The Evolving Threat Landscape: AI’s Role in Modern Cybersecurity Challenges
Published on: 2026-03-04
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Cybersecurity in the AI Era
1. BLUF (Bottom Line Up Front)
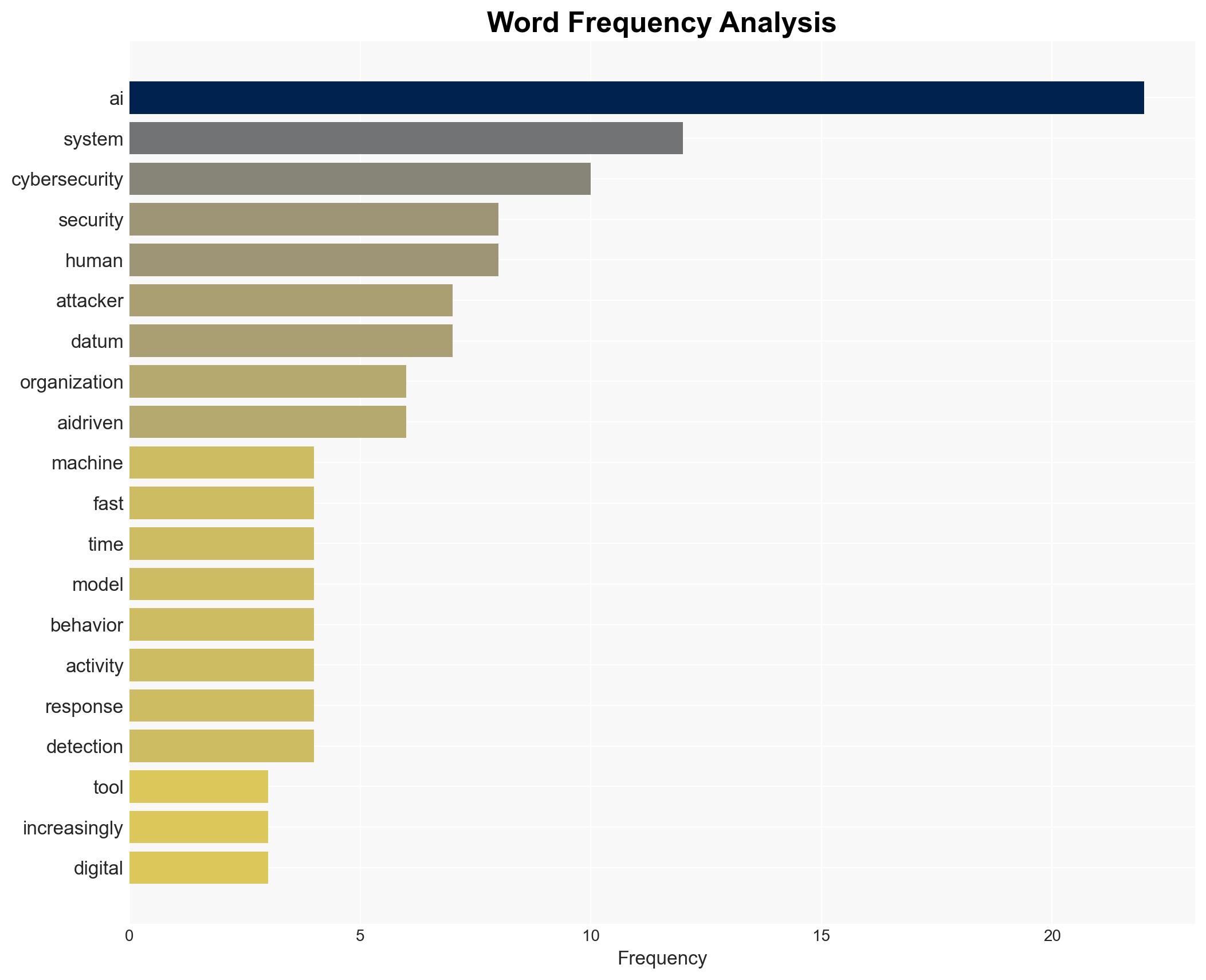
The dual-use nature of AI in cybersecurity has led to an arms race between cybercriminals and defenders, significantly increasing the sophistication of attacks and defenses. This development affects a wide range of industries, with large enterprises being particularly vulnerable. The most likely hypothesis is that AI will continue to enhance both offensive and defensive cyber capabilities, with moderate confidence in this assessment due to rapid technological advancements and evolving threat landscapes.
2. Competing Hypotheses
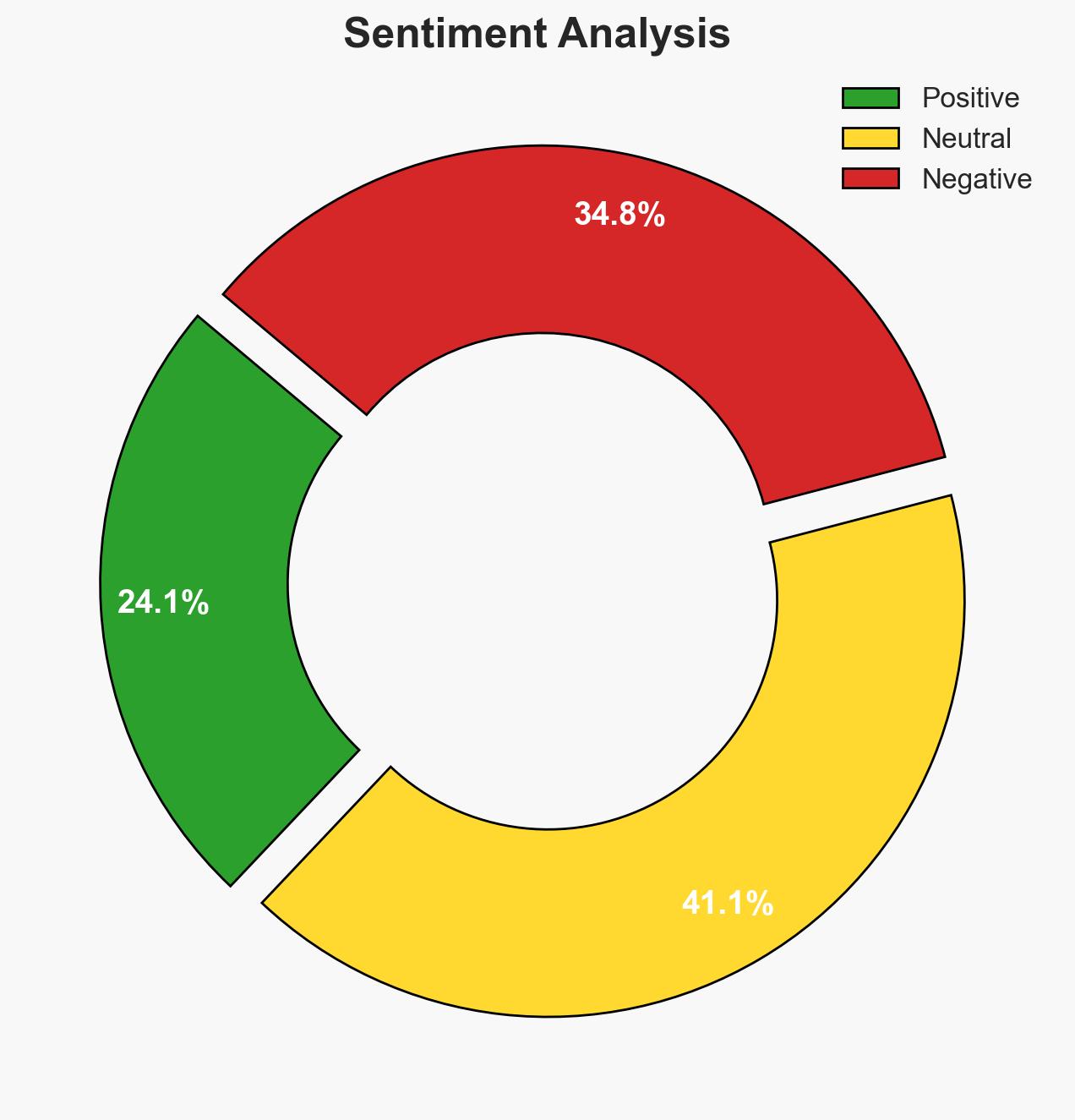
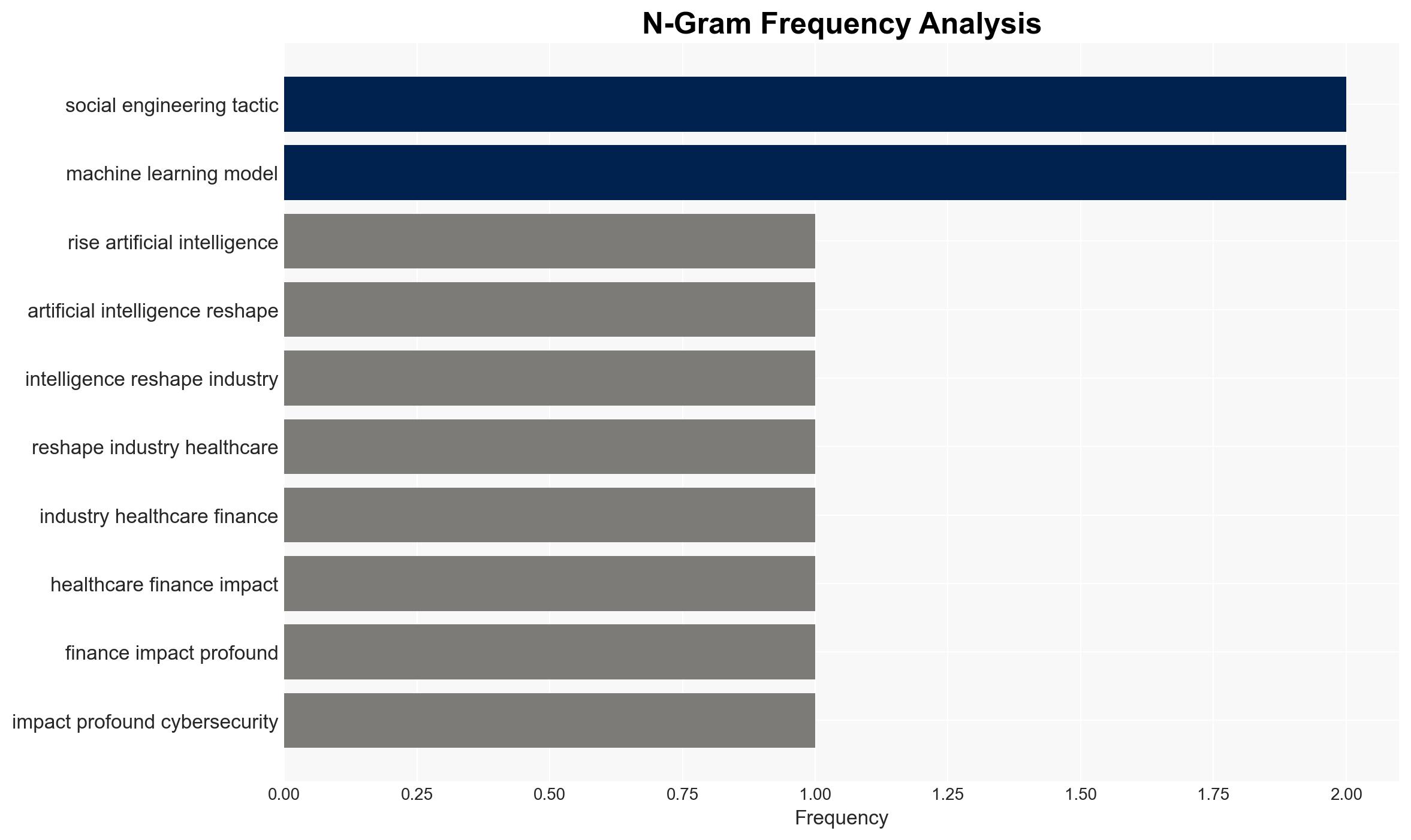
- Hypothesis A: AI will predominantly benefit cybercriminals, leading to more frequent and successful attacks. This is supported by the ability of AI to automate and enhance attack techniques such as phishing and deepfakes. However, uncertainties include the pace of defensive AI development and regulatory interventions.
- Hypothesis B: AI will primarily strengthen cybersecurity defenses, reducing the overall success rate of cyberattacks. Evidence includes the deployment of AI-driven security platforms by major companies and the adoption of zero-trust models. Contradicting this is the rapid adaptation of AI by attackers.
- Assessment: Hypothesis B is currently better supported due to the proactive integration of AI in cybersecurity by major technology firms and the development of autonomous response systems. Key indicators that could shift this judgment include breakthroughs in offensive AI capabilities or significant regulatory changes.
3. Key Assumptions and Red Flags
- Assumptions: AI technology will continue to advance at a rapid pace; organizations will invest in AI-driven security solutions; regulatory frameworks will evolve to address AI-related threats.
- Information Gaps: Detailed data on the effectiveness of AI-driven defenses versus AI-enhanced attacks; insights into the regulatory landscape’s impact on AI in cybersecurity.
- Bias & Deception Risks: Potential bias in favor of AI solutions due to industry investment; manipulation of AI systems by adversaries to produce false positives or negatives.
4. Implications and Strategic Risks
The integration of AI in cybersecurity is likely to intensify, with both attackers and defenders leveraging AI to gain an edge. This dynamic could lead to an escalation in the sophistication of cyber threats and defenses.
- Political / Geopolitical: Potential for increased cyber conflict between nation-states leveraging AI for offensive operations.
- Security / Counter-Terrorism: Enhanced threat detection capabilities may improve counter-terrorism efforts, but also increase the complexity of threat landscapes.
- Cyber / Information Space: AI-driven misinformation and deepfakes could undermine trust in digital communications and information integrity.
- Economic / Social: Increased cybersecurity costs for businesses; potential for economic disruption from successful AI-enhanced cyberattacks.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of AI-related cyber threats; increase awareness and training on AI-driven attack vectors.
- Medium-Term Posture (1–12 months): Develop partnerships with AI technology providers; invest in AI research for cybersecurity; advocate for regulatory frameworks addressing AI in cyber operations.
- Scenario Outlook:
- Best: AI defenses outpace offensive capabilities, reducing cyber threats.
- Worst: AI-enhanced attacks overwhelm defenses, leading to widespread disruptions.
- Most-Likely: Continued arms race with incremental improvements in both attack and defense capabilities.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
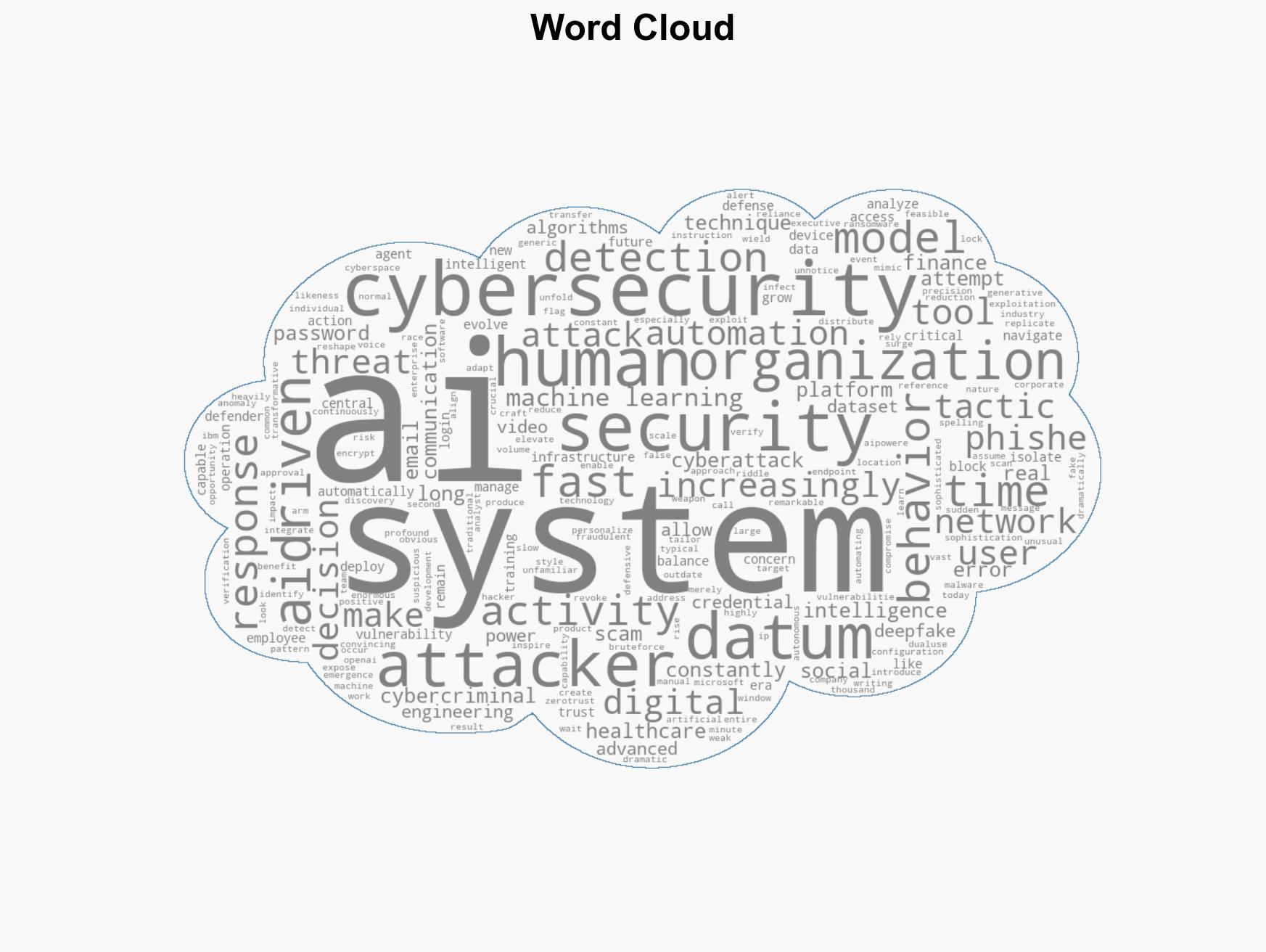
cybersecurity, artificial intelligence, cybercrime, deepfakes, zero-trust, autonomous systems, digital threats
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model hostile behavior to identify vulnerabilities.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Cognitive Bias Stress Test: Structured challenge to expose and correct biases.
- Network Influence Mapping: Map influence relationships to assess actor impact.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us