Top 5 Security Applications That Effectively Safeguard Your Computer Against Cyber Threats
Published on: 2025-11-29
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
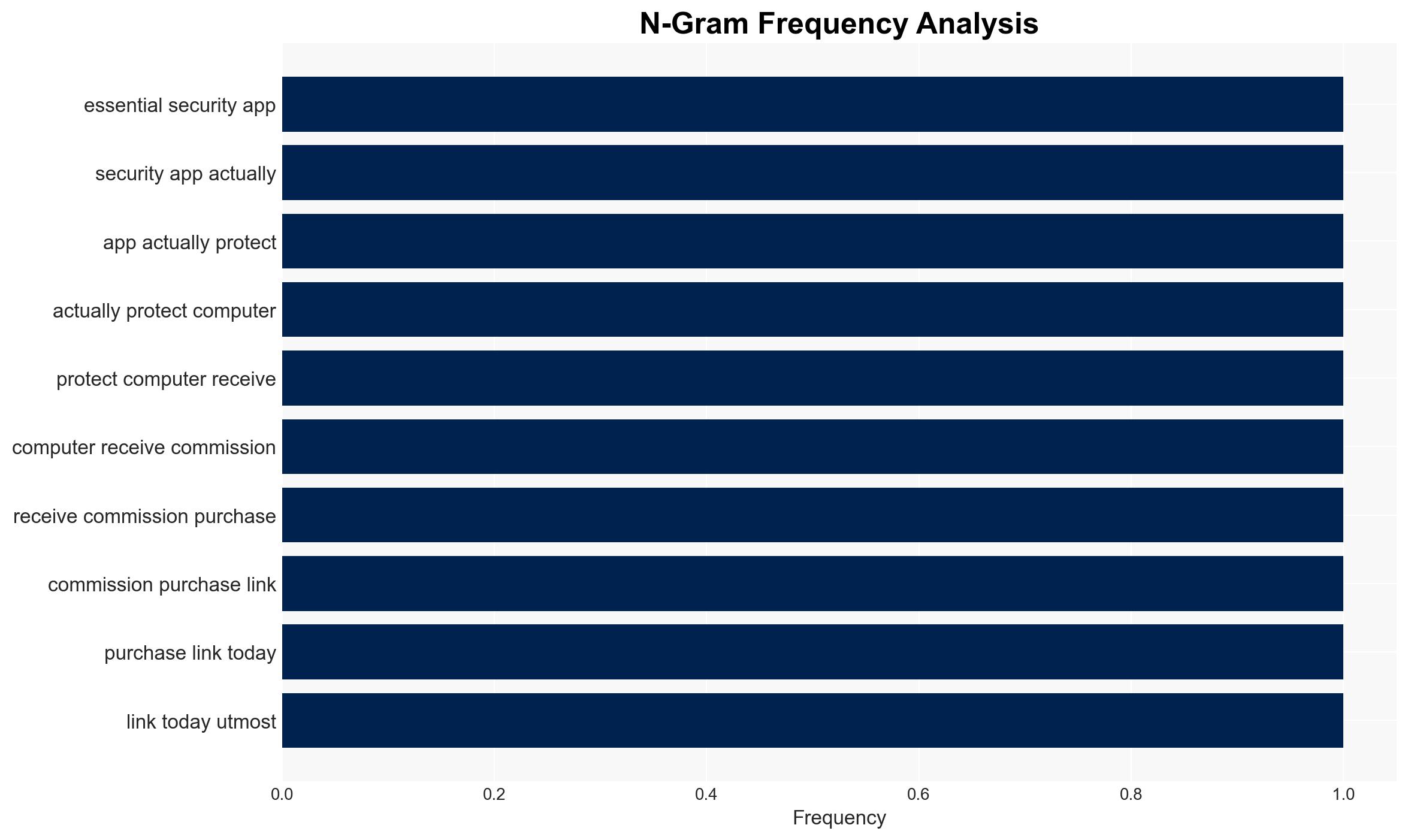
Intelligence Report: 5 Essential Security Apps That Actually Protect Your Computer
1. BLUF (Bottom Line Up Front)
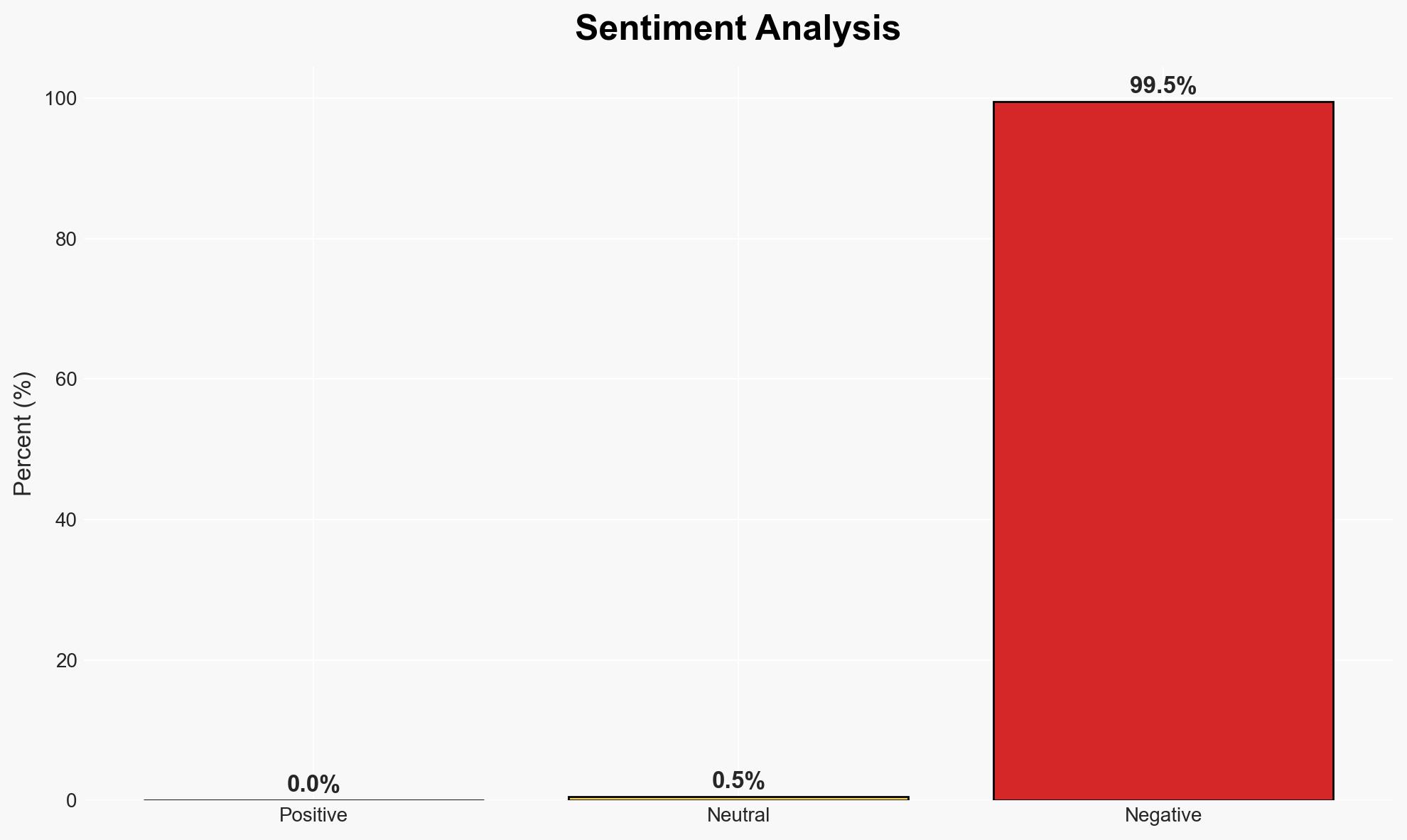
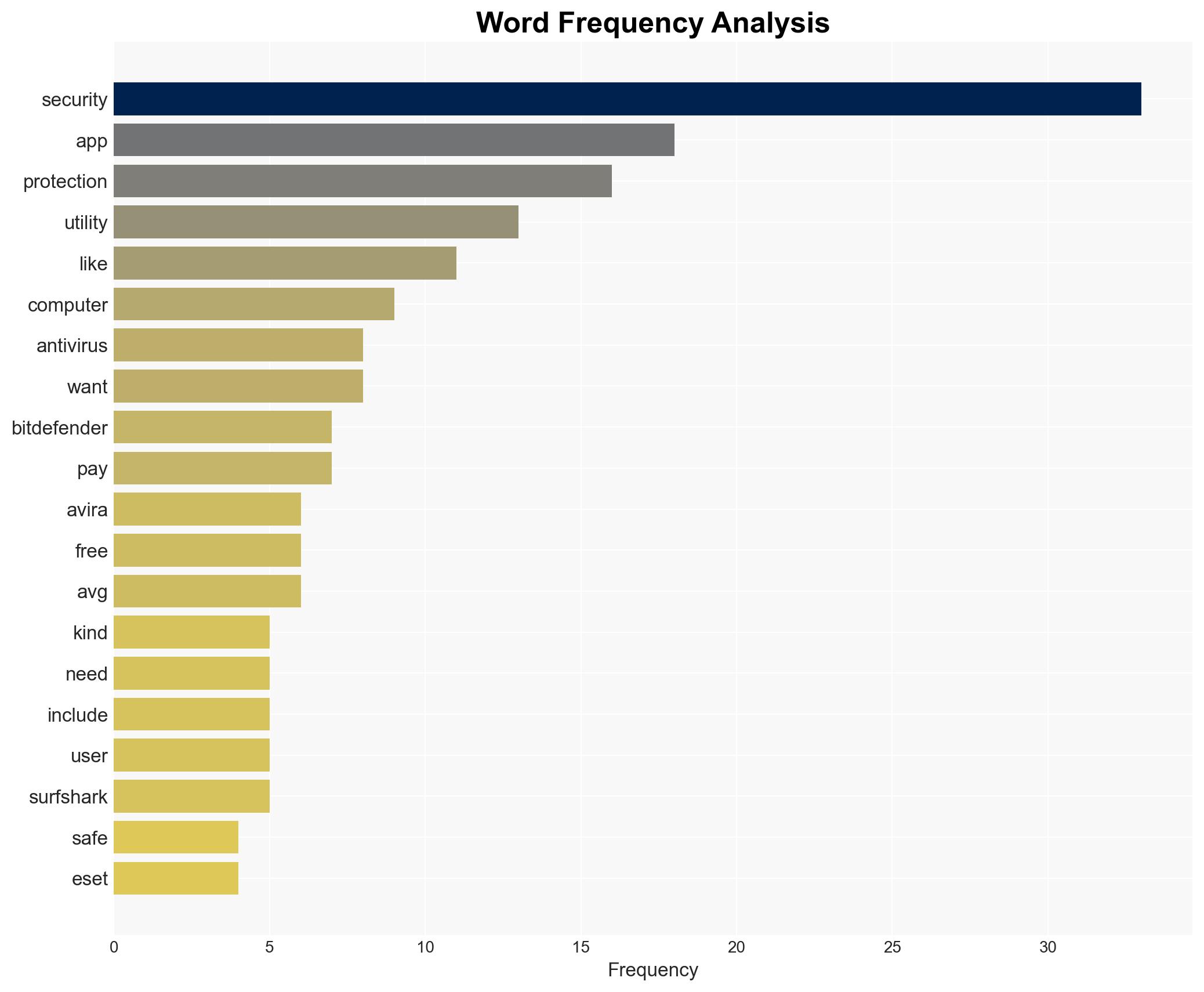
The analysis evaluates the effectiveness and strategic implications of various security applications in protecting computer systems against cyber threats. The most supported hypothesis is that comprehensive security suites offer better protection than free or piecemeal solutions. This assessment affects cybersecurity policy-makers and IT security professionals. Overall confidence in this judgment is moderate due to limited data on specific threat vectors and user behavior.
2. Competing Hypotheses
- Hypothesis A: Comprehensive security applications (e.g., ESET, Surfshark) provide superior protection against a broad range of cyber threats, including zero-day exploits and ransomware. This is supported by their advanced features like network traffic analysis and data encryption. However, the complexity of these tools may deter less experienced users.
- Hypothesis B: Free or basic security applications (e.g., Avira) are sufficient for most users, providing essential protection without the need for advanced features. This is contradicted by reports of resource limitations and potential gaps in protection against sophisticated threats.
- Assessment: Hypothesis A is currently better supported due to the comprehensive nature of the protection offered by advanced security suites. Indicators such as increasing sophistication of cyber threats and user demand for robust security solutions could further validate this hypothesis.
3. Key Assumptions and Red Flags
- Assumptions: Users have a basic understanding of cybersecurity; advanced threats require sophisticated protection; free applications have inherent limitations.
- Information Gaps: Specific data on the effectiveness of each security application against emerging threats; user behavior and compliance with security protocols.
- Bias & Deception Risks: Potential bias in source material favoring certain products; marketing influence on perceived effectiveness; lack of independent testing data.
4. Implications and Strategic Risks
The evolution of cybersecurity threats necessitates continuous adaptation of security measures. The reliance on comprehensive security suites may increase as threats become more sophisticated.
- Political / Geopolitical: Increased demand for cybersecurity solutions could influence international tech policy and trade relations.
- Security / Counter-Terrorism: Enhanced security measures may reduce vulnerability to cyber-terrorism and state-sponsored attacks.
- Cyber / Information Space: The adoption of advanced security applications could deter cybercriminals but may also lead to more sophisticated attack methods.
- Economic / Social: The cost of comprehensive security solutions could impact small businesses and individuals, potentially widening the digital divide.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a review of current cybersecurity measures; prioritize updates to comprehensive security suites where feasible.
- Medium-Term Posture (1–12 months): Invest in user education and training; develop partnerships with cybersecurity firms for threat intelligence sharing.
- Scenario Outlook: Best: Widespread adoption of advanced security measures reduces cyber incidents. Worst: Increased cyber threats outpace security advancements. Most-Likely: Gradual improvement in security posture with ongoing challenges from sophisticated threats.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
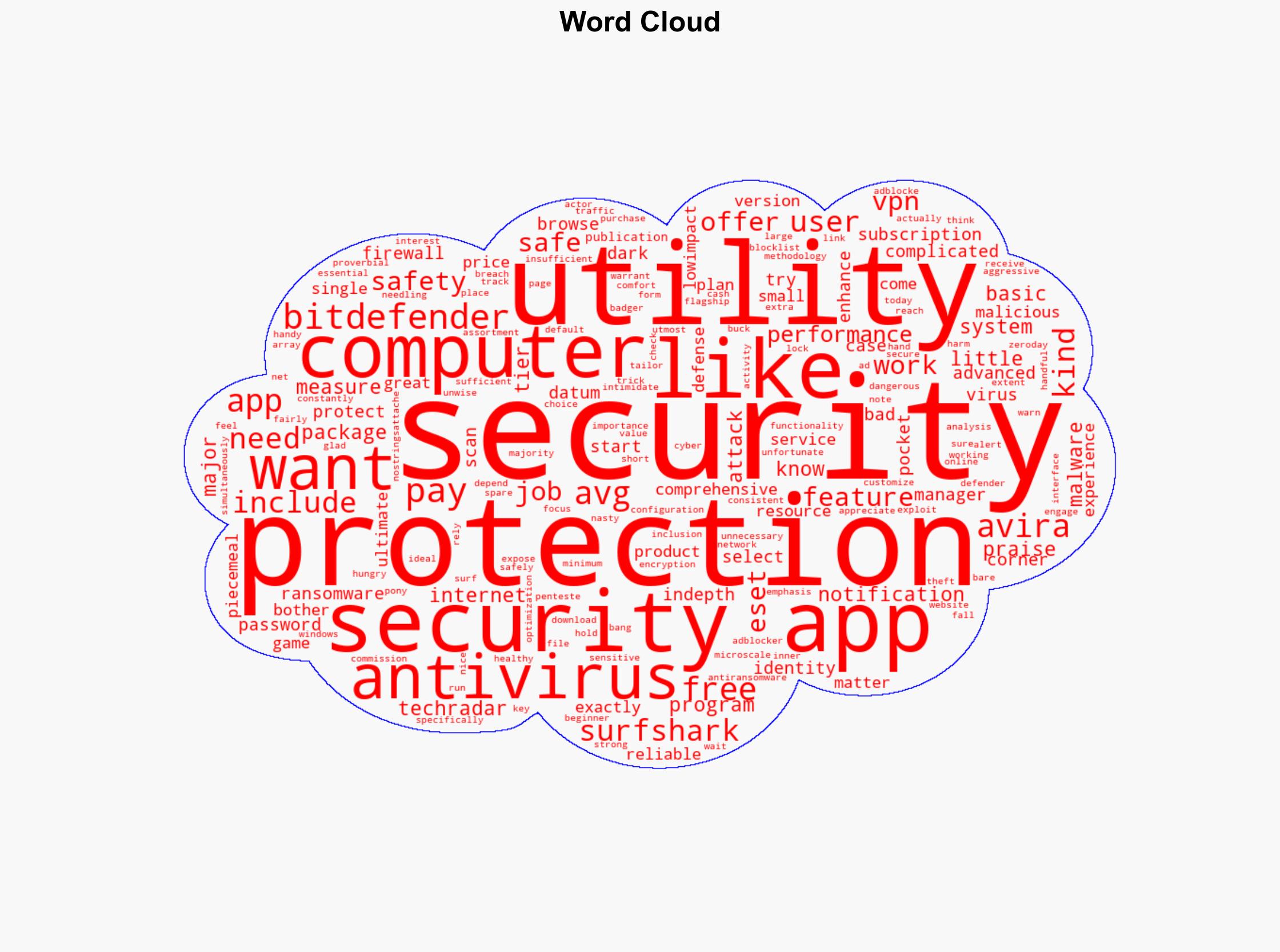
Cybersecurity, information security, cyber threats, antivirus software, digital protection, user education, technology policy
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us