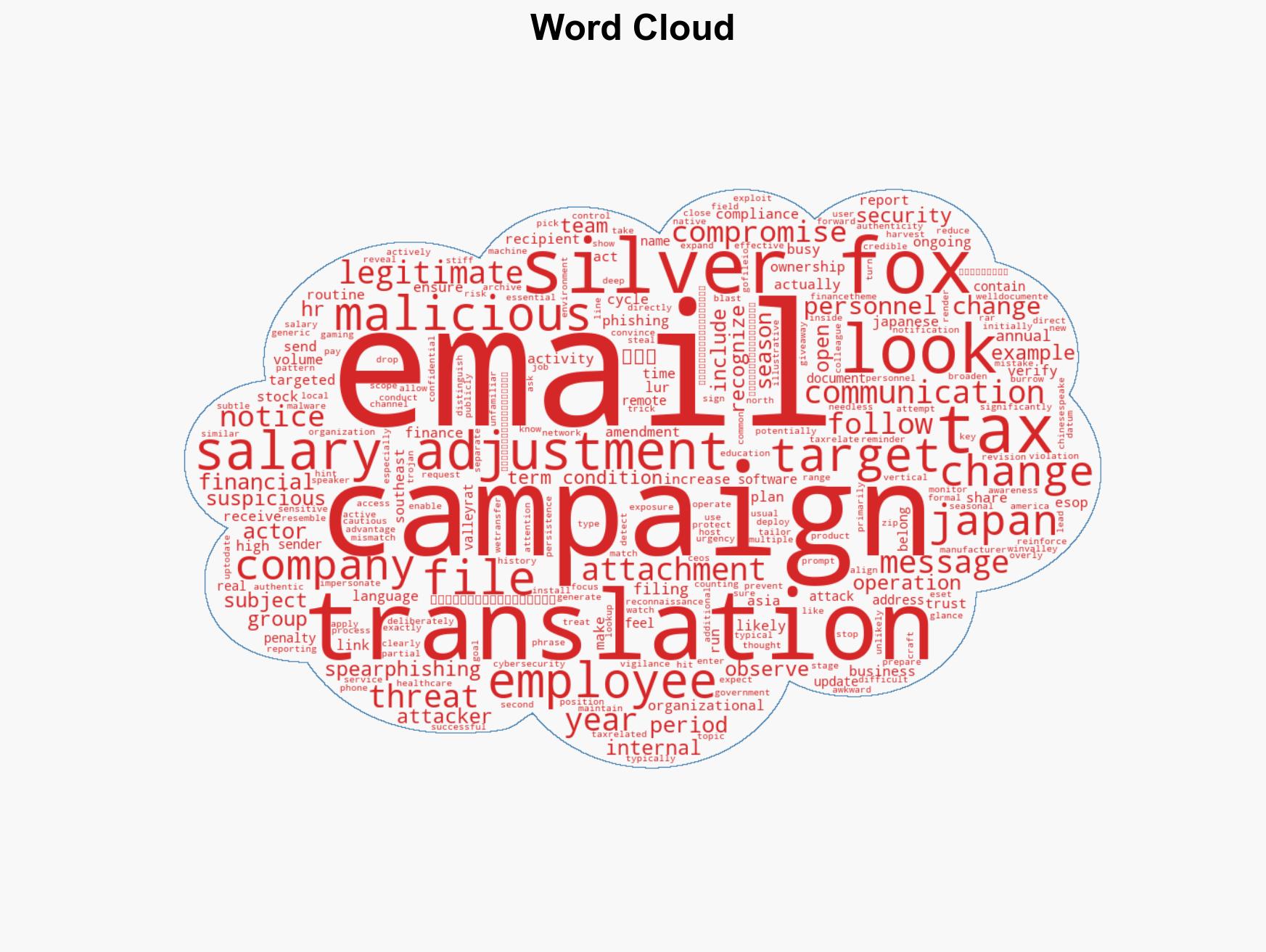
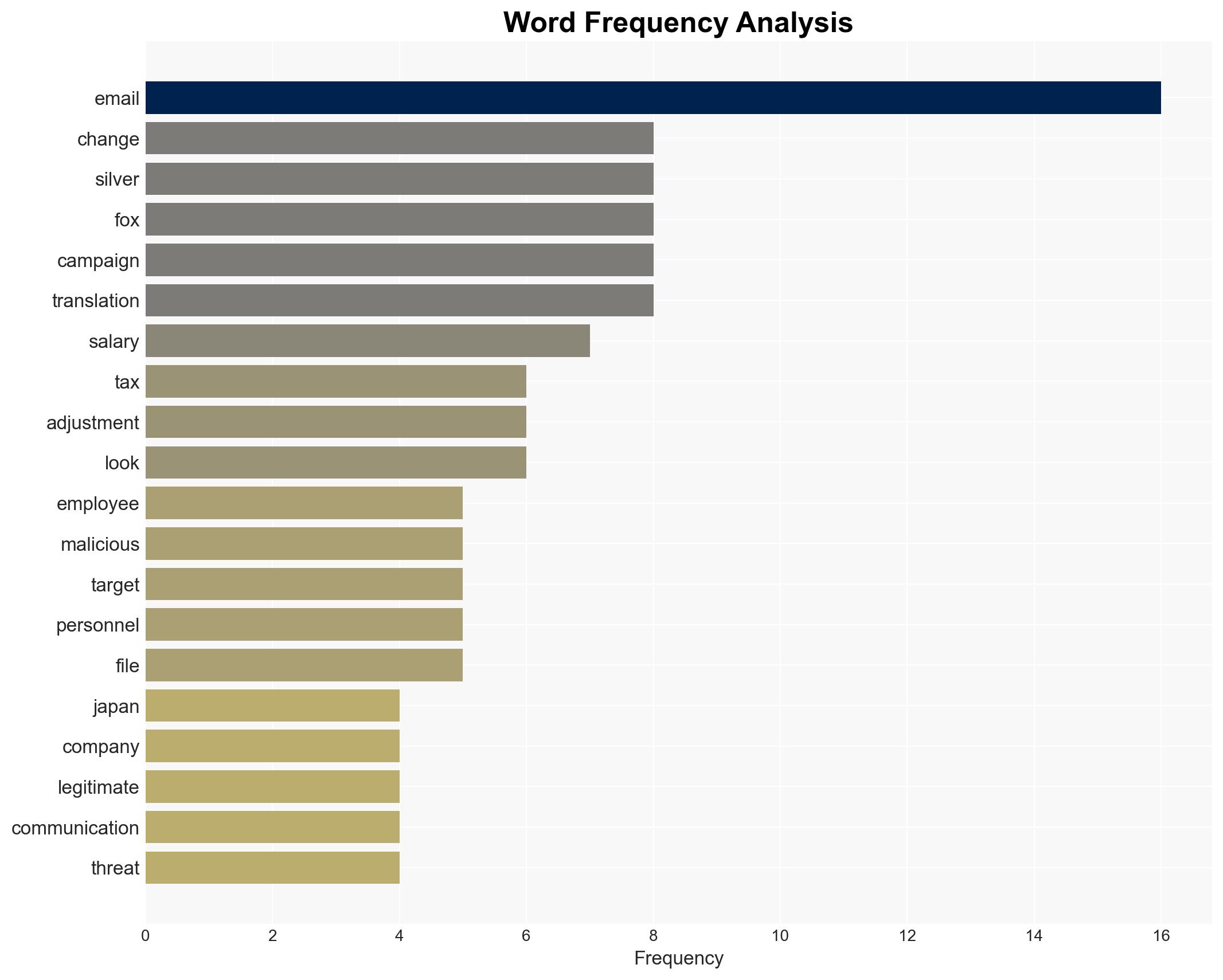
Silver Fox Exploits Tax Season to Target Japanese Firms with Spearphishing Campaign
Published on: 2026-03-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: A cunning predator How Silver Fox preys on Japanese firms this tax season
1. BLUF (Bottom Line Up Front)
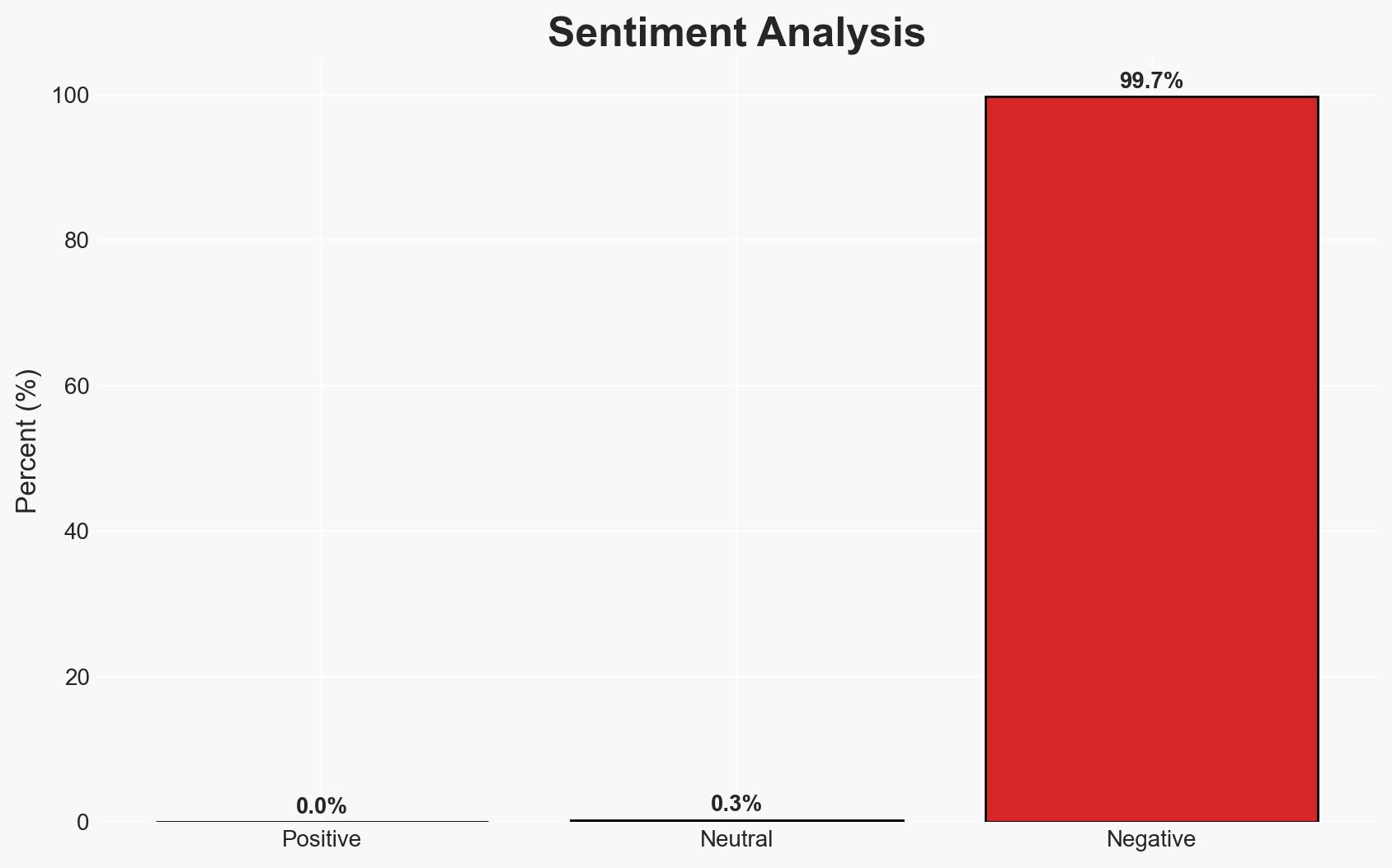
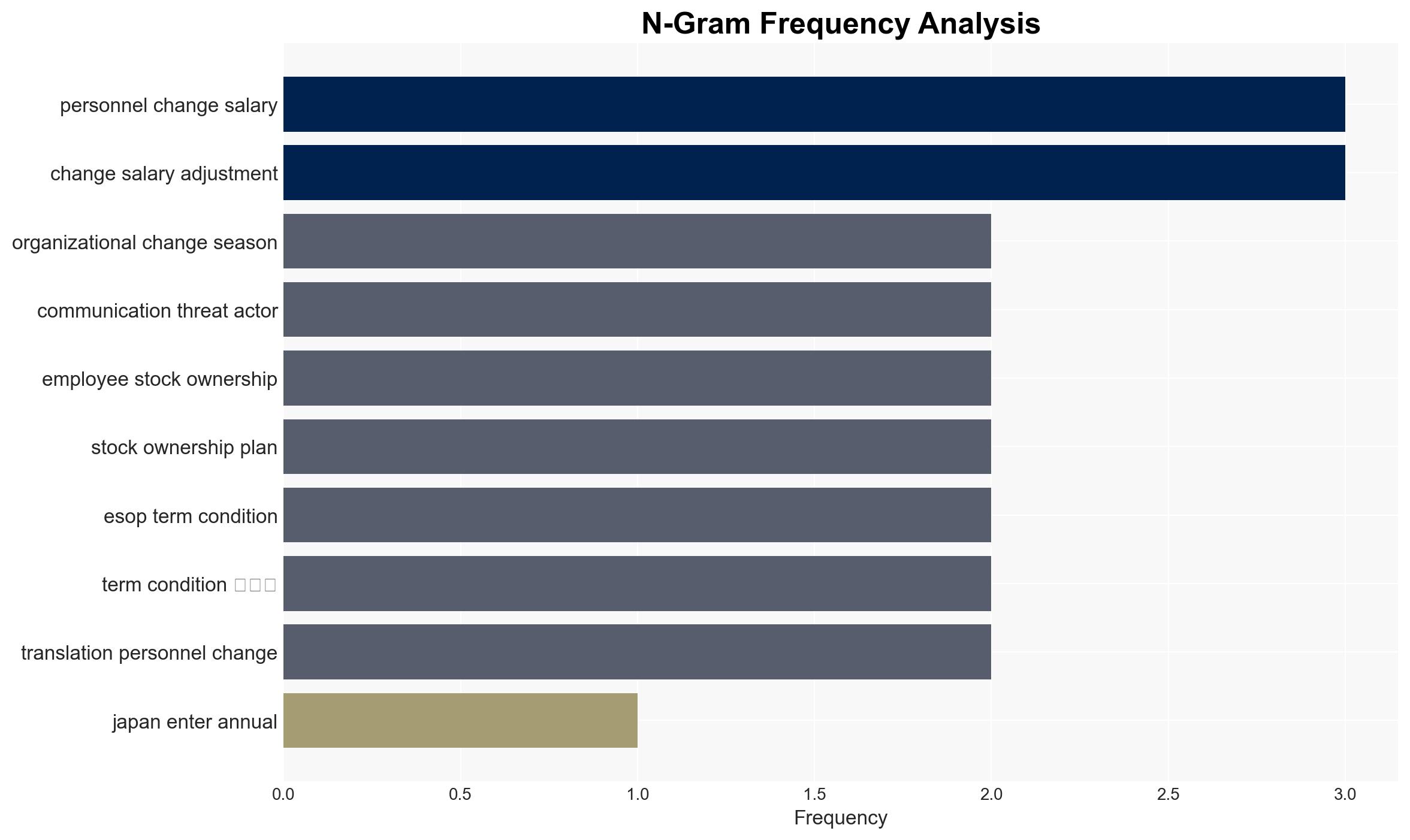
Silver Fox is exploiting Japan’s tax season to conduct a spearphishing campaign targeting Japanese firms, particularly in manufacturing. The campaign leverages expected tax and HR communications to increase the likelihood of compromise. This activity poses a significant cyber threat to Japanese businesses, with moderate confidence in the assessment due to the recurring nature of the campaign and its alignment with seasonal business cycles.
2. Competing Hypotheses
- Hypothesis A: Silver Fox is deliberately targeting Japanese firms during tax season to exploit increased communication traffic and reduce detection risk. This is supported by the timing of the campaign and the use of localized language in phishing emails. However, the full extent of their operational capabilities and specific targets remain uncertain.
- Hypothesis B: Silver Fox’s campaign is opportunistic rather than strategic, taking advantage of any high-traffic period without specific focus on Japan. This is contradicted by the observed pattern of targeting during tax seasons in various regions, suggesting a strategic approach.
- Assessment: Hypothesis A is currently better supported due to the consistent pattern of targeting during tax seasons and the use of localized tactics. Indicators such as changes in targeting patterns or new phishing themes could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Silver Fox has the capability to localize operations effectively; Japanese firms have not significantly improved phishing defenses since last year; the campaign’s success relies on the volume of legitimate communications.
- Information Gaps: Specific details on the malware used, the exact number of compromised entities, and the identity of Silver Fox’s leadership.
- Bias & Deception Risks: Potential over-reliance on patterns from previous years; source bias from cybersecurity firms with vested interests in highlighting threats.
4. Implications and Strategic Risks
This development could lead to increased cyber vulnerability for Japanese firms, affecting economic stability and potentially leading to geopolitical tensions if linked to state-sponsored actors.
- Political / Geopolitical: Potential strain on Japan’s international relations if Silver Fox is linked to a state actor.
- Security / Counter-Terrorism: Increased need for cybersecurity measures and potential shifts in threat actor focus.
- Cyber / Information Space: Heightened awareness and potential for increased cybersecurity investments and policy changes.
- Economic / Social: Possible financial losses for affected firms, leading to broader economic impacts and reduced trust in digital communications.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance phishing awareness training, implement robust email filtering, and increase monitoring of tax-related communications.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms for threat intelligence sharing and invest in advanced threat detection technologies.
- Scenario Outlook: Best: Improved defenses reduce successful phishing attempts. Worst: Widespread compromise leads to significant financial losses. Most-Likely: Continued targeted attempts with moderate success, prompting gradual improvements in cybersecurity posture.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, spearphishing, Japan, tax season, Silver Fox, cyber threat, economic impact
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us