TeamPCP Targets LiteLLM with Compromised PyPI Packages in Latest Supply Chain Attack
Published on: 2026-03-25
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: LiteLLM PyPI packages compromised in expanding TeamPCP supply chain attacks
1. BLUF (Bottom Line Up Front)
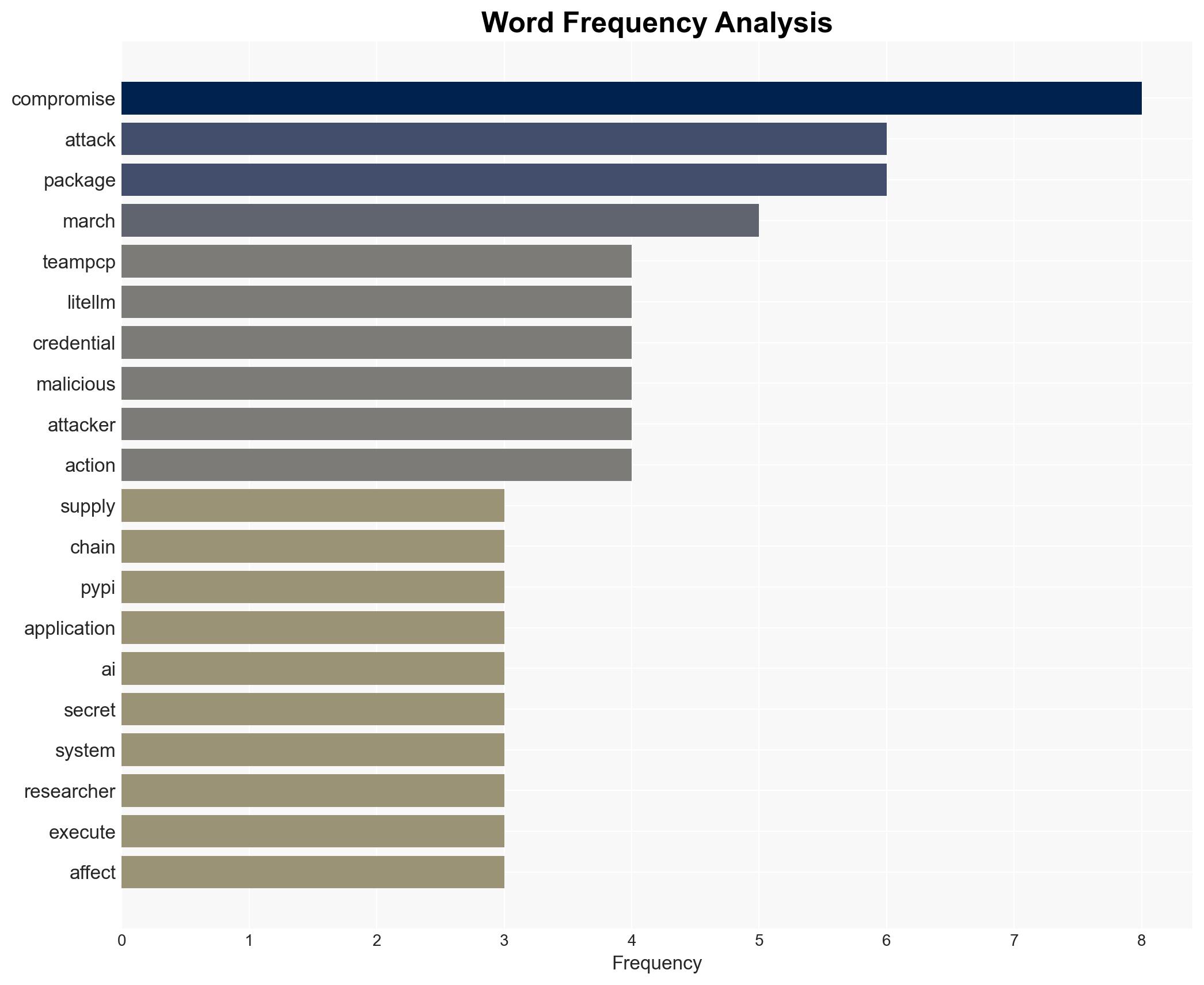
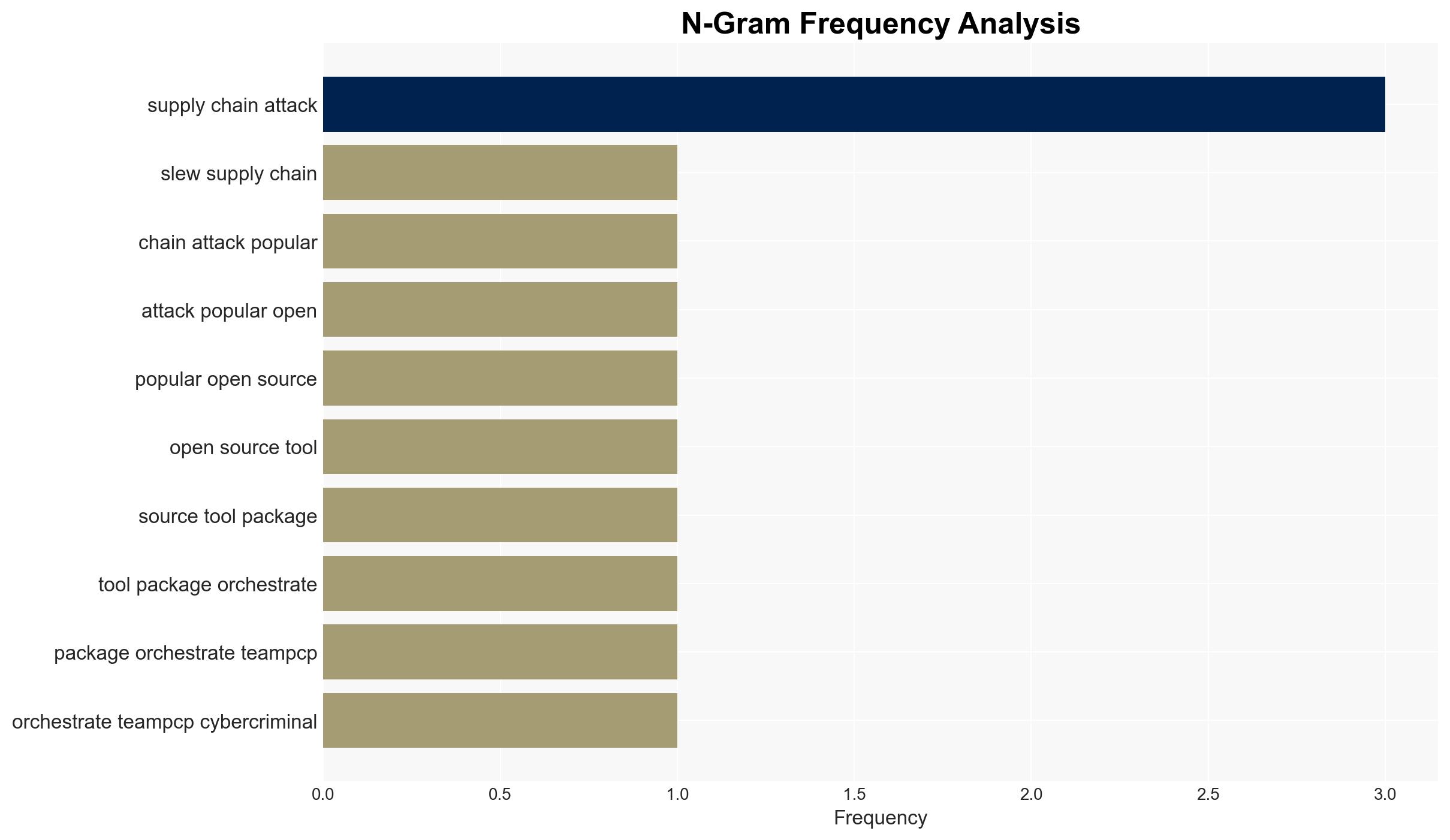
The cybercriminal group TeamPCP has compromised the LiteLLM library on PyPI, posing a significant threat to enterprises using open-source AI tools. The attack is part of a broader campaign targeting software supply chains. The most likely hypothesis is that TeamPCP aims to exfiltrate sensitive data from a wide range of targets. This assessment is made with moderate confidence due to the pattern of previous attacks and the strategic position of LiteLLM in the AI ecosystem.
2. Competing Hypotheses
- Hypothesis A: TeamPCP is targeting open-source software supply chains to exfiltrate sensitive data from enterprises. This is supported by the strategic targeting of LiteLLM, which has access to critical API keys and environment variables. However, the exact scope and scale of the data exfiltration remain uncertain.
- Hypothesis B: TeamPCP’s actions are primarily aimed at disrupting the development and deployment of AI applications to cause reputational damage to open-source platforms. While this could be a secondary effect, there is less direct evidence supporting this as the primary motive compared to data exfiltration.
- Assessment: Hypothesis A is currently better supported due to the specific targeting of tools that handle sensitive data. Indicators that could shift this judgment include evidence of coordinated disinformation campaigns or further attacks on less data-centric tools.
3. Key Assumptions and Red Flags
- Assumptions: TeamPCP has the technical capability to exploit vulnerabilities in widely used open-source tools; the compromised packages are part of a broader strategic campaign; affected organizations have not fully mitigated the risks.
- Information Gaps: The full extent of data exfiltration and the specific targets within enterprises remain unclear; the identity and motivations of TeamPCP’s leadership are not well-documented.
- Bias & Deception Risks: There is a risk of confirmation bias in attributing all recent supply chain attacks to TeamPCP without considering other actors; potential deception by TeamPCP in masking their true objectives.
4. Implications and Strategic Risks
The compromise of LiteLLM could lead to increased scrutiny and regulation of open-source software supply chains, impacting their adoption and trust. The ongoing threat from TeamPCP may drive organizations to reassess their cybersecurity strategies.
- Political / Geopolitical: Potential for international calls for stronger cybersecurity standards and cooperation in response to supply chain vulnerabilities.
- Security / Counter-Terrorism: Heightened threat environment for organizations relying on open-source tools, necessitating enhanced security measures.
- Cyber / Information Space: Increased risk of data breaches and information theft, with potential for subsequent misinformation campaigns if sensitive data is leaked.
- Economic / Social: Potential economic impact on companies reliant on compromised tools, leading to financial losses and reputational damage.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Organizations should immediately audit their systems for compromised packages, rotate credentials, and enhance monitoring for unusual activity.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms for threat intelligence sharing and invest in supply chain security tools to detect and mitigate future threats.
- Scenario Outlook:
- Best: TeamPCP’s activities are curtailed through international cooperation and improved security measures.
- Worst: Continued attacks lead to widespread data breaches and loss of trust in open-source tools.
- Most-Likely: Ongoing sporadic attacks with gradual improvements in organizational defenses and security practices.
6. Key Individuals and Entities
- TeamPCP (cybercriminal group)
- BerryAI (developer of LiteLLM)
- Callum McMahon (research scientist at FutureSearch)
- Sonatype (research organization)
- Aqua Security (affected by related supply chain attack)
- CheckMarx (affected by related supply chain attack)
7. Thematic Tags
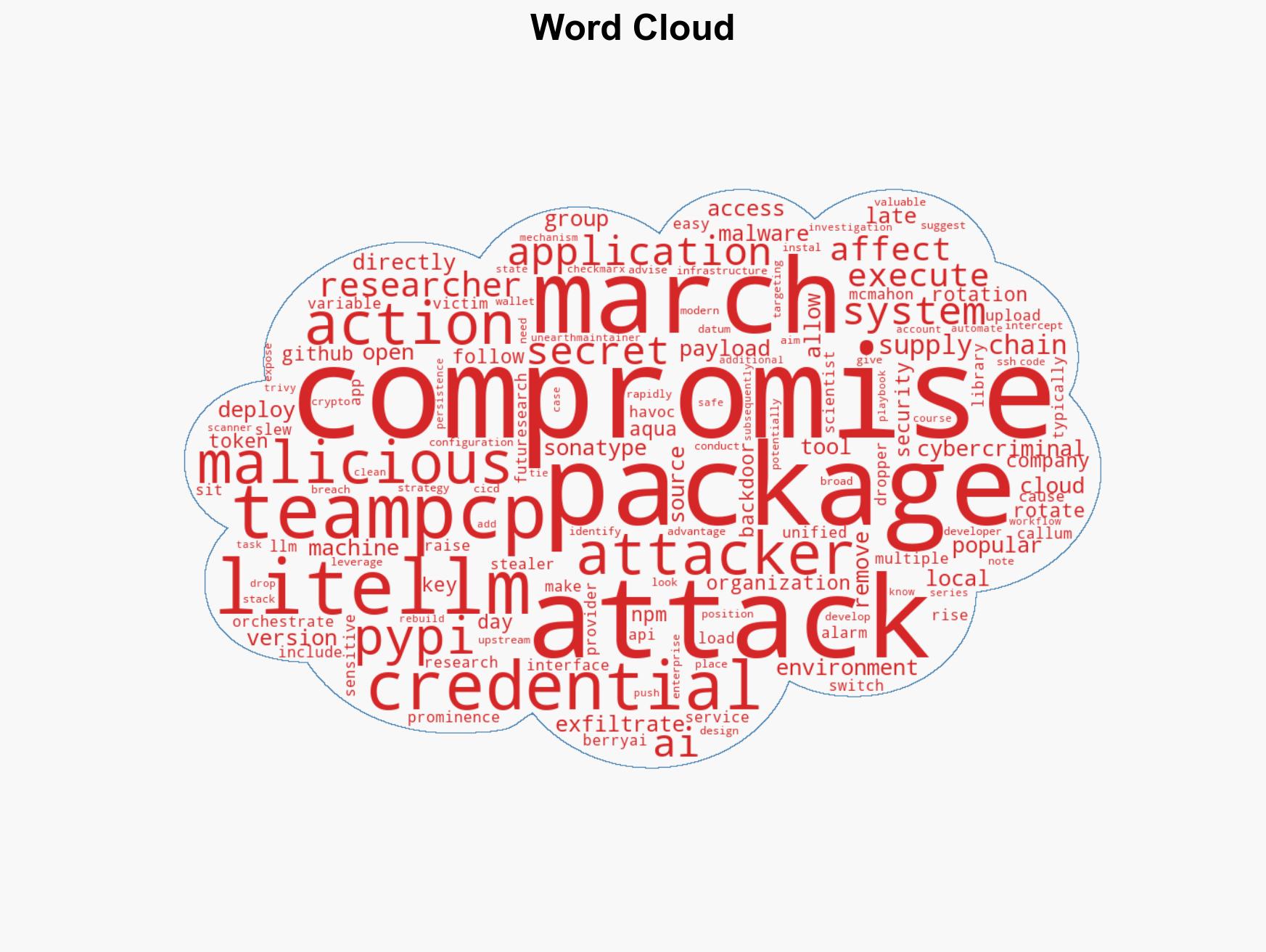
cybersecurity, supply chain attacks, cybercrime, open-source security, data exfiltration, AI infrastructure, malware, cybersecurity strategy
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us