Strengthening Global Mobile Networks: Addressing Security Vulnerabilities in Legacy Infrastructure
Published on: 2026-03-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: From Core to Edge Building Secure Always-On Infrastructure for Global Mobile Networks
1. BLUF (Bottom Line Up Front)
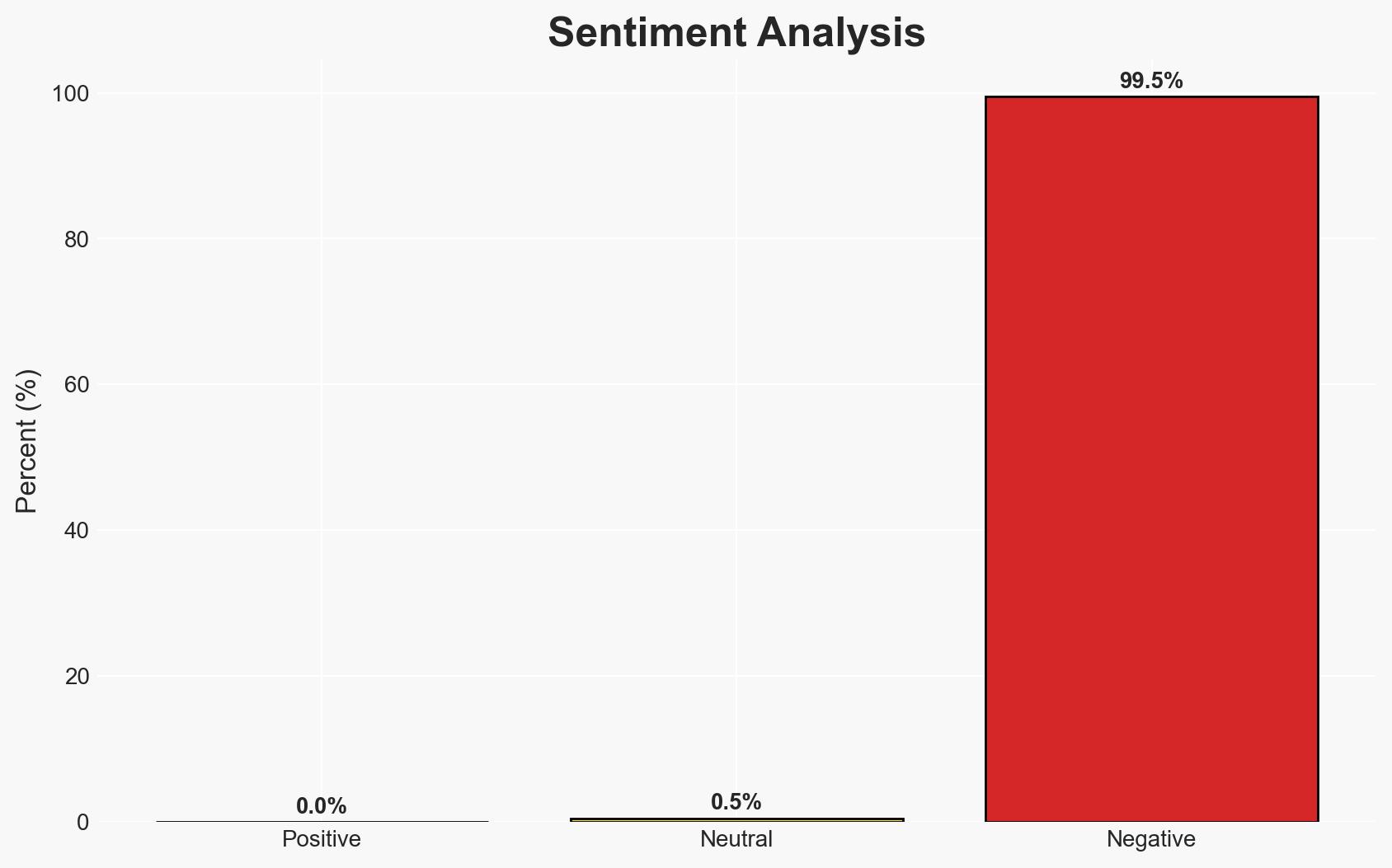
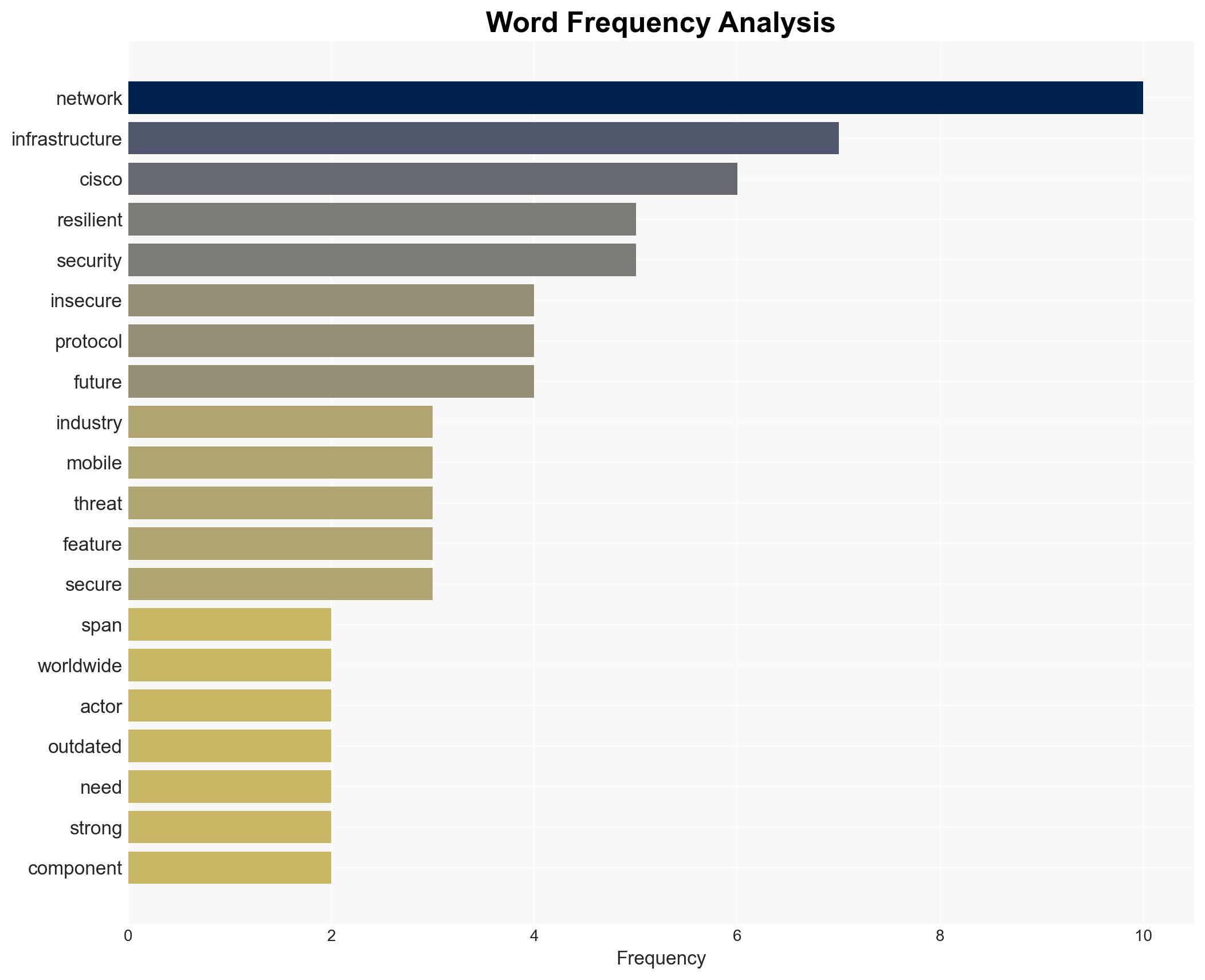
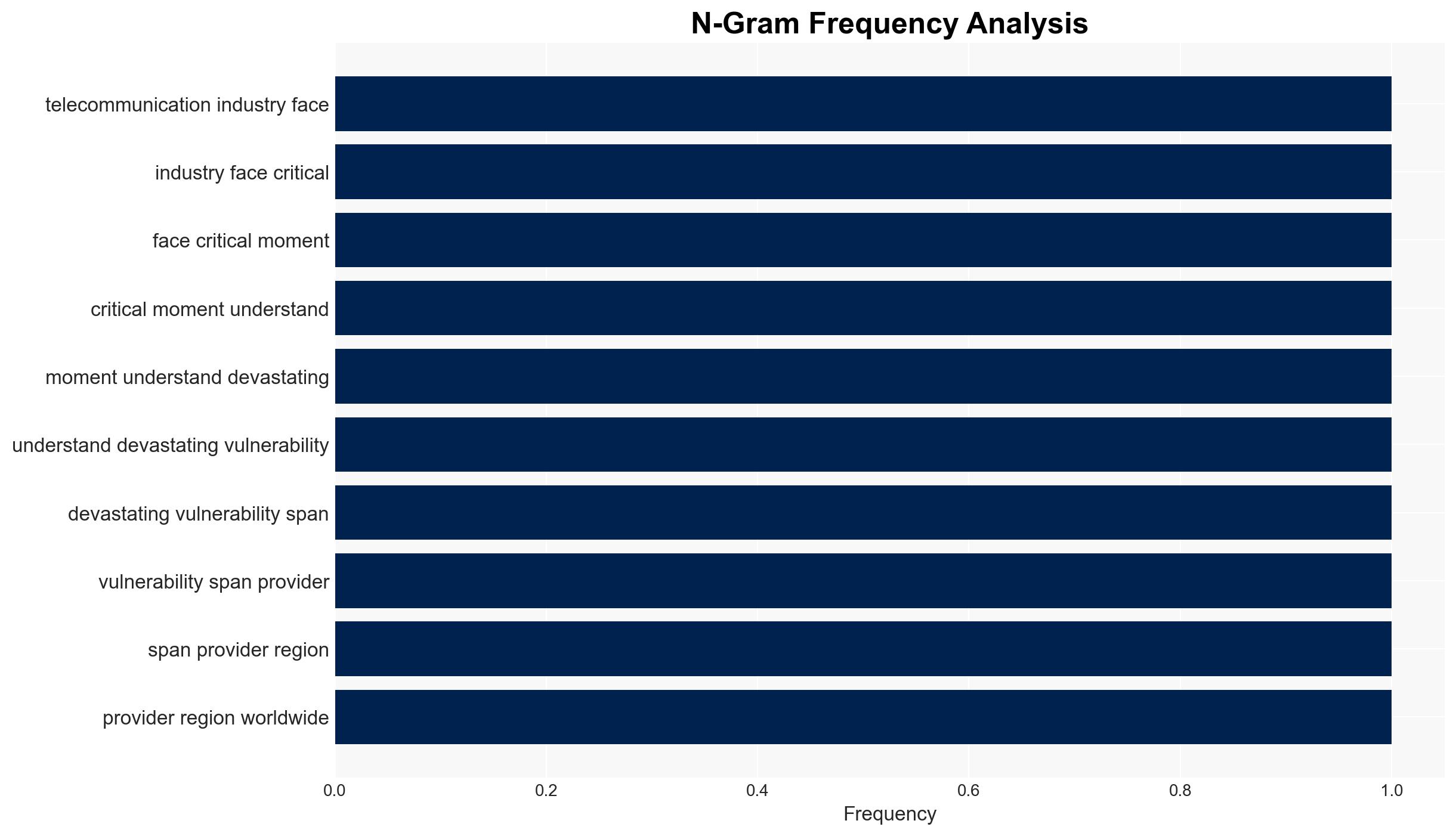
The telecommunications industry faces significant security vulnerabilities due to outdated infrastructure and insecure protocols. Cisco’s initiative to enhance network resilience is a critical step towards mitigating these risks. The most likely hypothesis is that industry-wide adoption of similar measures will improve global network security. Overall confidence in this assessment is moderate, given the reliance on industry cooperation and execution.
2. Competing Hypotheses
- Hypothesis A: The telecommunications industry will successfully implement resilient infrastructure improvements, significantly reducing vulnerabilities. Evidence includes Cisco’s proactive measures and the industry’s recognition of the need for change. Uncertainties involve the pace of adoption and integration across diverse global networks.
- Hypothesis B: Efforts to enhance network security will be insufficient or unevenly implemented, leaving critical vulnerabilities unaddressed. This is supported by historical challenges in coordinating industry-wide changes and the potential for resistance due to cost and complexity.
- Assessment: Hypothesis A is currently better supported due to Cisco’s leadership and the increasing awareness of security risks. Key indicators that could shift this judgment include widespread industry adoption of similar measures and evidence of reduced vulnerabilities.
3. Key Assumptions and Red Flags
- Assumptions: The industry will prioritize security over cost; Cisco’s measures will be effective; global cooperation will be achieved; technological advancements will support security improvements; regulatory frameworks will align with security needs.
- Information Gaps: Specific timelines for industry-wide adoption; detailed impact assessments of Cisco’s measures; data on current vulnerability levels across networks.
- Bias & Deception Risks: Potential over-reliance on vendor-provided information; confirmation bias towards successful implementation; possible underestimation of adversary capabilities.
4. Implications and Strategic Risks
The development of resilient telecommunications infrastructure could significantly alter the security landscape, affecting multiple domains over time.
- Political / Geopolitical: Enhanced network security could reduce state-sponsored cyber operations and influence geopolitical stability.
- Security / Counter-Terrorism: Improved infrastructure may decrease the likelihood of cyber-terrorist attacks on critical networks.
- Cyber / Information Space: Strengthened defenses could deter cyber espionage and data breaches, enhancing overall cyber hygiene.
- Economic / Social: Increased security may boost consumer confidence and economic stability, though initial costs could strain smaller providers.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive audit of current network vulnerabilities; engage with industry leaders to promote best practices; monitor for emerging threats.
- Medium-Term Posture (1–12 months): Develop partnerships for shared threat intelligence; invest in workforce training for new security protocols; advocate for supportive regulatory policies.
- Scenario Outlook:
- Best: Industry-wide adoption leads to a significant reduction in vulnerabilities, with minimal disruption.
- Worst: Fragmented implementation results in persistent vulnerabilities, exploited by adversaries.
- Most-Likely: Gradual improvement in security posture, with ongoing challenges in coordination and resource allocation.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
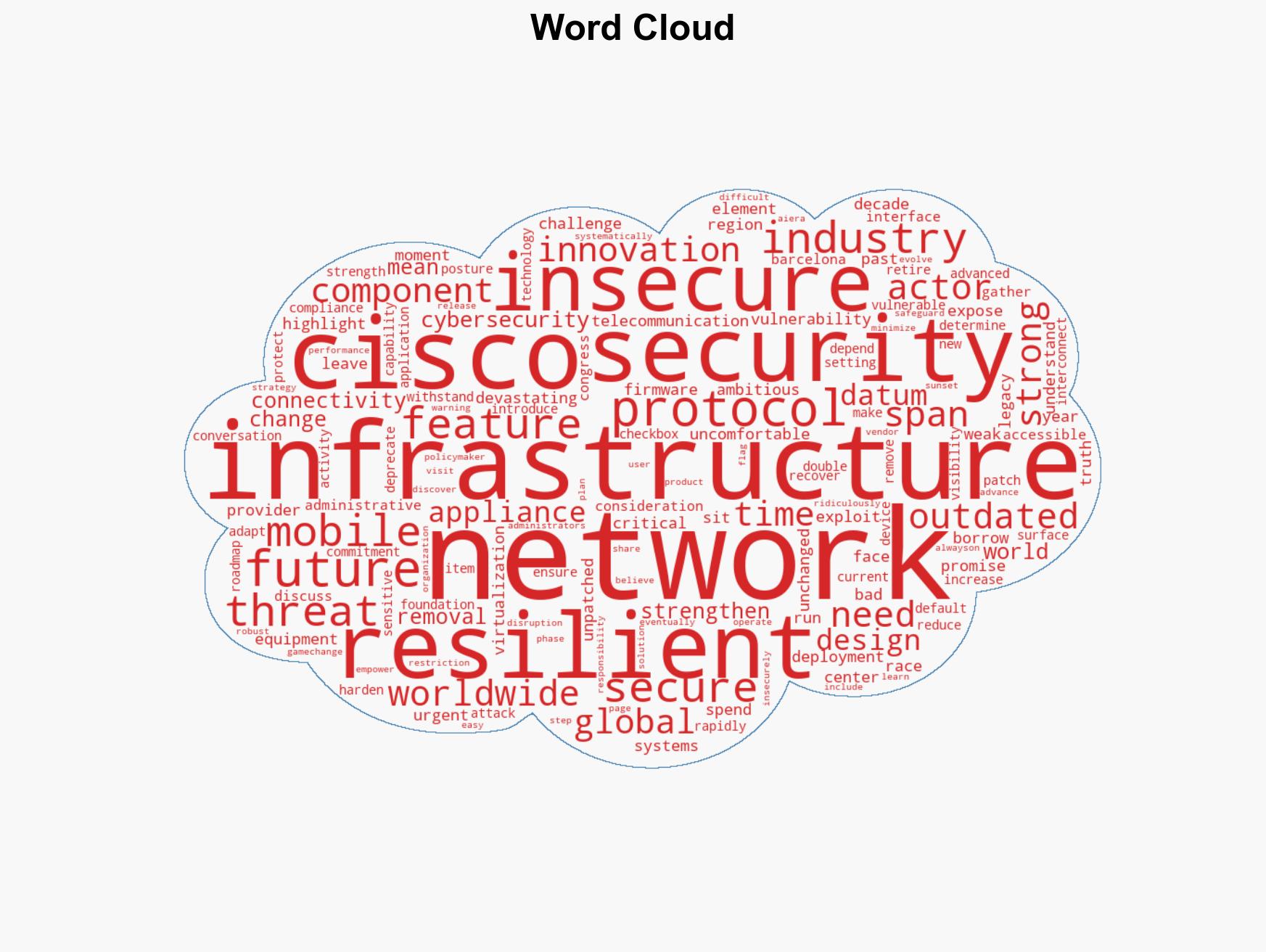
cybersecurity, telecommunications security, network resilience, cyber vulnerabilities, infrastructure modernization, global cooperation, Cisco, mobile networks
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us