Teenager’s confinement foils planned Southport-inspired attack, leading to police confession and arrest.
Published on: 2026-03-07
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Locked door made ‘incel’ teen give up Southport copycat massacre plan
1. BLUF (Bottom Line Up Front)
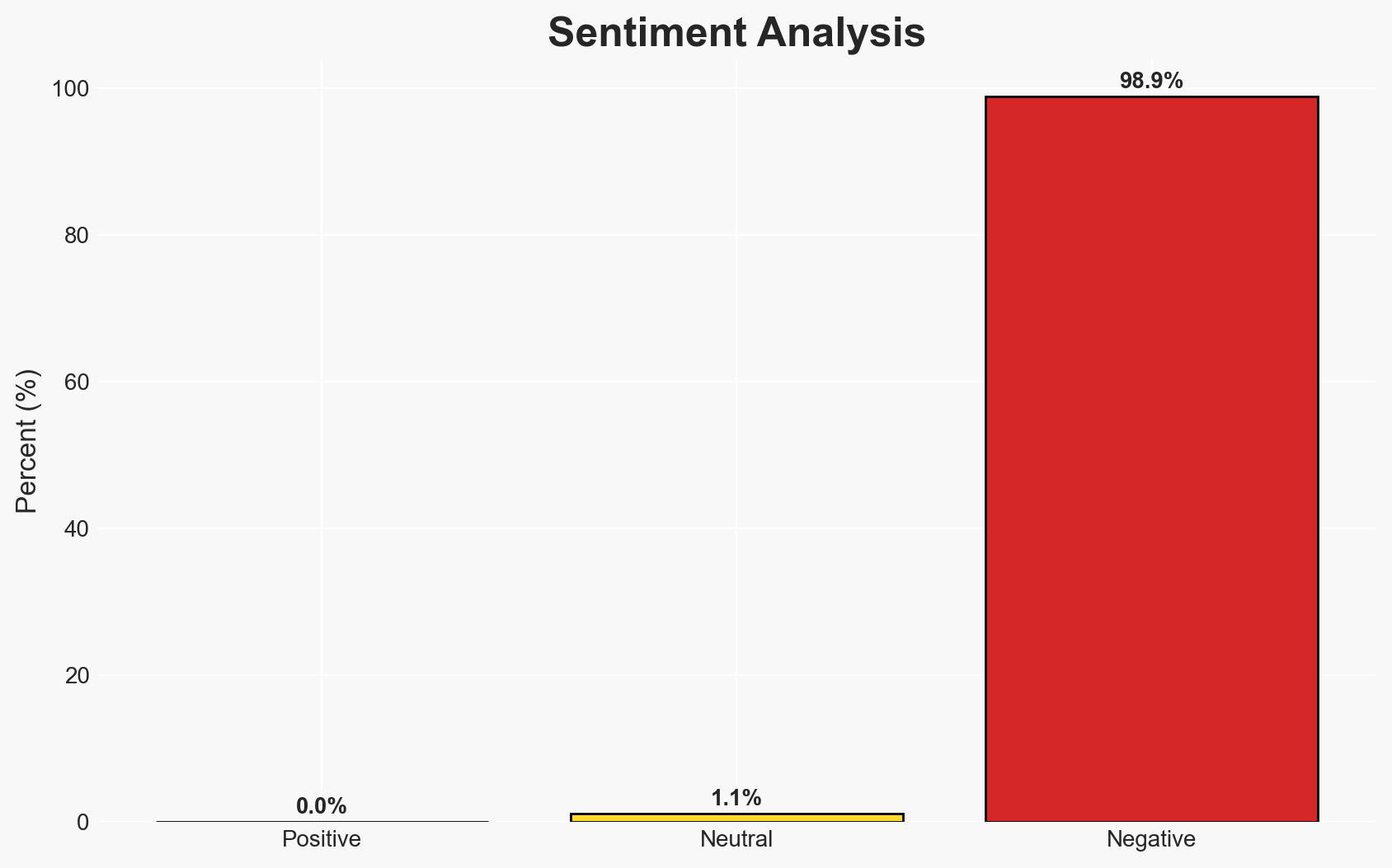
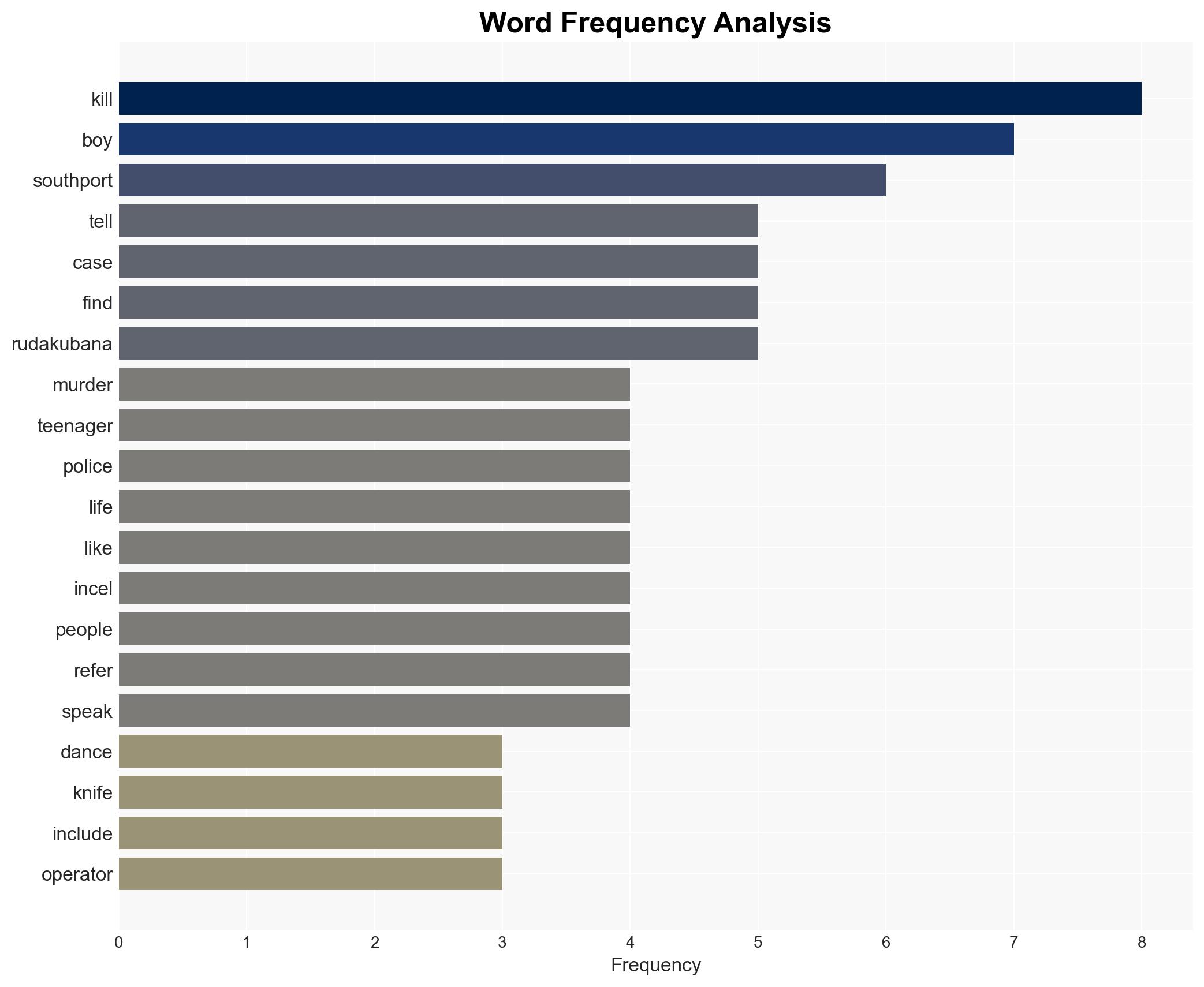
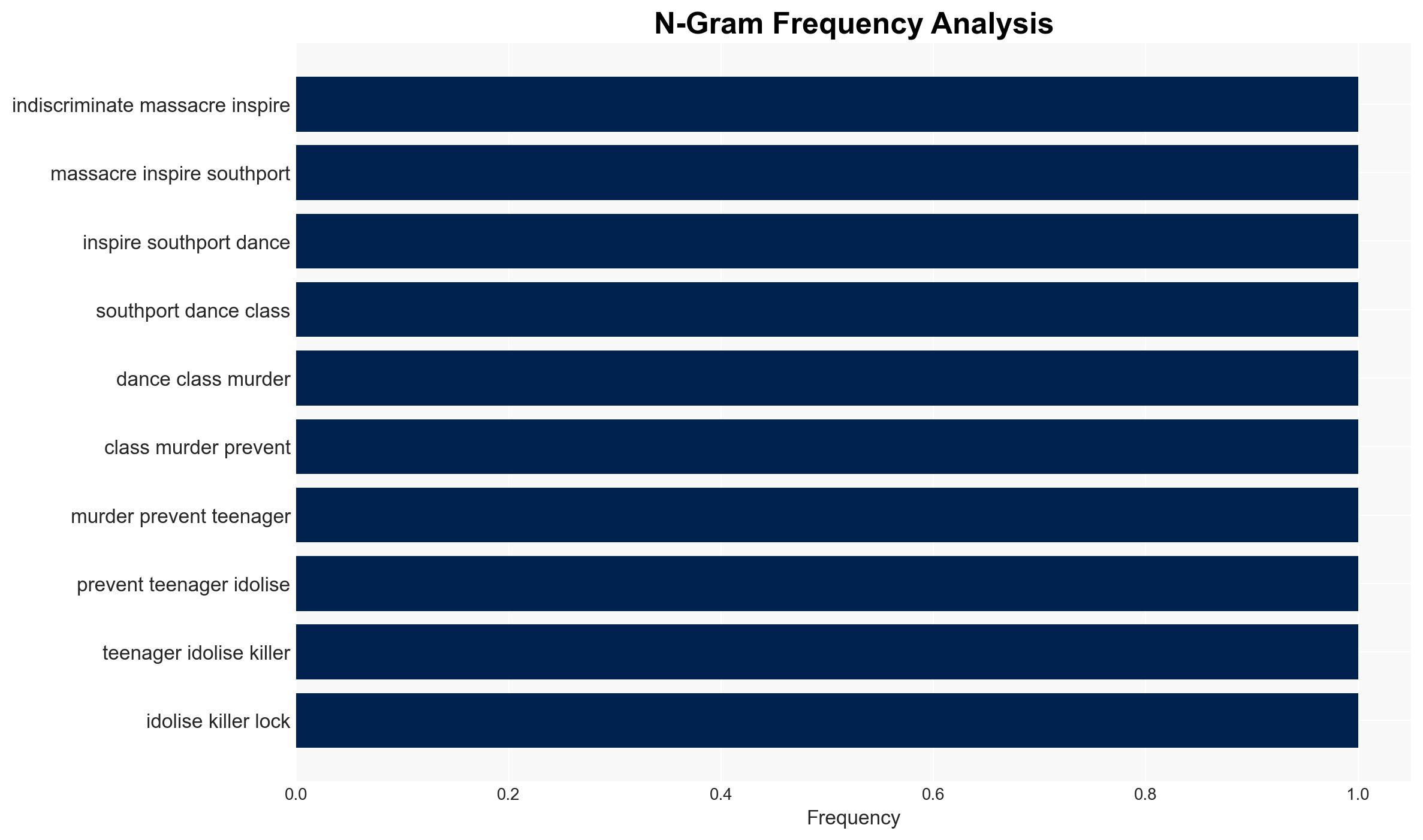
A potential mass casualty event inspired by incel ideology was averted when a teenager from Kirkby, Merseyside, called the police after being unable to leave his home. The individual had planned attacks on a primary school and an LGBT pride event. This incident underscores the persistent threat posed by radicalized individuals influenced by extremist online subcultures. Overall confidence in this assessment is moderate, given the limited information on the broader network or support structure.
2. Competing Hypotheses
- Hypothesis A: The teenager acted alone, driven by personal grievances and immersion in incel culture. Supporting evidence includes his self-reported lack of empathy, possession of extremist materials, and idolization of known incel attackers. Key uncertainties involve the extent of his online interactions and potential influences.
- Hypothesis B: The teenager was part of a broader network or influenced by external actors encouraging violent acts. Contradicting evidence includes the lack of reported communication with other extremists and his decision to call the police, suggesting a lack of external pressure or coordination.
- Assessment: Hypothesis A is currently better supported due to the absence of evidence indicating network involvement. Indicators that could shift this judgment include discovery of communications with other extremists or evidence of external encouragement.
3. Key Assumptions and Red Flags
- Assumptions: The teenager’s actions were primarily self-motivated; his online activity was not coordinated with others; incel culture remains a significant radicalizing influence.
- Information Gaps: Details on his online interactions and any potential contacts with other extremists; psychological evaluations that could provide insight into his motivations.
- Bias & Deception Risks: Potential bias in interpreting the teenager’s motivations based on limited data; risk of deception if the teenager minimized external influences during police interactions.
4. Implications and Strategic Risks
This development highlights the ongoing threat from individuals radicalized online, particularly within incel communities. The incident could prompt increased scrutiny and counter-radicalization efforts targeting these subcultures.
- Political / Geopolitical: Potential for increased legislative focus on online extremism and radicalization.
- Security / Counter-Terrorism: Heightened alertness to lone-actor threats and the need for improved monitoring of extremist online spaces.
- Cyber / Information Space: Challenges in tracking and countering radicalization in decentralized online communities.
- Economic / Social: Potential social tensions and stigmatization of individuals with similar profiles, impacting community cohesion.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of online incel communities; engage with local law enforcement for threat assessment and community outreach.
- Medium-Term Posture (1–12 months): Develop partnerships with tech companies to identify and mitigate extremist content; invest in mental health and counter-radicalization programs.
- Scenario Outlook:
- Best: Successful intervention and deradicalization efforts reduce similar threats.
- Worst: Increased incidents of violence inspired by incel ideology.
- Most-Likely: Continued sporadic threats from isolated individuals, prompting ongoing security measures.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
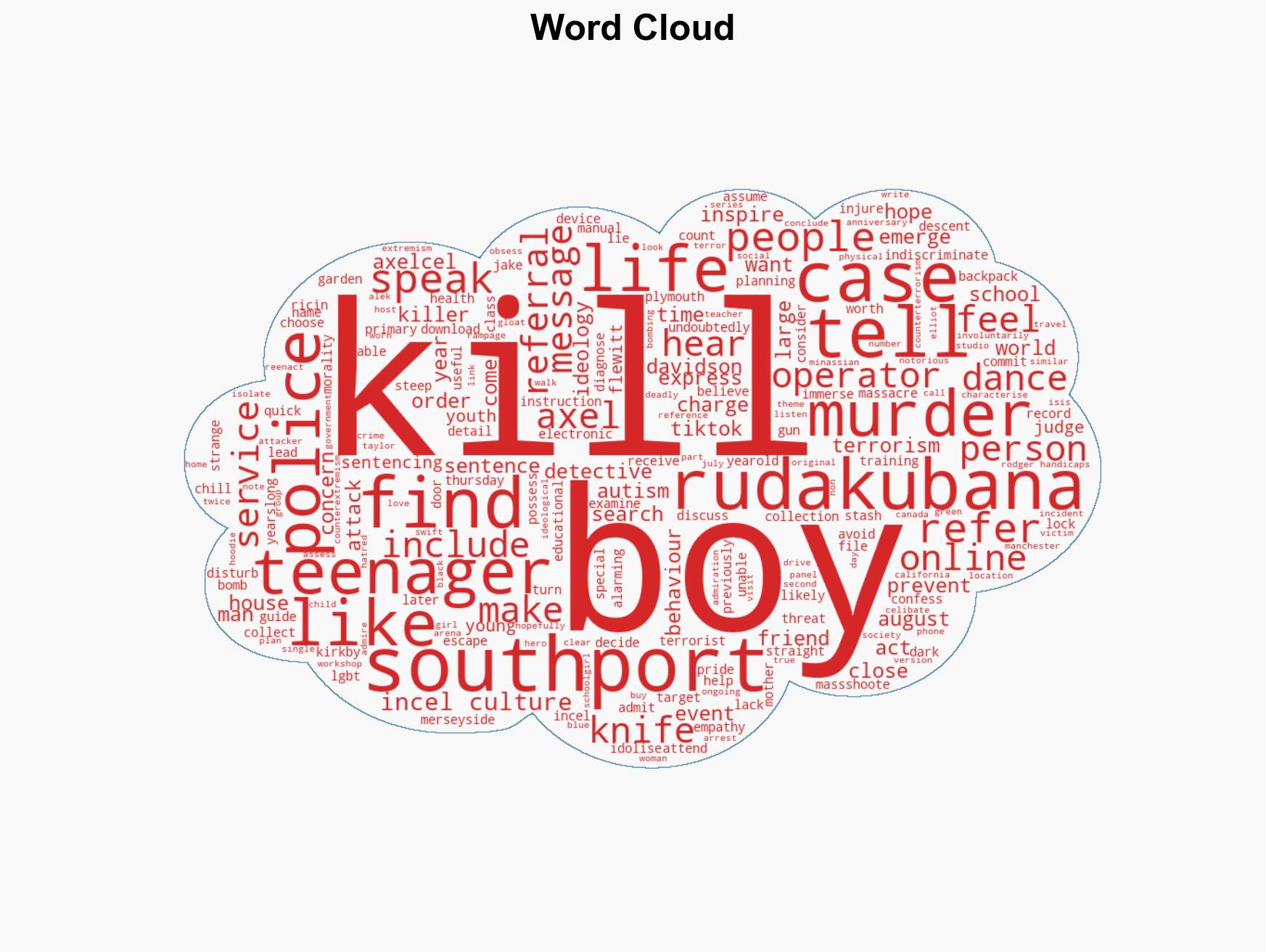
Counter-Terrorism, incel ideology, online radicalization, lone-actor threats, extremist content, law enforcement, community resilience
Structured Analytic Techniques Applied
- ACH 2.0: Reconstruct likely threat actor intentions via hypothesis testing and structured refutation.
- Indicators Development: Track radicalization signals and propaganda patterns to anticipate operational planning.
- Narrative Pattern Analysis: Analyze spread/adaptation of ideological narratives for recruitment/incitement signals.
Explore more:
Counter-Terrorism Briefs ·
Daily Summary ·
Support us