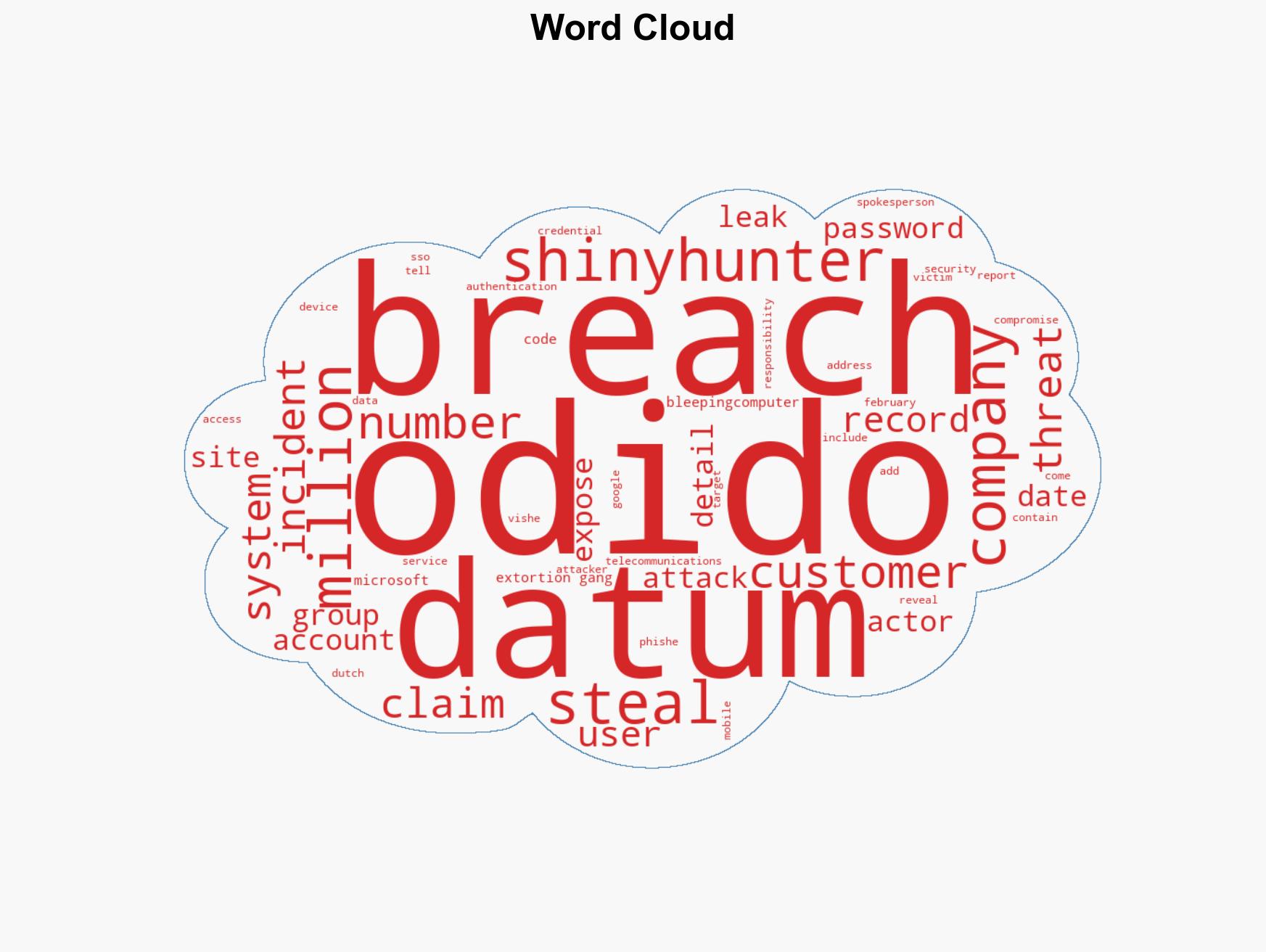
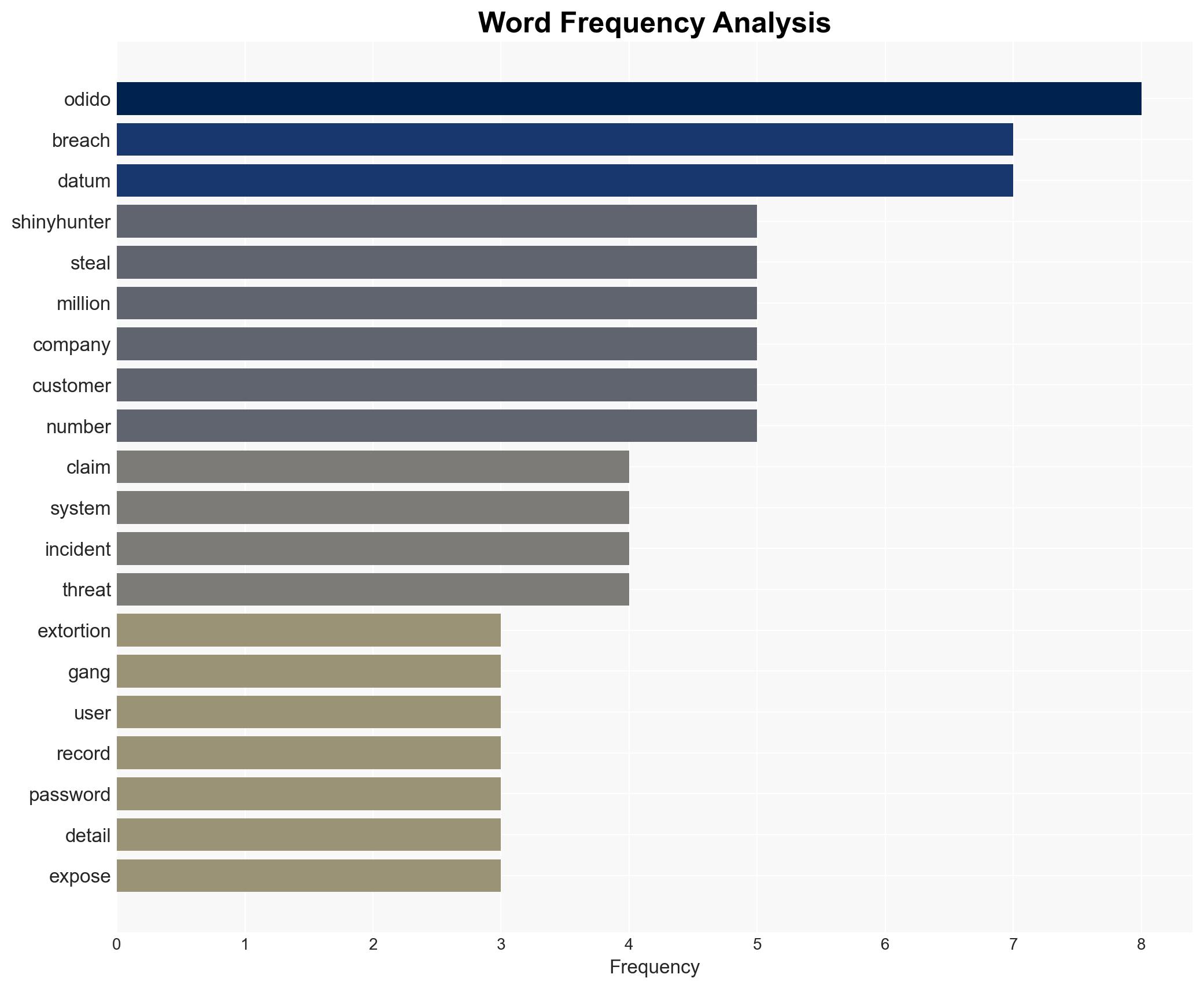
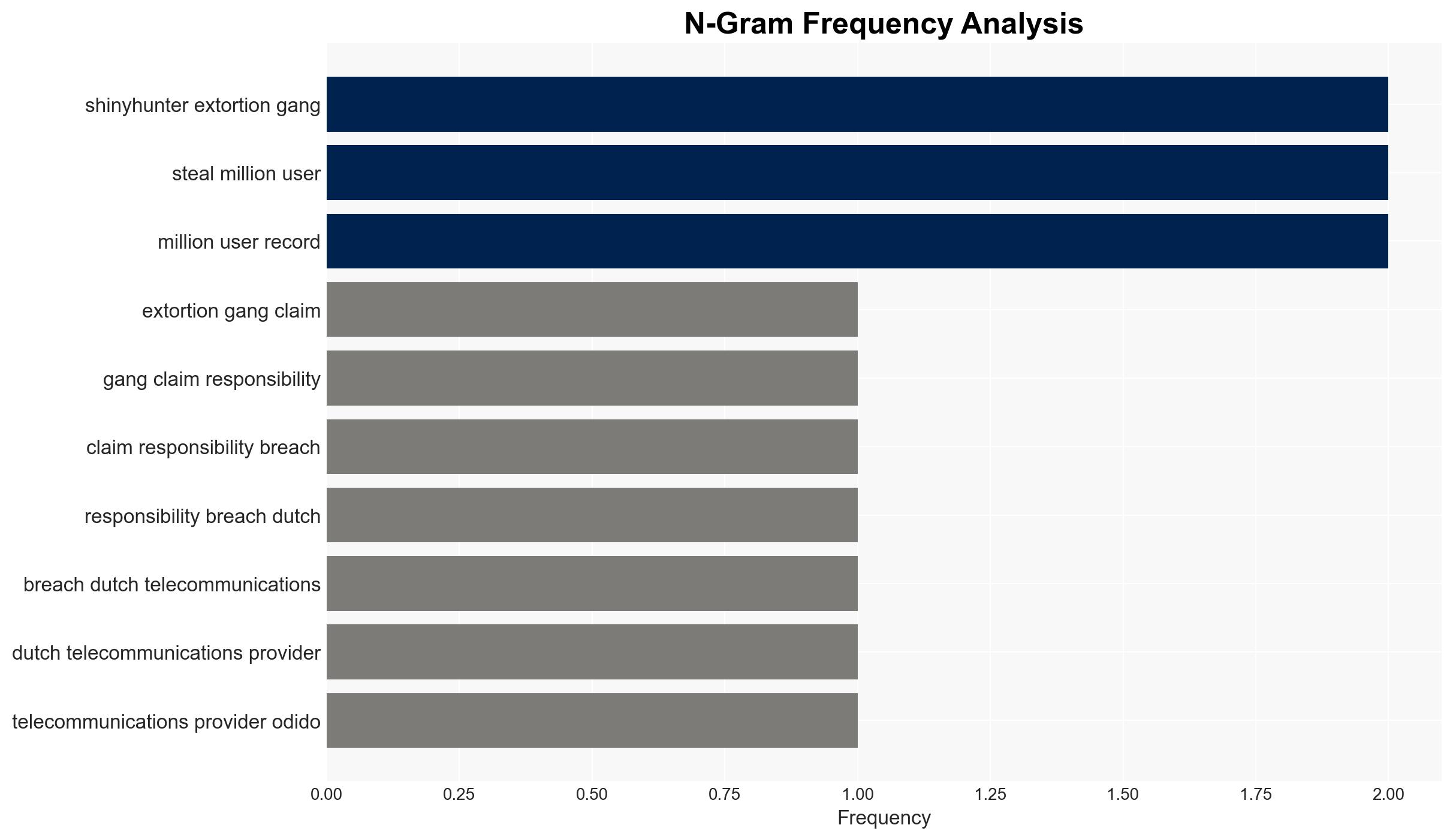
ShinyHunters claims responsibility for Odido breach impacting 6.2 million users’ personal data
Published on: 2026-02-24
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: ShinyHunters extortion gang claims Odido breach affecting millions
1. BLUF (Bottom Line Up Front)
The ShinyHunters extortion gang claims to have breached Odido, a major Dutch telecommunications provider, affecting millions of users. The breach reportedly exposed personal data, although Odido denies the exposure of sensitive information such as passwords. The situation presents a moderate confidence level in the attribution to ShinyHunters, given their history and claims, but uncertainty remains about the full extent of data compromised.
2. Competing Hypotheses
- Hypothesis A: ShinyHunters successfully breached Odido and accessed extensive user data, including sensitive internal corporate data and plaintext passwords. This is supported by ShinyHunters’ claims and their track record of similar breaches. However, Odido’s denial of certain data exposure introduces uncertainty.
- Hypothesis B: The breach was less severe than claimed by ShinyHunters, with no sensitive data such as passwords or billing information compromised. This is supported by Odido’s official statements, but lacks independent verification and could be influenced by reputational concerns.
- Assessment: Hypothesis A is currently better supported due to ShinyHunters’ established pattern of similar breaches and their public claims. Confirmation of data exposure beyond Odido’s statements could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Odido’s public statements accurately reflect the internal assessment of the breach; ShinyHunters’ claims are not exaggerated for leverage; the breach method aligns with known tactics of ShinyHunters.
- Information Gaps: Independent verification of the data types exposed; technical details of the breach method; confirmation of ShinyHunters’ involvement from third-party cybersecurity experts.
- Bias & Deception Risks: Potential bias in Odido’s public disclosures to minimize reputational damage; ShinyHunters may exaggerate claims to increase extortion pressure.
4. Implications and Strategic Risks
This breach could lead to increased scrutiny on Odido’s cybersecurity practices and potentially impact customer trust and market position. The incident may also embolden ShinyHunters and similar groups, increasing the threat landscape.
- Political / Geopolitical: Potential regulatory responses from Dutch authorities; increased pressure on telecommunications sector to enhance cybersecurity.
- Security / Counter-Terrorism: Heightened risk of further attacks on critical infrastructure; potential for copycat incidents.
- Cyber / Information Space: Increased activity on dark web markets; potential misinformation campaigns exploiting the breach.
- Economic / Social: Possible financial impact on Odido; erosion of consumer confidence in data security practices.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a thorough forensic investigation; enhance monitoring of dark web for leaked data; engage with law enforcement and cybersecurity partners.
- Medium-Term Posture (1–12 months): Strengthen cybersecurity infrastructure; implement regular security audits; develop crisis communication strategies.
- Scenario Outlook:
- Best: No further data exposure confirmed; Odido enhances security and regains customer trust.
- Worst: Further sensitive data leaks occur, leading to significant financial and reputational damage.
- Most-Likely: Limited additional data exposure; Odido faces moderate reputational challenges but mitigates long-term impact through proactive measures.
6. Key Individuals and Entities
- ShinyHunters (extortion gang)
- Odido (Dutch telecommunications provider)
- Dutch Data Protection Authority (regulatory body)
- BleepingComputer (media outlet)
7. Thematic Tags
cybersecurity, data breach, extortion, telecommunications, ShinyHunters, regulatory response, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us