Telus Digital faces major data breach as hackers claim to have stolen nearly 1,000TB of sensitive information.
Published on: 2026-03-12
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Hackers reportedly stole nearly 1000TB of data from Telus Digital
1. BLUF (Bottom Line Up Front)
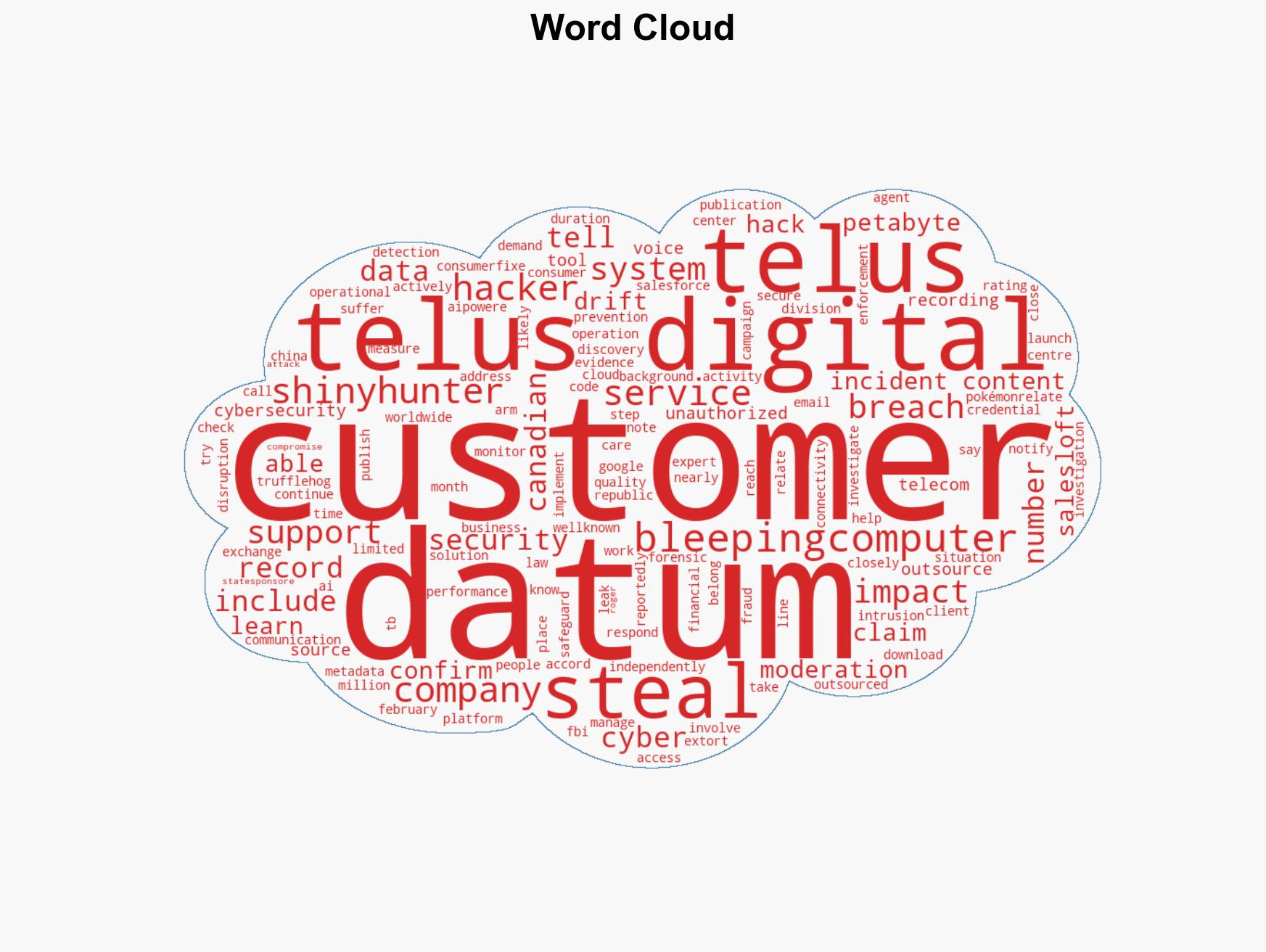
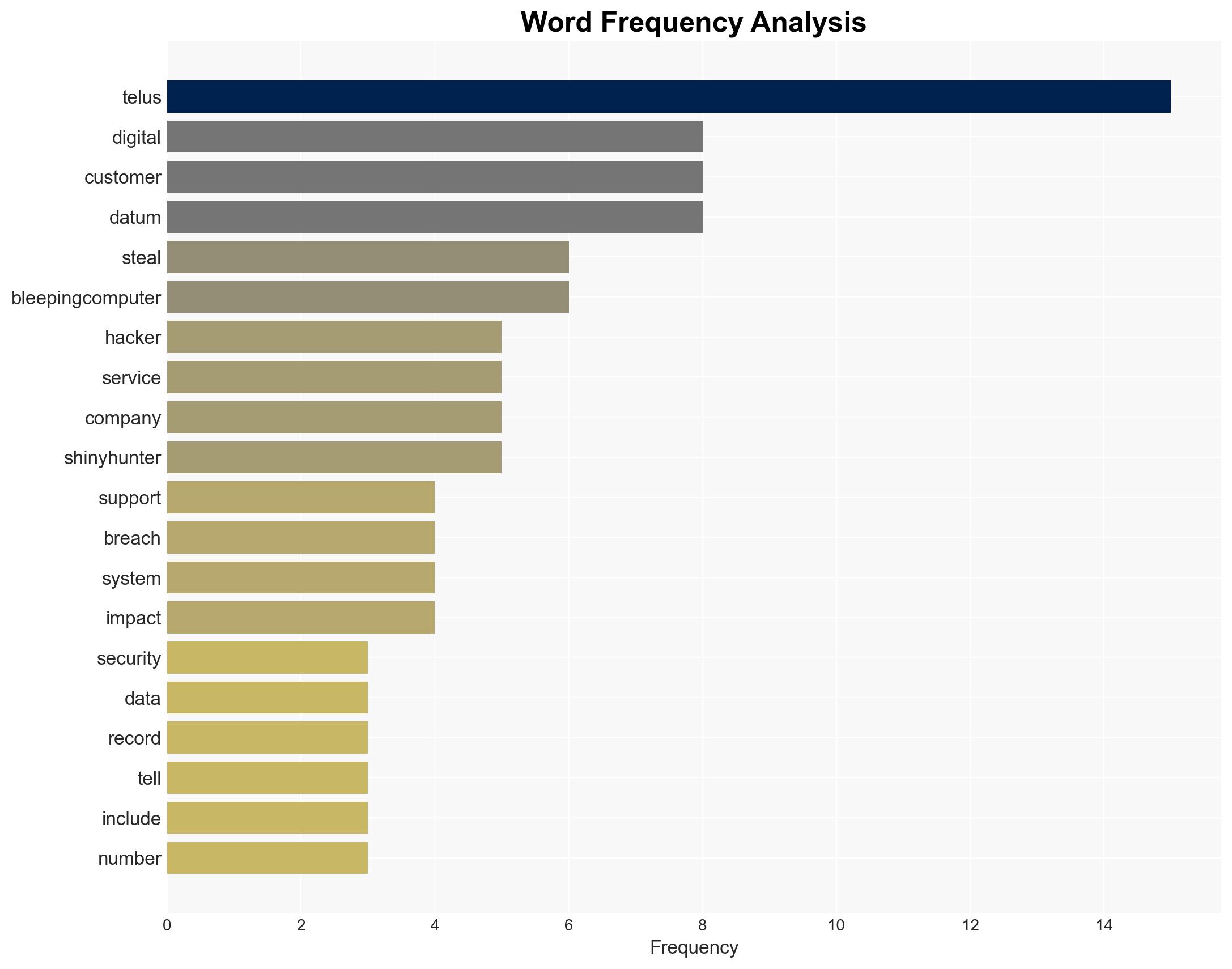
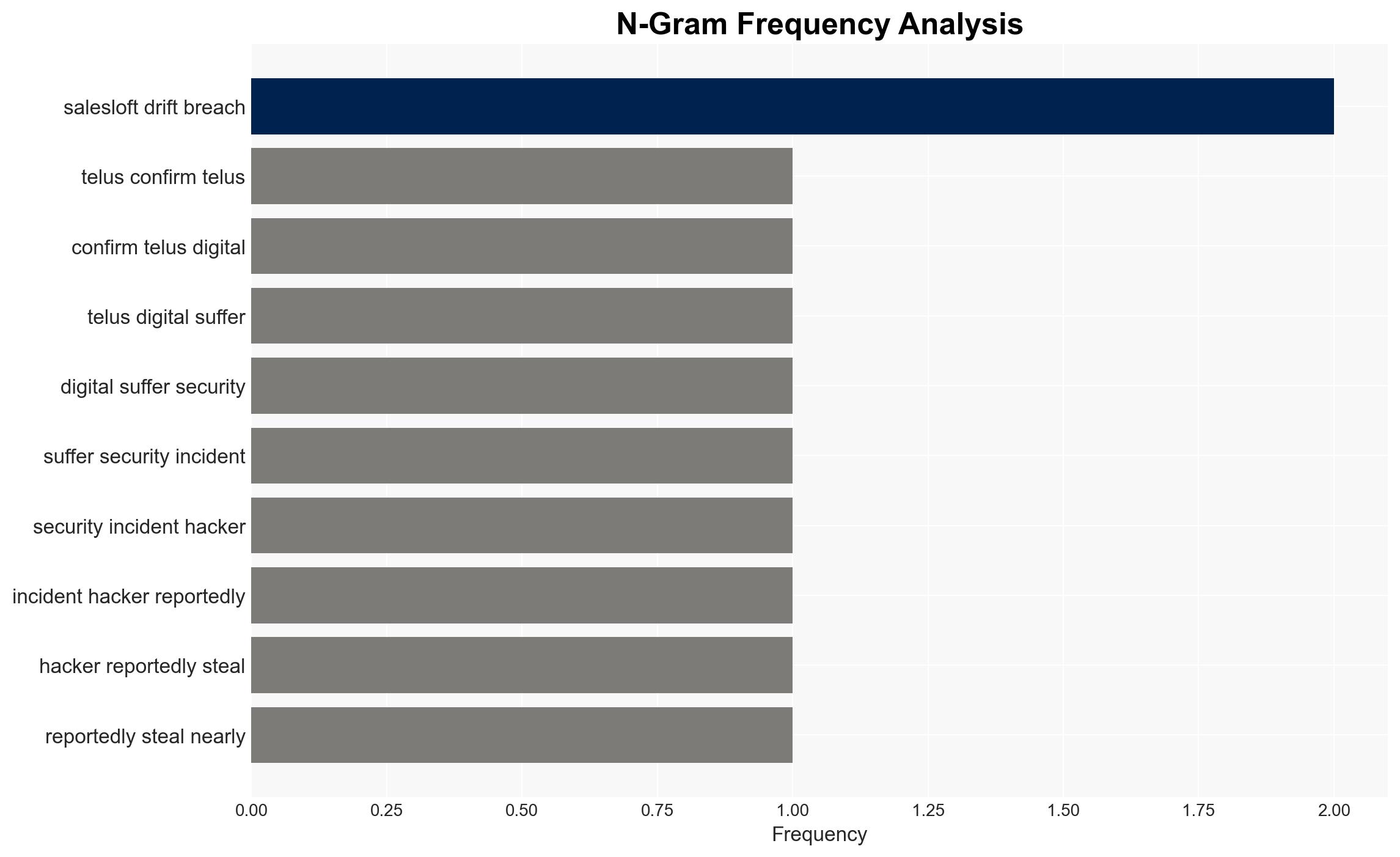
Hackers identified as ShinyHunters have reportedly stolen nearly 1,000TB of data from Telus Digital, impacting multiple companies and potentially compromising sensitive customer data. The breach was facilitated through credentials obtained from a previous Salesloft Drift breach. The most likely hypothesis is that ShinyHunters exploited existing vulnerabilities to conduct a large-scale data theft operation. This assessment is made with moderate confidence due to the lack of independent verification of all claims.
2. Competing Hypotheses
- Hypothesis A: ShinyHunters exploited vulnerabilities in Telus Digital’s systems using credentials from the Salesloft Drift breach to steal data. Supporting evidence includes the hackers’ claims and the reported use of trufflehog to extract data. Contradicting evidence includes the lack of independent confirmation of the full scope of the breach.
- Hypothesis B: The breach is exaggerated by ShinyHunters to extort Telus, with the actual data theft being significantly less than claimed. Supporting evidence includes the absence of independent verification of the 1,000TB claim and potential exaggeration for extortion purposes. Contradicting evidence includes specific details provided about the types of data stolen.
- Assessment: Hypothesis A is currently better supported due to the detailed method of breach and specific data types mentioned. However, confirmation of the breach’s full extent and independent verification could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The hackers’ claims are partially accurate; Telus Digital’s systems had exploitable vulnerabilities; ShinyHunters have the capability to manage and process large volumes of data.
- Information Gaps: Independent verification of the data volume stolen; confirmation of the impact on the 28 companies mentioned; detailed analysis of the stolen data’s content.
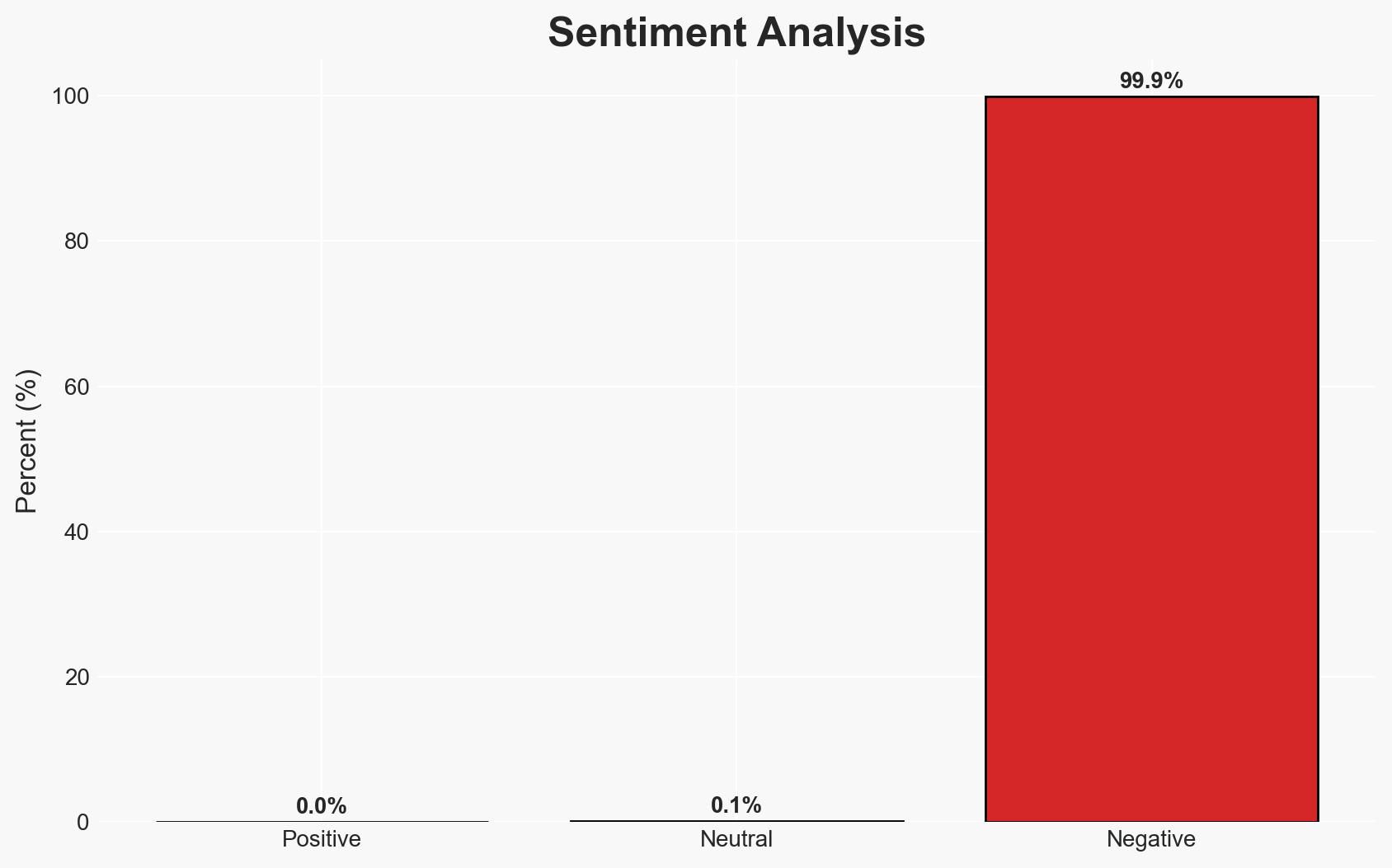
- Bias & Deception Risks: Potential exaggeration by ShinyHunters for extortion; reliance on hacker-provided information introduces bias; media reports may lack technical verification.
4. Implications and Strategic Risks
This development could lead to increased scrutiny on Telus Digital’s cybersecurity practices and potential regulatory actions. It may also embolden other hacker groups to target similar vulnerabilities.
- Political / Geopolitical: Potential diplomatic tensions if international companies are significantly affected.
- Security / Counter-Terrorism: Increased risk of further cyber-attacks on telecommunications and digital service providers.
- Cyber / Information Space: Heightened awareness and potential for increased cyber defense measures across the industry.
- Economic / Social: Potential financial losses for affected companies and erosion of customer trust in digital services.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive forensic investigation; enhance monitoring of Telus Digital’s systems; engage with affected companies to mitigate data misuse.
- Medium-Term Posture (1–12 months): Strengthen cybersecurity frameworks; develop partnerships for threat intelligence sharing; invest in employee training on cybersecurity best practices.
- Scenario Outlook:
- Best: Breach impact is contained, leading to improved cybersecurity measures.
- Worst: Data misuse results in significant financial and reputational damage.
- Most-Likely: Moderate impact with increased regulatory scrutiny and improved security posture.
6. Key Individuals and Entities
- ShinyHunters (hacker group)
- Telus Digital (affected entity)
- Salesloft Drift (source of compromised credentials)
- BleepingComputer (reporting entity)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, data breach, telecommunications, cybercrime, information security, extortion, digital services
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us