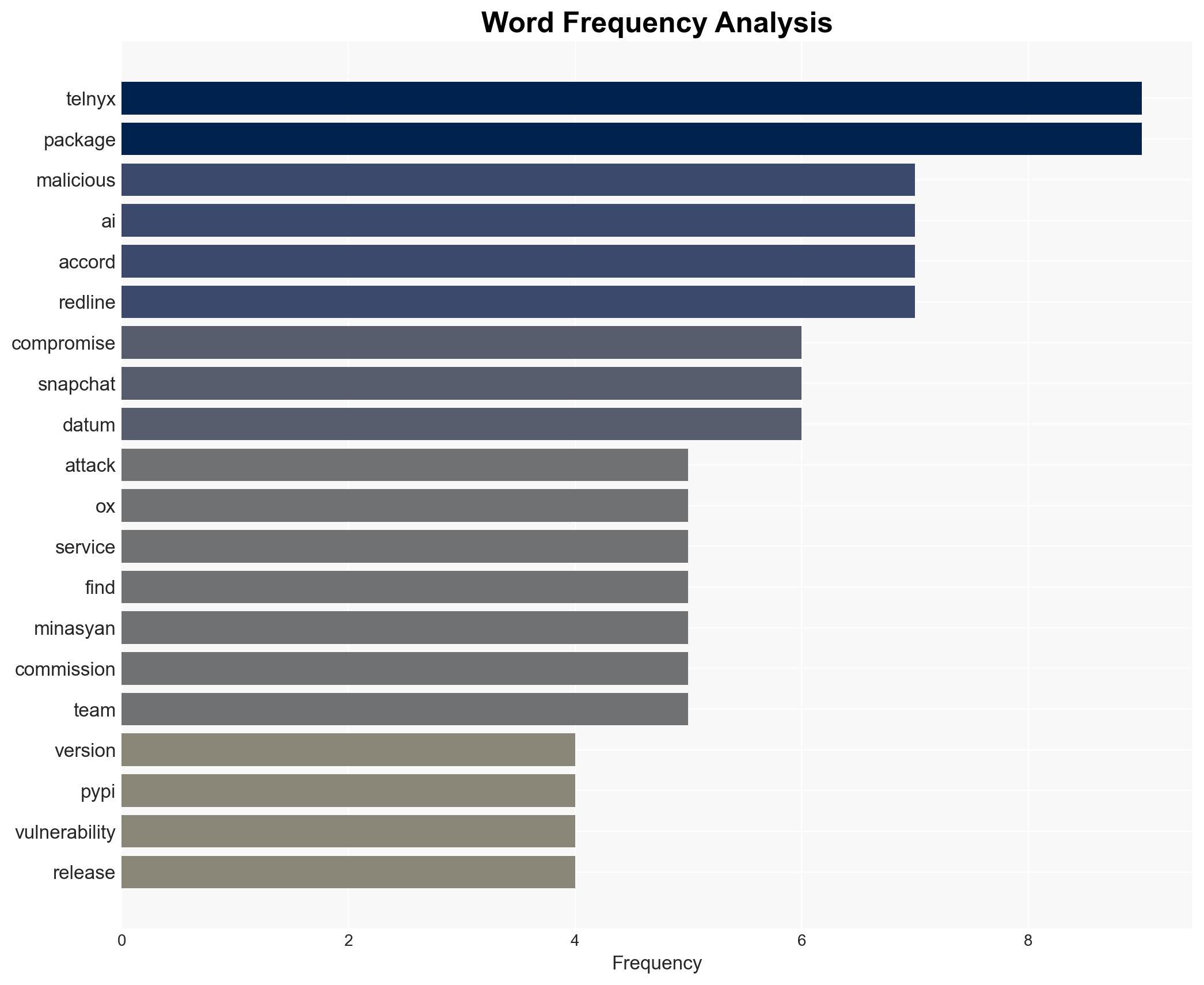
Telnyx targeted in new PyPI package attack linked to Trivy breach, delivering credential-stealing malware
Published on: 2026-03-30
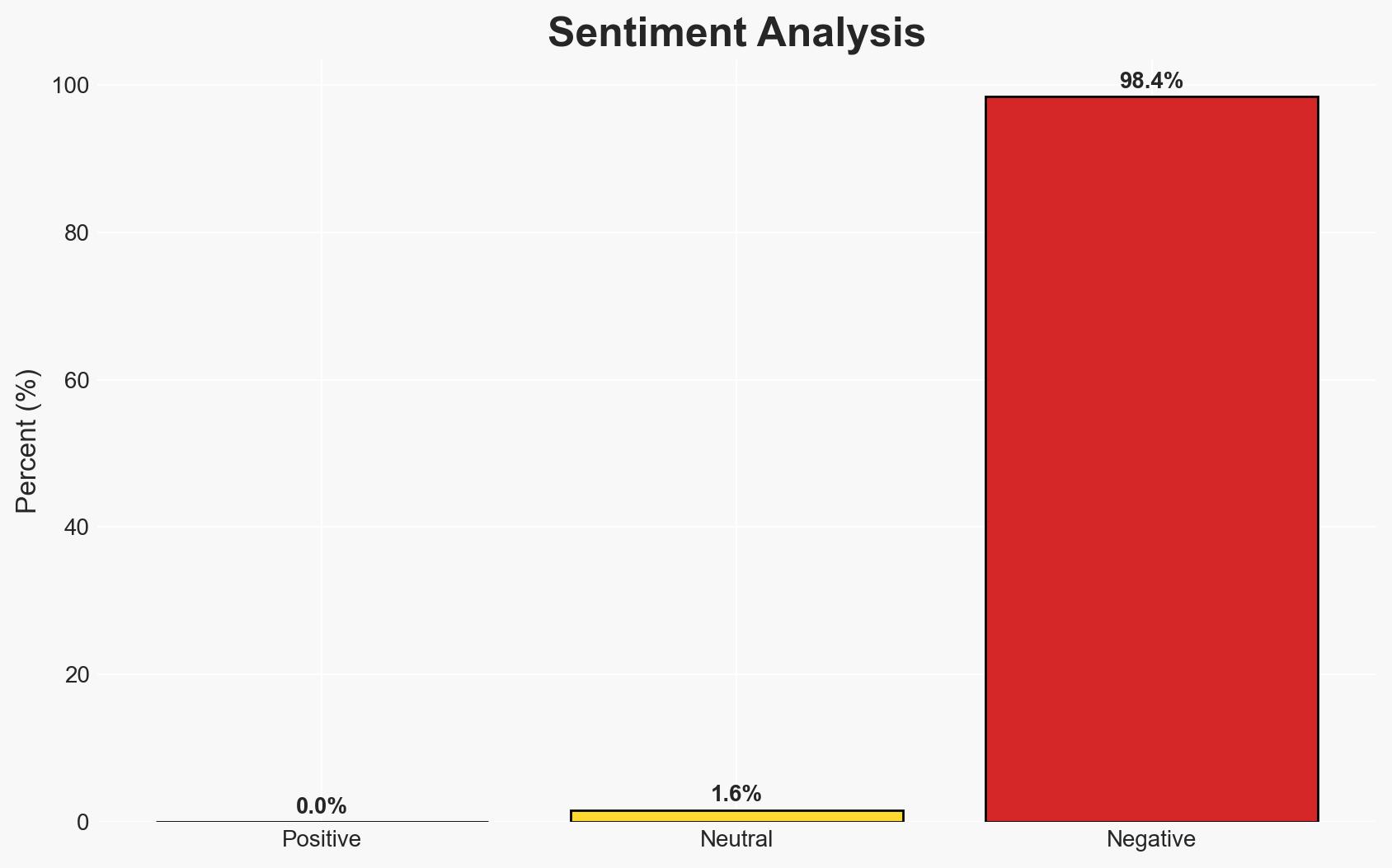
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Telnyx joins LiteLLM in latest PyPI package poisoning tied to Trivy breach
1. BLUF (Bottom Line Up Front)
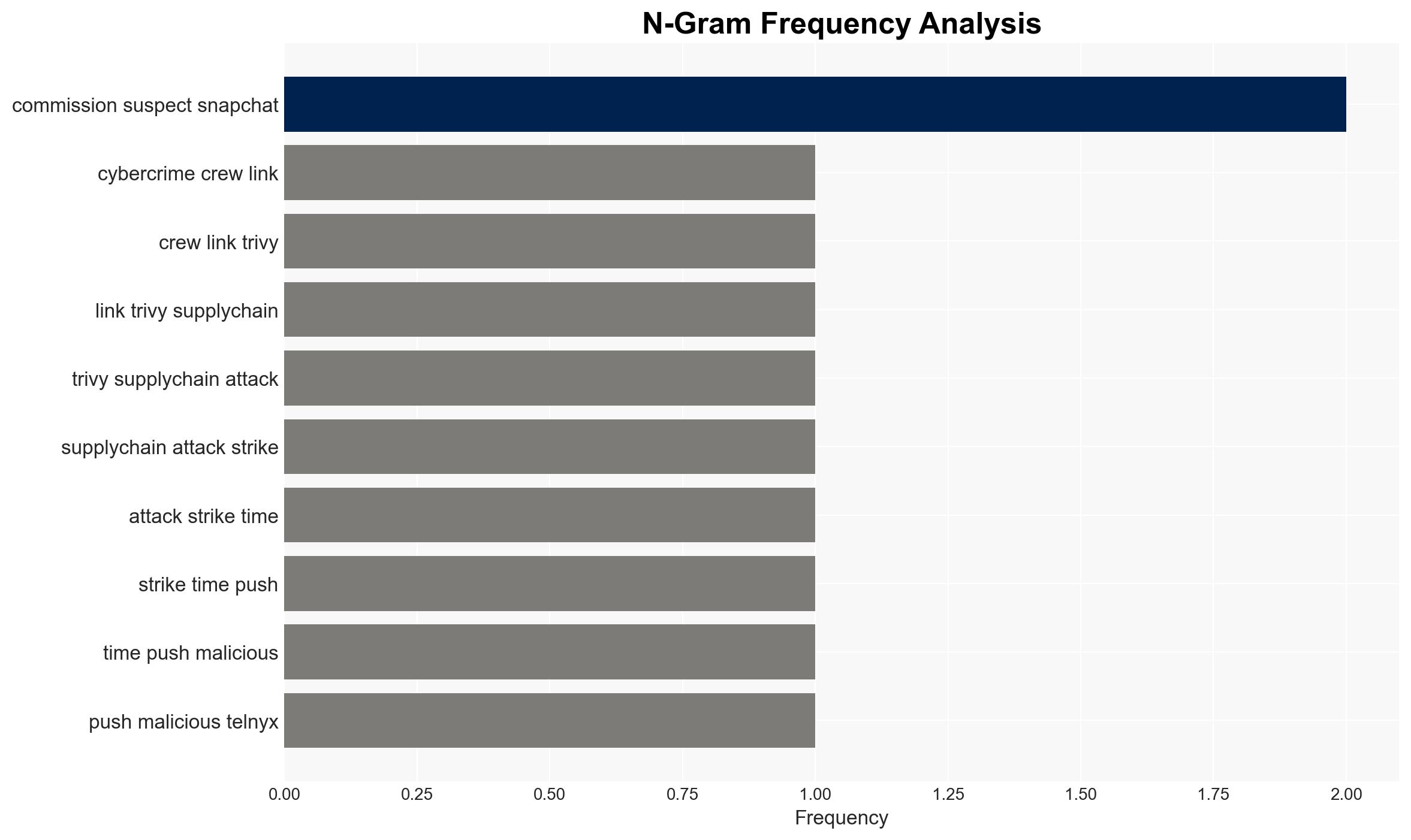
The cybercrime group TeamPCP has executed another supply-chain attack by compromising the PyPI distribution of Telnyx’s Python SDK, embedding a multi-stage infostealer. This incident follows a similar compromise involving LiteLLM linked to the Trivy breach. The attack potentially affects a significant number of developers and services due to the high download rate of the package. Overall confidence in this assessment is moderate, given the available evidence and ongoing investigation.
2. Competing Hypotheses
- Hypothesis A: TeamPCP is systematically targeting popular open-source packages to distribute malware, leveraging the high download rates to maximize impact. This is supported by the pattern of attacks on both LiteLLM and Telnyx, both linked to the Trivy breach. However, the exact motivations and end goals remain unclear.
- Hypothesis B: The attacks are opportunistic rather than systematic, with TeamPCP exploiting vulnerabilities as they are discovered without a broader strategic plan. This is contradicted by the similar methodologies used in both incidents, suggesting a more deliberate approach.
- Assessment: Hypothesis A is currently better supported due to the consistent pattern and methodology observed in the attacks. Key indicators that could shift this judgment include evidence of unrelated opportunistic attacks or a broader strategic manifesto from TeamPCP.
3. Key Assumptions and Red Flags
- Assumptions: TeamPCP has the technical capability to compromise widely used software packages; the group’s primary goal is to distribute credential-stealing malware; Telnyx’s infrastructure was not compromised beyond the Python package.
- Information Gaps: The full extent of the compromise’s impact on end-users; detailed motivations and objectives of TeamPCP; potential connections to other cybercrime groups.
- Bias & Deception Risks: Potential bias in relying on reports from Ox Security, which may have commercial interests; risk of deception from TeamPCP in misrepresenting their capabilities or intentions.
4. Implications and Strategic Risks
This development could lead to increased scrutiny of open-source software security and supply-chain vulnerabilities. It may also prompt a reassessment of security protocols among developers and organizations using affected packages.
- Political / Geopolitical: Potential for increased international cooperation on cybersecurity standards and responses to supply-chain attacks.
- Security / Counter-Terrorism: Heightened awareness and defensive measures against similar cyber threats; potential for increased law enforcement action against cybercrime groups.
- Cyber / Information Space: Increased focus on securing open-source repositories and enhancing detection mechanisms for malicious code.
- Economic / Social: Potential economic impact on affected companies and developers; erosion of trust in open-source software ecosystems.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor PyPI and other open-source repositories for similar attacks; advise developers to verify package integrity before installation; enhance incident response capabilities.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms for threat intelligence sharing; invest in security audits of critical software dependencies; promote best practices for secure software development.
- Scenario Outlook:
- Best Case: Enhanced security measures prevent further attacks, restoring confidence in open-source ecosystems.
- Worst Case: Continued attacks lead to significant disruptions and loss of trust in software supply chains.
- Most-Likely: Incremental improvements in security posture reduce but do not eliminate the risk of similar attacks.
6. Key Individuals and Entities
- TeamPCP (cybercrime group)
- Telnyx (VoIP and AI voice services provider)
- Ox Security (cybersecurity firm)
- Hambardzum Minasyan (alleged RedLine operator)
7. Thematic Tags
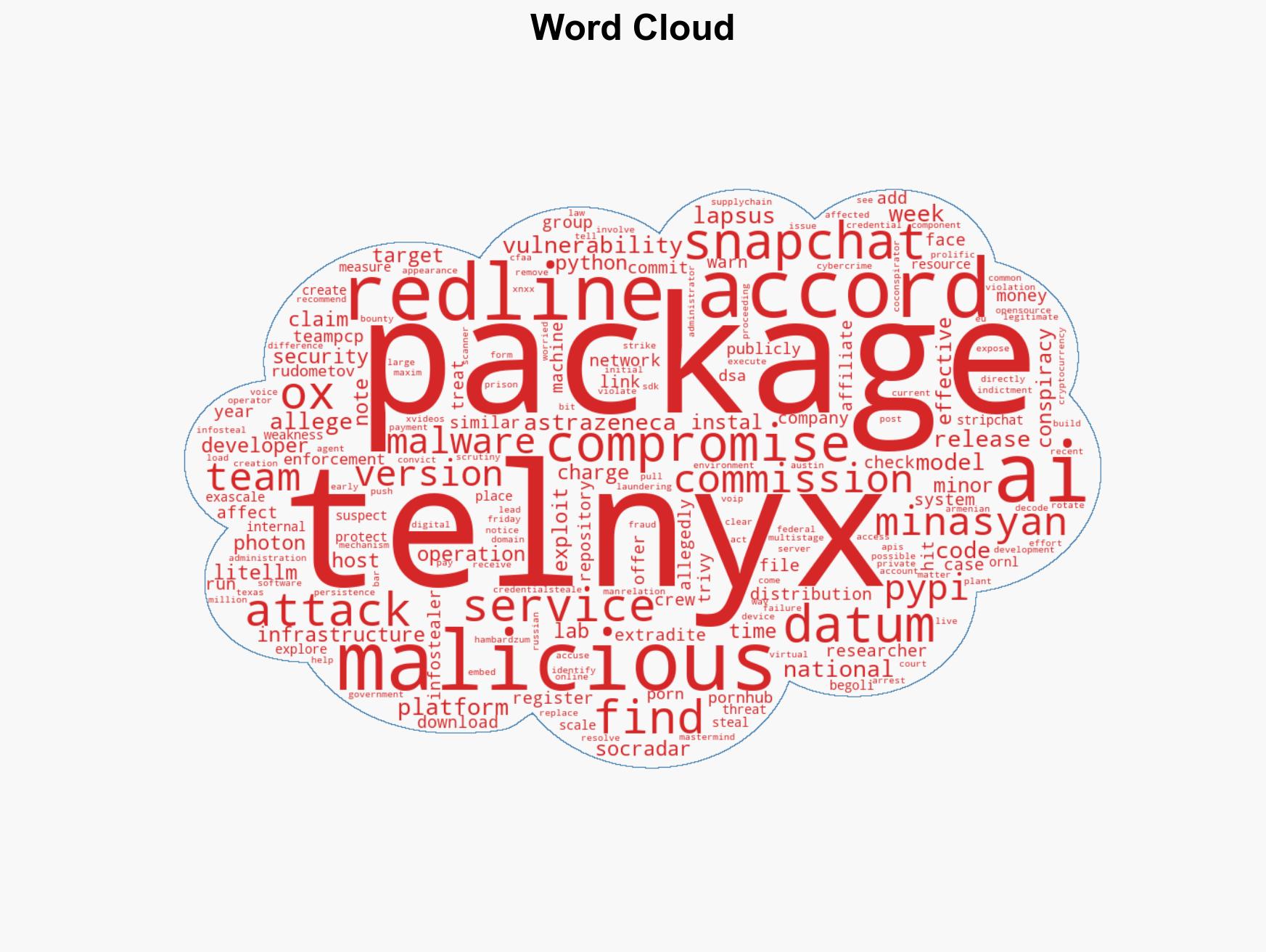
cybersecurity, supply-chain attack, cybercrime, open-source security, malware distribution, credential theft, software vulnerability
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us