Texas Governor Initiates Cybersecurity Assessment for Chinese-Made Medical Devices in State Facilities
Published on: 2026-03-14
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Texas Governor Directs Review of Chinese-Made Medical Device Cybersecurity
1. BLUF (Bottom Line Up Front)
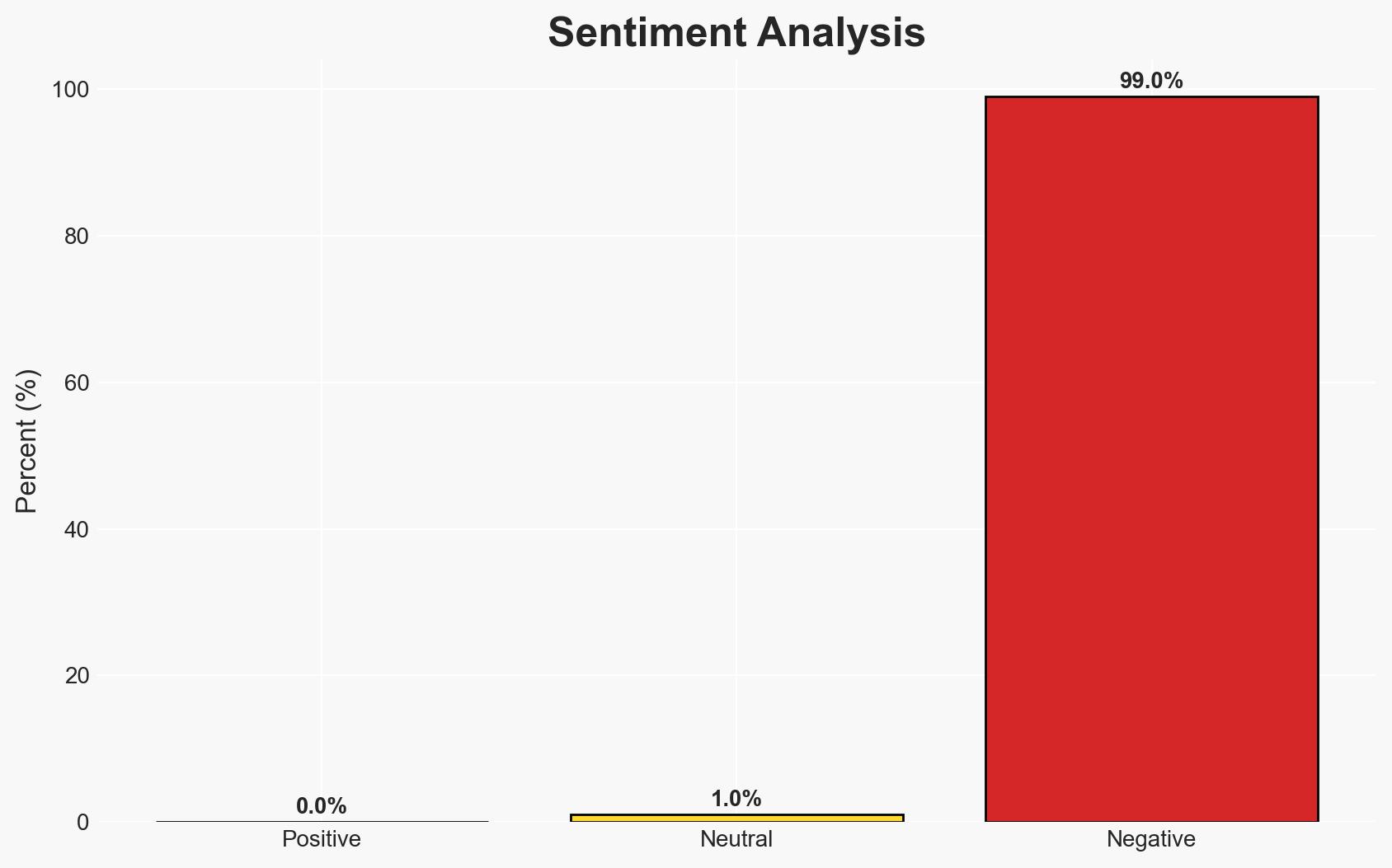
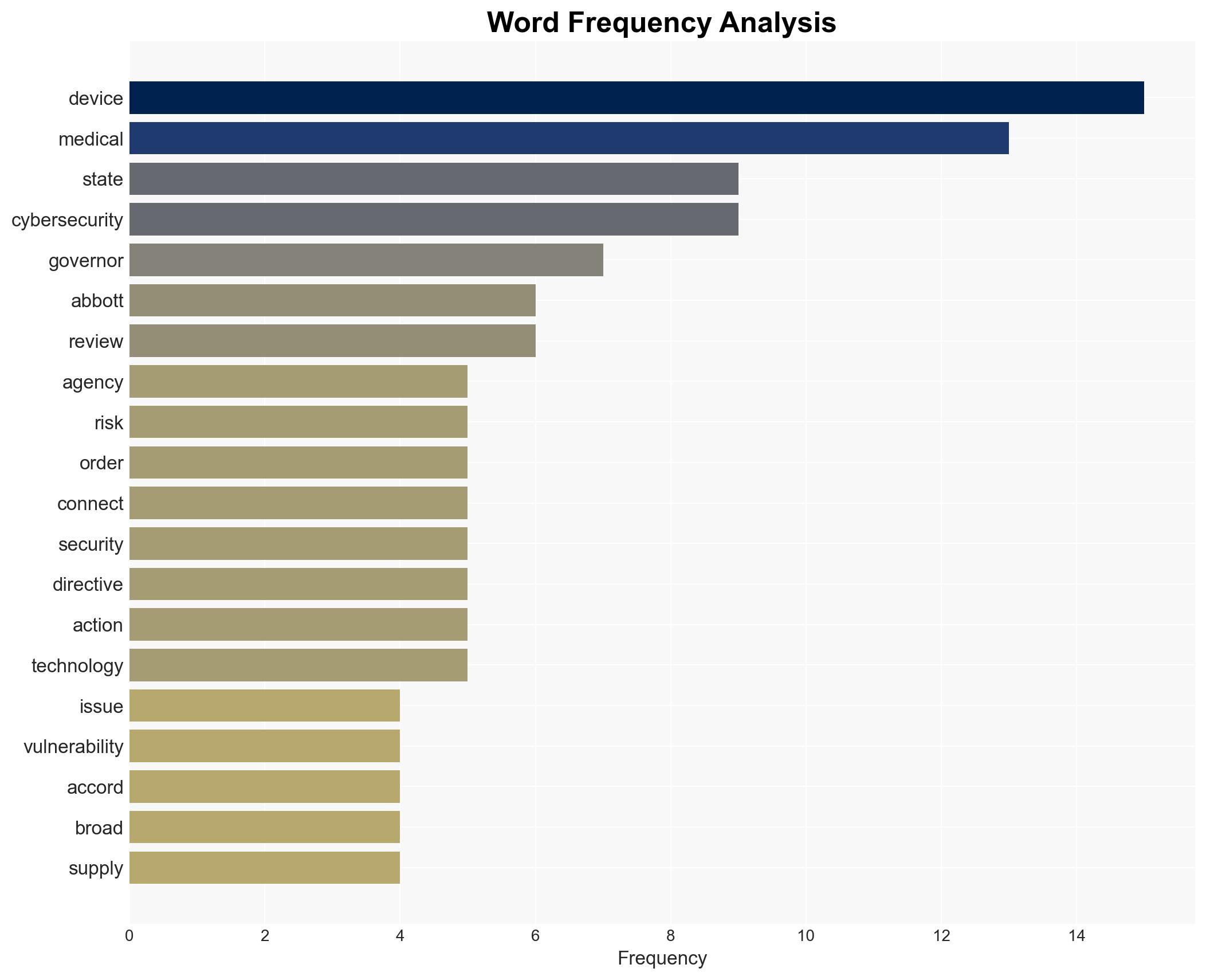
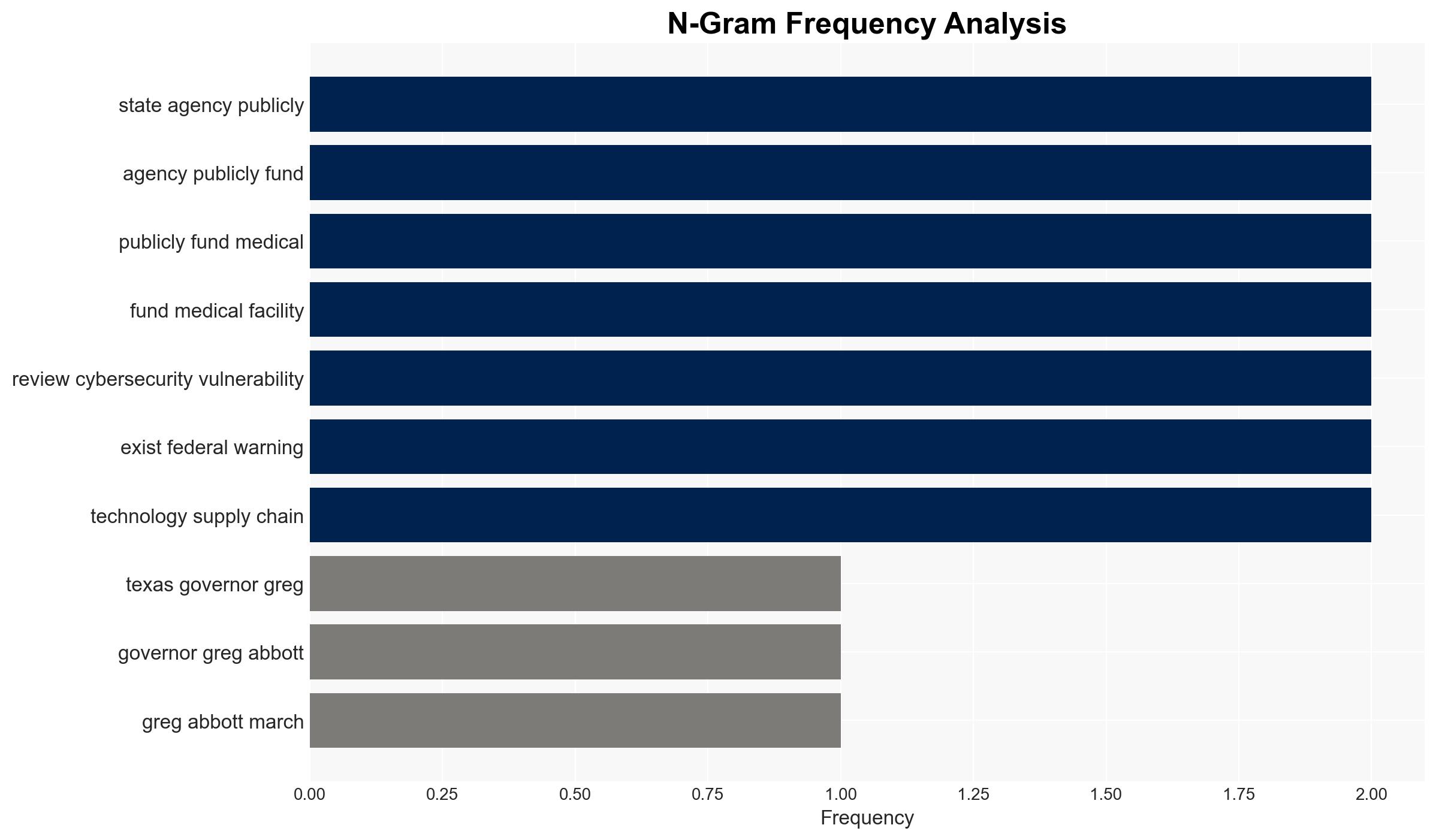
Governor Greg Abbott’s directive to review cybersecurity vulnerabilities in Chinese-made medical devices reflects heightened concerns over potential espionage and data breaches. The initiative primarily affects Texas state agencies and publicly funded medical facilities. The most likely hypothesis is that this action is a precautionary measure in response to federal warnings, with moderate confidence due to existing gaps in specific threat identification.
2. Competing Hypotheses
- Hypothesis A: The directive is a proactive measure to mitigate potential cybersecurity threats from Chinese-made medical devices, supported by federal warnings and the integration of these devices into critical healthcare infrastructure. Key uncertainties include the absence of specific threat incidents and the lack of named manufacturers or devices.
- Hypothesis B: The directive is primarily a political maneuver aimed at reinforcing a broader geopolitical stance against China, with cybersecurity concerns as a secondary justification. Evidence includes the lack of specific incidents or data breaches linked to these devices in Texas.
- Assessment: Hypothesis A is currently better supported due to the alignment with existing federal advisories and the growing integration of IoT in healthcare, which increases vulnerability. Indicators that could shift this judgment include the emergence of specific threat incidents or changes in federal policy.
3. Key Assumptions and Red Flags
- Assumptions: The directive is based on credible federal warnings; Chinese-made devices pose a unique cybersecurity risk; Texas agencies can effectively assess and mitigate these risks.
- Information Gaps: Specific vulnerabilities or incidents involving the targeted devices; detailed criteria for the review process; the scope of potential foreign influence or espionage.
- Bias & Deception Risks: Potential political bias against China influencing the directive; lack of transparency in the review process; possible underestimation of non-Chinese device vulnerabilities.
4. Implications and Strategic Risks
This development could lead to increased scrutiny of foreign-manufactured devices, influencing procurement policies and international relations. The directive may also prompt similar actions in other states or at the federal level.
- Political / Geopolitical: Potential escalation in U.S.-China tensions; influence on state and federal procurement policies.
- Security / Counter-Terrorism: Enhanced focus on cybersecurity in healthcare; potential for increased state-level cybersecurity initiatives.
- Cyber / Information Space: Increased awareness and potential for improved cybersecurity measures in medical IoT devices.
- Economic / Social: Potential impact on supply chains and costs for medical facilities; public perception of foreign-manufactured technology.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive risk assessment of existing medical devices; establish a task force to oversee the review process; engage with federal agencies for intelligence sharing.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms; invest in training for state agency staff; explore alternative suppliers for medical devices.
- Scenario Outlook:
- Best: Enhanced cybersecurity measures lead to reduced risks and improved trust in medical devices.
- Worst: Escalation in geopolitical tensions results in supply chain disruptions and increased costs.
- Most-Likely: Incremental improvements in cybersecurity with ongoing political rhetoric against foreign influence.
6. Key Individuals and Entities
- Governor Greg Abbott
- Texas state agencies
- Publicly funded medical facilities in Texas
- U.S. Food and Drug Administration
- Chinese medical device manufacturers (not specifically named)
7. Thematic Tags
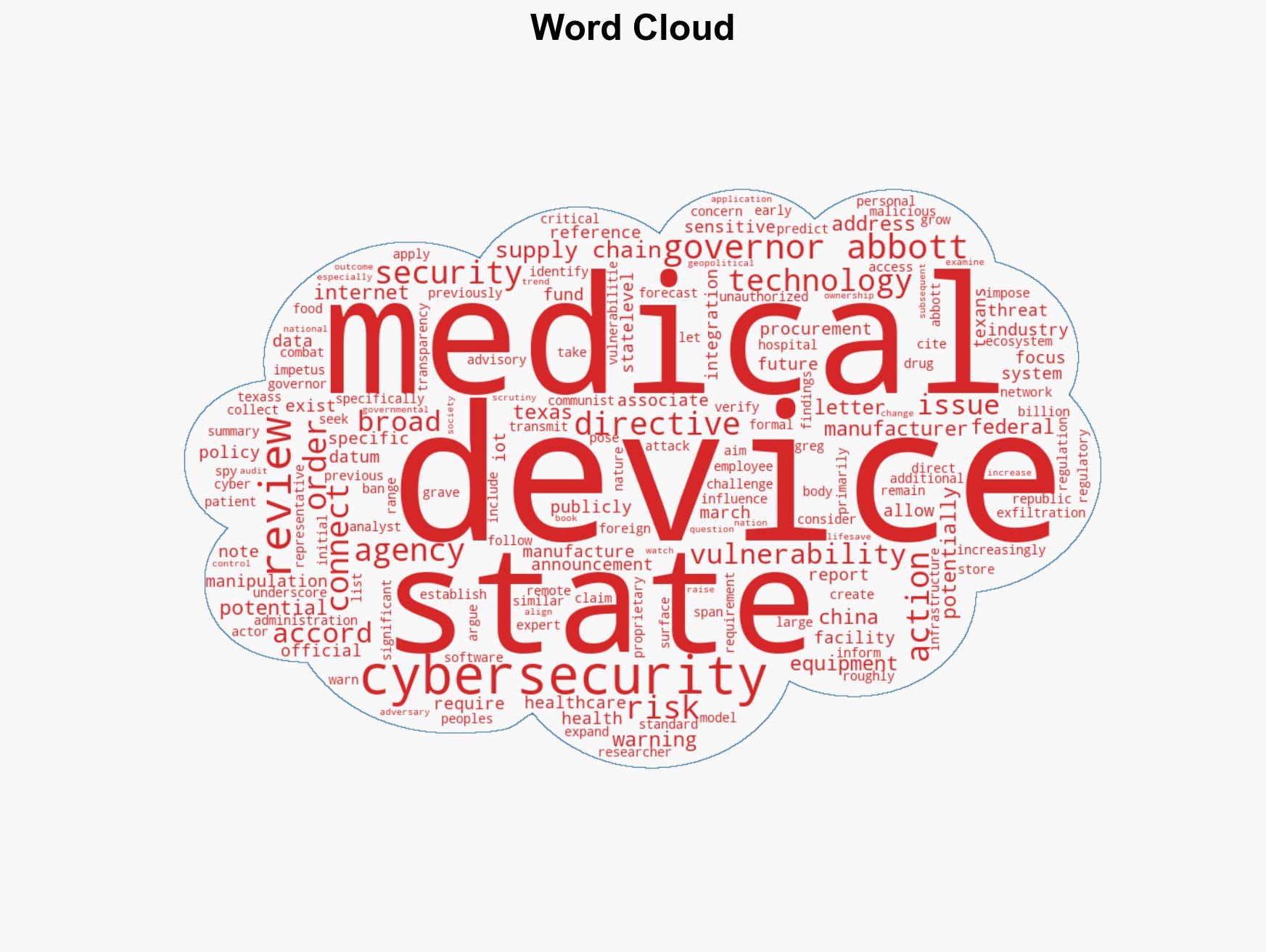
cybersecurity, medical devices, U.S.-China relations, state policy, IoT vulnerabilities, healthcare security, supply chain risk
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us