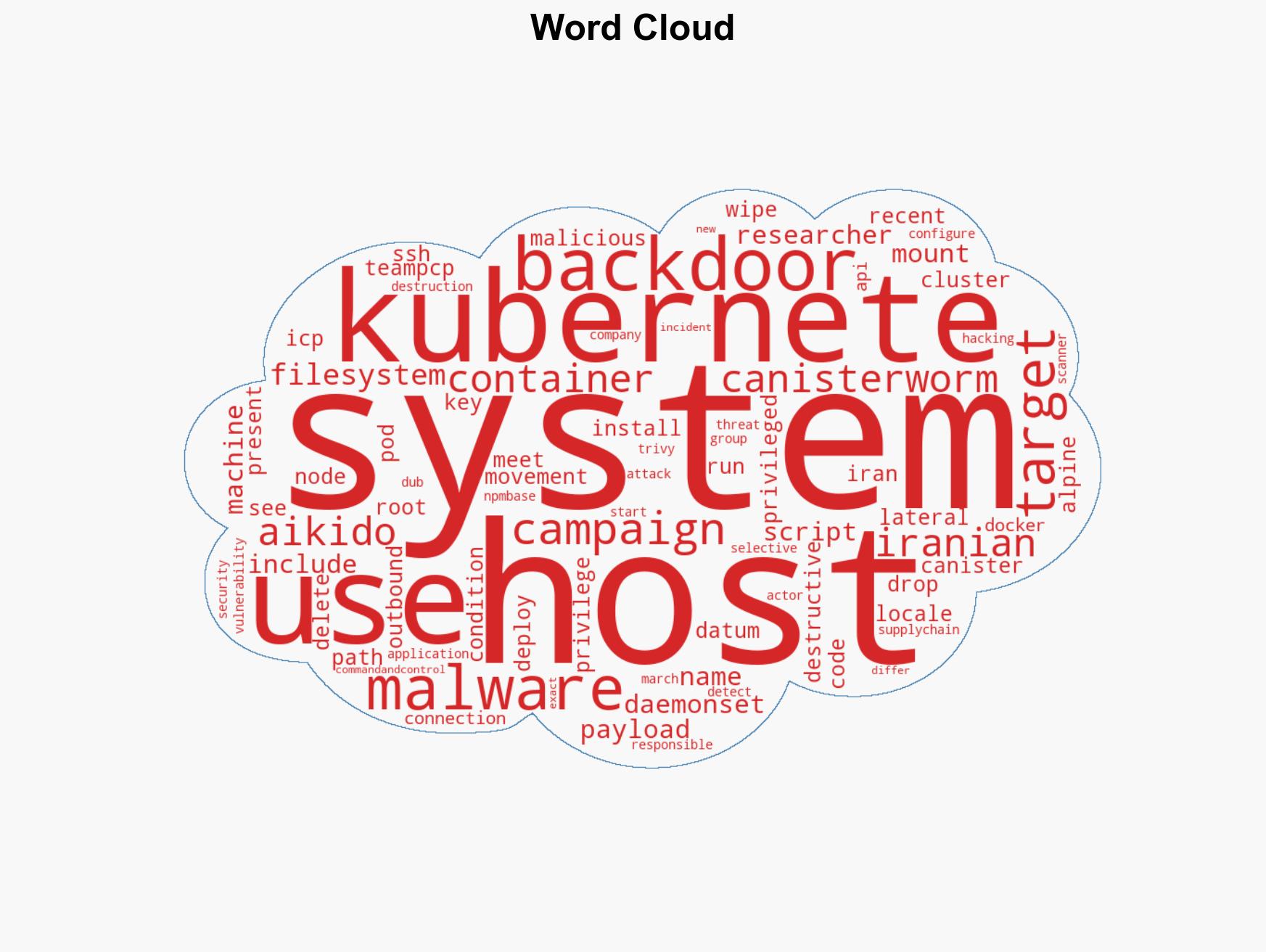
TeamPCP Targets Kubernetes Clusters with Destructive Wiper Aimed at Iranian Systems
Published on: 2026-03-23
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: TeamPCP deploys Iran-targeted wiper in Kubernetes attacks
1. BLUF (Bottom Line Up Front)
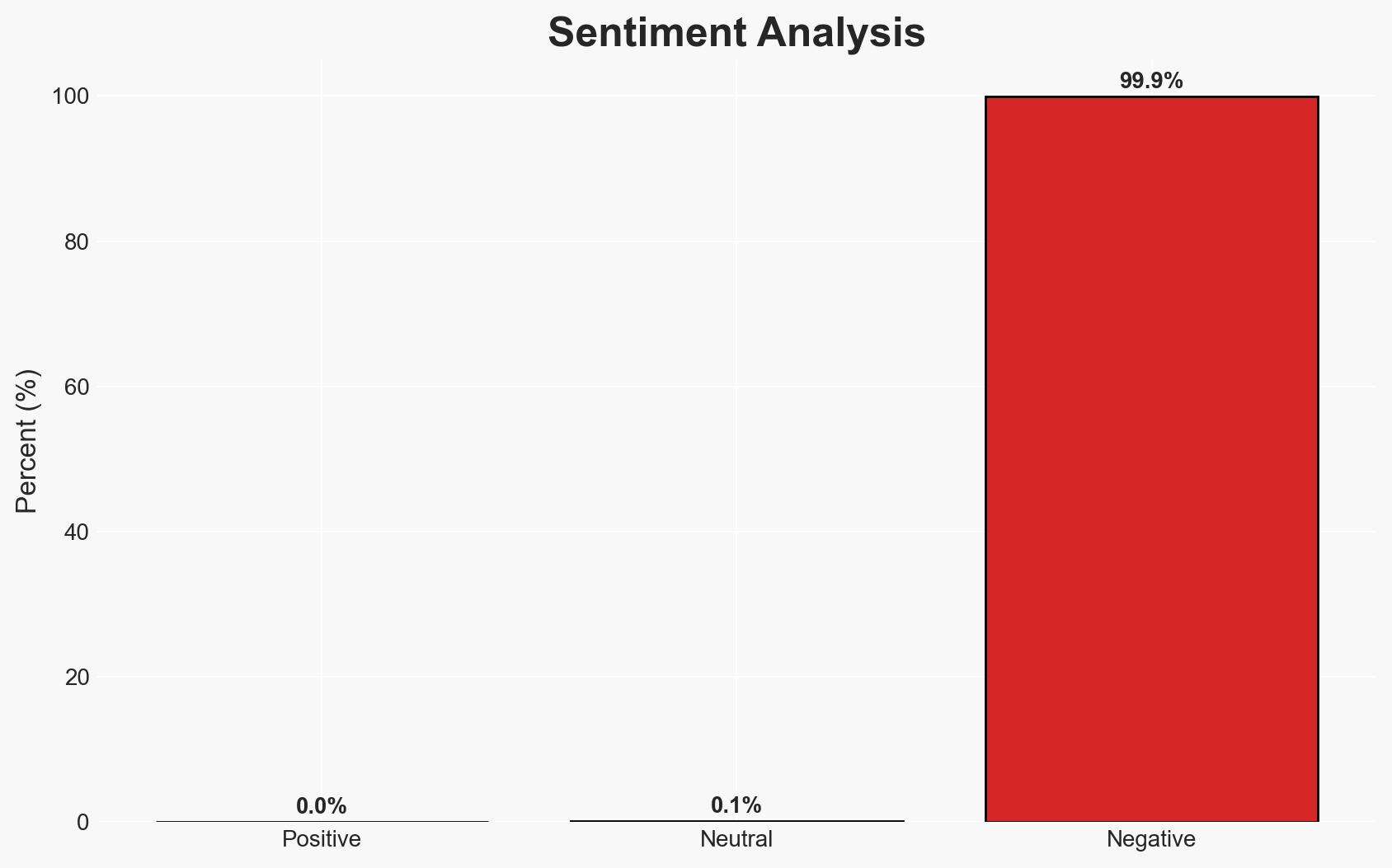
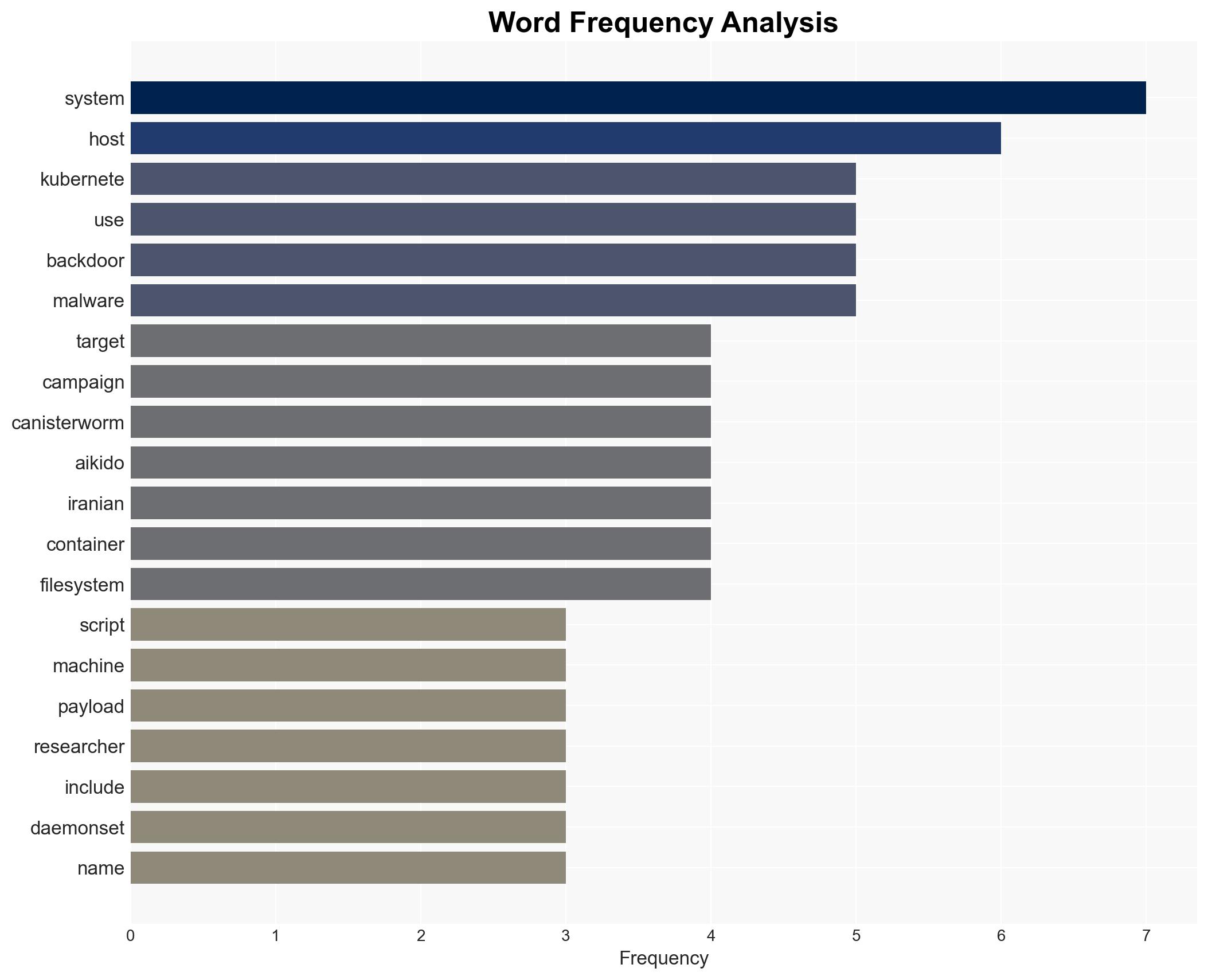
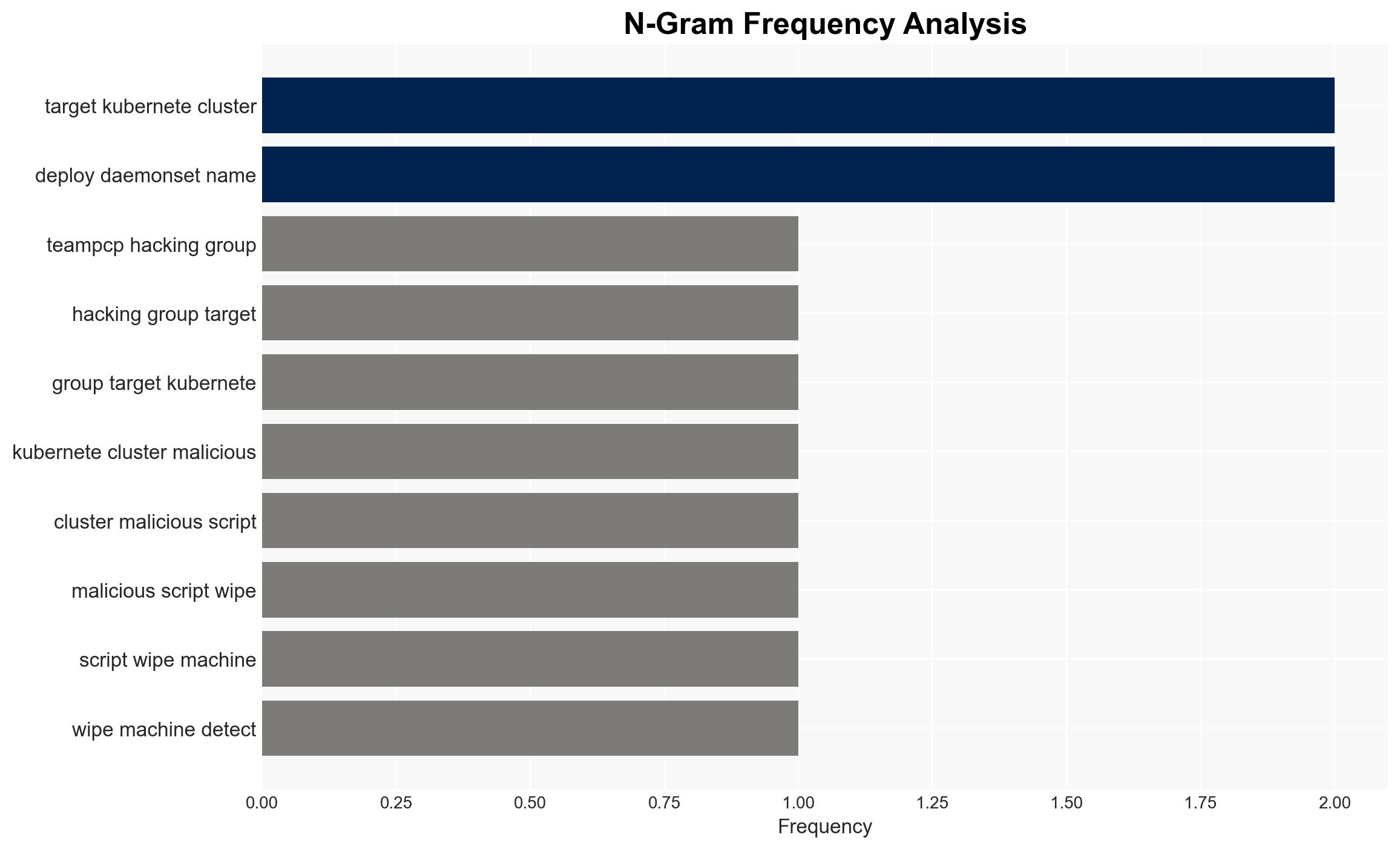
The TeamPCP hacking group has launched a targeted cyber campaign against Iranian systems, using a wiper malware that destroys data on machines configured for Iran. This operation represents an escalation in their tactics, potentially indicating geopolitical motives. The campaign also installs backdoors on non-Iranian systems, suggesting broader surveillance objectives. Overall confidence in this assessment is moderate due to limited source diversity and potential deception by the threat actor.
2. Competing Hypotheses
- Hypothesis A: TeamPCP is conducting a politically motivated cyber operation specifically targeting Iranian systems to disrupt or degrade their capabilities. This is supported by the selective destruction payload aimed at Iranian locales and the geopolitical context. However, the lack of direct attribution or stated political motives introduces uncertainty.
- Hypothesis B: TeamPCP’s actions are primarily financially motivated, using the Iran-targeted wiper as a diversion while focusing on installing backdoors for broader cybercriminal activities. The use of backdoors on non-Iranian systems supports this, but the specific targeting of Iranian systems with destructive payloads contradicts purely financial motives.
- Assessment: Hypothesis A is currently better supported due to the targeted nature of the attack on Iranian systems, suggesting a geopolitical motive. Indicators such as changes in geopolitical tensions or further targeted attacks could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The malware’s targeting criteria are accurately reported; TeamPCP has the capability and intent to execute geopolitically motivated attacks; the observed tactics are representative of the group’s broader strategy.
- Information Gaps: Direct evidence linking TeamPCP to a state sponsor; comprehensive understanding of the group’s long-term objectives; details on the full scope of affected systems.
- Bias & Deception Risks: Potential confirmation bias in interpreting geopolitical motives; source bias from security researchers with vested interests; possible deception by TeamPCP to mislead attribution efforts.
4. Implications and Strategic Risks
This development could exacerbate regional tensions and provoke retaliatory cyber operations. The dual-use nature of the campaign—destructive in Iran, surveillance elsewhere—complicates attribution and response strategies.
- Political / Geopolitical: Potential escalation in cyber conflict between Iran and perceived adversaries; increased scrutiny on state-sponsored cyber activities.
- Security / Counter-Terrorism: Heightened threat environment for Iranian critical infrastructure; possible spillover effects on regional cybersecurity dynamics.
- Cyber / Information Space: Increased risk of similar tactics being adopted by other threat actors; potential for misinformation campaigns leveraging the attack.
- Economic / Social: Disruption to Iranian economic activities reliant on affected systems; potential public unrest if critical services are impacted.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of systems for indicators of compromise; collaborate with international partners to share threat intelligence; issue alerts to potentially affected sectors.
- Medium-Term Posture (1–12 months): Develop resilience measures for critical infrastructure; strengthen partnerships with cybersecurity firms for threat detection and response; invest in capability development for attribution and mitigation.
- Scenario Outlook:
- Best: Rapid identification and neutralization of the threat actor, minimizing impact.
- Worst: Escalation into broader cyber conflict with significant economic and political repercussions.
- Most-Likely: Continued low-level cyber skirmishes with periodic escalations, driven by geopolitical developments.
6. Key Individuals and Entities
- TeamPCP (hacking group)
- Aikido (application security company)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, geopolitical conflict, cyber-espionage, Iran, supply-chain attacks, malware, cyber operations
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us