-03-14
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Proof over promises a new doctrine for cybersecurity
1. BLUF (Bottom Line Up Front)
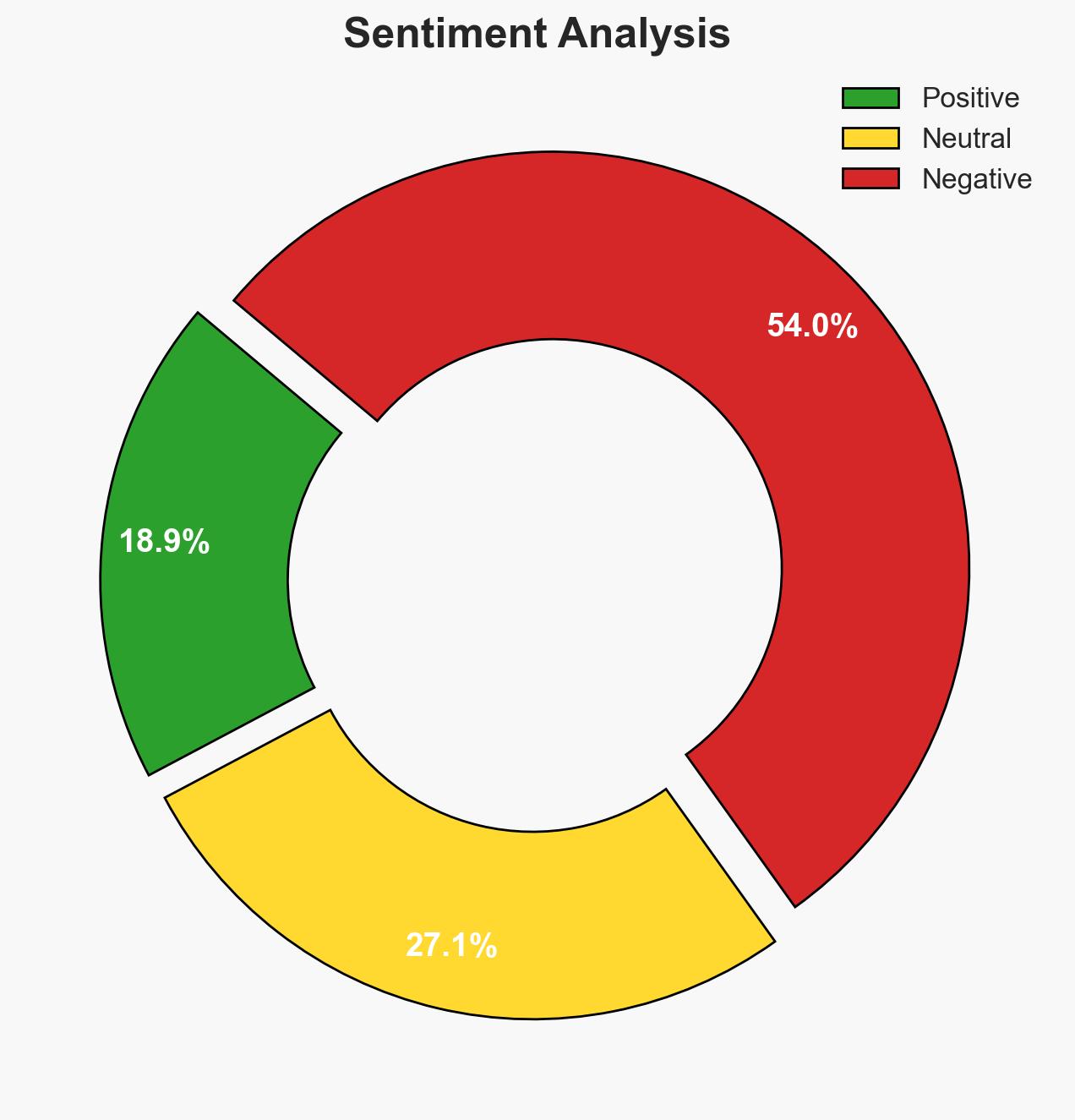
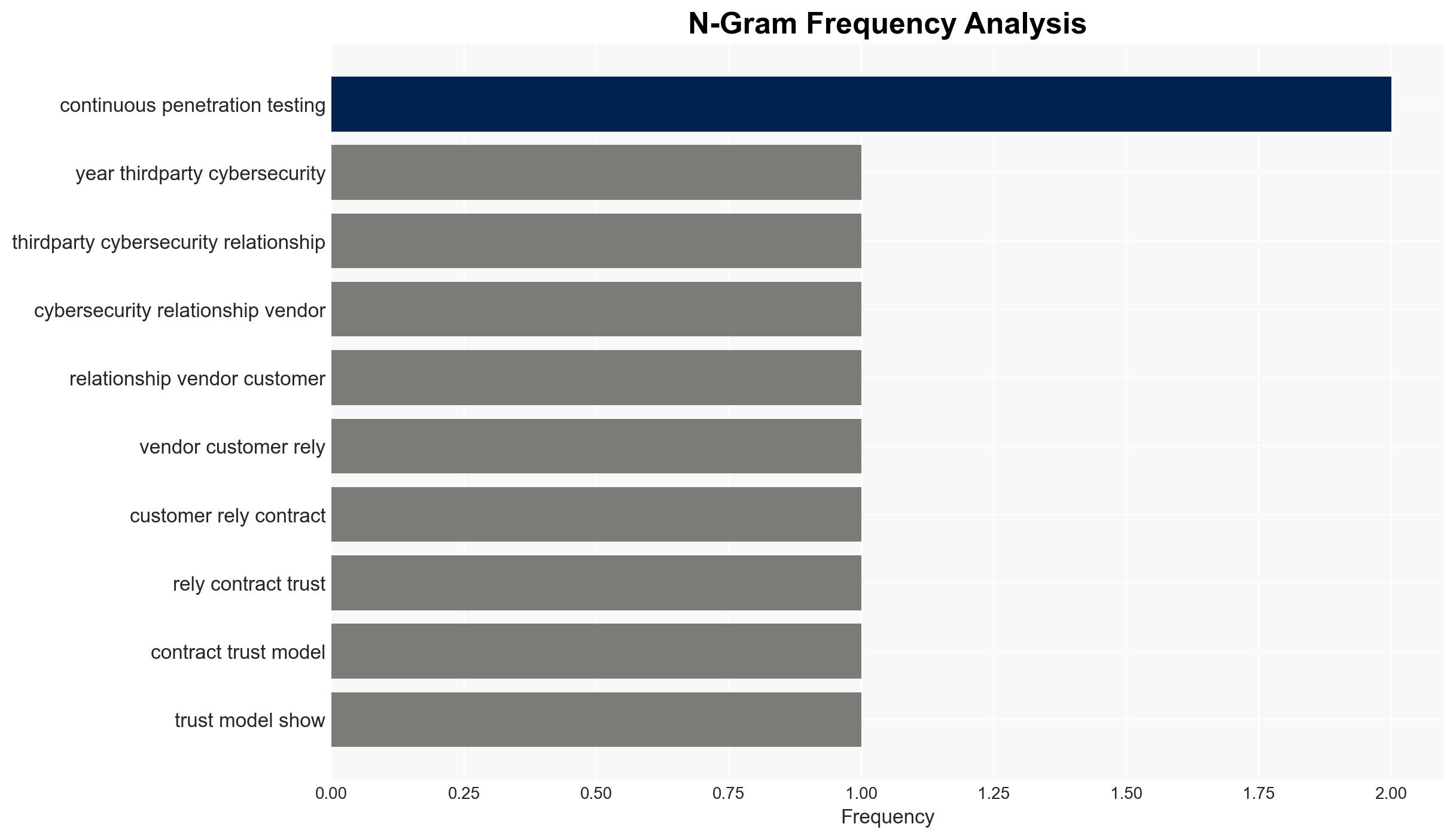
The current model of cybersecurity, based on trust and contractual assurances, is inadequate in addressing modern threats. A shift towards an evidence-based model is necessary, emphasizing continuous assessment and proactive vulnerability management. This affects vendors and their clients, with moderate confidence in the need for this transition.
2. Competing Hypotheses
- Hypothesis A: The inadequacy of the current trust-based cybersecurity model is primarily due to the increasing sophistication and frequency of cyber attacks. Evidence supports this with the high percentage of breaches linked to third-party vendors, but it is uncertain if all vendors are equally vulnerable.
- Hypothesis B: The failure of the current model is more about the lack of continuous monitoring and visibility into vendor security postures rather than the sophistication of attacks. This is supported by the emphasis on outdated point-in-time assessments, though it assumes vendors have the capability to implement continuous monitoring.
- Assessment: Hypothesis B is currently better supported, as the primary issue appears to be the lack of continuous visibility and proactive management rather than attack sophistication. Key indicators that could shift this judgment include evidence of increased attack complexity or successful continuous monitoring implementations.
3. Key Assumptions and Red Flags
- Assumptions: Vendors have the technical capability to implement continuous monitoring; Customers are willing to invest in enhanced security measures; Cyber threats will continue to evolve rapidly.
- Information Gaps: Specific data on the effectiveness of continuous monitoring in reducing breaches; Vendor willingness and capability to transition to an evidence-based model.
- Bias & Deception Risks: Potential bias in vendor self-reporting of security postures; Risk of vendors overstating capabilities to maintain client trust.
4. Implications and Strategic Risks
The shift towards an evidence-based cybersecurity model could significantly alter vendor-client relationships and the broader cybersecurity landscape.
- Political / Geopolitical: Increased regulatory scrutiny on cybersecurity practices may arise, affecting international vendor operations.
- Security / Counter-Terrorism: Enhanced vendor security could reduce attack vectors for hostile actors, potentially lowering the risk of cyber-terrorism.
- Cyber / Information Space: A focus on continuous monitoring may drive innovation in cybersecurity technologies and practices.
- Economic / Social: Vendors may face increased costs, potentially impacting pricing and market competitiveness; customer trust may be restored, enhancing market stability.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Initiate dialogues with vendors to assess current security practices; Begin pilot programs for continuous monitoring.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms specializing in continuous assessment; Invest in training for internal security teams.
- Scenario Outlook: Best: Widespread adoption of continuous monitoring reduces breaches. Worst: Vendors resist change, leading to increased breaches. Most-Likely: Gradual adoption with mixed results, driven by regulatory pressure and market demand.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, third-party risk, vendor management, continuous monitoring, cyber resilience, regulatory compliance, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us