Targeting Islamic State Hideouts in Somalia’s Al-Miskad Mountains
Published on: 2026-03-16
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
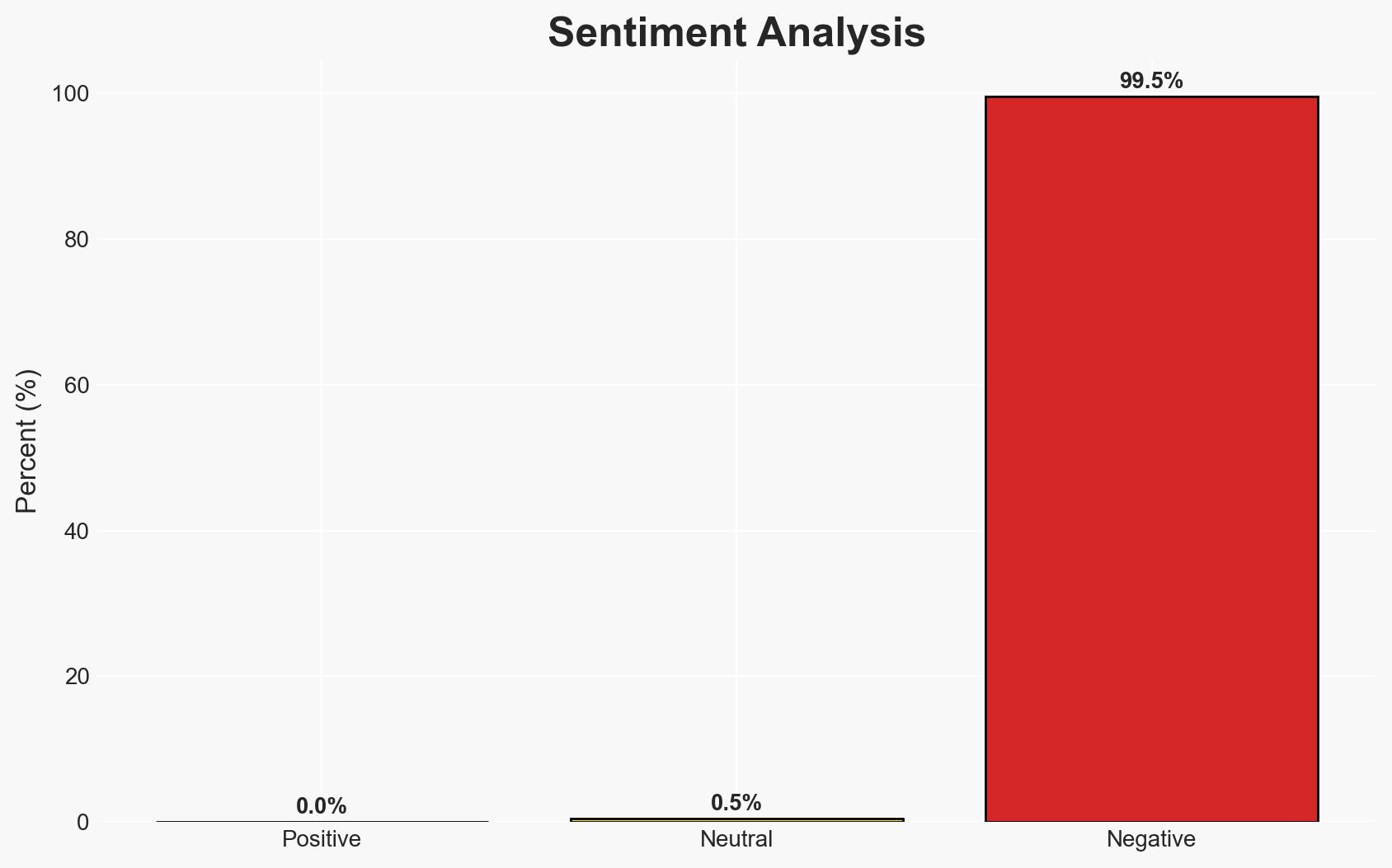
Intelligence Report: ‘We will go wherever they hide’ Rooting out IS in Somalia
1. BLUF (Bottom Line Up Front)
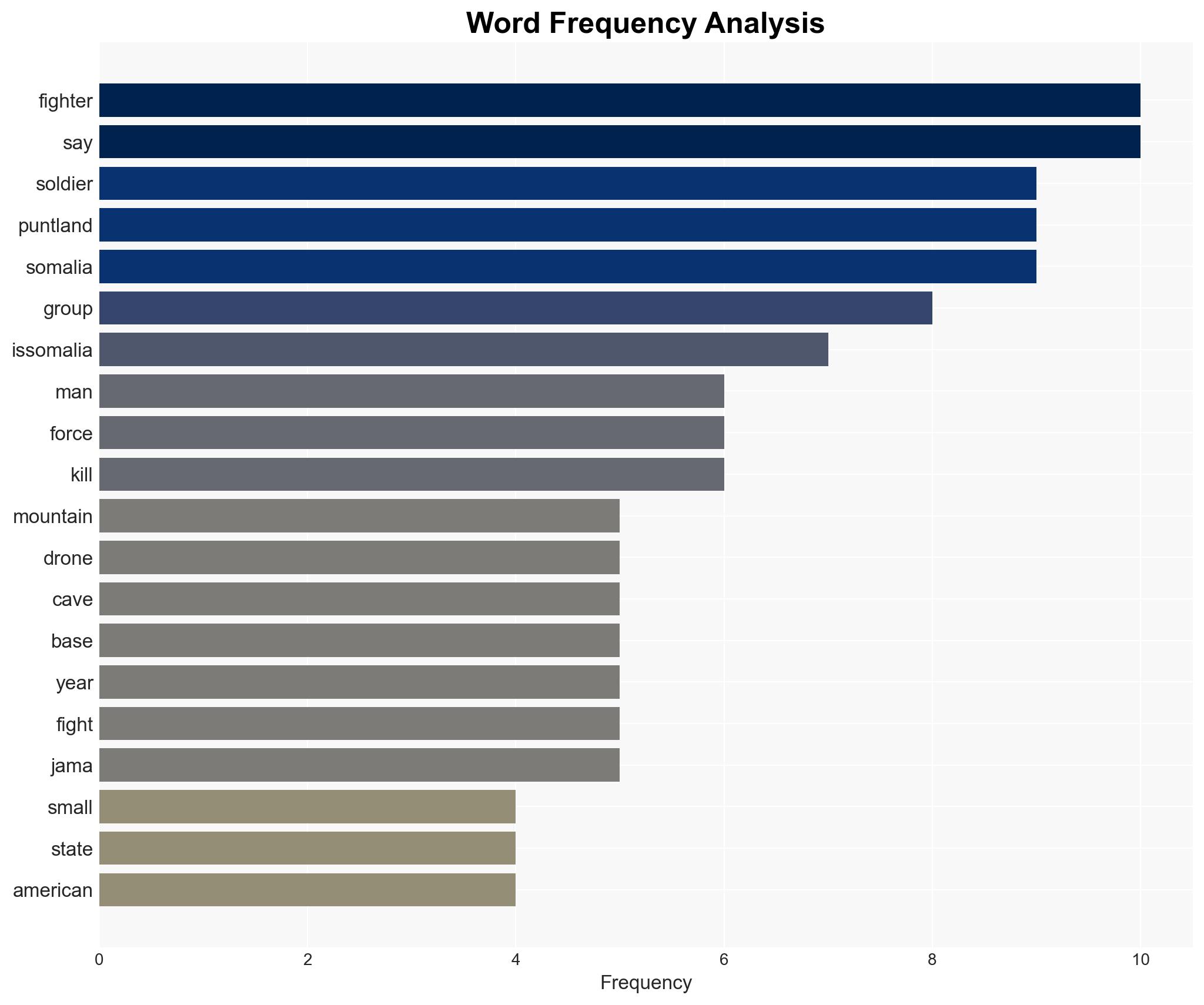
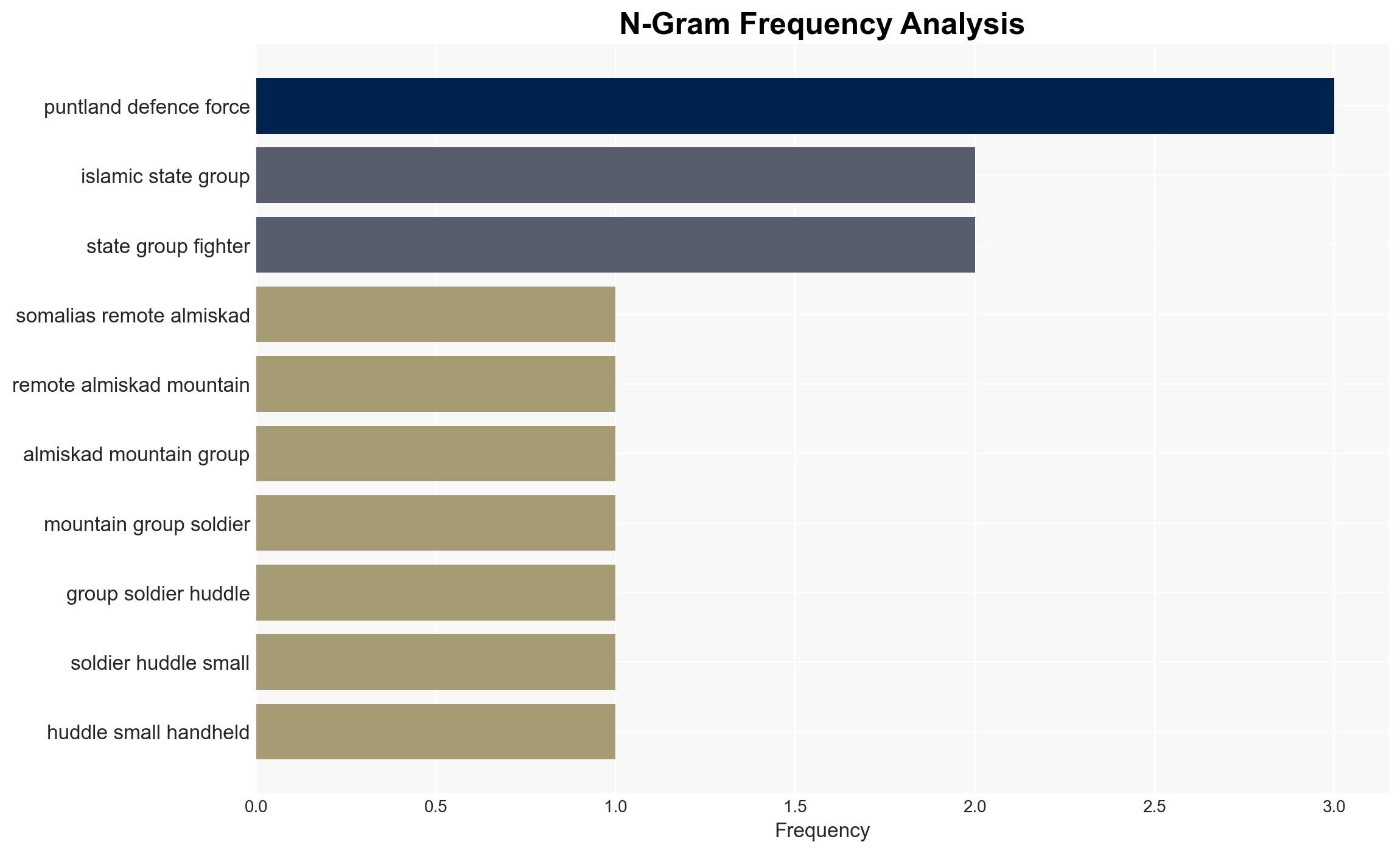
IS-Somalia’s operational capabilities have been significantly degraded due to concerted military efforts by Puntland Defence Forces and US airstrikes. However, IS-Somalia remains a critical node for IS’s global network, providing resources and support to affiliates. The threat to Puntland and broader Somalia is reduced, but the group’s influence persists. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: IS-Somalia’s operational capabilities are severely weakened, limiting its threat to local and regional stability. This is supported by the reduction in IS’s ability to stage attacks and the successful military operations against them. However, uncertainties remain regarding their capacity to regroup or shift tactics.
- Hypothesis B: IS-Somalia retains significant influence and could re-emerge as a potent threat, leveraging its role in IS’s global network. This is supported by its continued resource facilitation and historical resilience. Contradictory evidence includes recent military setbacks and loss of territorial control.
- Assessment: Hypothesis A is currently better supported due to recent military successes and diminished local threat levels. Indicators that could shift this judgment include evidence of regrouping, increased recruitment, or renewed attacks.
3. Key Assumptions and Red Flags
- Assumptions: IS-Somalia’s current operational capacity is accurately assessed; US and Puntland forces maintain current levels of pressure; IS global network continues to rely on Somalia as a hub.
- Information Gaps: Detailed intelligence on IS-Somalia’s internal leadership dynamics and external support networks.
- Bias & Deception Risks: Potential over-reliance on military sources; IS propaganda may exaggerate capabilities or downplay losses.
4. Implications and Strategic Risks
The degradation of IS-Somalia’s capabilities could lead to a temporary reduction in regional instability, but the group’s role in the global IS network poses ongoing risks.
- Political / Geopolitical: Potential for increased regional cooperation against IS; risk of IS shifting focus to weaker areas.
- Security / Counter-Terrorism: Reduced immediate threat but ongoing vigilance required to prevent resurgence.
- Cyber / Information Space: IS may increase online recruitment and propaganda to compensate for territorial losses.
- Economic / Social: Continued extortion and resource extraction could undermine local economies and social cohesion.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance intelligence-sharing among regional partners; maintain pressure on IS hideouts.
- Medium-Term Posture (1–12 months): Strengthen local governance and economic resilience in affected areas; support deradicalization programs.
- Scenario Outlook: Best: IS-Somalia further weakened and isolated; Worst: IS-Somalia regroups and escalates attacks; Most-Likely: Continued low-level threat with sporadic activity.
6. Key Individuals and Entities
- Abdulqadir Mumin (IS-Somalia leader)
- Puntland Defence Forces
- United States Africa Command (Africom)
- Tricia Bacon (Director, Policy Anti-Terrorism Hub)
7. Thematic Tags
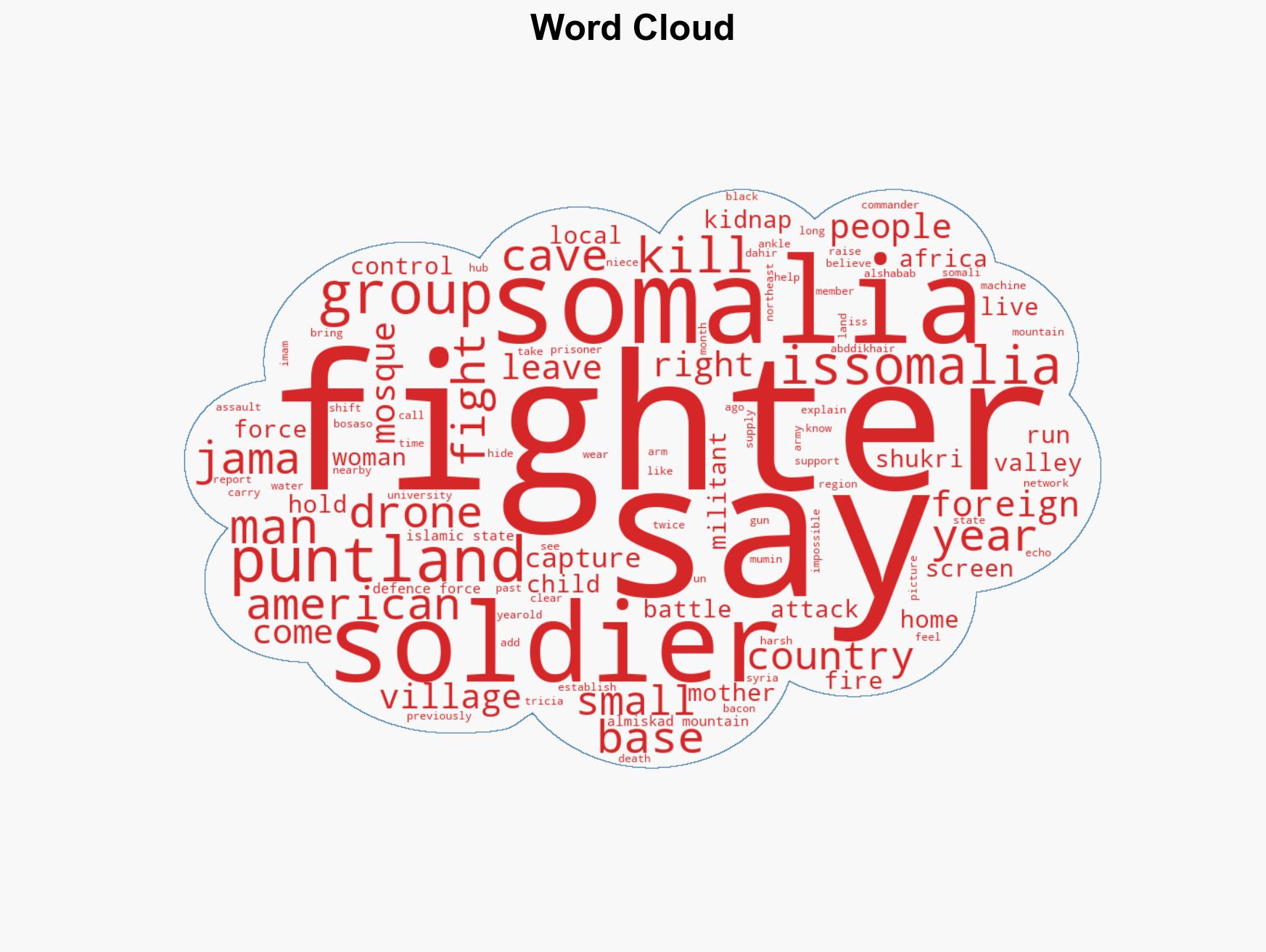
regional conflicts, counter-terrorism, IS-Somalia, Puntland, military operations, regional security, global network, resource facilitation
Structured Analytic Techniques Applied
- Causal Layered Analysis (CLA): Analyze events across surface happenings, systems, worldviews, and myths.
- Cross-Impact Simulation: Model ripple effects across neighboring states, conflicts, or economic dependencies.
- Scenario Generation: Explore divergent futures under varying assumptions to identify plausible paths.
- Network Influence Mapping: Map influence relationships to assess actor impact.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
Explore more:
Regional Conflicts Briefs ·
Daily Summary ·
Support us