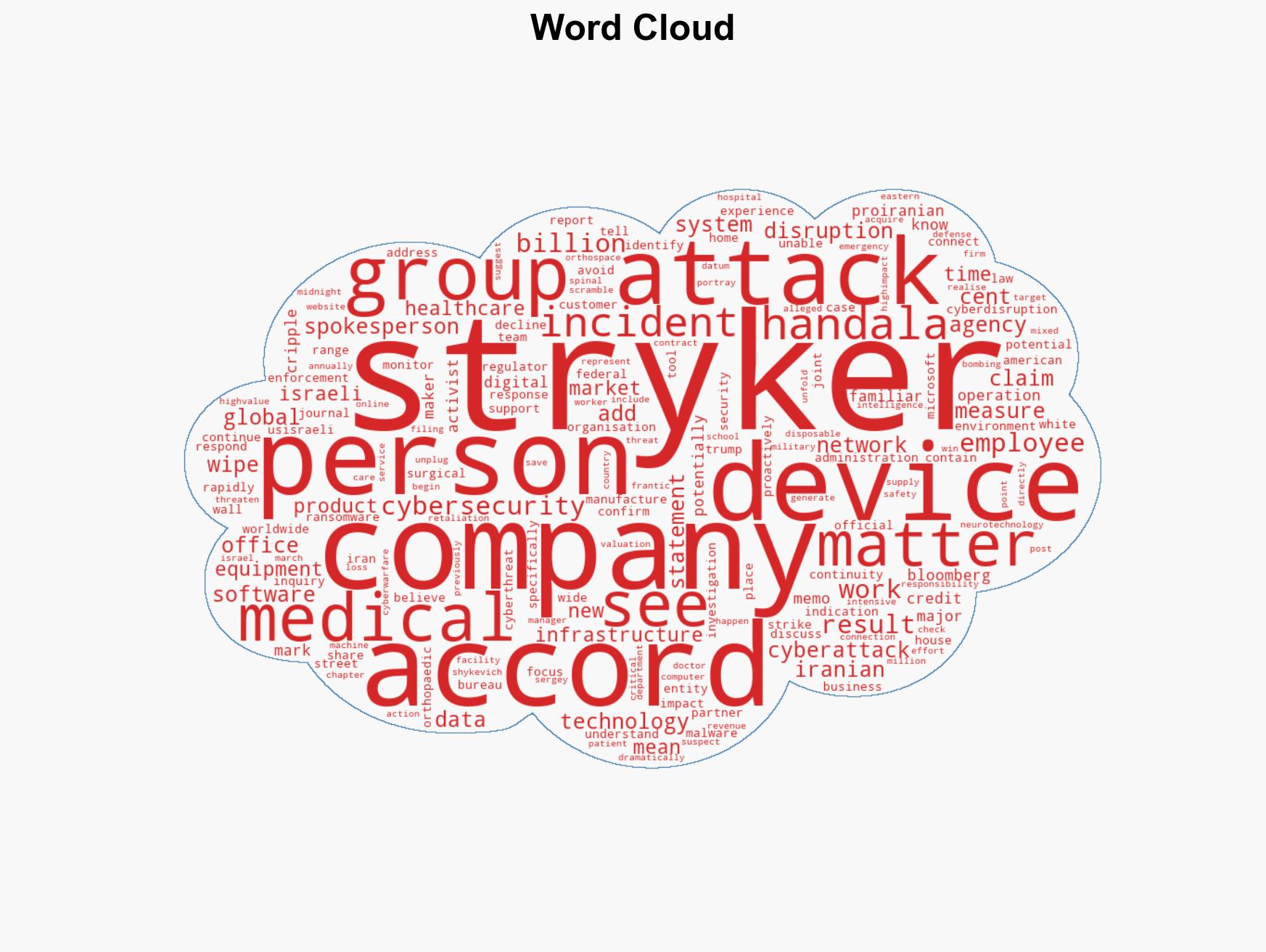
Stryker Faces Global Disruption After Cyberattack Claimed by Pro-Iran Group Handala
Published on: 2026-03-12
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: US medical tech firm Stryker hacked pro-Iran group claims credit
1. BLUF (Bottom Line Up Front)
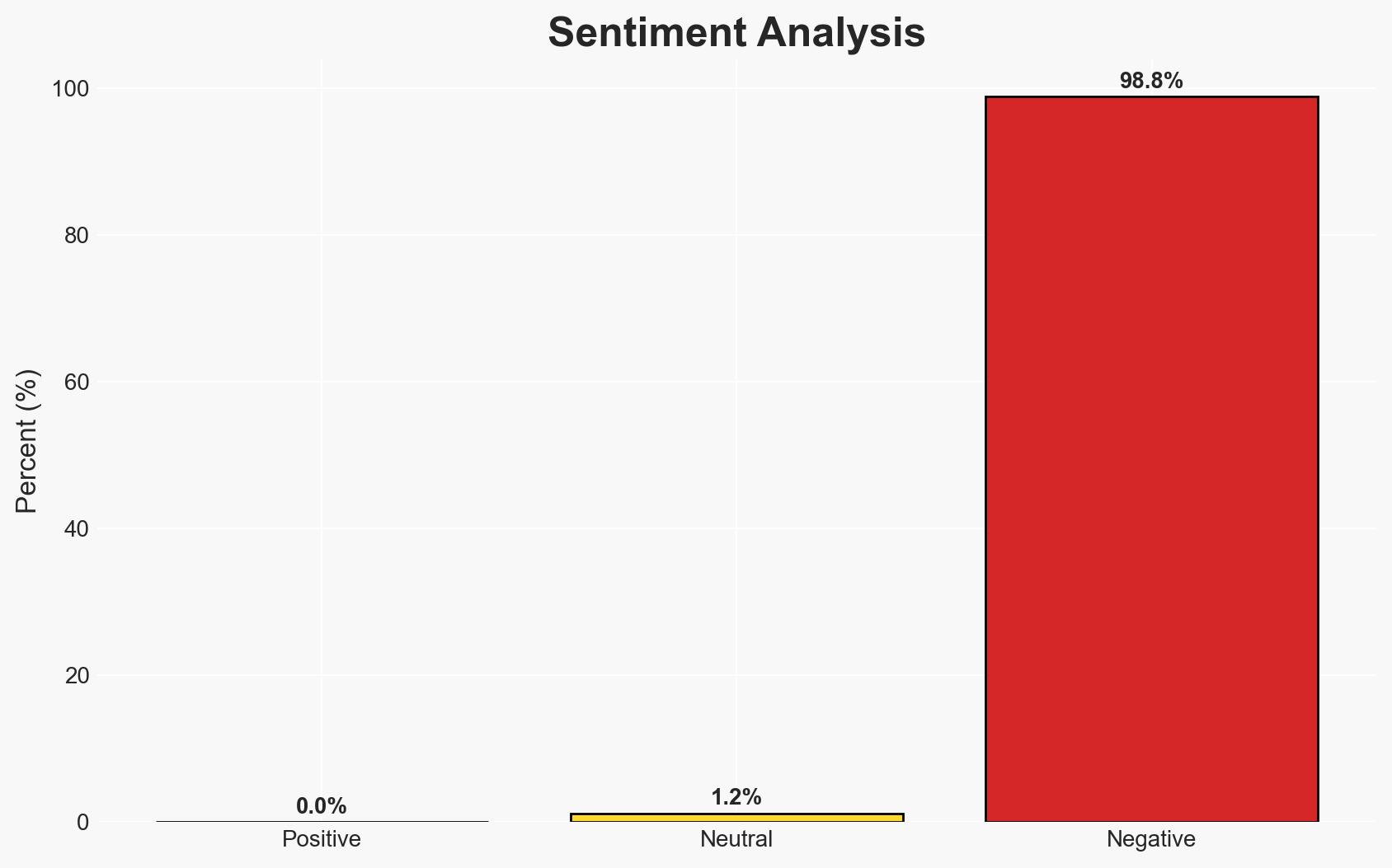
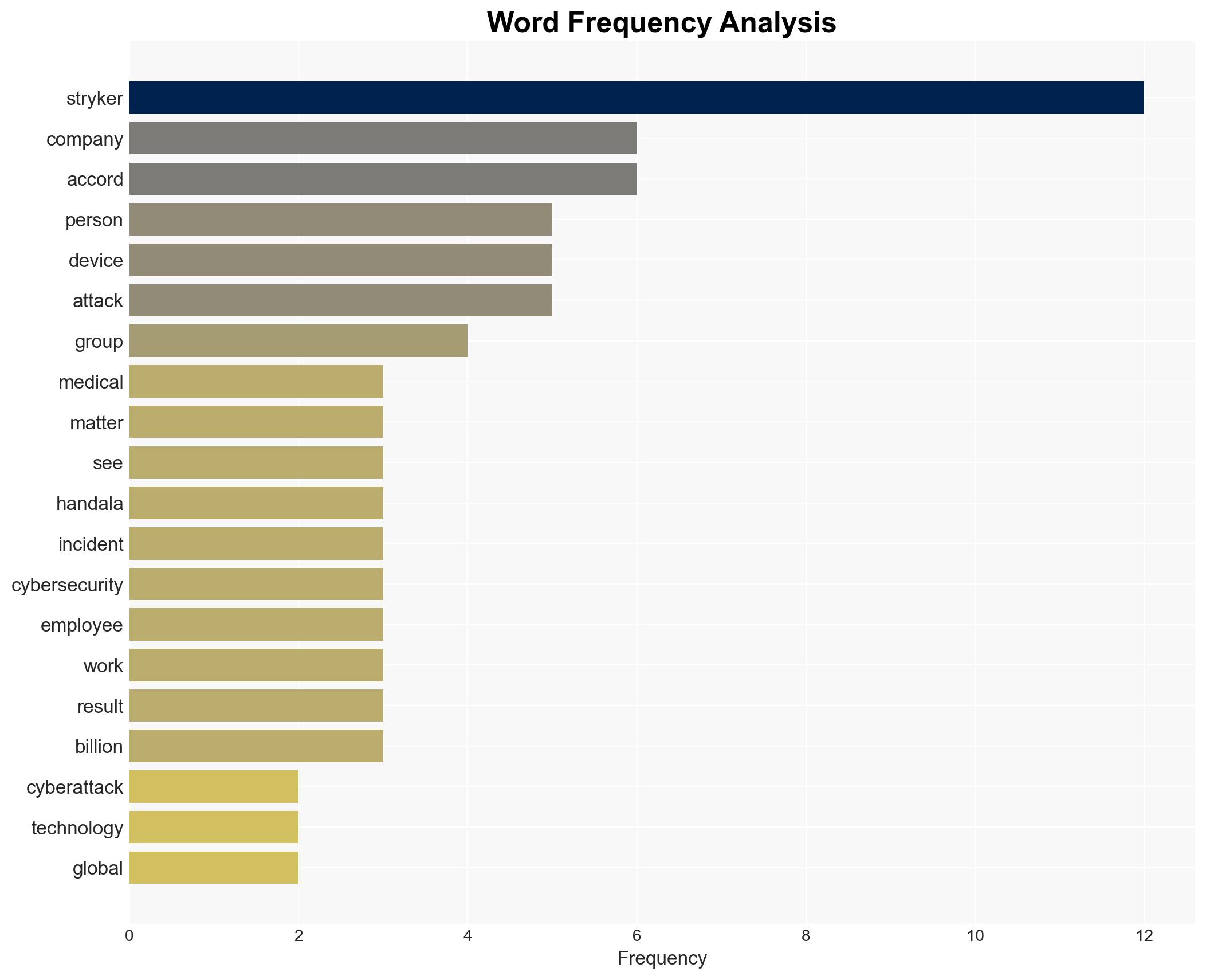
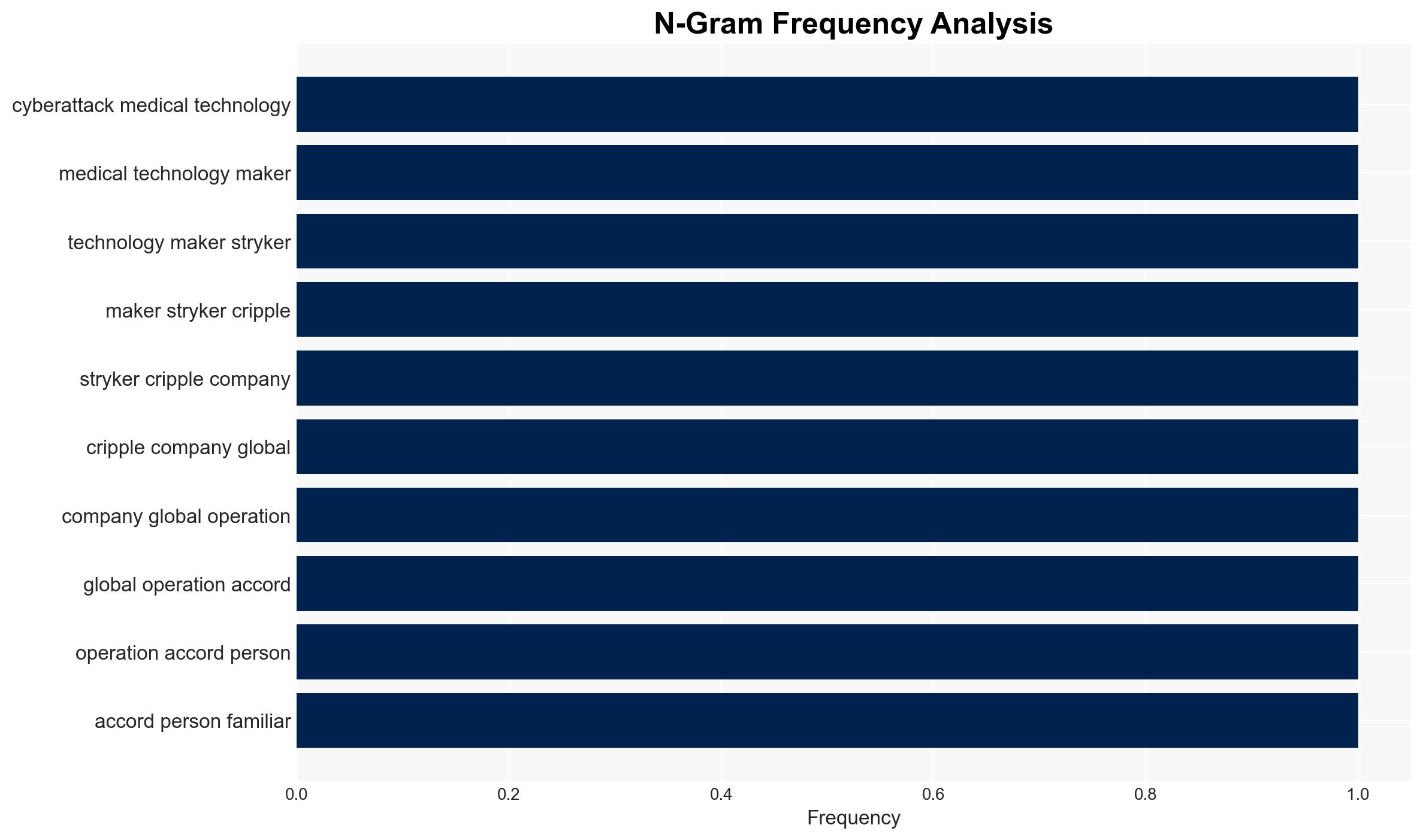
A cyberattack attributed to the pro-Iranian group Handala has disrupted Stryker’s global operations, impacting employee productivity and market valuation. The attribution remains unconfirmed by official sources, and the incident raises concerns about potential retaliatory cyber actions. Overall confidence in the attribution to Handala is moderate, pending further verification.
2. Competing Hypotheses
- Hypothesis A: The cyberattack was conducted by the pro-Iranian group Handala as a retaliatory measure for perceived US actions against Iran. This is supported by Handala’s claim of responsibility and the context of recent geopolitical tensions. However, the lack of confirmation from cybersecurity agencies and potential for false claims introduces uncertainty.
- Hypothesis B: The attack was perpetrated by an unrelated cybercriminal group seeking to exploit vulnerabilities in Stryker’s network for financial gain or disruption. The absence of ransomware or malware indicators and the lack of direct evidence linking Handala to the attack support this alternative explanation.
- Assessment: Hypothesis A is currently better supported due to the group’s public claim and the geopolitical context. Key indicators that could shift this judgment include forensic evidence linking the attack to Handala or confirmation from cybersecurity agencies.
3. Key Assumptions and Red Flags
- Assumptions: The claim by Handala is genuine; Stryker’s network vulnerabilities were exploited; geopolitical tensions influence cyber threat activities.
- Information Gaps: Lack of forensic evidence confirming the attacker’s identity; absence of detailed technical analysis of the attack vectors used.
- Bias & Deception Risks: Potential bias in attributing the attack to Handala based on geopolitical narratives; risk of deception by the claiming group to mislead attribution efforts.
4. Implications and Strategic Risks
The attack on Stryker could signal an escalation in cyber operations targeting US critical infrastructure, with potential for increased geopolitical tensions and retaliatory actions. The incident underscores vulnerabilities in healthcare-related cyber defenses.
- Political / Geopolitical: Potential for increased US-Iran tensions and retaliatory cyber actions.
- Security / Counter-Terrorism: Heightened alert for similar attacks on critical infrastructure, particularly in healthcare.
- Cyber / Information Space: Increased focus on securing healthcare networks and potential for misinformation campaigns.
- Economic / Social: Negative impact on Stryker’s market valuation and potential disruptions in healthcare services.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of Stryker’s network for further intrusions, engage with cybersecurity agencies for forensic analysis, and issue advisories to similar firms.
- Medium-Term Posture (1–12 months): Develop resilience measures, strengthen public-private cybersecurity partnerships, and invest in threat intelligence capabilities.
- Scenario Outlook:
- Best Case: Rapid attribution and mitigation prevent further incidents; geopolitical tensions de-escalate.
- Worst Case: Continued cyberattacks on critical infrastructure lead to significant disruptions and geopolitical escalation.
- Most-Likely: Ongoing cyber threats necessitate enhanced cybersecurity measures and diplomatic engagement.
6. Key Individuals and Entities
- Handala (pro-Iranian digital activist group)
- Stryker (US medical technology firm)
- Federal Bureau of Investigation (FBI)
- US Cybersecurity and Infrastructure Security Agency (CISA)
- Sergey Shykevich (Check Point Software Technologies)
7. Thematic Tags
cybersecurity, healthcare infrastructure, US-Iran relations, cyber-espionage, geopolitical tensions, critical infrastructure, cyber defense
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us