The Persistence of Credential Abuse Despite Multifactor Authentication Measures
Published on: 2026-03-22
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Why stolen credentials continue to work even where MFA is in place
1. BLUF (Bottom Line Up Front)
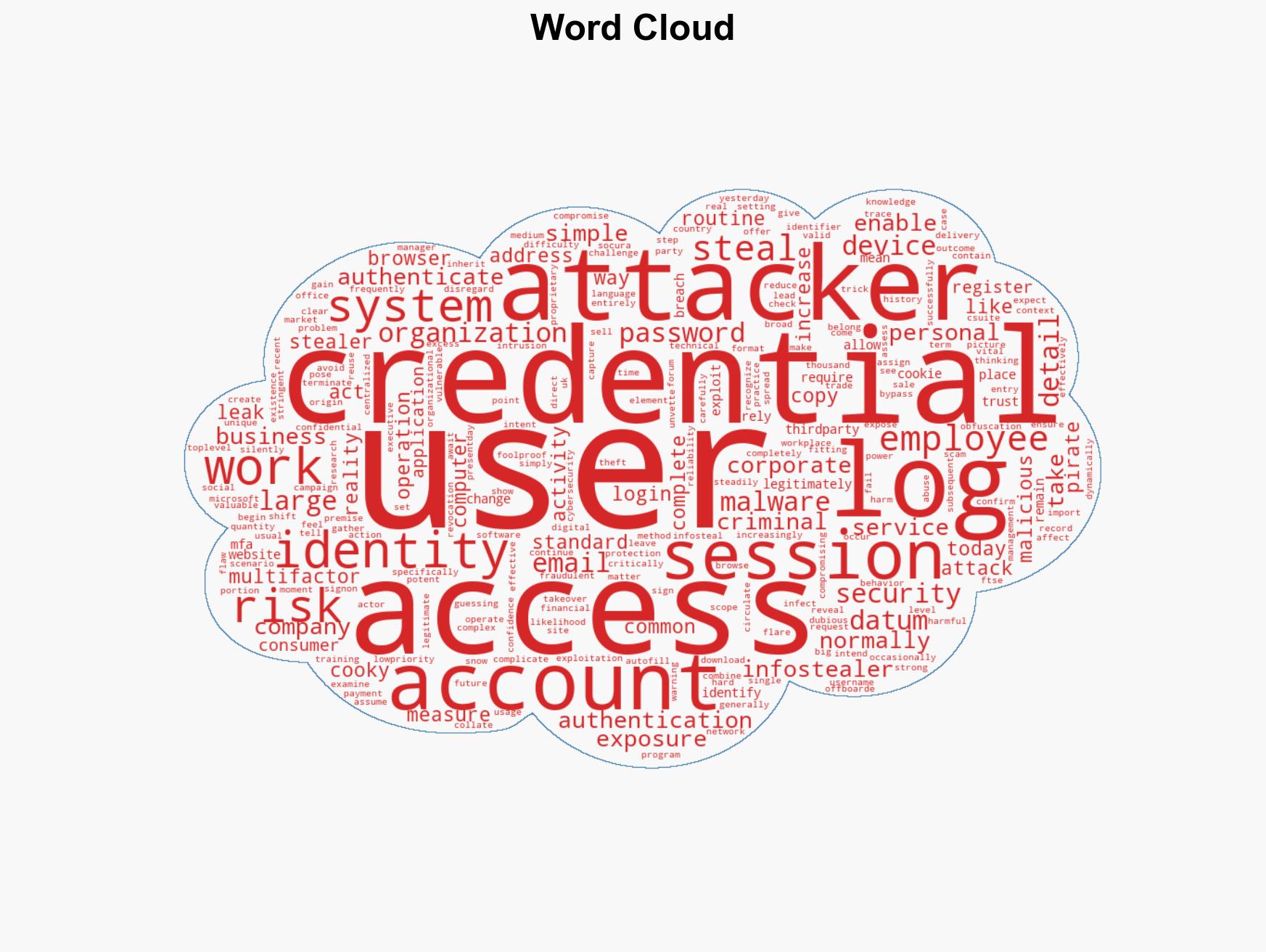
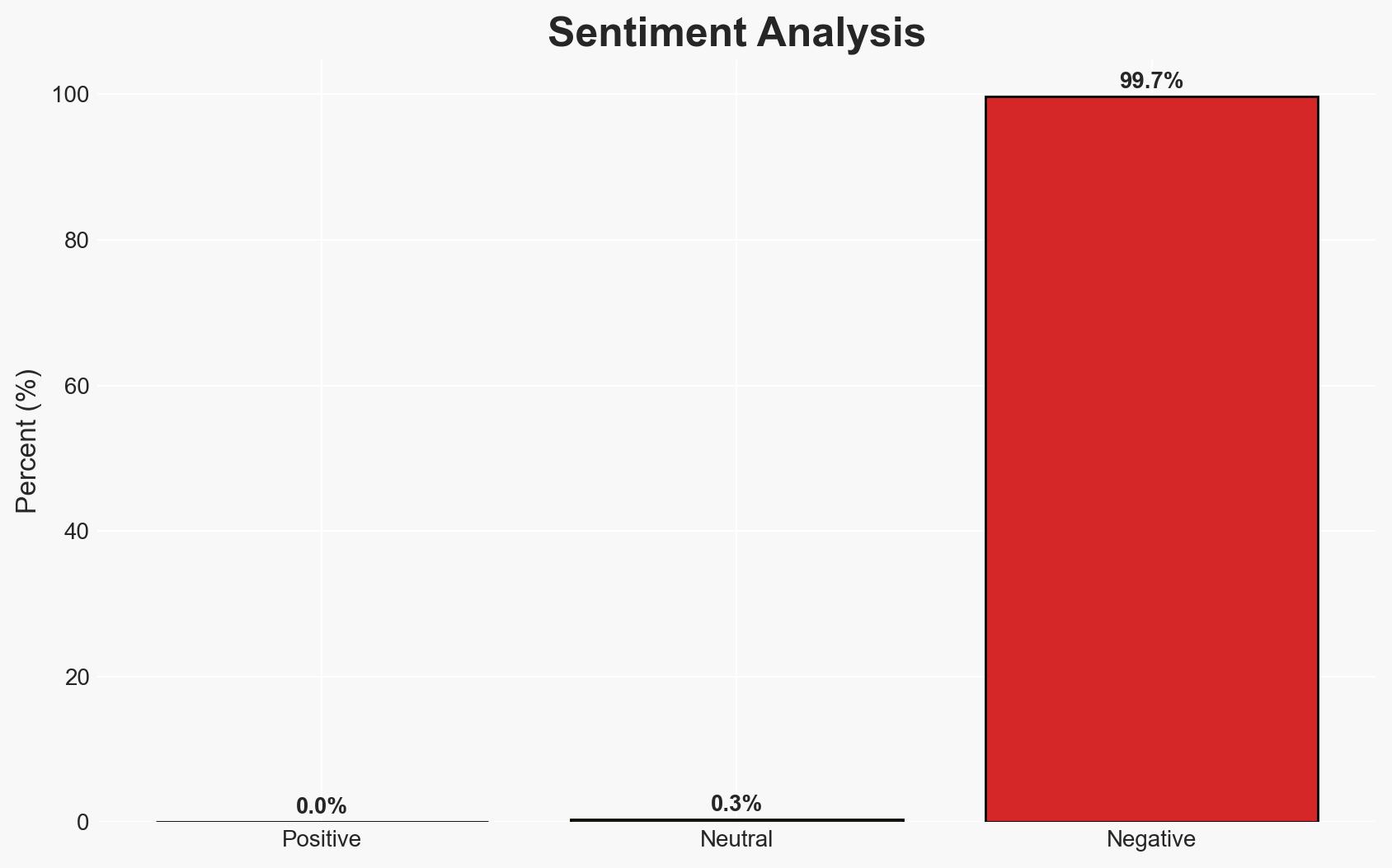
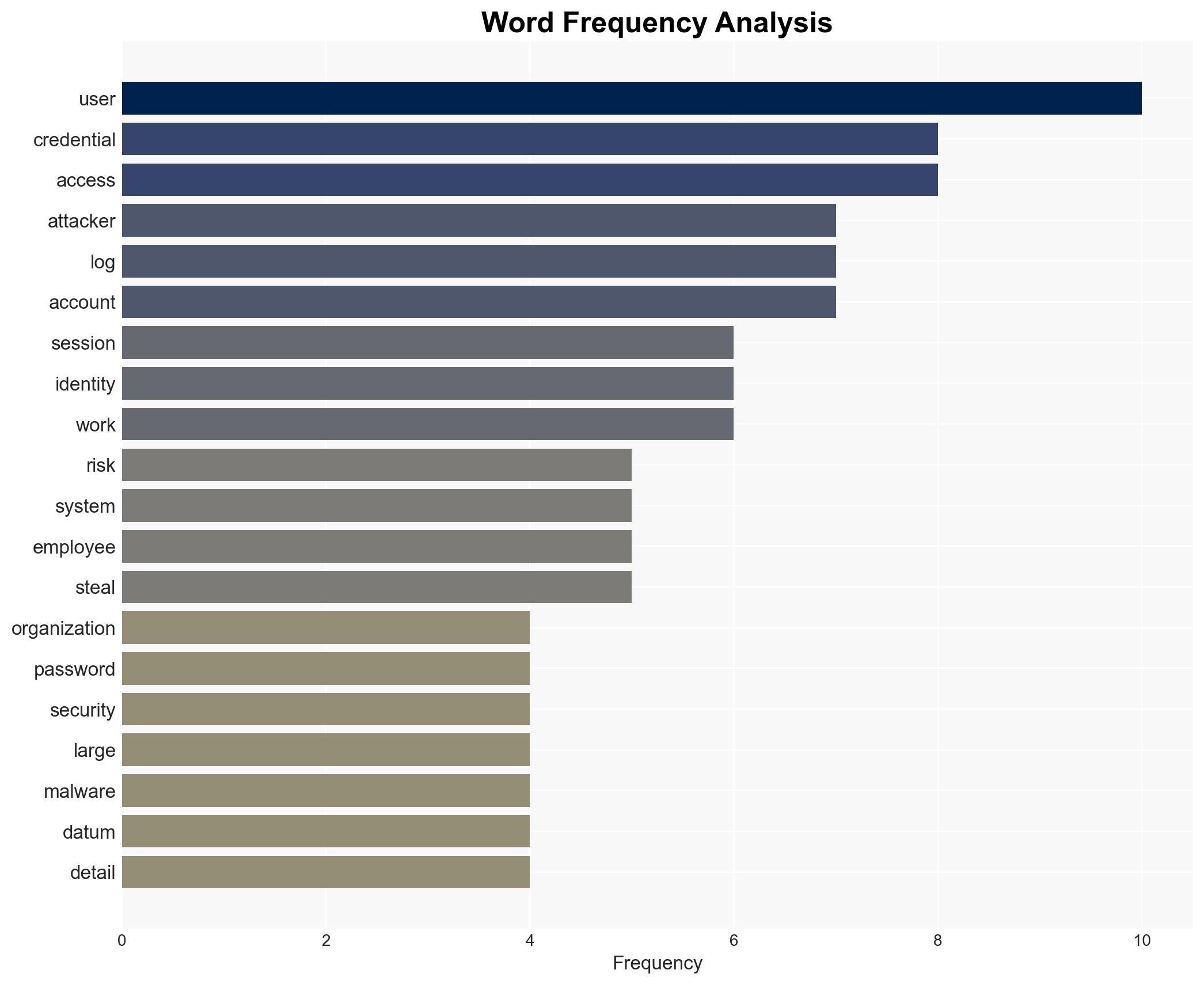
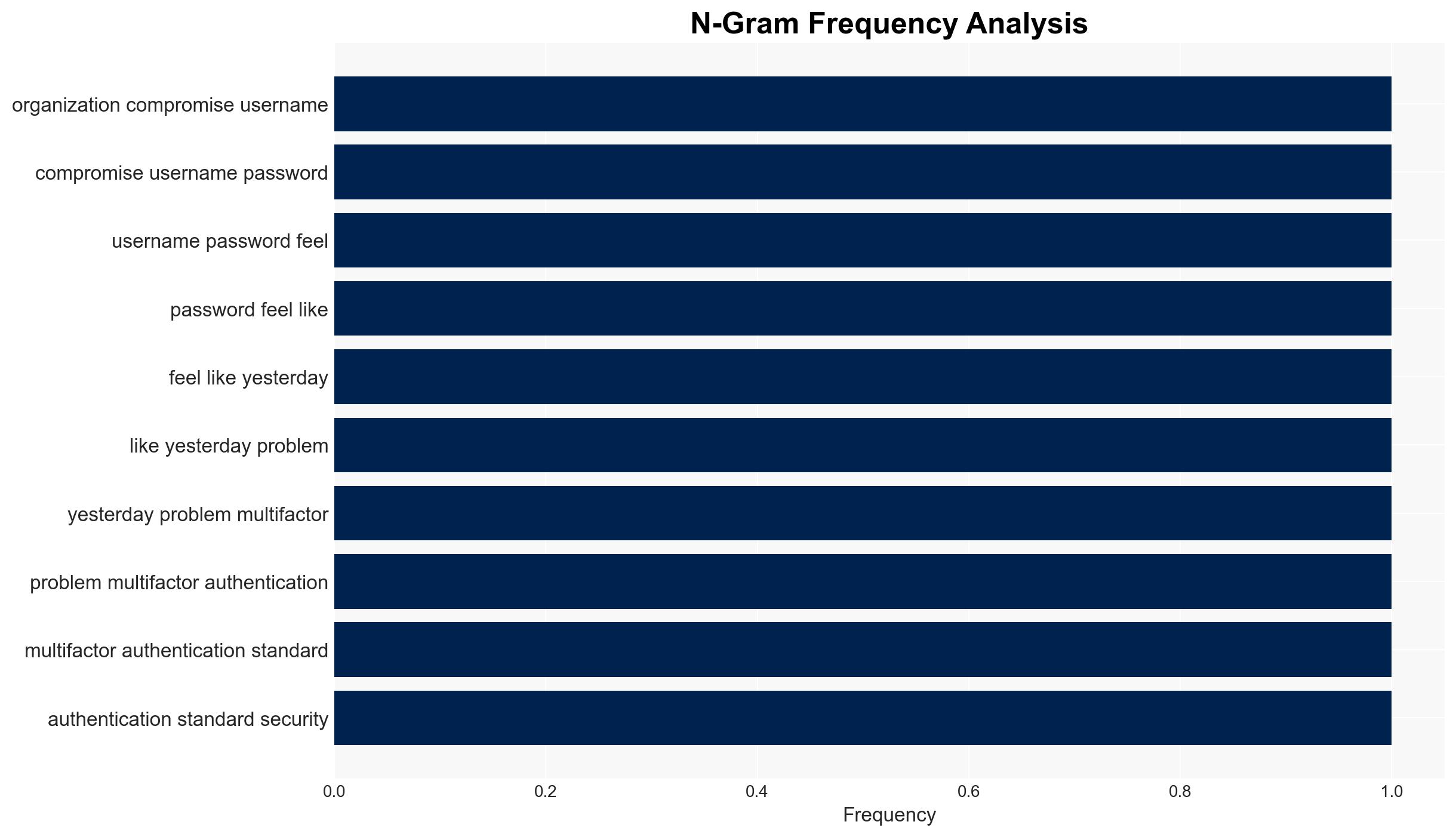
The continued effectiveness of stolen credentials, despite the implementation of multifactor authentication (MFA), is primarily due to the use of infostealer malware that captures extensive user data, including session cookies. This allows attackers to bypass MFA by mimicking authenticated sessions. The exposure of credentials is widespread, affecting even major corporations. Overall confidence in this assessment is moderate, given the reliance on reported data and the inherent uncertainties in cyber threat intelligence.
2. Competing Hypotheses
- Hypothesis A: Infostealer malware is the primary vector for credential compromise, enabling attackers to bypass MFA by using session cookies. This is supported by reports of widespread credential leaks linked to infostealer logs and the ability of such malware to capture comprehensive user data. Key uncertainties include the full extent of malware distribution and the effectiveness of organizational defenses.
- Hypothesis B: Credential compromise is primarily due to user behavior, such as password reuse and exposure through third-party breaches. While user behavior is a known risk factor, the specific mention of infostealer malware in the source text suggests a more direct and technical method of bypassing MFA.
- Assessment: Hypothesis A is currently better supported due to the detailed description of infostealer malware operations and their impact on credential security. Indicators that could shift this judgment include new evidence of significant user behavior-related breaches or changes in malware tactics.
3. Key Assumptions and Red Flags
- Assumptions: Organizations have implemented MFA; infostealer malware can effectively capture session cookies; credential leaks are primarily due to malware, not direct system attacks.
- Information Gaps: The specific distribution methods and prevalence of infostealer malware; the effectiveness of current MFA implementations against such threats.
- Bias & Deception Risks: Potential bias in source reporting towards technical solutions over user behavior; possible underreporting of successful MFA defenses.
4. Implications and Strategic Risks
The evolving threat landscape suggests that reliance on MFA alone is insufficient to prevent credential compromise. Organizations must adapt to increasingly sophisticated cyber threats that exploit both technical vulnerabilities and user behavior.
- Political / Geopolitical: Increased cyber espionage risks as state and non-state actors exploit credential leaks for intelligence gathering.
- Security / Counter-Terrorism: Potential for compromised credentials to facilitate unauthorized access to sensitive systems, impacting national security.
- Cyber / Information Space: Growing need for advanced threat detection and response capabilities to address malware-based credential theft.
- Economic / Social: Financial losses and reputational damage to affected organizations; potential erosion of trust in digital security measures.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring for infostealer malware activity; conduct security audits to identify and mitigate credential exposure risks.
- Medium-Term Posture (1–12 months): Develop partnerships for threat intelligence sharing; invest in user education and advanced authentication technologies.
- Scenario Outlook:
- Best: Successful mitigation of infostealer threats through improved defenses and user practices.
- Worst: Widespread credential compromises leading to significant breaches and operational disruptions.
- Most-Likely: Continued adaptation by both attackers and defenders, with incremental improvements in security posture.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, credential theft, multifactor authentication, infostealer malware, corporate security, cyber threat intelligence, digital identity
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us