Stryker Corporation resumes full operations after recovering from significant cyberattack disruption
Published on: 2026-04-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Medtech giant Stryker fully operational after data-wiping attack
1. BLUF (Bottom Line Up Front)
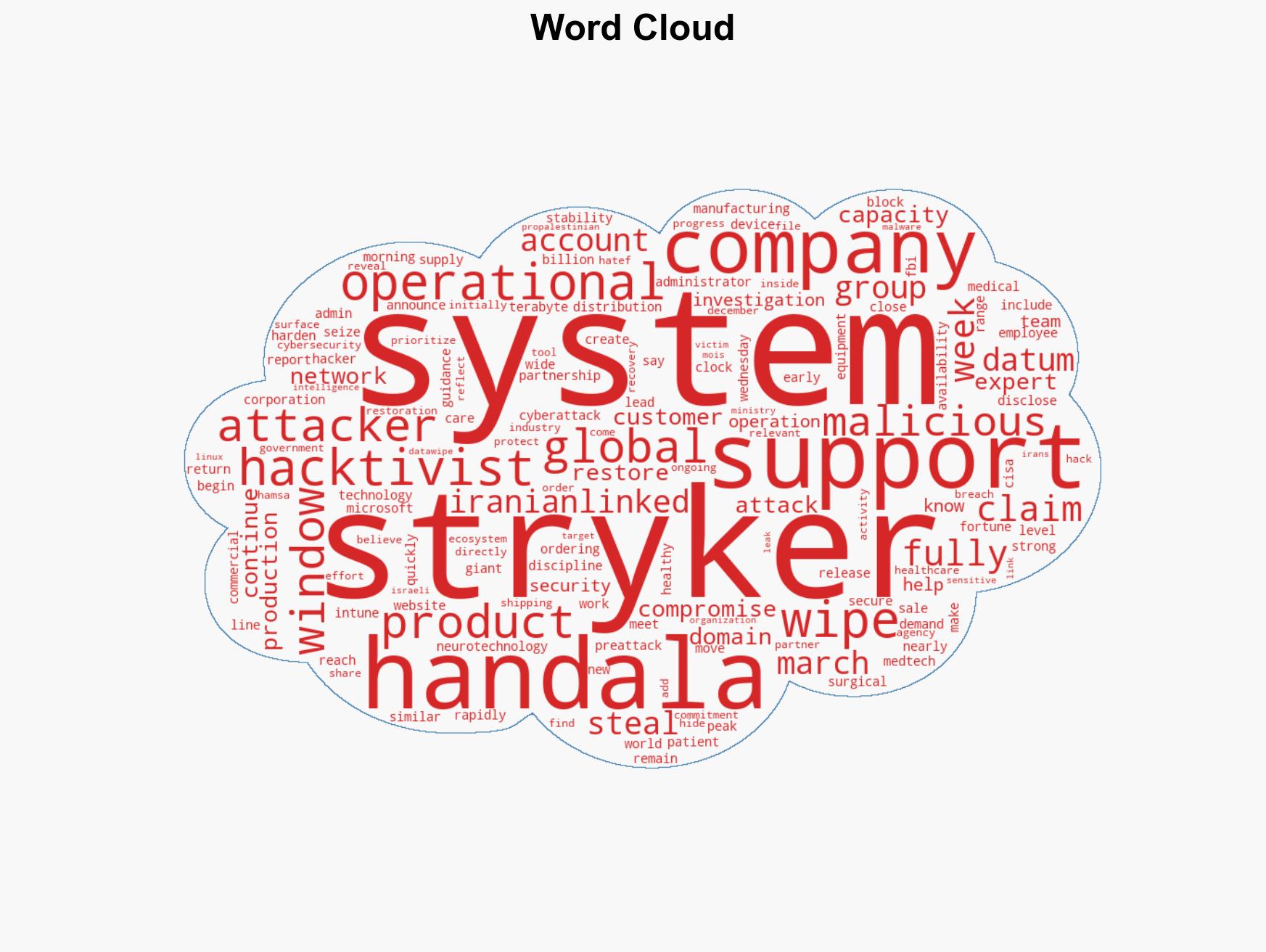
Stryker Corporation has restored operations following a significant cyberattack attributed to the Iranian-linked Handala hacktivist group. The attack involved data wiping and potential data theft, impacting Stryker’s global operations. The most likely hypothesis is that the attack was politically motivated, targeting a high-profile Western corporation to demonstrate capability and influence. Overall confidence in this assessment is moderate, given the limited direct evidence of the attackers’ ultimate objectives.
2. Competing Hypotheses
- Hypothesis A: The attack was primarily politically motivated, aimed at demonstrating cyber capabilities and exerting influence against Western entities. This is supported by the group’s known affiliations and past targets. However, the lack of direct evidence linking the attack to specific geopolitical events introduces uncertainty.
- Hypothesis B: The attack was financially motivated, with the data theft intended for ransom or resale. The claim of stealing 50 terabytes of data supports this, but the absence of ransom demands or evidence of data resale contradicts this hypothesis.
- Assessment: Hypothesis A is currently better supported due to the group’s known political motivations and lack of financial follow-up actions. Indicators such as future attacks on similar targets or political statements by the group could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The Handala group is acting with some level of state support or approval; Stryker’s public statements accurately reflect their operational status; the cyberattack was intended to cause disruption rather than financial gain.
- Information Gaps: Details on the specific data stolen and its current status; confirmation of the attackers’ ultimate objectives; technical specifics of the malware used.
- Bias & Deception Risks: Potential bias in attributing the attack solely based on the group’s claims; risk of deception in the attackers’ stated motivations and claimed data theft.
4. Implications and Strategic Risks
This development highlights vulnerabilities in critical infrastructure and the potential for politically motivated cyberattacks to disrupt global operations. The situation could evolve with further attacks or escalations in geopolitical tensions.
- Political / Geopolitical: Potential for increased tensions between Iran-linked entities and Western corporations, possibly leading to retaliatory measures.
- Security / Counter-Terrorism: Heightened alert for similar attacks on other high-profile targets, necessitating increased cybersecurity measures.
- Cyber / Information Space: Increased focus on securing Windows domains and related infrastructure, with potential for new attack vectors to emerge.
- Economic / Social: Short-term disruptions in medical technology supply chains, with potential long-term impacts on trust in corporate cybersecurity resilience.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of cyber threats, particularly from politically motivated groups; engage with cybersecurity experts to review and strengthen defenses.
- Medium-Term Posture (1–12 months): Develop partnerships with government agencies for threat intelligence sharing; invest in advanced cybersecurity training and infrastructure resilience.
- Scenario Outlook:
- Best Case: Enhanced security measures prevent further incidents, and geopolitical tensions de-escalate.
- Worst Case: Continued attacks lead to significant operational disruptions and geopolitical conflict.
- Most Likely: Sporadic cyber incidents continue, prompting ongoing adjustments in cybersecurity strategies.
6. Key Individuals and Entities
- Stryker Corporation
- Handala hacktivist group
- Iran’s Ministry of Intelligence and Security (MOIS)
- CISA (Cybersecurity and Infrastructure Security Agency)
- Microsoft
- FBI
7. Thematic Tags
cybersecurity, hacktivism, Iran, medical technology, geopolitical tensions, data breach, operational resilience
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us