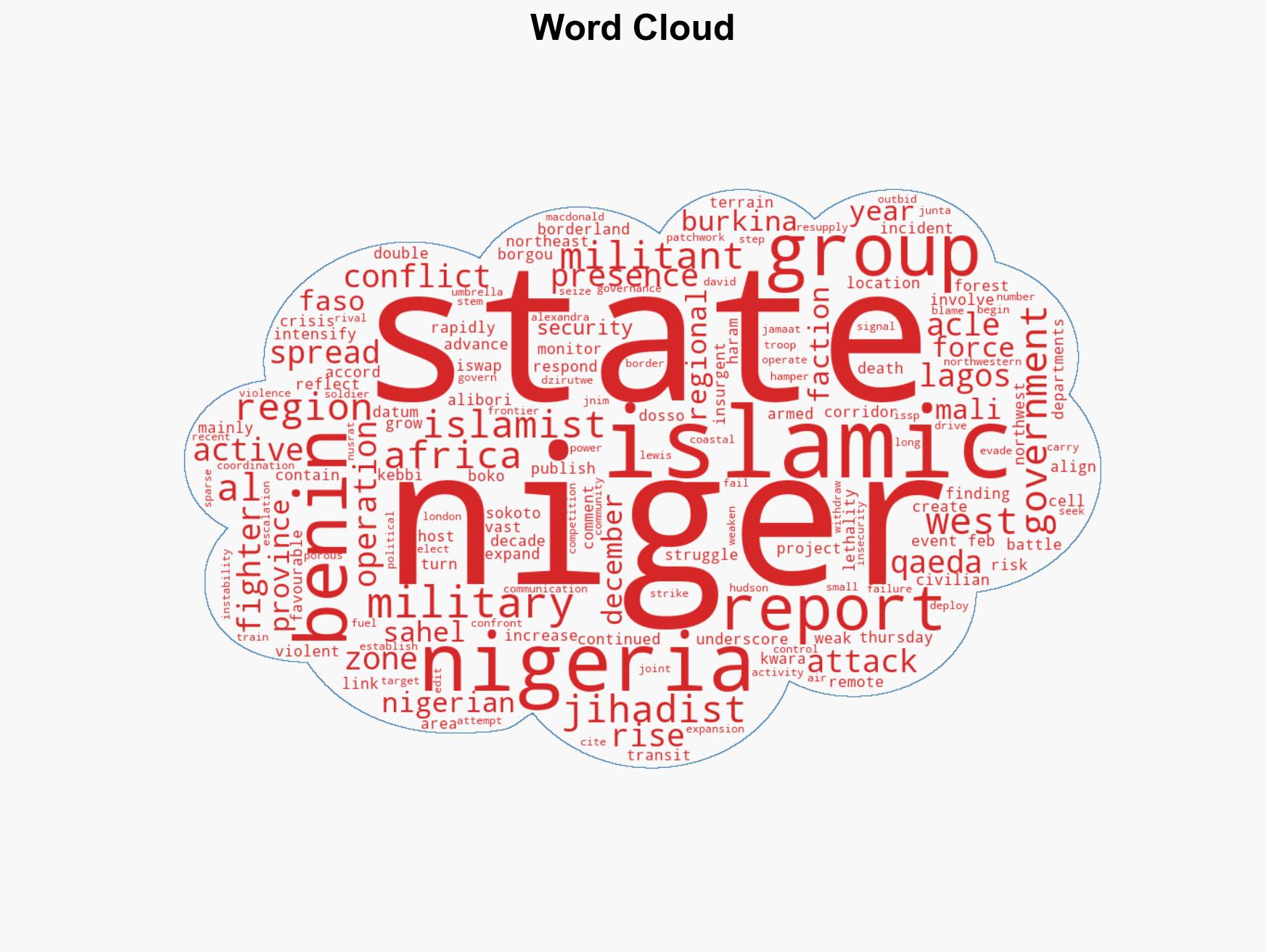
Surge in Islamist Attacks in Niger, Benin, and Nigeria’s Border Region Signals Escalating Conflict Threats
Published on: 2026-02-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Islamist militant attacks on Niger Benin and Nigeria border zone soaring research shows
1. BLUF (Bottom Line Up Front)
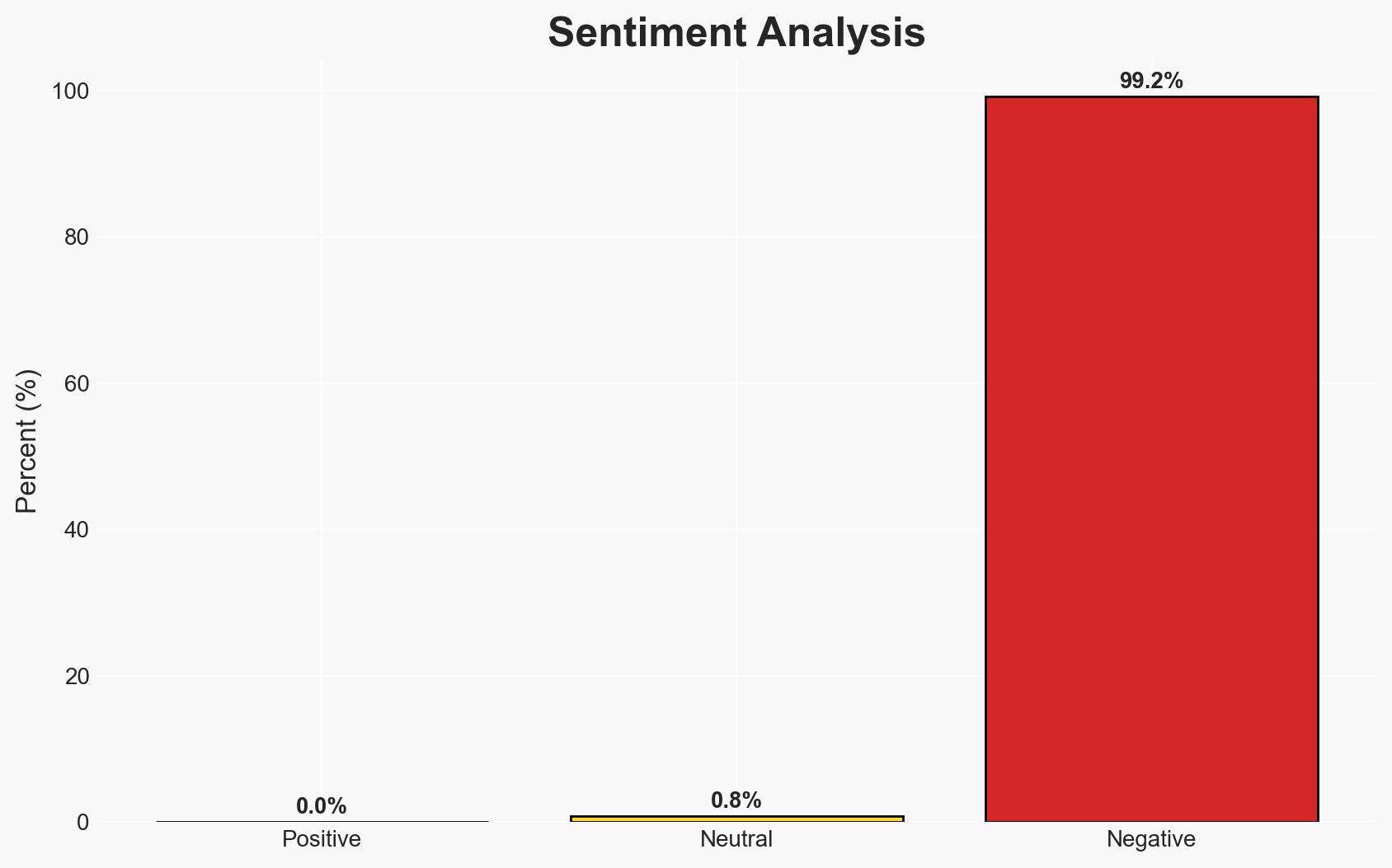
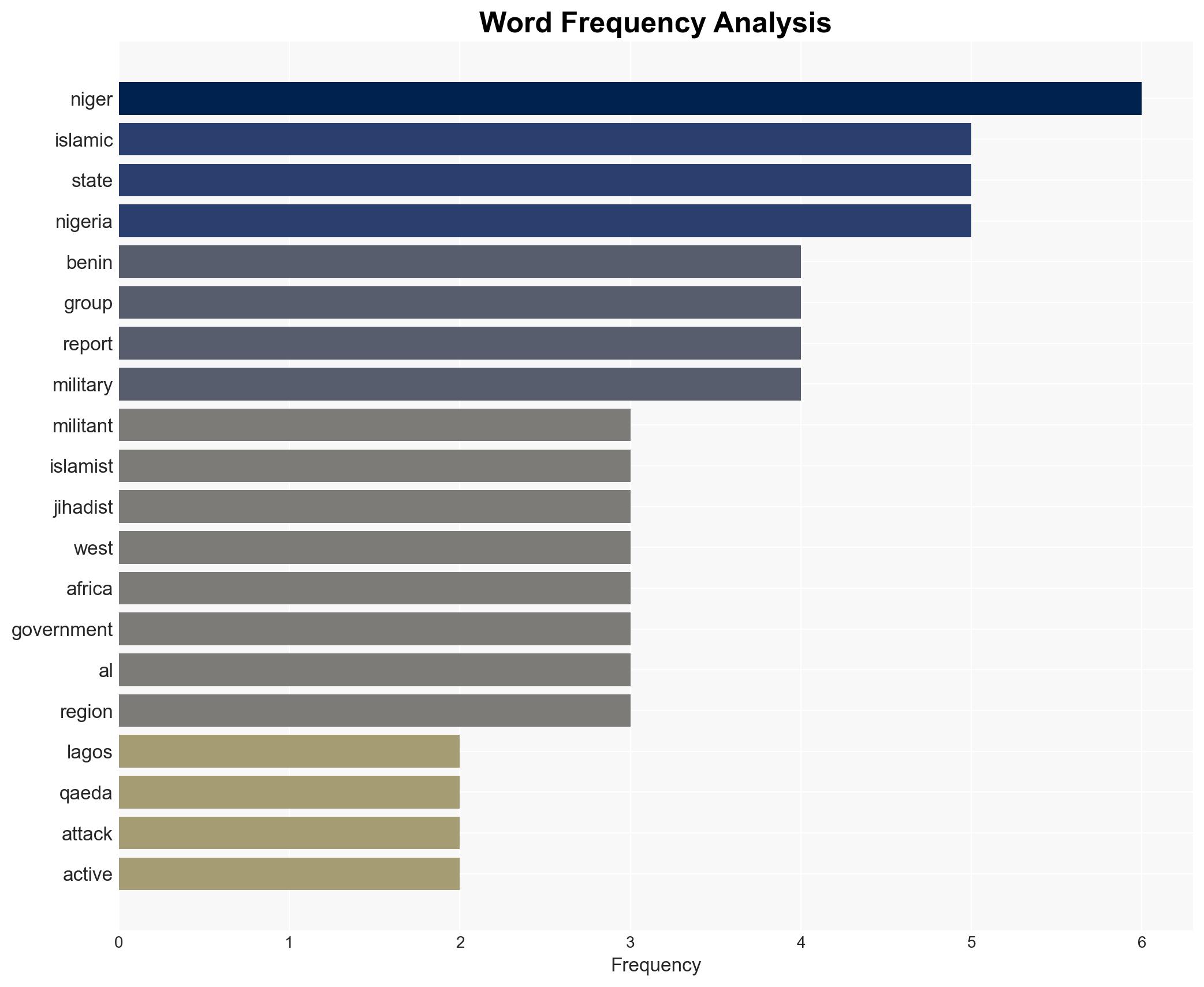
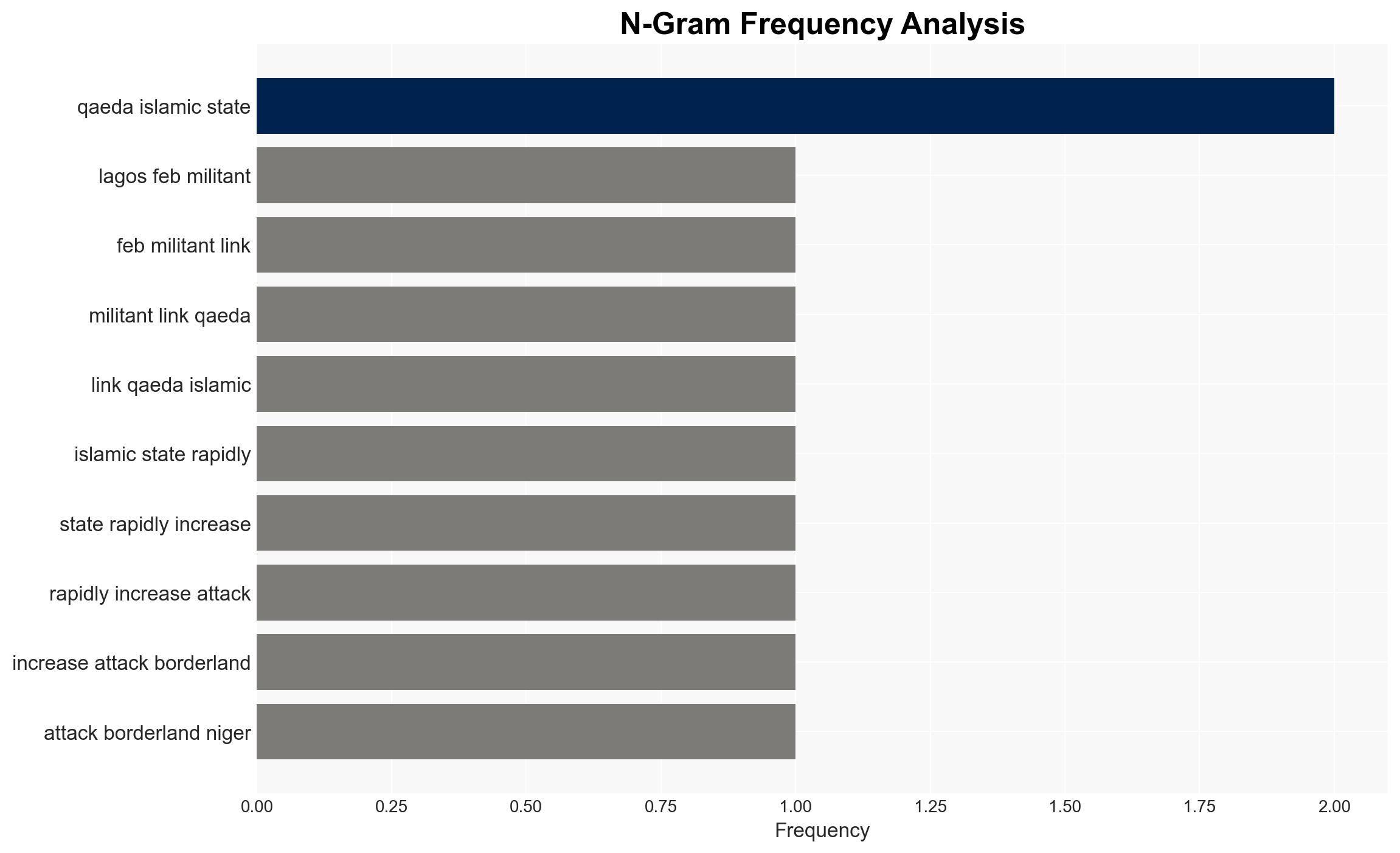
Militant attacks by groups linked to al Qaeda and Islamic State are significantly increasing in the border regions of Niger, Benin, and Nigeria, with a 90% rise in incidents and over 1,000 deaths reported. This escalation poses a growing threat to regional stability and civilian safety. The most likely hypothesis is that these groups are exploiting weak governance and porous borders to expand their influence. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: Islamist militant groups are expanding due to weak state presence and favorable terrain, allowing them to establish control over strategic transit corridors. This is supported by the reported increase in attacks and the deepening presence in specific regions. Key uncertainties include the extent of local support and the effectiveness of countermeasures.
- Hypothesis B: The surge in attacks is primarily driven by internal competition among jihadist factions, leading to increased violence as groups attempt to outbid each other for dominance. Evidence includes increased communication about activities, but this is less directly linked to the observed geographic expansion.
- Assessment: Hypothesis A is currently better supported due to the strategic advantages offered by the terrain and weak governance, which are consistent with historical patterns of militant expansion. Indicators such as changes in local governance or military effectiveness could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Militants have sufficient resources to sustain operations; local governments remain unable to effectively counter the threat; regional coordination will not improve significantly in the short term.
- Information Gaps: Detailed intelligence on the internal dynamics of jihadist groups; precise local support levels; effectiveness of recent counter-terrorism measures.
- Bias & Deception Risks: Potential bias in source reporting due to limited access; risk of overestimating militant capabilities based on reported incidents; possible manipulation of information by involved parties.
4. Implications and Strategic Risks
This development could lead to increased regional instability, with potential spillover effects into neighboring countries. The persistent threat may undermine local governance and international confidence in regional security efforts.
- Political / Geopolitical: Potential for further coups or political instability as governments struggle to manage security threats.
- Security / Counter-Terrorism: Increased operational challenges for local and international forces; potential for higher civilian casualties and displacement.
- Cyber / Information Space: Possible increase in propaganda and recruitment efforts online by jihadist groups.
- Economic / Social: Disruption of local economies, increased refugee flows, and heightened social tensions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance intelligence sharing among regional and international partners; increase surveillance and reconnaissance in affected areas.
- Medium-Term Posture (1–12 months): Strengthen regional security cooperation; invest in capacity building for local forces; support governance and development initiatives to address root causes.
- Scenario Outlook:
- Best Case: Improved regional cooperation leads to a reduction in attacks.
- Worst Case: Continued escalation results in widespread instability and humanitarian crises.
- Most Likely: Persistent low-level conflict with periodic surges in violence.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
Counter-Terrorism, regional instability, jihadist expansion, border security, West Africa, militant activity, governance challenges
Structured Analytic Techniques Applied
- ACH 2.0: Reconstruct likely threat actor intentions via hypothesis testing and structured refutation.
- Indicators Development: Track radicalization signals and propaganda patterns to anticipate operational planning.
- Narrative Pattern Analysis: Analyze spread/adaptation of ideological narratives for recruitment/incitement signals.
Explore more:
Counter-Terrorism Briefs ·
Daily Summary ·
Support us