Supply Chain Breaches Lead to Increased Data Theft and Cloud Intrusions by North Korean Hackers
Published on: 2026-04-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
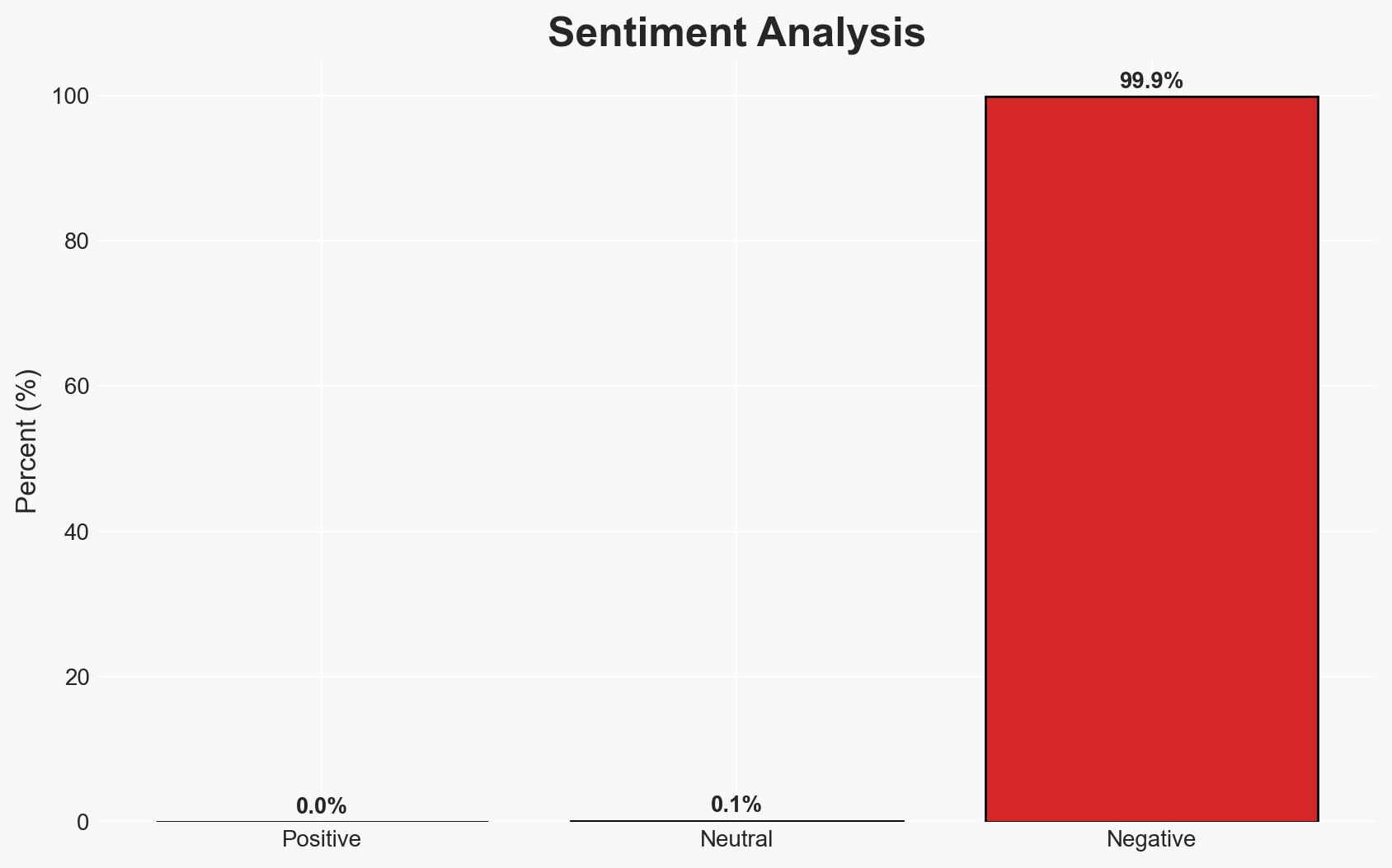
Intelligence Report: Software supply chain hacks trigger wave of intrusions data theft
1. BLUF (Bottom Line Up Front)
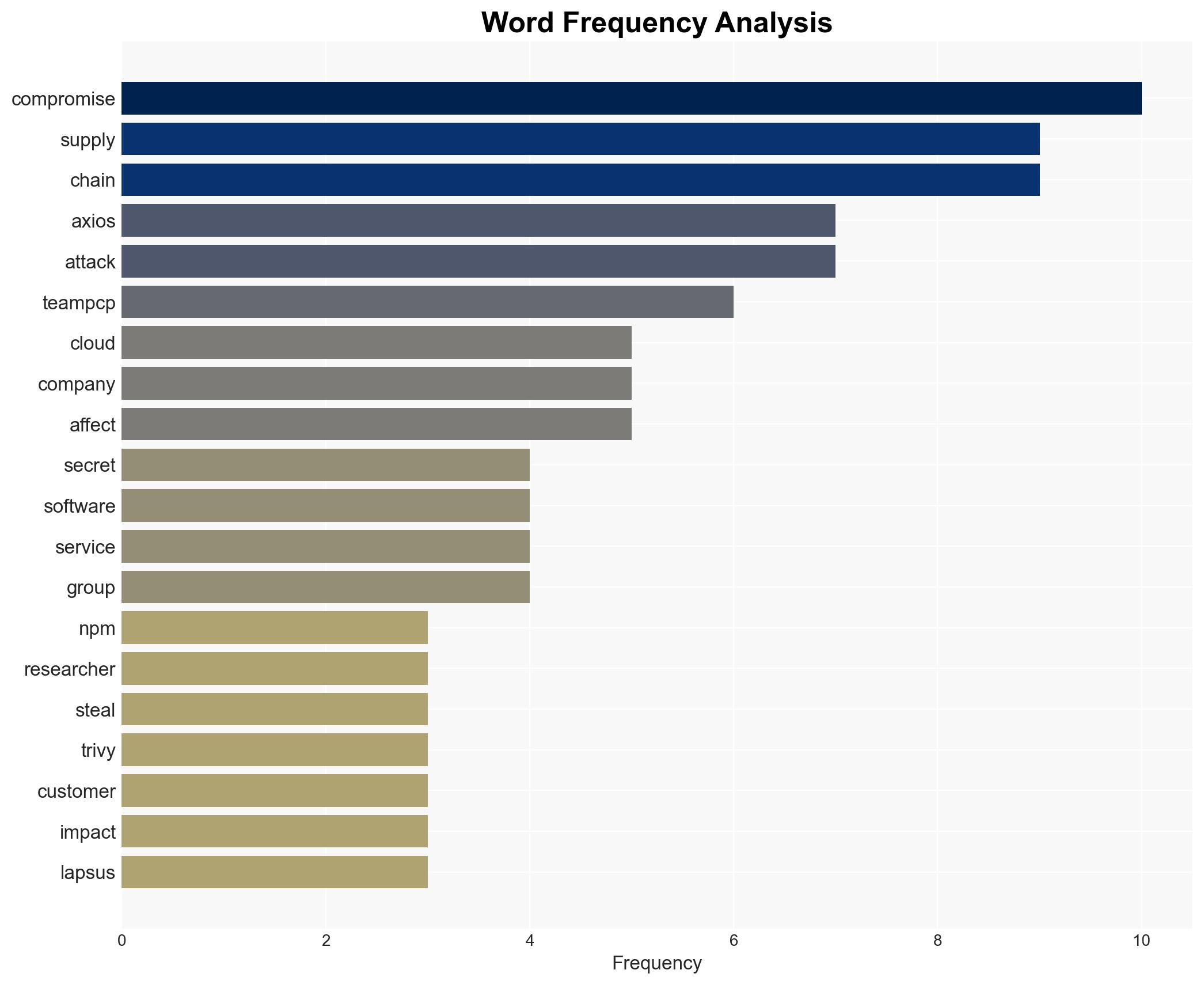
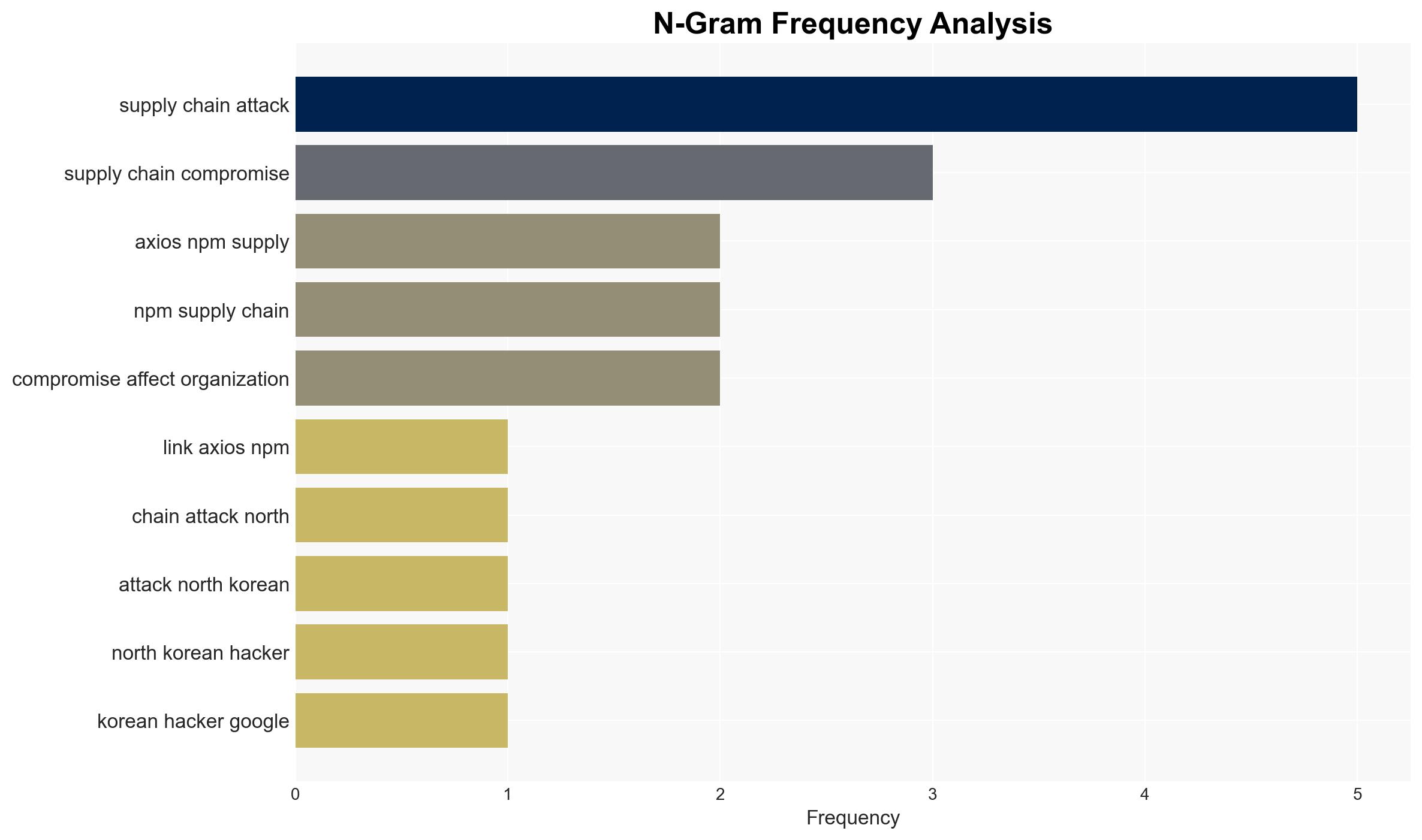
The recent wave of software supply chain attacks, attributed to North Korean hackers and TeamPCP, has led to significant data theft and potential downstream compromises. The attacks have affected a wide range of industries globally, with the potential for further cyber incidents such as ransomware and cryptocurrency theft. Overall confidence in this assessment is moderate due to existing information gaps and potential deception risks.
2. Competing Hypotheses
- Hypothesis A: The attacks are primarily orchestrated by TeamPCP and North Korean hackers, leveraging stolen secrets for cloud intrusions and data exfiltration. Evidence includes the rapid use of stolen credentials and documented connections between TeamPCP and Lapsus$. However, the possibility of secrets being shared with other groups remains uncertain.
- Hypothesis B: Multiple independent threat actors are exploiting the same vulnerabilities opportunistically, with TeamPCP and North Korean hackers being only part of a broader threat landscape. This hypothesis is less supported due to the lack of concrete evidence of other actors’ involvement.
- Assessment: Hypothesis A is currently better supported by the evidence, including the speed and coordination of the attacks, and the documented connections between involved groups. Indicators that could shift this judgment include evidence of other groups using the stolen secrets independently.
3. Key Assumptions and Red Flags
- Assumptions: The attackers have the capability to exploit stolen secrets rapidly; TeamPCP and North Korean hackers are coordinating their efforts; the affected organizations have not fully disclosed the extent of their breaches.
- Information Gaps: The full scope of the data exfiltrated; the extent of collaboration between different threat groups; the specific vulnerabilities exploited in each attack.
- Bias & Deception Risks: Potential bias in attributing attacks solely to known groups; risk of deception by threat actors to mislead attribution efforts.
4. Implications and Strategic Risks
The ongoing supply chain attacks could lead to increased geopolitical tensions, particularly if state-sponsored actors are confirmed. The security landscape may see heightened alert levels and increased demand for cybersecurity solutions.
- Political / Geopolitical: Potential for diplomatic disputes or sanctions if state involvement is confirmed.
- Security / Counter-Terrorism: Increased risk of further cyber attacks and the potential for physical security threats if critical infrastructure is compromised.
- Cyber / Information Space: Escalation in cyber warfare tactics and a likely increase in defensive cyber operations.
- Economic / Social: Possible economic disruptions due to compromised supply chains and loss of consumer trust in affected industries.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of affected supply chains, share threat intelligence with industry partners, and conduct thorough security audits of cloud environments.
- Medium-Term Posture (1–12 months): Develop resilience measures, strengthen international cybersecurity partnerships, and invest in advanced threat detection capabilities.
- Scenario Outlook:
- Best Case: Rapid containment and patching of vulnerabilities, minimizing further impact.
- Worst Case: Prolonged exploitation leading to widespread economic and security disruptions.
- Most Likely: Continued targeted attacks with gradual improvements in defensive measures.
6. Key Individuals and Entities
- TeamPCP
- Lapsus$
- North Korean hackers
- Google researchers
- Wiz
- OwnCloud
- Mercor
7. Thematic Tags
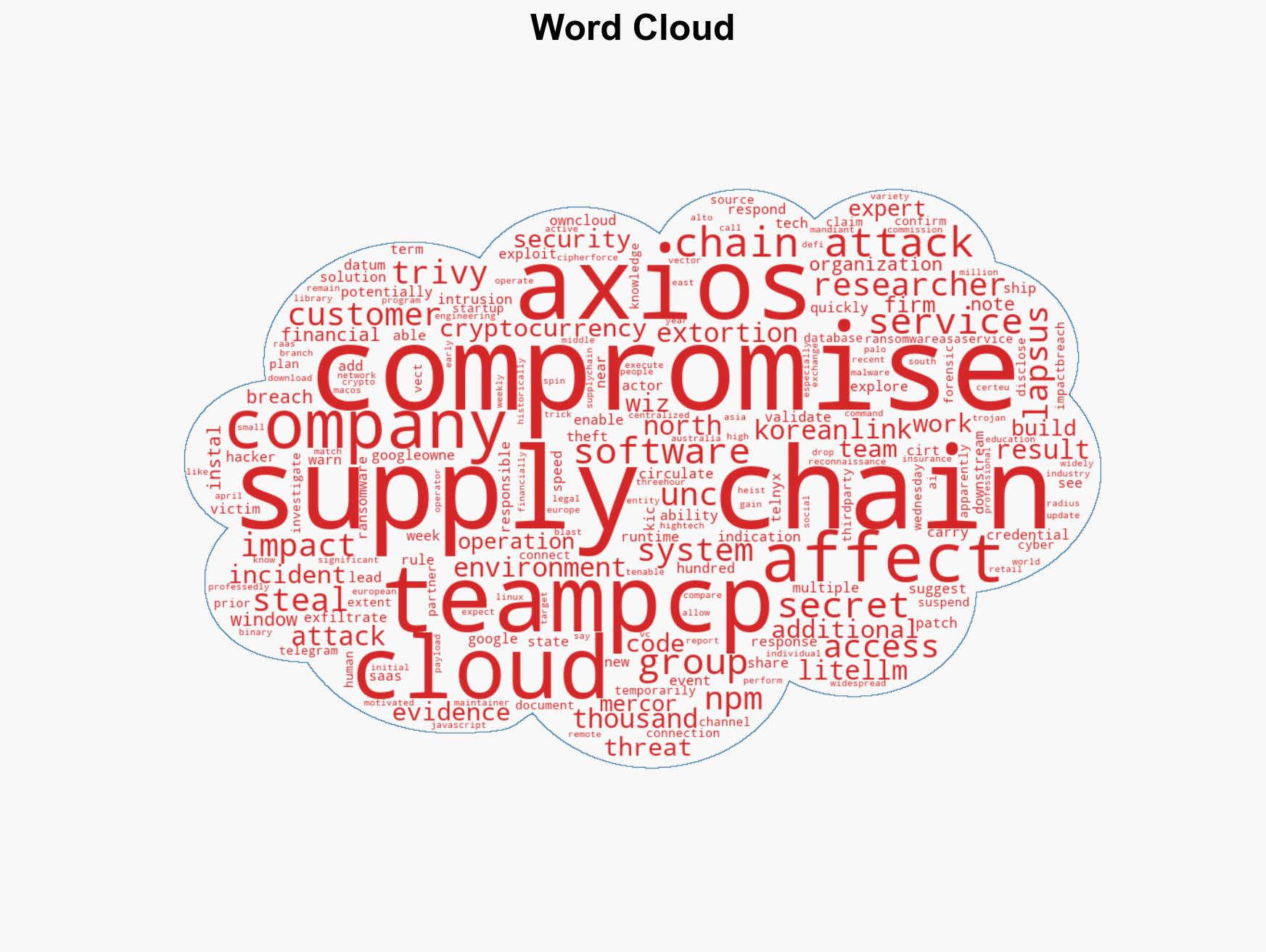
cybersecurity, supply chain attacks, data theft, ransomware, North Korea, TeamPCP, Lapsus$
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us