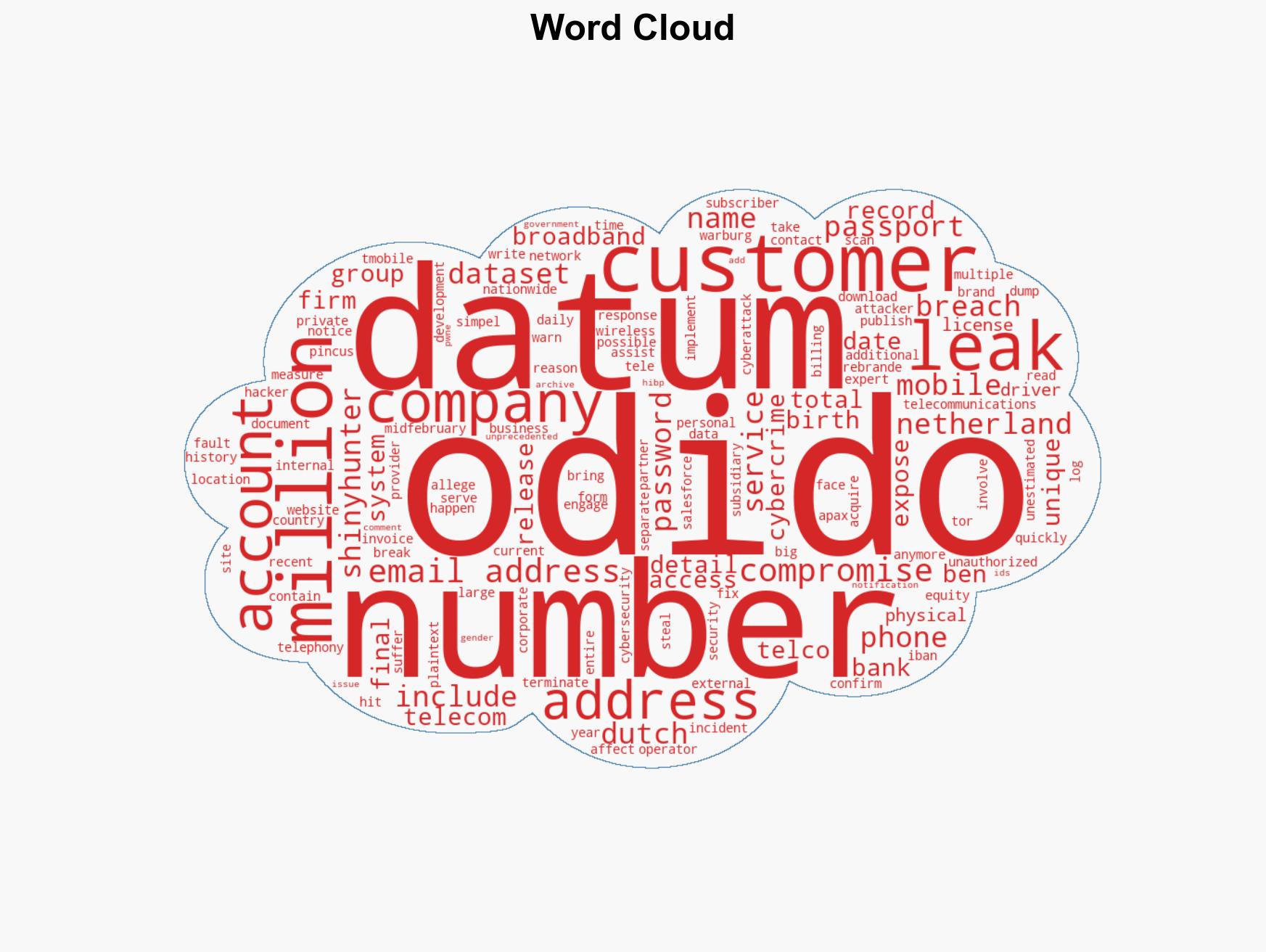
ShinyHunters Exposes Comprehensive Data Breach at Dutch Telecom Odido, Affecting Millions of Customers
Published on: 2026-03-01
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: ShinyHunters leaked the full Odido dataset
1. BLUF (Bottom Line Up Front)
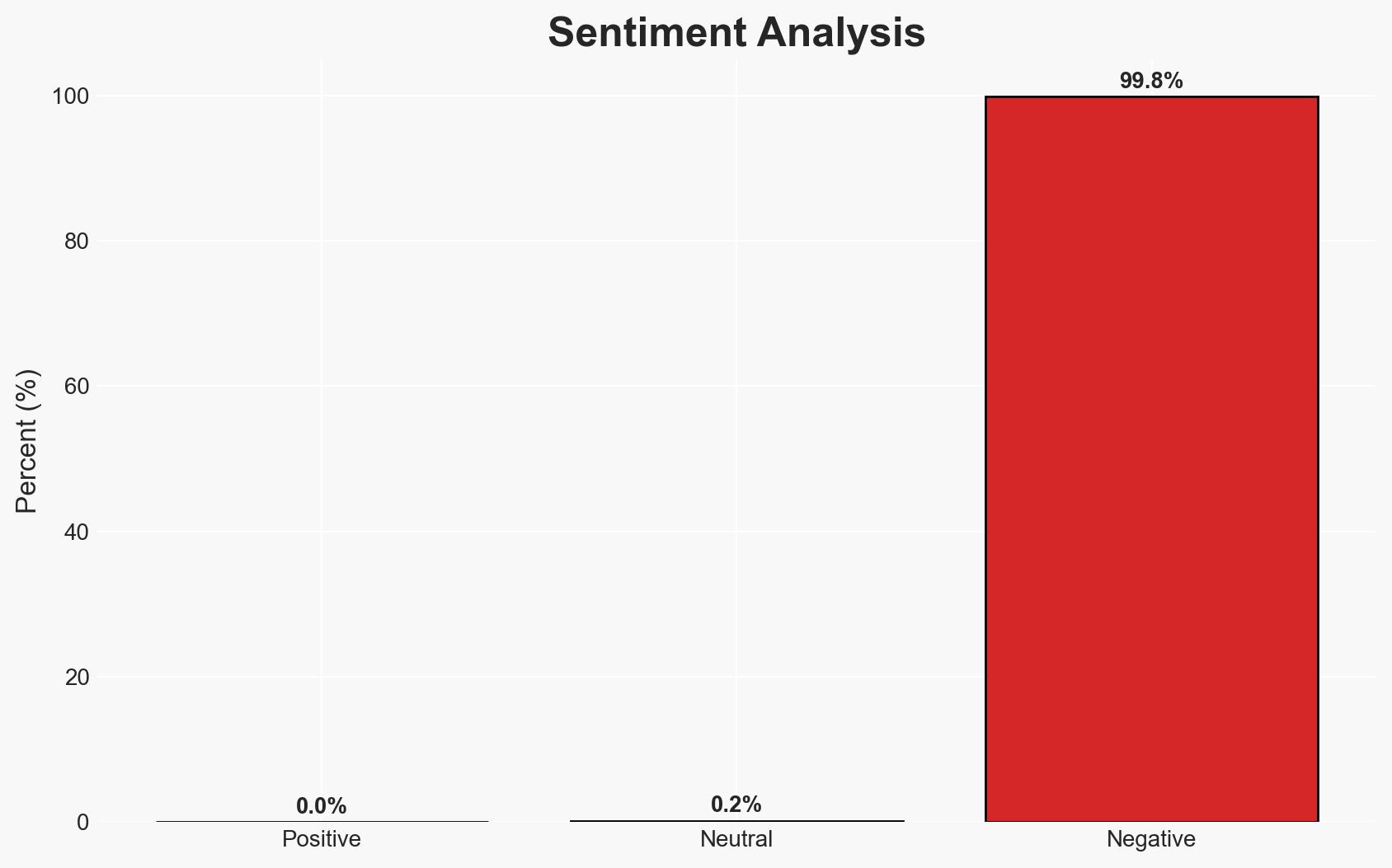
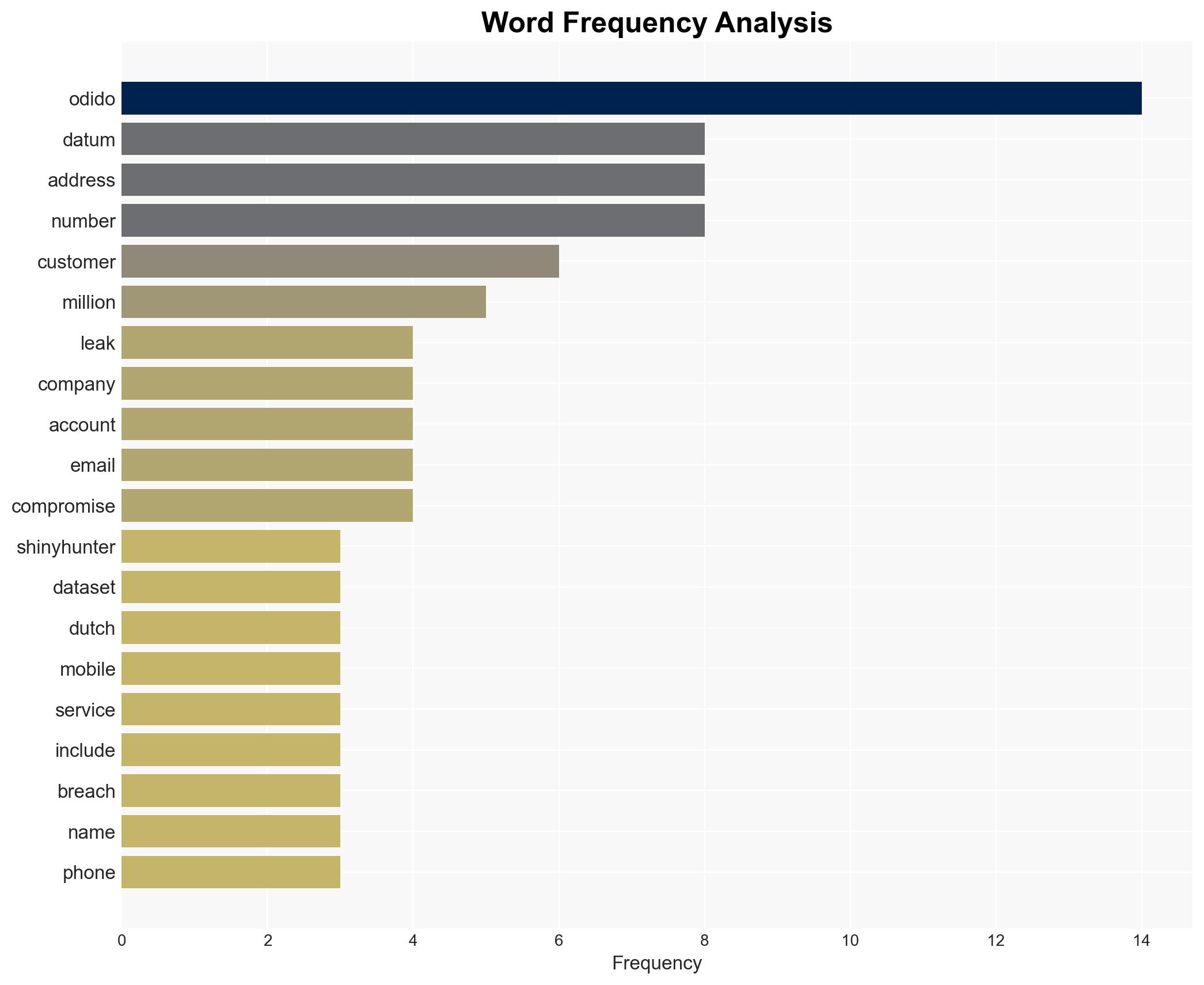
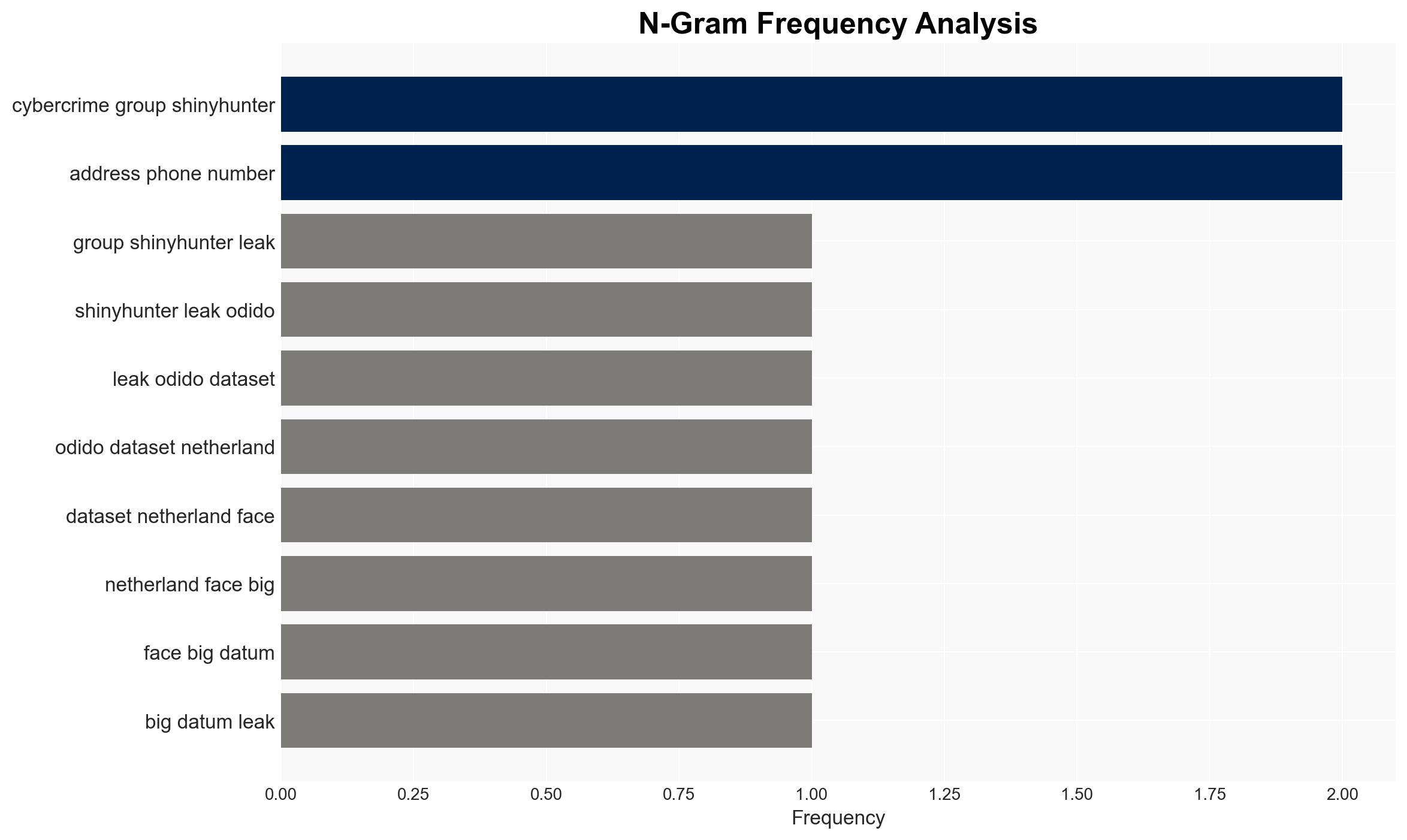
The cybercrime group ShinyHunters has leaked a comprehensive dataset from Odido, a major Dutch telecommunications company, marking the largest data breach in the Netherlands to date. This breach affects millions of customers and poses significant risks to personal privacy and national security. The most likely hypothesis is that ShinyHunters targeted Odido for financial gain and to exploit vulnerabilities in the company’s cybersecurity infrastructure. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: ShinyHunters targeted Odido primarily for financial gain, exploiting vulnerabilities in the company’s cybersecurity defenses. Supporting evidence includes the nature of the data stolen, which is valuable for identity theft and fraud. Contradicting evidence is limited but includes the possibility of other motives such as reputational damage.
- Hypothesis B: The attack on Odido was motivated by a desire to cause reputational damage and destabilize the Dutch telecommunications sector. Supporting evidence includes the public release of the data and statements blaming Odido for the breach. However, the financial value of the data suggests economic motives are more likely.
- Assessment: Hypothesis A is currently better supported due to the financial value of the stolen data and typical patterns of cybercriminal behavior. Indicators that could shift this judgment include evidence of state-sponsored involvement or further statements from ShinyHunters indicating non-financial motives.
3. Key Assumptions and Red Flags
- Assumptions: Odido’s cybersecurity measures were insufficient to prevent the breach; ShinyHunters operates primarily for financial gain; the breach was not state-sponsored.
- Information Gaps: Details on how ShinyHunters gained access to Odido’s systems; potential involvement of insider threats; full scope of data misuse.
- Bias & Deception Risks: Potential bias in Odido’s public statements minimizing the breach impact; ShinyHunters’ claims may be exaggerated to increase perceived threat.
4. Implications and Strategic Risks
This breach could lead to increased scrutiny of cybersecurity practices in the Dutch telecommunications sector and potentially influence regulatory changes. The exposure of sensitive personal data may result in widespread identity theft and financial fraud.
- Political / Geopolitical: Potential for increased regulatory pressure on telecommunications firms; diplomatic tensions if foreign actors are involved.
- Security / Counter-Terrorism: Heightened risk of cyber-attacks on critical infrastructure; potential exploitation by terrorist groups for identity theft.
- Cyber / Information Space: Increased cyber threat landscape; potential for misinformation campaigns exploiting the breach.
- Economic / Social: Possible financial losses for affected individuals; erosion of trust in digital services and telecommunications providers.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of affected accounts; engage with cybersecurity firms to assess and mitigate vulnerabilities; communicate transparently with affected customers.
- Medium-Term Posture (1–12 months): Strengthen cybersecurity infrastructure; collaborate with law enforcement to track and apprehend perpetrators; develop public awareness campaigns on data protection.
- Scenario Outlook:
- Best Case: Rapid containment of breach impacts, improved cybersecurity measures, and minimal long-term damage.
- Worst Case: Prolonged exploitation of leaked data, significant financial and reputational damage to Odido, and increased regulatory burdens.
- Most-Likely: Moderate financial and reputational impact with gradual recovery and improved cybersecurity practices.
6. Key Individuals and Entities
- Odido (Dutch telecommunications company)
- ShinyHunters (cybercrime group)
- Apax Partners (private equity firm)
- Warburg Pincus (private equity firm)
- Not clearly identifiable from open sources in this snippet for specific individuals involved.
7. Thematic Tags
cybersecurity, data breach, telecommunications, identity theft, cybercrime
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us