TP-Link issues urgent patch for serious authentication bypass vulnerability in Archer NX routers
Published on: 2026-03-25
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
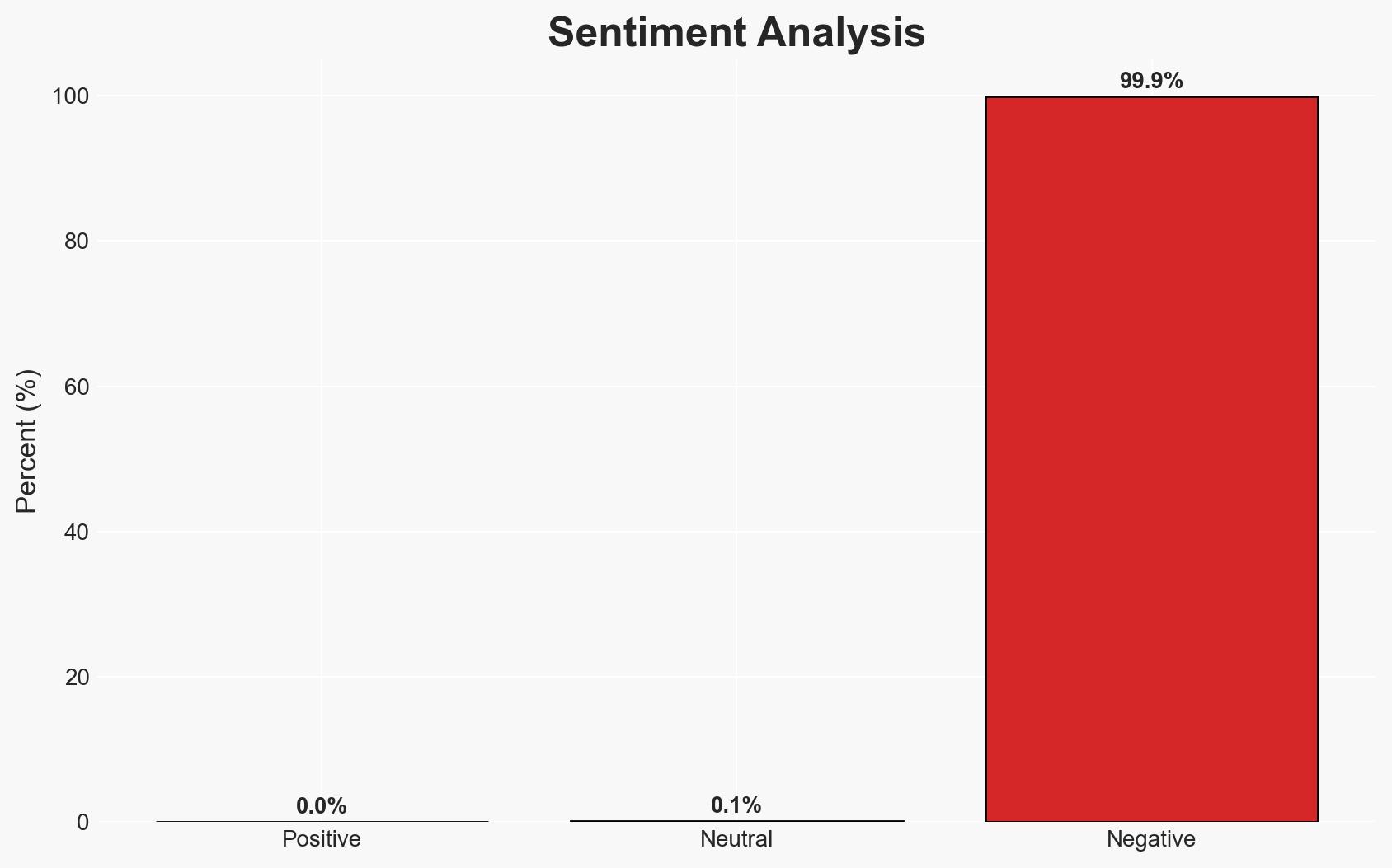
Intelligence Report: TP-Link warns users to patch critical router auth bypass flaw
1. BLUF (Bottom Line Up Front)
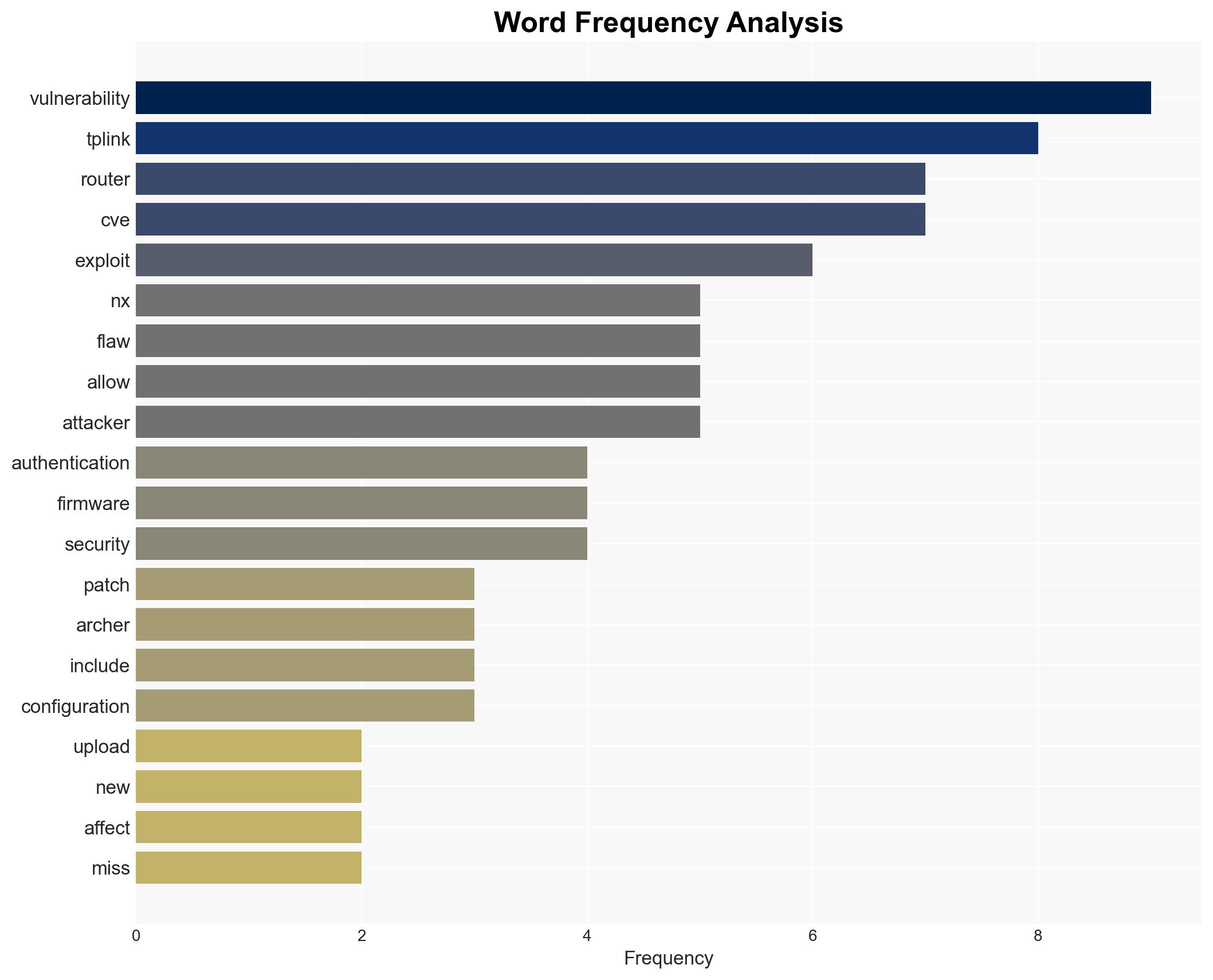
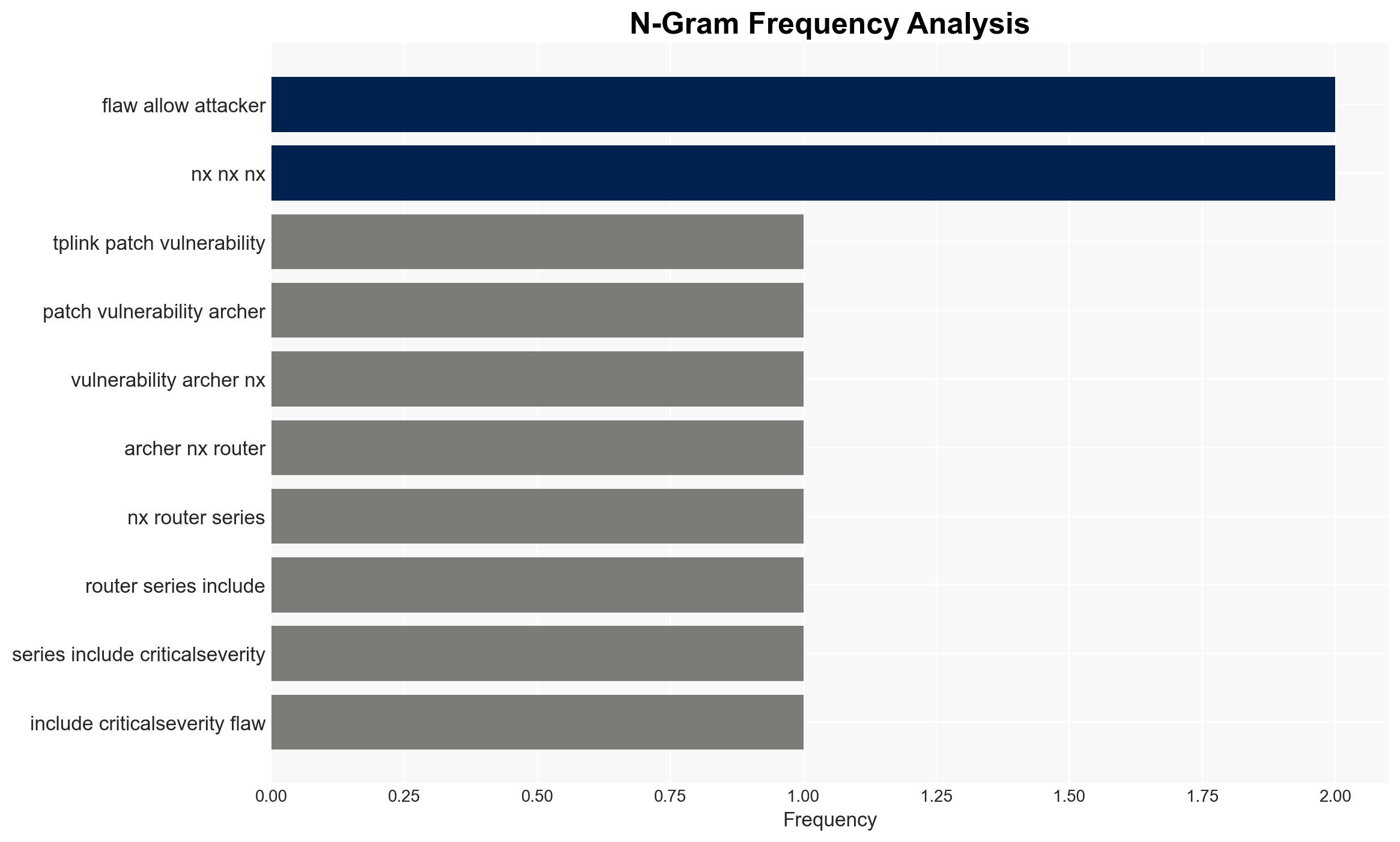
TP-Link has addressed critical vulnerabilities in its Archer NX router series that could allow unauthorized firmware uploads and configuration changes. This poses a significant security risk to users, potentially enabling cyber-attacks. The most likely hypothesis is that these vulnerabilities could be exploited by state-sponsored actors, given historical precedents. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The vulnerabilities are primarily being exploited by state-sponsored actors, possibly linked to Chinese interests, as suggested by past allegations and the Texas Attorney General’s lawsuit. Supporting evidence includes historical exploitation patterns and geopolitical tensions. However, direct attribution remains uncertain.
- Hypothesis B: The vulnerabilities are being exploited by a diverse set of threat actors, including cybercriminals and opportunistic hackers, not limited to state-sponsored groups. This is supported by the broad nature of the vulnerabilities and the inclusion in CISA’s Known Exploited Vulnerability catalog, indicating widespread exploitation.
- Assessment: Hypothesis A is currently better supported due to the geopolitical context and past allegations against TP-Link. Indicators such as increased targeting of U.S. infrastructure or further legal actions could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: TP-Link’s patches are effective; state-sponsored actors have the capability and intent to exploit these vulnerabilities; users will not universally apply patches promptly.
- Information Gaps: Lack of direct evidence linking specific threat actors to current exploits; incomplete data on the adoption rate of the patches by end-users.
- Bias & Deception Risks: Potential bias from sources with vested interests in attributing attacks to state-sponsored actors; TP-Link’s public statements may understate the severity to protect brand reputation.
4. Implications and Strategic Risks
The exploitation of these vulnerabilities could lead to increased cyber-attacks on critical infrastructure, affecting national security and economic stability. The situation may exacerbate geopolitical tensions, particularly between the U.S. and China.
- Political / Geopolitical: Potential for increased regulatory scrutiny and diplomatic tensions between the U.S. and China.
- Security / Counter-Terrorism: Enhanced threat landscape for U.S. infrastructure, requiring heightened vigilance and response capabilities.
- Cyber / Information Space: Increased cyber espionage and data theft risks, with potential misinformation campaigns exploiting the vulnerabilities.
- Economic / Social: Potential economic impact on TP-Link and consumer trust in foreign-made technology products.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor for exploitation patterns; encourage rapid patch adoption; enhance public-private information sharing on threat indicators.
- Medium-Term Posture (1–12 months): Develop resilience measures, including diversified supply chains and enhanced cybersecurity frameworks; strengthen international partnerships for threat intelligence sharing.
- Scenario Outlook:
- Best: Rapid patch adoption mitigates risk, and no significant exploitation occurs.
- Worst: Widespread exploitation leads to major infrastructure disruptions and escalates geopolitical tensions.
- Most-Likely: Moderate exploitation occurs, prompting increased regulatory and security measures.
6. Key Individuals and Entities
- TP-Link
- Texas Attorney General Paxton
- U.S. Federal Communications Commission (FCC)
- Cybersecurity and Infrastructure Security Agency (CISA)
- Quad7 botnet
7. Thematic Tags
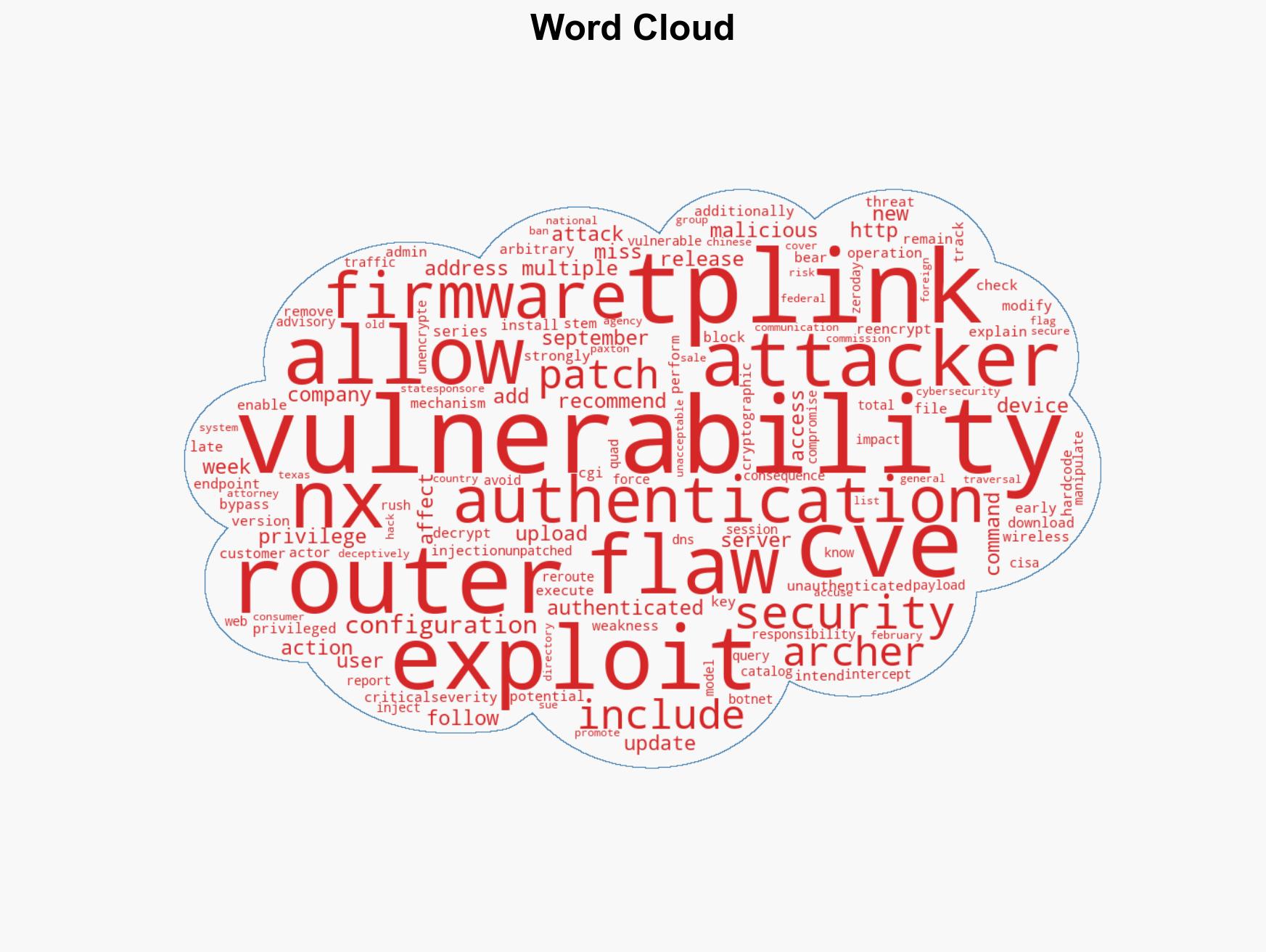
cybersecurity, state-sponsored hacking, router vulnerabilities, U.S.-China relations, critical infrastructure, regulatory response, cyber espionage
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us