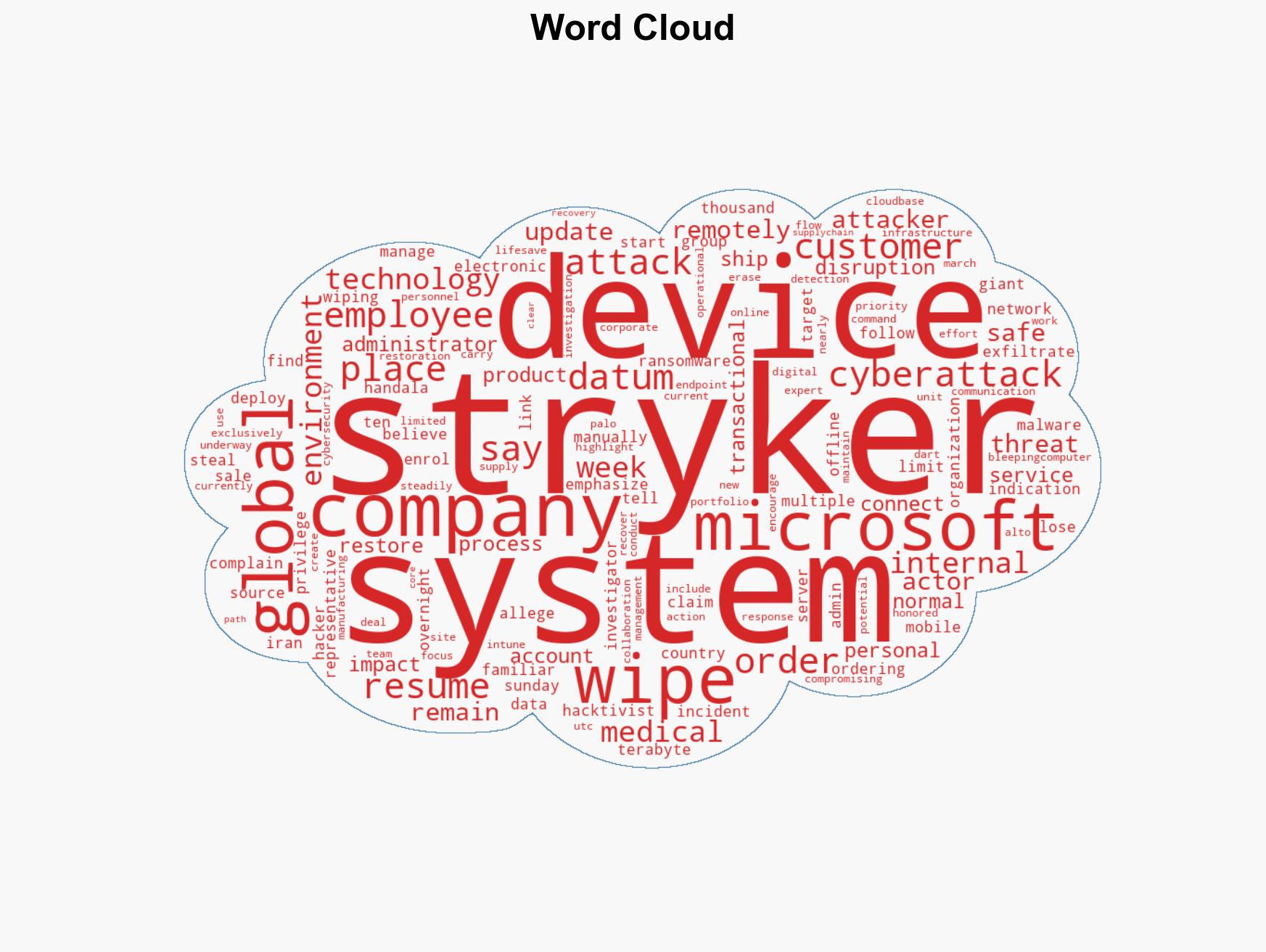
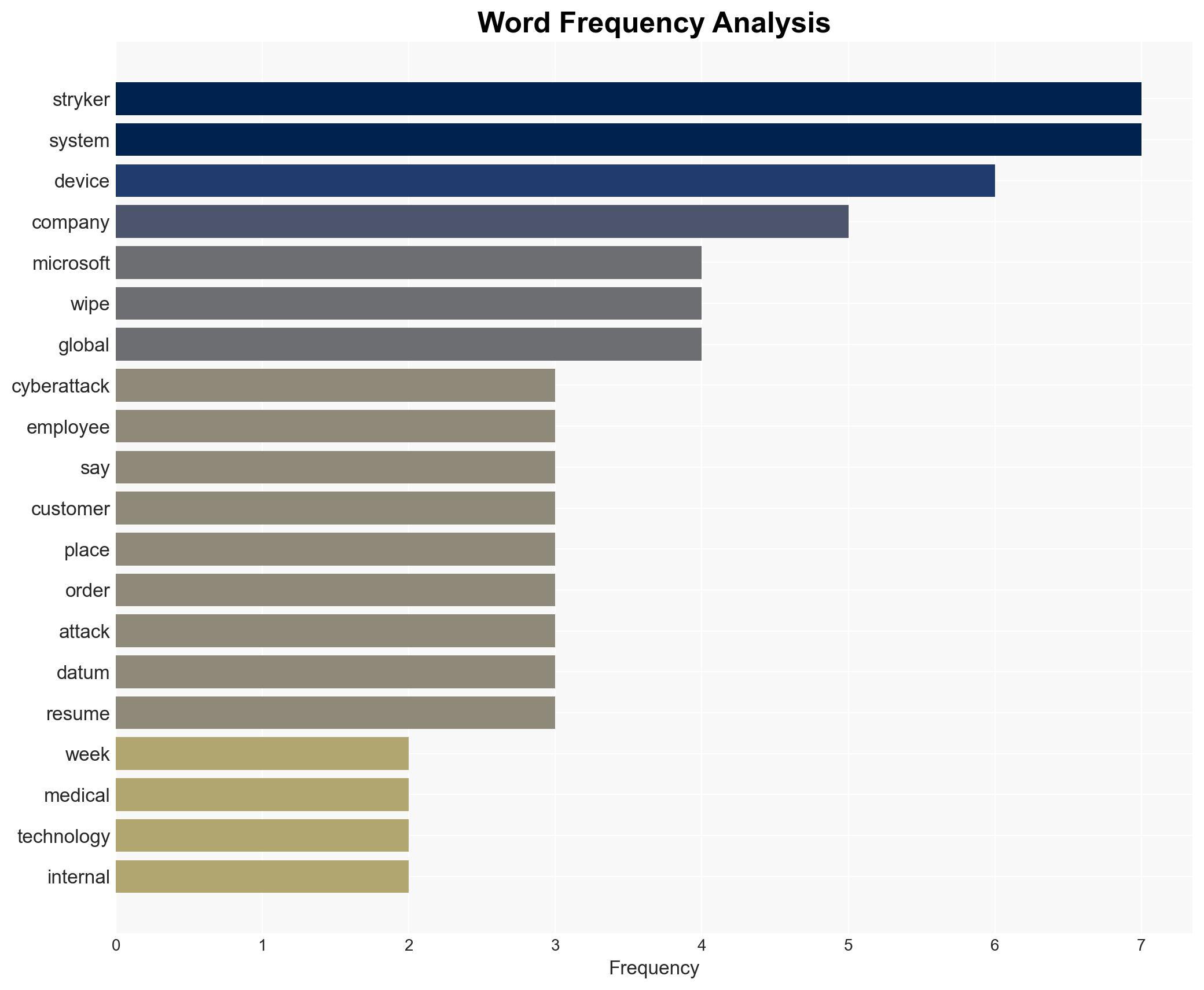
Stryker Cyberattack Erases Thousands of Devices Without Malware, Disrupting Operations and Customer Orders
Published on: 2026-03-16
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Stryker attack wiped tens of thousands of devices no malware needed
1. BLUF (Bottom Line Up Front)
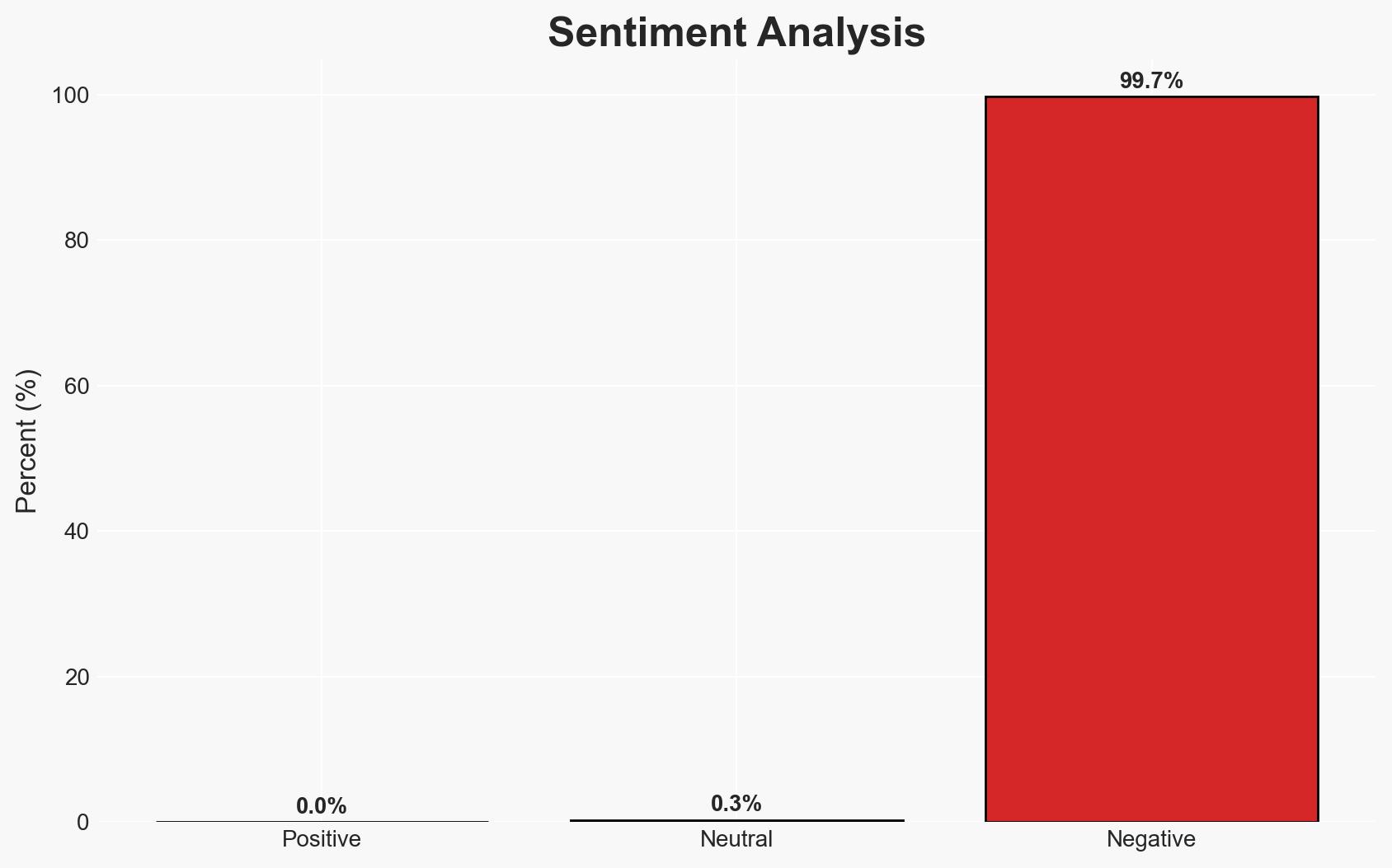
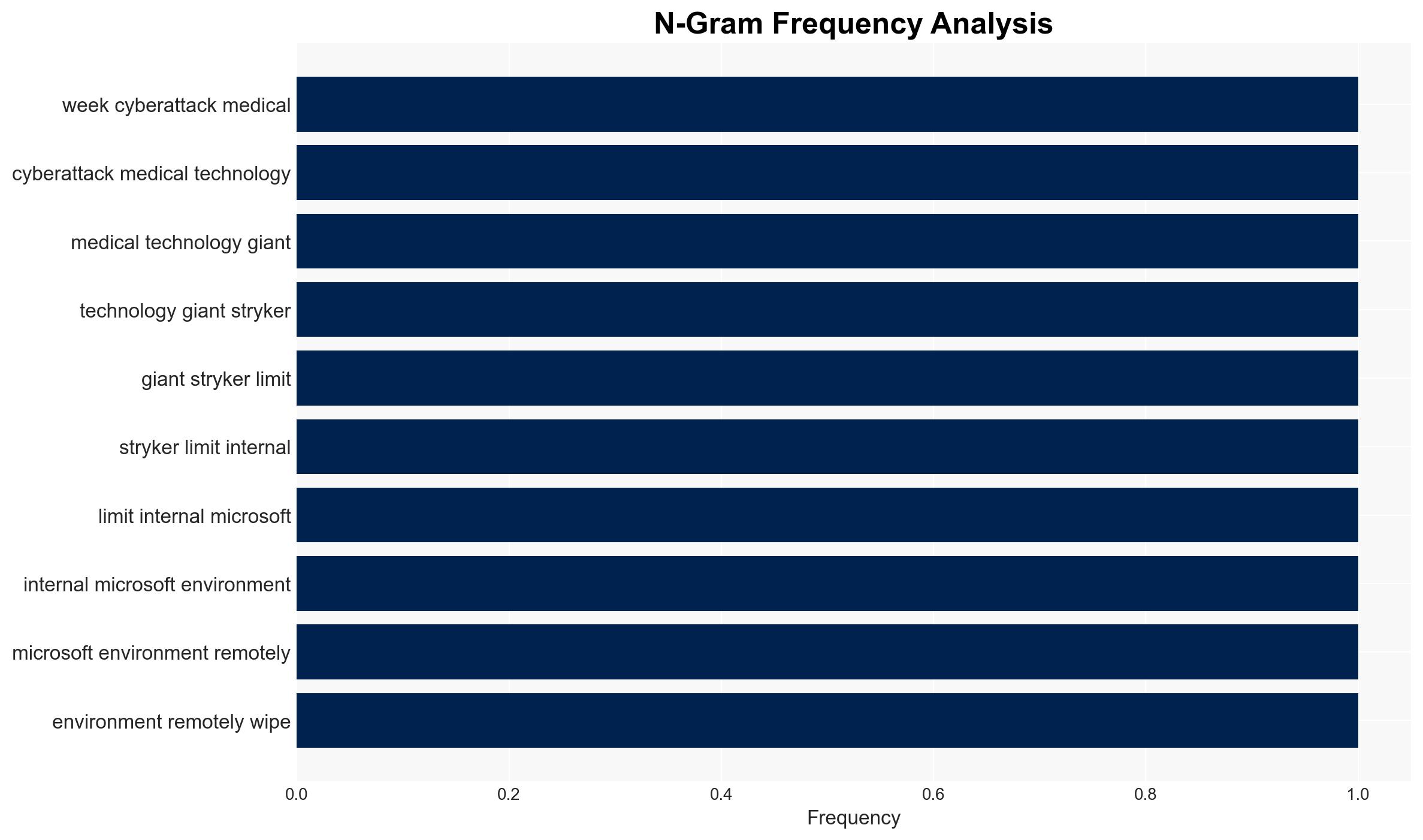
The cyberattack on Stryker, attributed to the Handala hacktivist group, resulted in the wiping of tens of thousands of devices without malware use, affecting internal operations but not medical products. The attack exploited administrative privileges in Stryker’s Microsoft environment. Current assessment supports the hypothesis of a politically motivated attack rather than a financially driven one, with moderate confidence due to limited evidence of data exfiltration.
2. Competing Hypotheses
- Hypothesis A: The attack was politically motivated, conducted by the Handala hacktivist group linked to Iran, aiming to disrupt Stryker’s operations without financial gain. Supporting evidence includes the lack of ransomware or data exfiltration and the group’s claim of responsibility. Key uncertainties include the true identity and motivations of the attackers.
- Hypothesis B: The attack was a financially motivated operation disguised as hacktivism, intending to extort Stryker or its stakeholders. Contradicting evidence includes the absence of ransom demands and the non-deployment of malware, which is atypical for financially motivated attacks.
- Assessment: Hypothesis A is currently better supported due to the absence of financial indicators and the group’s claim of responsibility. Indicators that could shift this judgment include evidence of financial transactions or ransom demands.
3. Key Assumptions and Red Flags
- Assumptions: The Handala group is accurately linked to Iran; the attack’s primary goal was disruption rather than financial gain; Stryker’s medical devices remain unaffected by the attack.
- Information Gaps: The full extent of the attacker’s access and potential undiscovered data breaches; motivations and affiliations of the Handala group beyond current attributions.
- Bias & Deception Risks: Potential bias in attributing the attack to Iran-linked groups without conclusive evidence; risk of deception by the attackers in claiming responsibility to mislead investigators.
4. Implications and Strategic Risks
This development could lead to increased scrutiny of corporate cybersecurity measures and potential geopolitical tensions if Iran’s involvement is confirmed. The incident highlights vulnerabilities in cloud-based management systems.
- Political / Geopolitical: Potential diplomatic repercussions if state sponsorship is confirmed, affecting Iran’s international relations.
- Security / Counter-Terrorism: Increased vigilance required for similar attacks on critical infrastructure and corporate environments.
- Cyber / Information Space: Emphasizes the need for robust access controls and monitoring of administrative privileges in cloud services.
- Economic / Social: Disruption in Stryker’s operations may impact supply chains and customer trust, with potential economic repercussions if prolonged.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of administrative access, conduct a thorough forensic analysis to confirm no data exfiltration, and improve communication with stakeholders about recovery efforts.
- Medium-Term Posture (1–12 months): Strengthen partnerships with cybersecurity firms, invest in employee training on cyber hygiene, and review cloud security protocols.
- Scenario Outlook: Best: Full recovery with no further incidents; Worst: Discovery of data breaches leading to regulatory penalties; Most-Likely: Gradual recovery with increased cybersecurity measures.
6. Key Individuals and Entities
- Handala hacktivist group
- Stryker Corporation
- Microsoft Detection and Response Team (DART)
- Palo Alto Unit 42
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, hacktivism, cloud security, Iran, corporate security, data protection, supply chain disruption
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us