Texas Attorney General files lawsuits against companies linked to China over national security threats
Published on: 2026-02-24
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Texas AG takes action against Chinese-linked companies over national security concerns
1. BLUF (Bottom Line Up Front)
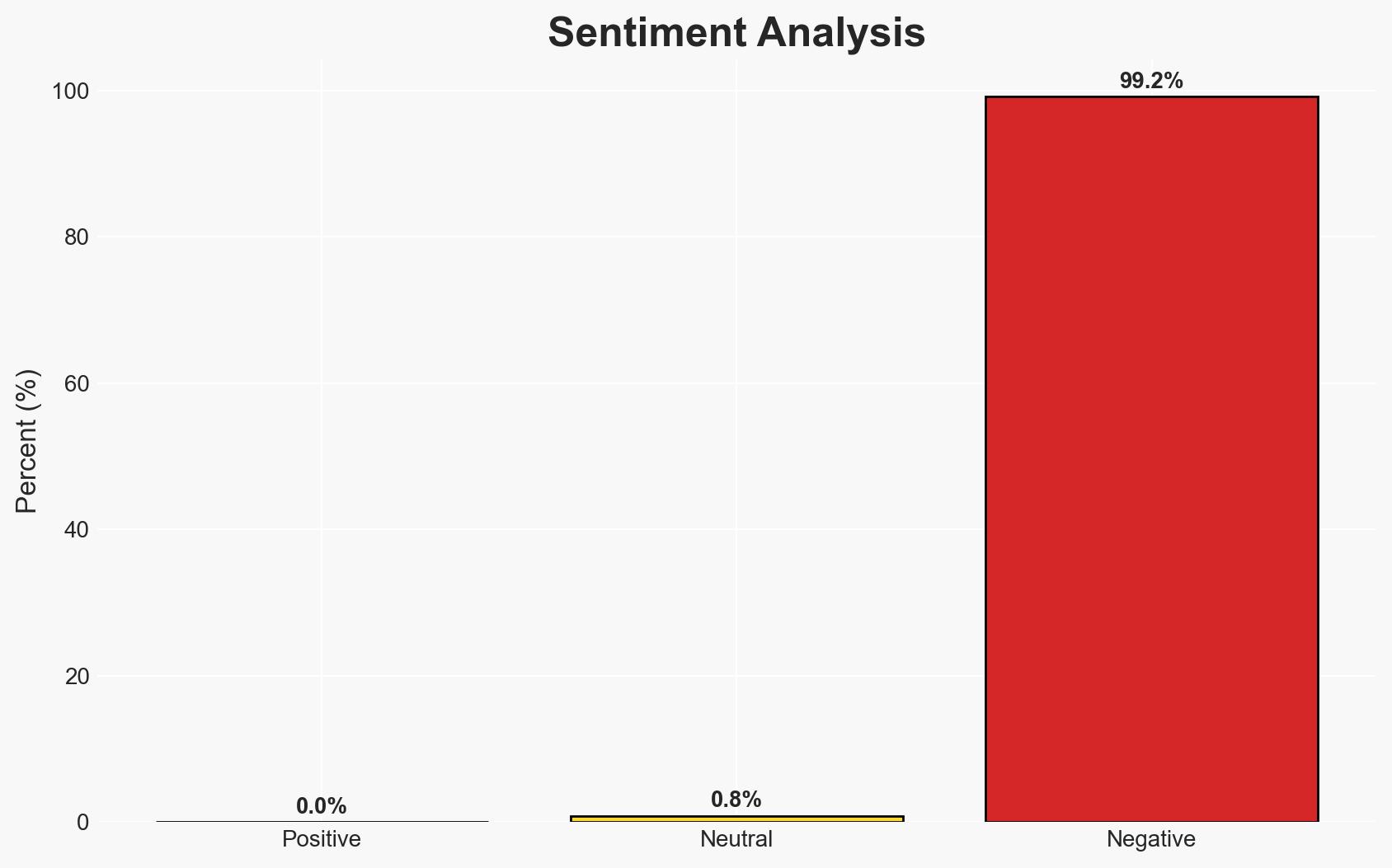
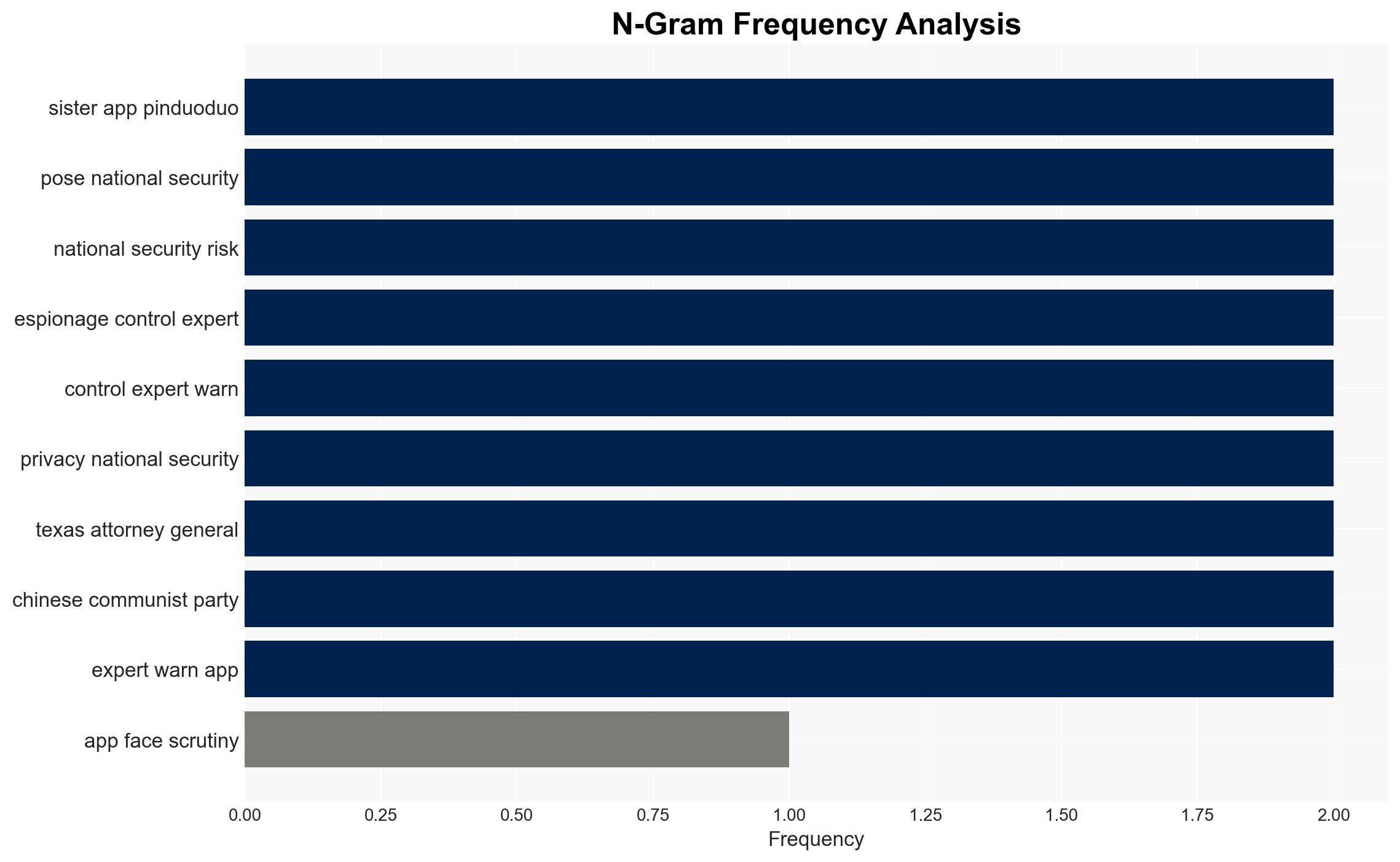
The Texas Attorney General’s lawsuits against Lorex and Temu highlight significant concerns over Chinese-linked data harvesting and potential surveillance activities, posing national security risks. The actions reflect growing scrutiny of Chinese technology firms’ influence in Western markets. The most likely hypothesis is that these companies maintain connections to the Chinese Communist Party (CCP) that could facilitate espionage. Overall confidence in this judgment is moderate due to existing information gaps and potential biases.
2. Competing Hypotheses
- Hypothesis A: Lorex and Temu are actively facilitating CCP-linked data collection and surveillance activities in the U.S., posing a national security threat. This is supported by past allegations against related entities and the lawsuits filed by the Texas AG. However, the transfer of Lorex ownership to a Taiwan-based firm introduces uncertainty about current CCP influence.
- Hypothesis B: Lorex and Temu are independent entities with no current operational ties to the CCP, and the allegations are based on outdated or misinterpreted information. Lorex’s denial of the allegations and the lack of direct evidence of ongoing CCP influence support this hypothesis.
- Assessment: Hypothesis A is currently better supported due to the historical context of CCP-linked activities and the pattern of legal actions against similar firms. Key indicators that could shift this judgment include concrete evidence of operational independence from the CCP or further legal findings.
3. Key Assumptions and Red Flags
- Assumptions: The CCP has a strategic interest in leveraging technology firms for intelligence purposes; U.S. legal actions are based on credible intelligence; Lorex’s ownership change does not fully sever CCP ties.
- Information Gaps: Detailed evidence of current CCP influence over Lorex and Temu; specific mechanisms of data collection and transmission to CCP entities.
- Bias & Deception Risks: Potential confirmation bias in interpreting Chinese tech activities as inherently malicious; possible misinformation or disinformation campaigns by involved entities.
4. Implications and Strategic Risks
This development could heighten tensions between the U.S. and China, impacting diplomatic and trade relations. It may also lead to increased regulatory scrutiny of foreign tech firms operating in the U.S., influencing market dynamics and consumer trust.
- Political / Geopolitical: Potential escalation in U.S.-China tech and trade conflicts; increased legislative actions targeting foreign tech firms.
- Security / Counter-Terrorism: Enhanced focus on securing critical infrastructure and consumer data from foreign influence.
- Cyber / Information Space: Potential for increased cyber defense measures and public awareness campaigns regarding data privacy.
- Economic / Social: Possible disruptions in tech markets and consumer behavior shifts due to privacy concerns.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase monitoring of CCP-linked tech activities; engage with international partners to share intelligence and coordinate responses.
- Medium-Term Posture (1–12 months): Develop resilience measures for critical infrastructure; foster public-private partnerships to enhance cybersecurity capabilities.
- Scenario Outlook: Best: Clear evidence of independence from CCP emerges, reducing tensions. Worst: Escalation of legal and diplomatic conflicts with China. Most-Likely: Continued scrutiny and regulatory actions against Chinese-linked tech firms.
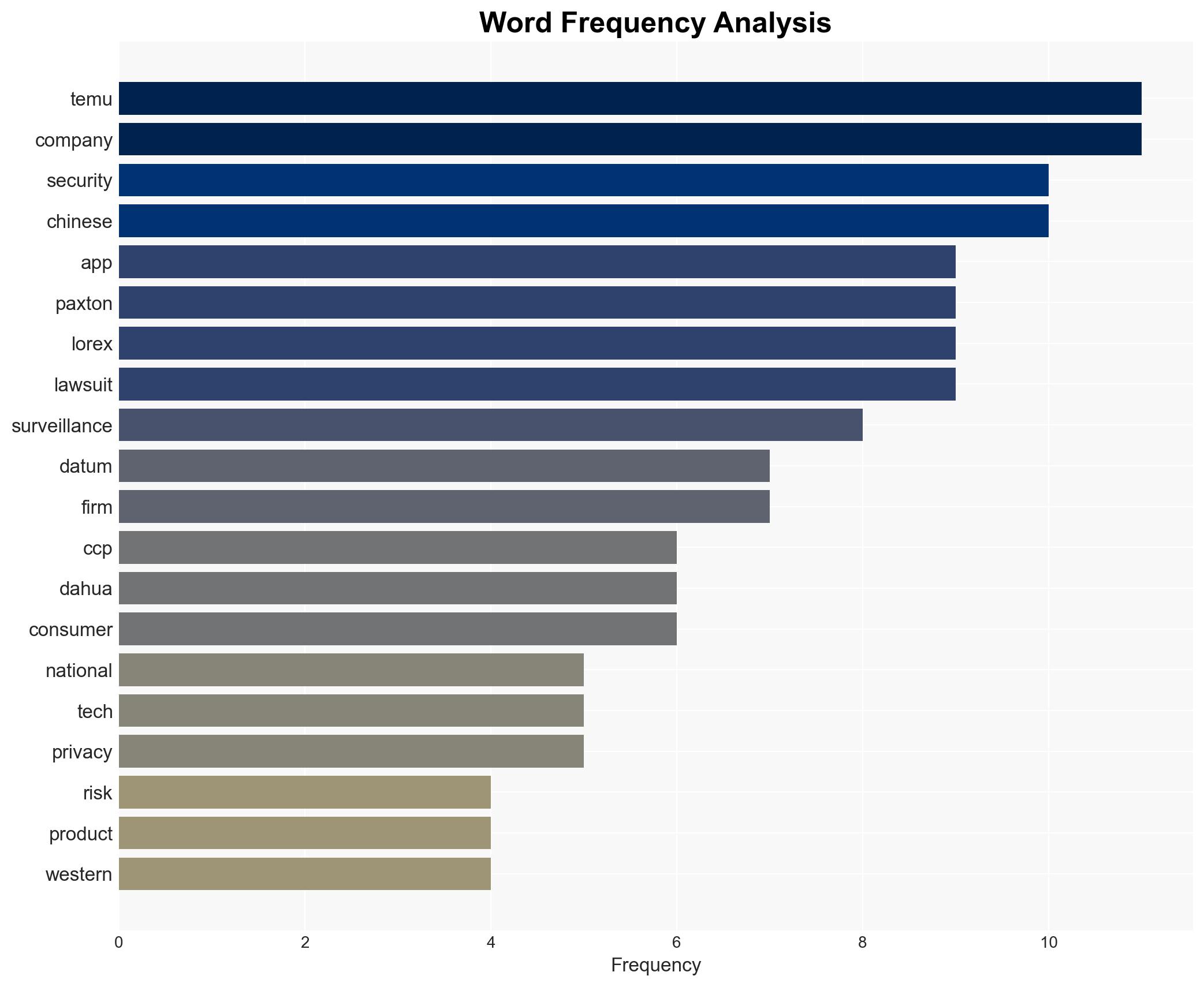
6. Key Individuals and Entities
- Ken Paxton (Texas Attorney General)
- Lorex (Surveillance camera company)
- Temu (E-commerce app)
- Dahua Technology (Chinese firm)
- Skywatch (Taiwan-based firm)
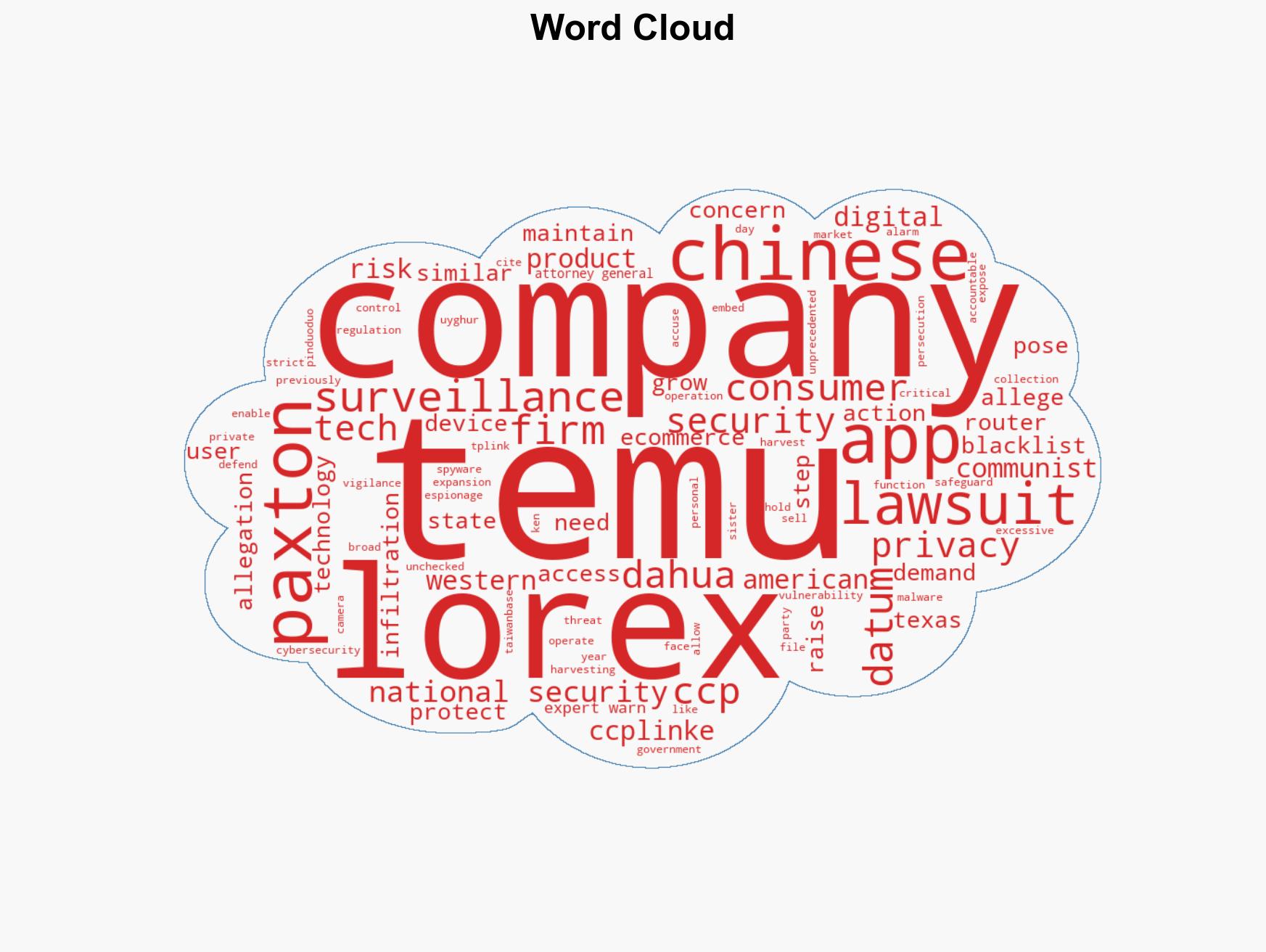
7. Thematic Tags
cybersecurity, national security, Chinese tech, data privacy, CCP surveillance, legal actions, U.S.-China relations
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
- Causal Layered Analysis (CLA): Empirical → systemic → worldview → myth layers.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us