The Role of Information Technology Audit in Strengthening Cybersecurity Compliance – Typeforyou.org
Published on: 2025-04-02
Intelligence Report: The Role of Information Technology Audit in Strengthening Cybersecurity Compliance – Typeforyou.org
1. BLUF (Bottom Line Up Front)
Information technology audits are critical in enhancing cybersecurity compliance by identifying vulnerabilities, ensuring adherence to regulations, and improving security infrastructure. Organizations across all sectors must prioritize these audits to mitigate risks and protect sensitive data from cyber threats. Key recommendations include regular audits, updating security policies, and ensuring compliance with relevant regulations.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
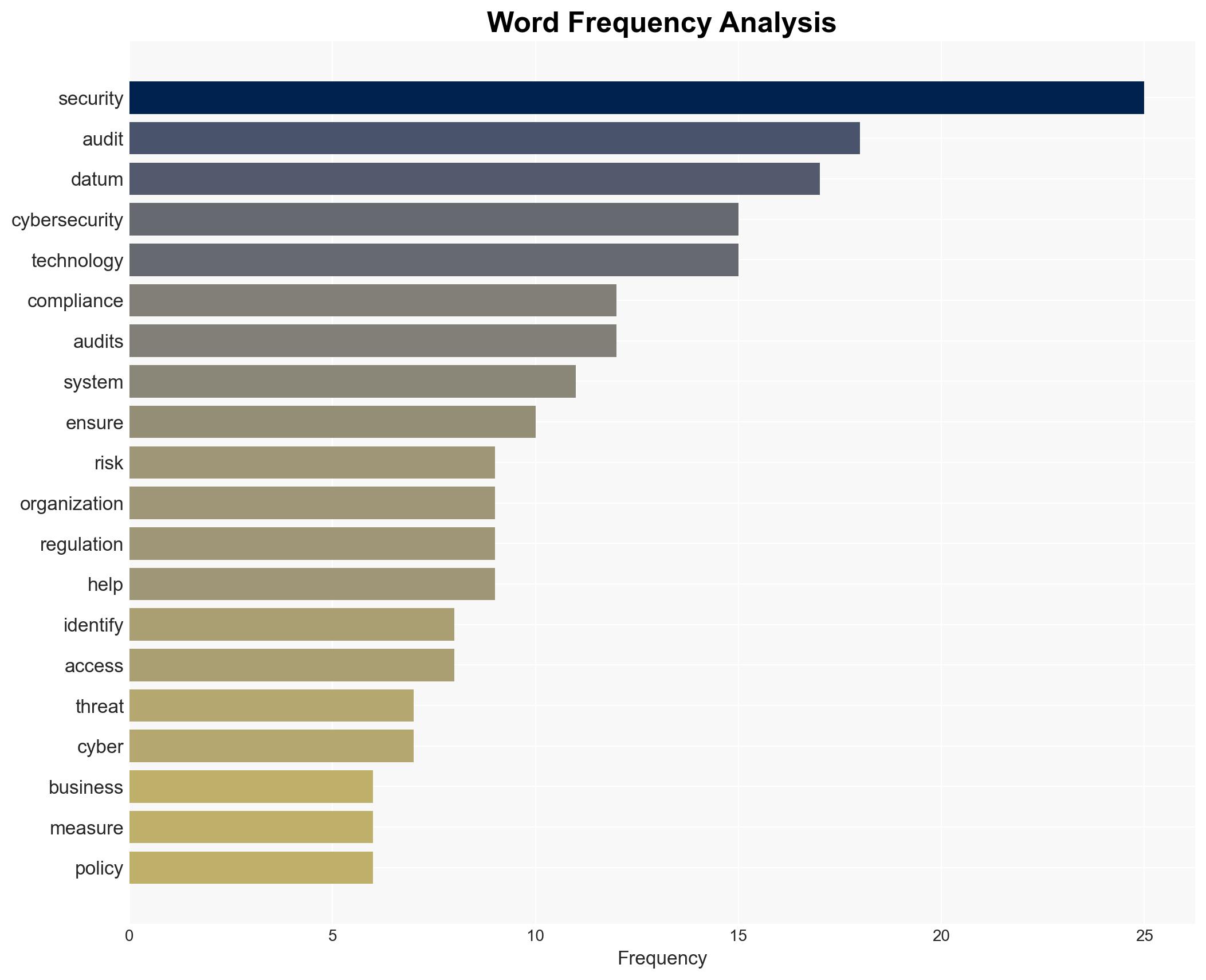
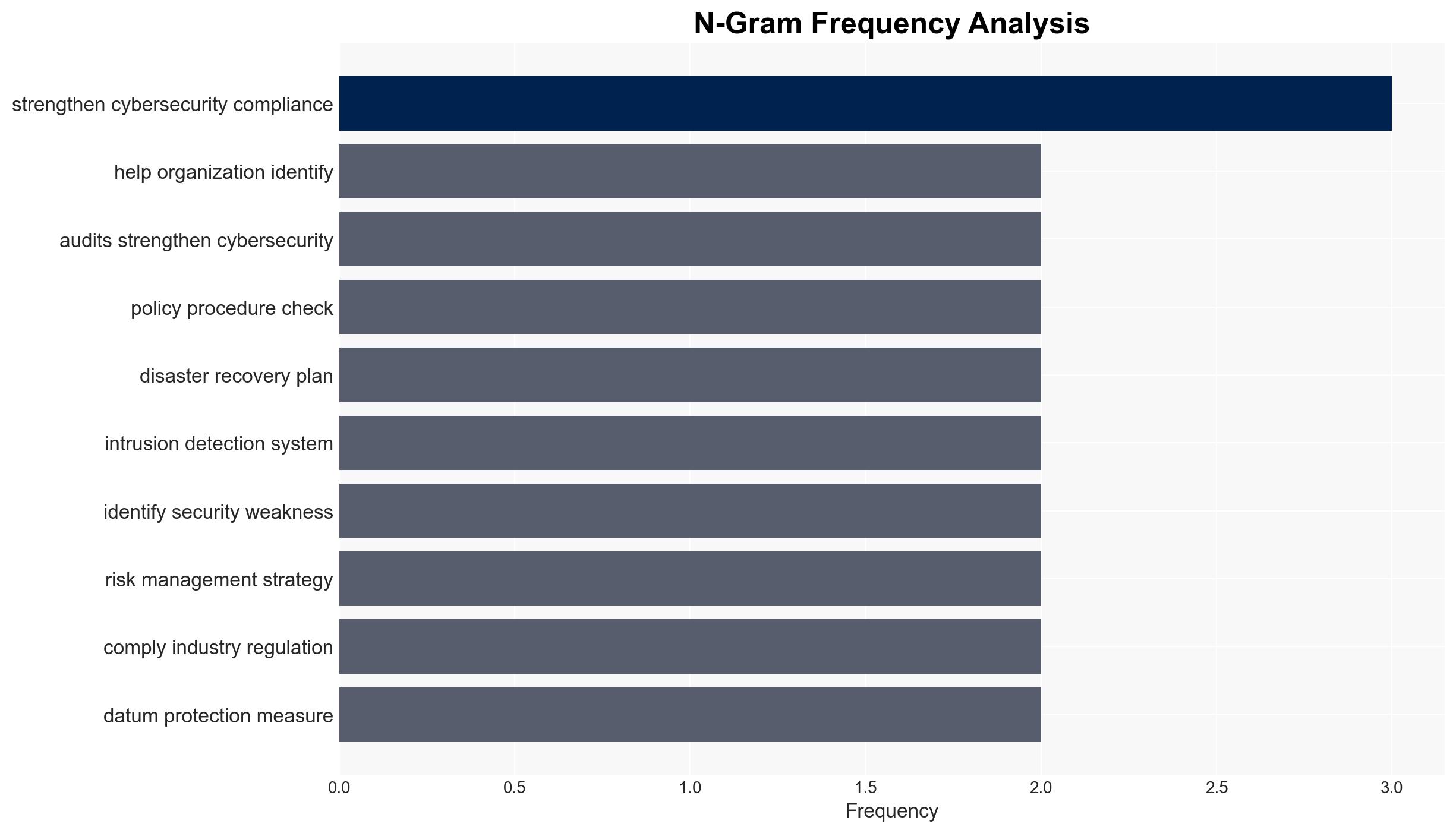
The digital landscape is increasingly threatened by cybersecurity risks, affecting businesses, government agencies, and individuals. Technology audits play a pivotal role in examining system security policies and compliance with cybersecurity regulations. These audits help organizations identify vulnerabilities, improve security measures, and ensure compliance with legal and industry-specific requirements. Key areas covered in audits include security policy checks, access control evaluations, data protection reviews, network security assessments, and compliance with regulations such as GDPR, HIPAA, and PCI DSS.
3. Implications and Strategic Risks
The failure to conduct regular technology audits can result in significant risks, including data breaches, legal penalties, and reputational damage. Non-compliance with cybersecurity regulations can lead to heavy fines and loss of customer trust. The increasing sophistication of cybercriminals poses a continuous threat to network security, emphasizing the need for robust risk management strategies and regular audits to mitigate potential attacks.
4. Recommendations and Outlook
Recommendations:
- Conduct regular technology audits to identify and address security vulnerabilities.
- Update security policies and procedures to align with current cybersecurity standards.
- Ensure compliance with relevant regulations such as GDPR, HIPAA, and PCI DSS.
- Enhance data protection measures, including encryption and secure cloud storage.
- Strengthen network security through updated firewall, antivirus, and intrusion detection systems.
Outlook:
In the best-case scenario, organizations that implement regular technology audits and update their security measures will significantly reduce their risk of cyberattacks and ensure compliance with regulations. In the worst-case scenario, failure to prioritize these audits could lead to increased data breaches and legal consequences. The most likely outcome is a gradual improvement in cybersecurity compliance as more organizations recognize the importance of technology audits.
5. Key Individuals and Entities
This report does not mention specific individuals or entities by name, focusing instead on the general importance of technology audits in cybersecurity compliance.