SolarWinds addresses critical Serv-U vulnerabilities allowing root access to servers with security updates
Published on: 2026-02-24
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Critical SolarWinds Serv-U flaws offer root access to servers
1. BLUF (Bottom Line Up Front)
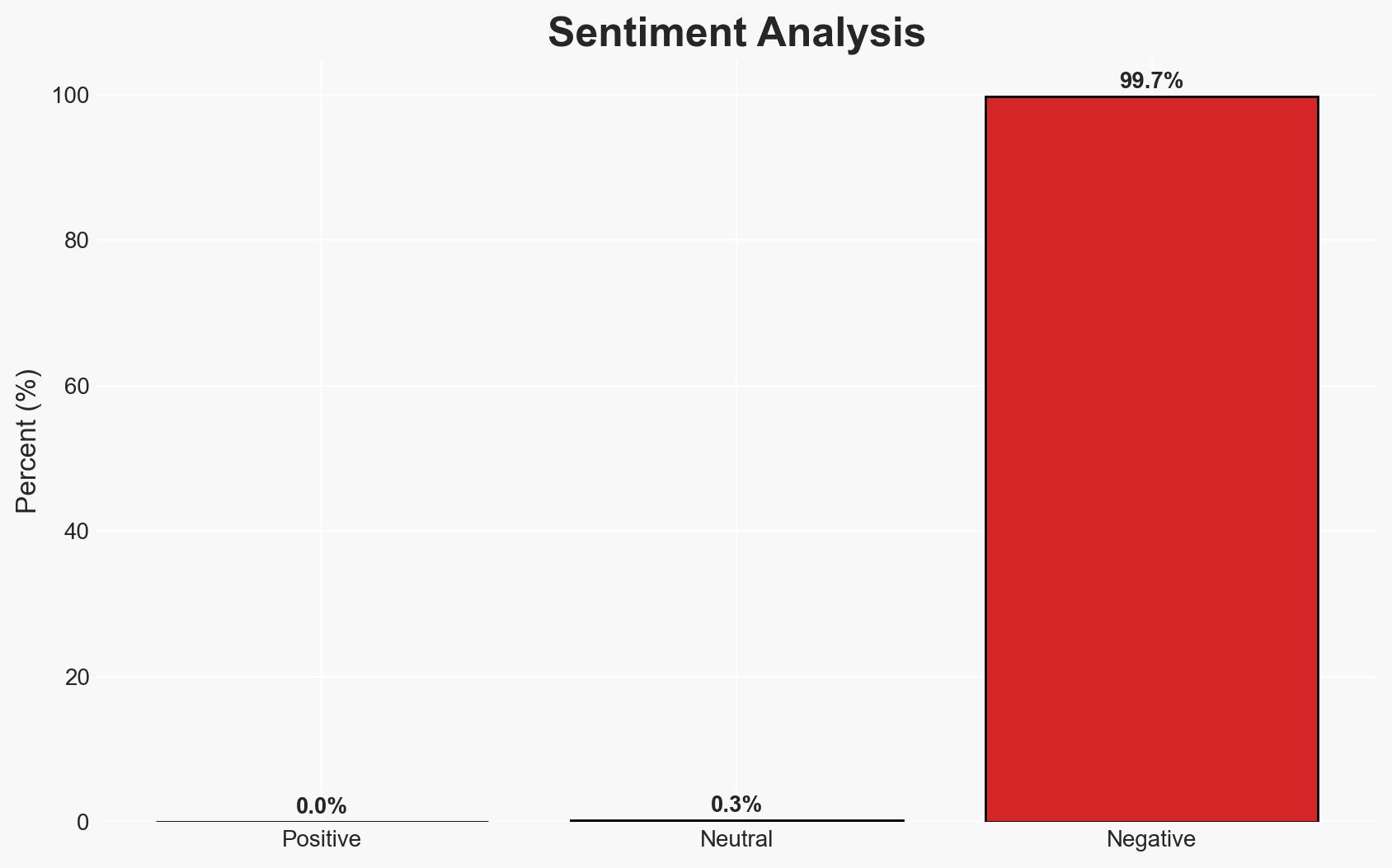
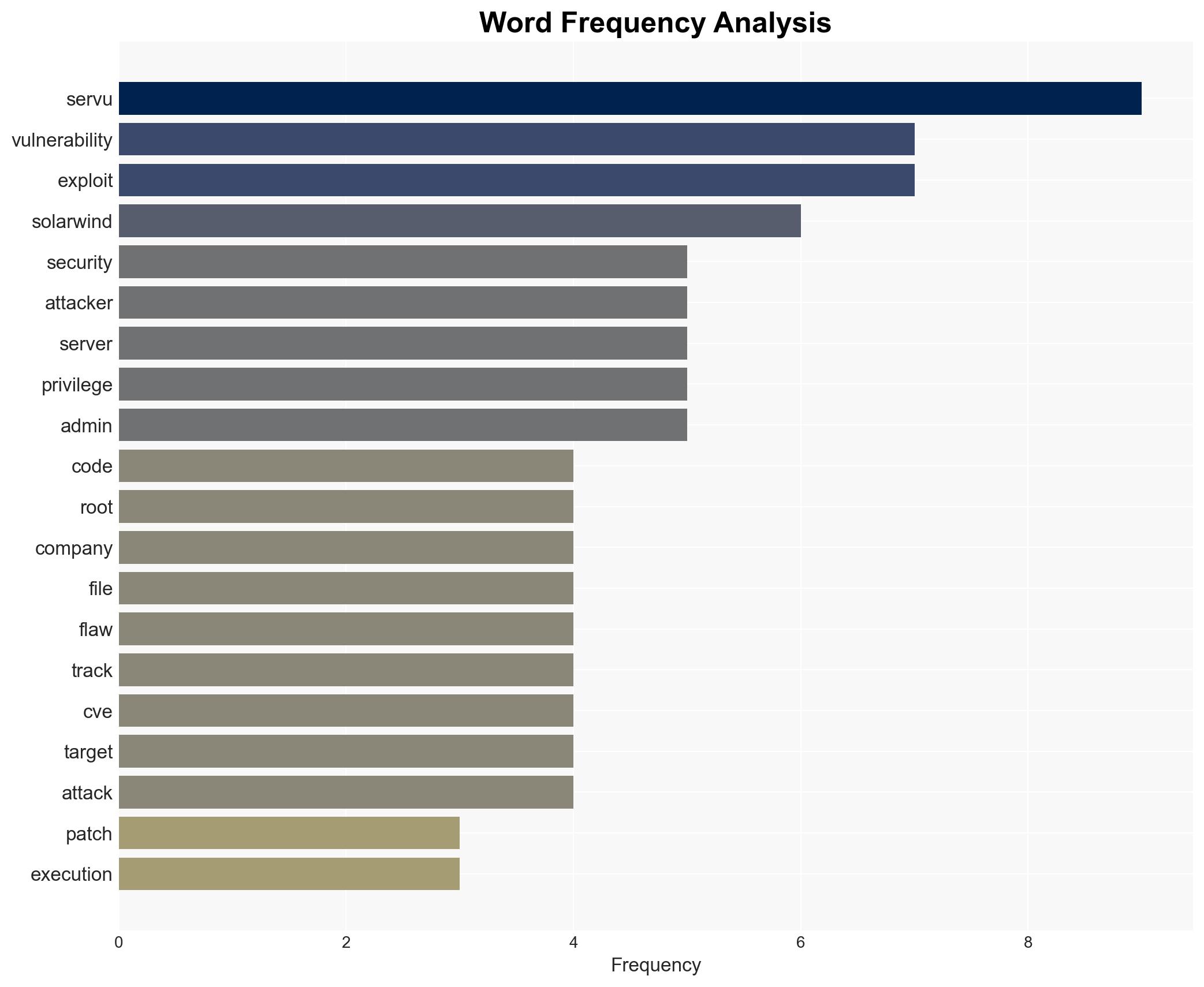
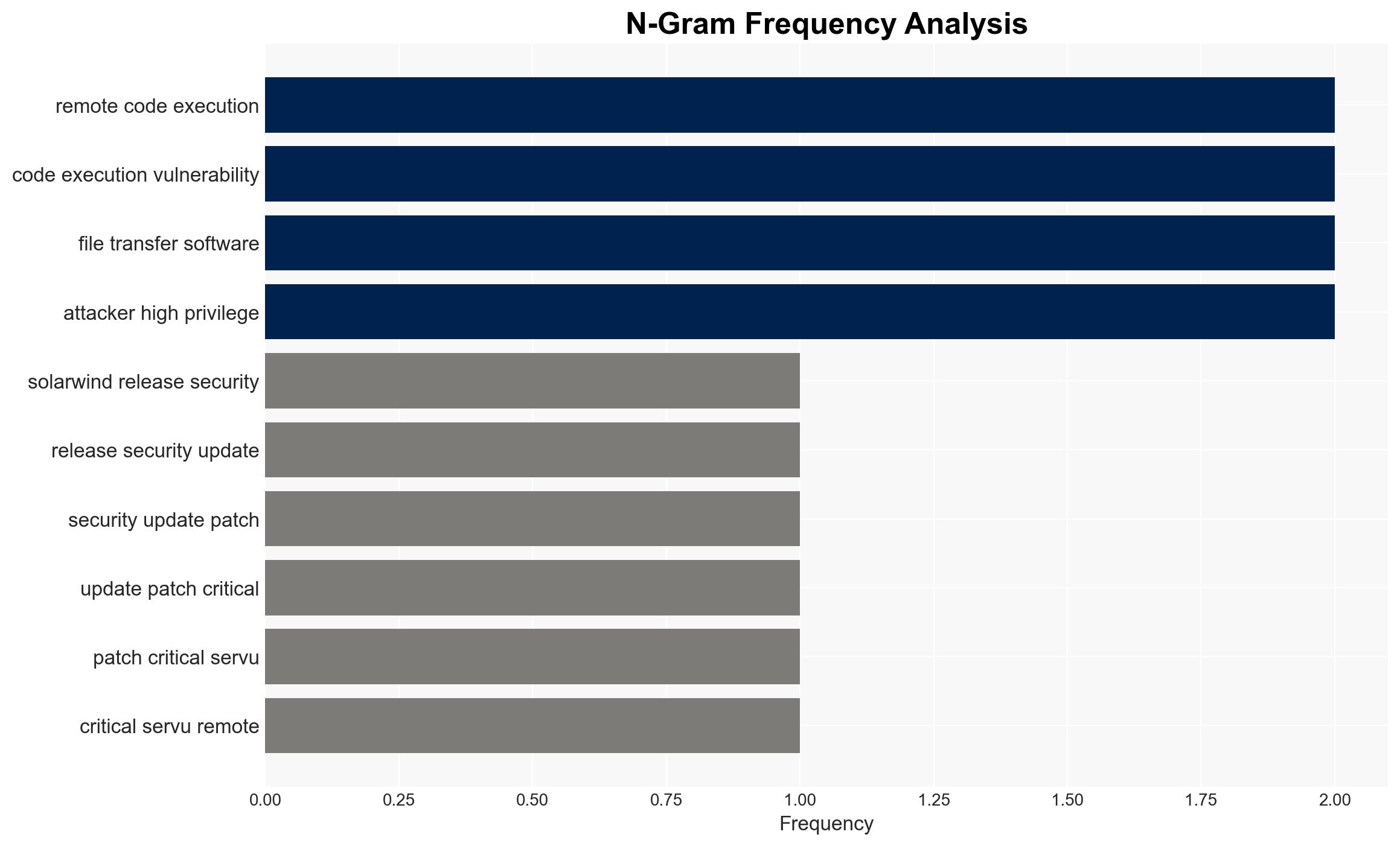
SolarWinds has patched critical vulnerabilities in its Serv-U software that could allow attackers to gain root access to servers. These vulnerabilities are particularly concerning due to historical targeting by cybercriminals and state-sponsored actors. The most likely scenario involves limited exploitation due to the requirement for existing high privileges. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The vulnerabilities will be exploited primarily by sophisticated threat actors who can leverage existing access or stolen credentials. Supporting evidence includes the requirement for high privileges and historical targeting by advanced groups. Key uncertainty lies in the potential for new privilege escalation techniques.
- Hypothesis B: The vulnerabilities will remain largely unexploited due to the high privilege requirement, limiting the attack surface. This is supported by the need for existing access, but contradicted by the history of exploitation by determined actors.
- Assessment: Hypothesis A is currently better supported due to the track record of exploitation by capable actors and the potential for combining these vulnerabilities with other exploits. Indicators such as new privilege escalation methods could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Attackers will require existing high privileges; organizations will apply patches promptly; threat actors have the capability to exploit these vulnerabilities.
- Information Gaps: Details on the speed and extent of patch deployment; specific threat actor intentions and capabilities.
- Bias & Deception Risks: Potential underestimation of less sophisticated actors; reliance on vendor-reported information without independent verification.
4. Implications and Strategic Risks
The exploitation of these vulnerabilities could lead to significant data breaches and operational disruptions, particularly in sectors with high-value data. The situation could evolve with the discovery of new exploitation techniques or increased targeting by state actors.
- Political / Geopolitical: Increased tensions if state-sponsored actors are implicated, particularly involving U.S. and China relations.
- Security / Counter-Terrorism: Heightened alert for potential data theft and ransomware attacks, impacting critical infrastructure.
- Cyber / Information Space: Potential for widespread exploitation if privilege escalation methods are developed; increased focus on securing file transfer systems.
- Economic / Social: Possible financial losses for affected companies and erosion of trust in digital infrastructure.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urgently apply patches, monitor for unusual access patterns, and review access controls.
- Medium-Term Posture (1–12 months): Enhance detection capabilities for privilege escalation attempts, and strengthen partnerships for threat intelligence sharing.
- Scenario Outlook:
- Best: Rapid patch adoption prevents significant exploitation.
- Worst: New privilege escalation techniques lead to widespread breaches.
- Most-Likely: Limited exploitation by sophisticated actors, with isolated incidents of data theft.
6. Key Individuals and Entities
- SolarWinds
- Clop gang
- DEV-0322 (China-based hackers)
- U.S. Cybersecurity and Infrastructure Security Agency (CISA)
- Rapid7
- GreyNoise
7. Thematic Tags
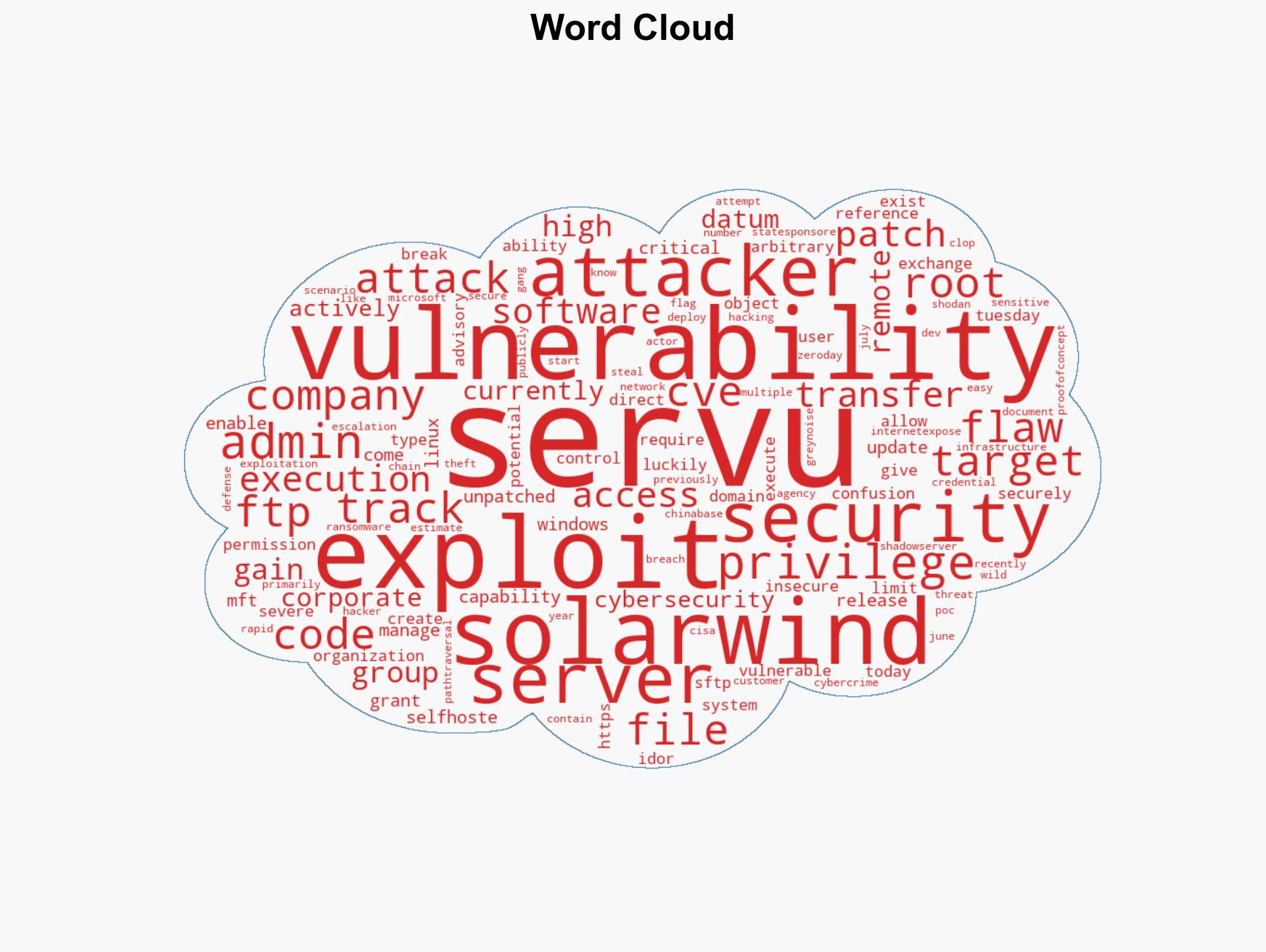
cybersecurity, vulnerability management, state-sponsored attacks, data breach, ransomware, digital infrastructure, threat intelligence
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us