TeamPCP’s supply chain breaches halt as focus shifts to ransomware collaboration with Vect.
Published on: 2026-03-30
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: TeamPCPs attack spree slows but threat escalates with ransomware pivot
1. BLUF (Bottom Line Up Front)
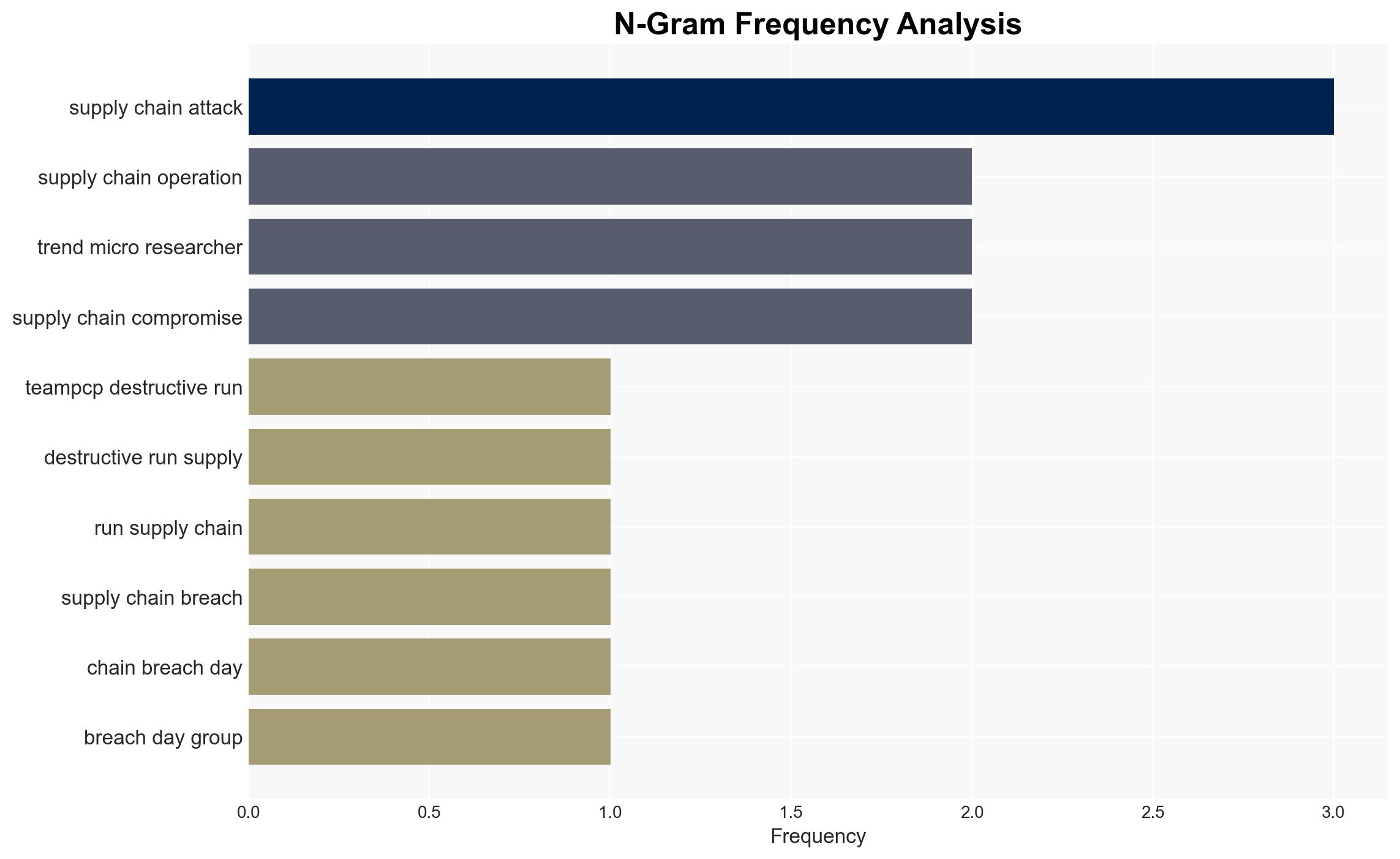
TeamPCP has temporarily halted its aggressive supply chain attacks, likely shifting focus to monetizing stolen credentials through a partnership with the Vect ransomware group. This pivot increases the ransomware threat to previously compromised entities. The overall confidence in this assessment is moderate, given the current evidence and potential for strategic deception.
2. Competing Hypotheses
- Hypothesis A: TeamPCP has paused its supply chain attacks to focus on monetizing stolen credentials through ransomware deployment with Vect. This is supported by the recent pause in attacks and the announcement of their partnership with Vect. However, the pause could be temporary, and attacks might resume.
- Hypothesis B: TeamPCP’s pause in attacks is due to operational setbacks or external pressures, rather than a strategic shift to ransomware. The lack of new attacks could indicate resource constraints or defensive measures by targets. This hypothesis lacks direct supporting evidence compared to Hypothesis A.
- Assessment: Hypothesis A is currently better supported due to the explicit announcement of the partnership with Vect and the confirmed ransomware deployment using TeamPCP credentials. Indicators that could shift this judgment include resumption of supply chain attacks or evidence of external pressures on TeamPCP.
3. Key Assumptions and Red Flags
- Assumptions: TeamPCP has the capability to effectively deploy ransomware; Vect’s announcement is credible; the pause in attacks is strategic rather than forced.
- Information Gaps: Details on the internal motivations and resource status of TeamPCP; comprehensive data on the extent of credential compromises.
- Bias & Deception Risks: Potential over-reliance on cybercriminal forums for information; possibility of misinformation or exaggeration by Vect to enhance reputation.
4. Implications and Strategic Risks
The shift from supply chain attacks to ransomware could lead to increased financial and operational impacts on affected companies. This development might encourage other threat actors to adopt similar strategies, increasing the overall ransomware threat landscape.
- Political / Geopolitical: Potential for increased tensions between nations if state actors are perceived to be supporting or ignoring these cybercriminal activities.
- Security / Counter-Terrorism: Heightened threat environment for organizations with previous TeamPCP compromises; increased need for robust cybersecurity measures.
- Cyber / Information Space: Enhanced focus on ransomware as a service (RaaS) models; potential for more sophisticated and widespread cyber attacks.
- Economic / Social: Potential economic disruptions for targeted companies; increased insurance and cybersecurity costs.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase monitoring of known compromised entities; enhance ransomware defenses; engage with cybersecurity partners for intelligence sharing.
- Medium-Term Posture (1–12 months): Develop resilience measures against ransomware; strengthen international cooperation on cybercrime; invest in cybersecurity training and awareness.
- Scenario Outlook:
- Best: TeamPCP’s operations are disrupted by law enforcement, reducing the threat.
- Worst: Successful ransomware campaigns lead to significant financial losses and operational disruptions.
- Most-Likely: Continued ransomware attempts with varying success, prompting increased cybersecurity measures.
6. Key Individuals and Entities
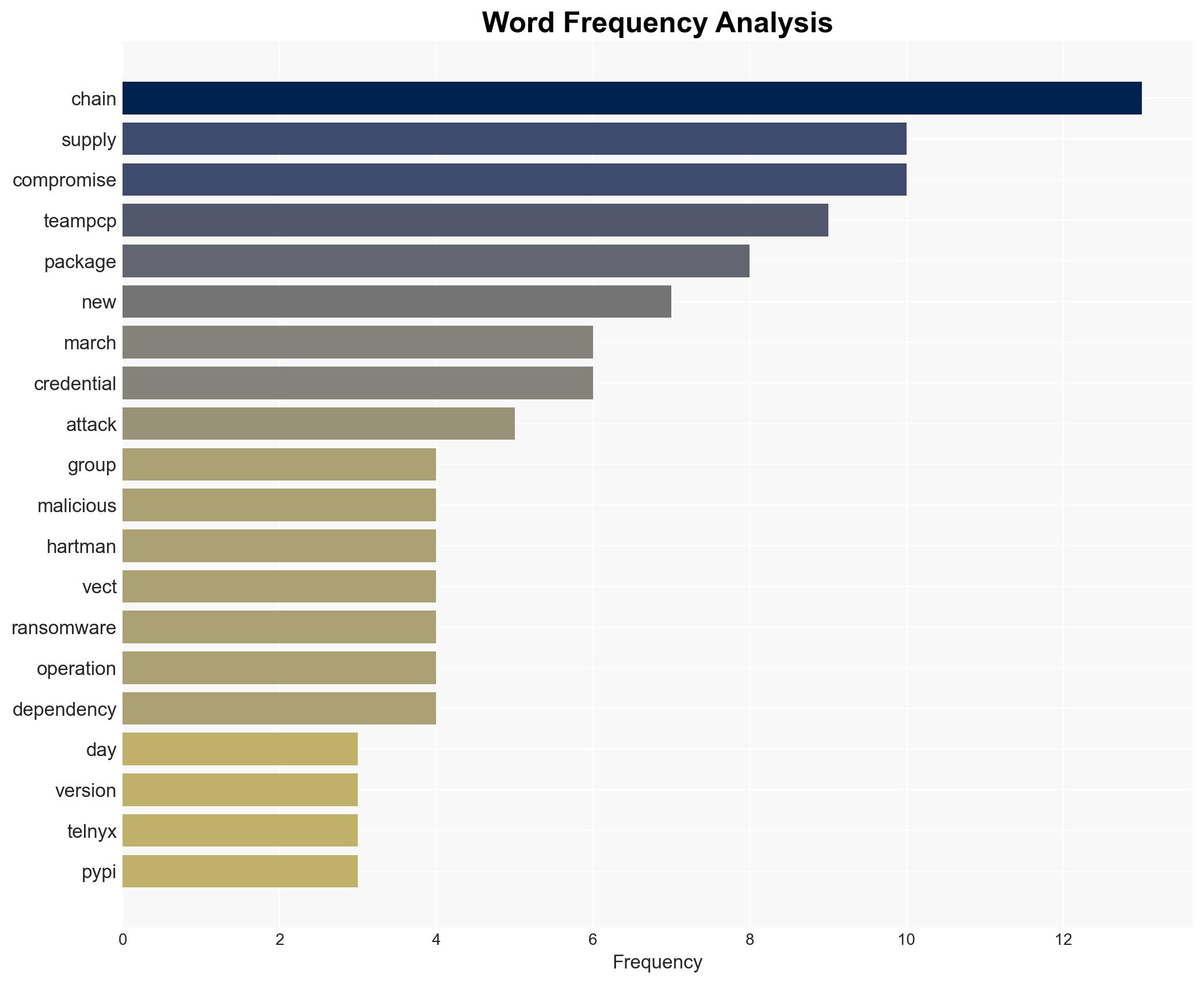
- TeamPCP
- Vect
- Telnyx
- Trivy
- CanisterWorm
- Checkmarx
- LiteLLM
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
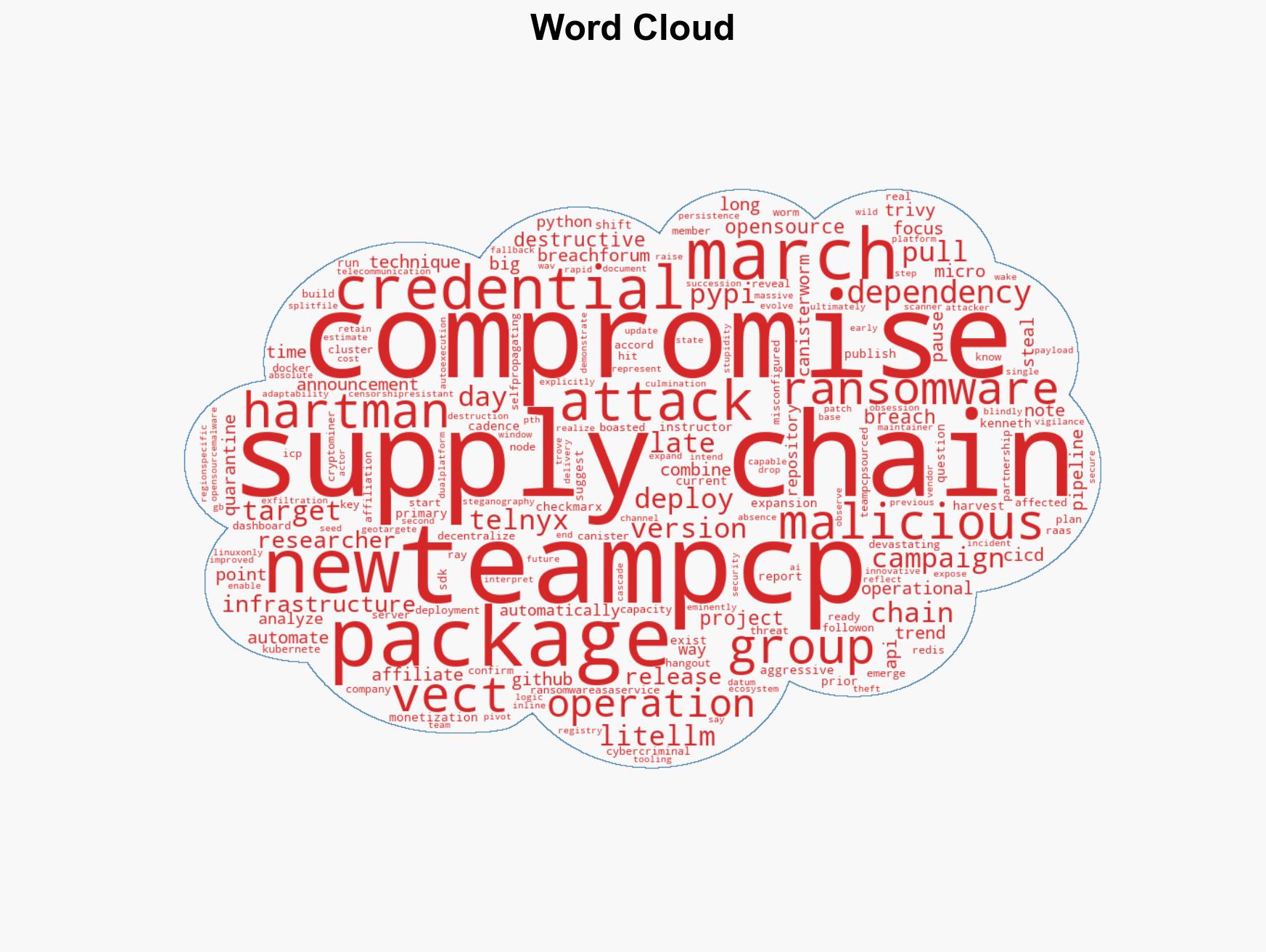
cybersecurity, ransomware, supply chain attacks, cybercrime, threat intelligence, ransomware-as-a-service, credential theft
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us