Traditional Security Metrics Mislead CISOs Amid Rising Cyber Threats and Unresolved Vulnerabilities
Published on: 2026-04-03
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Why traditional metrics are giving CISOs a false sense of security
1. BLUF (Bottom Line Up Front)
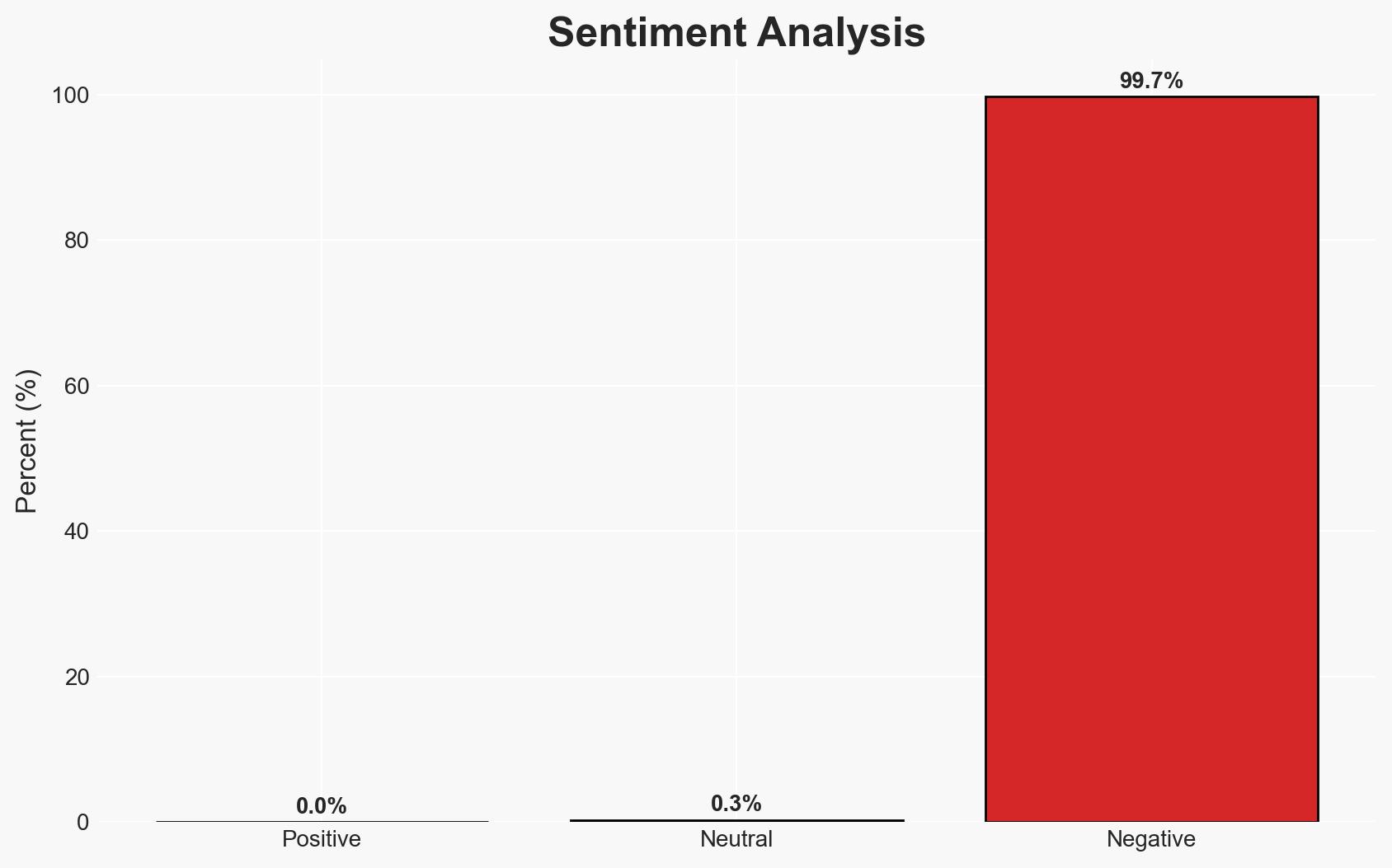
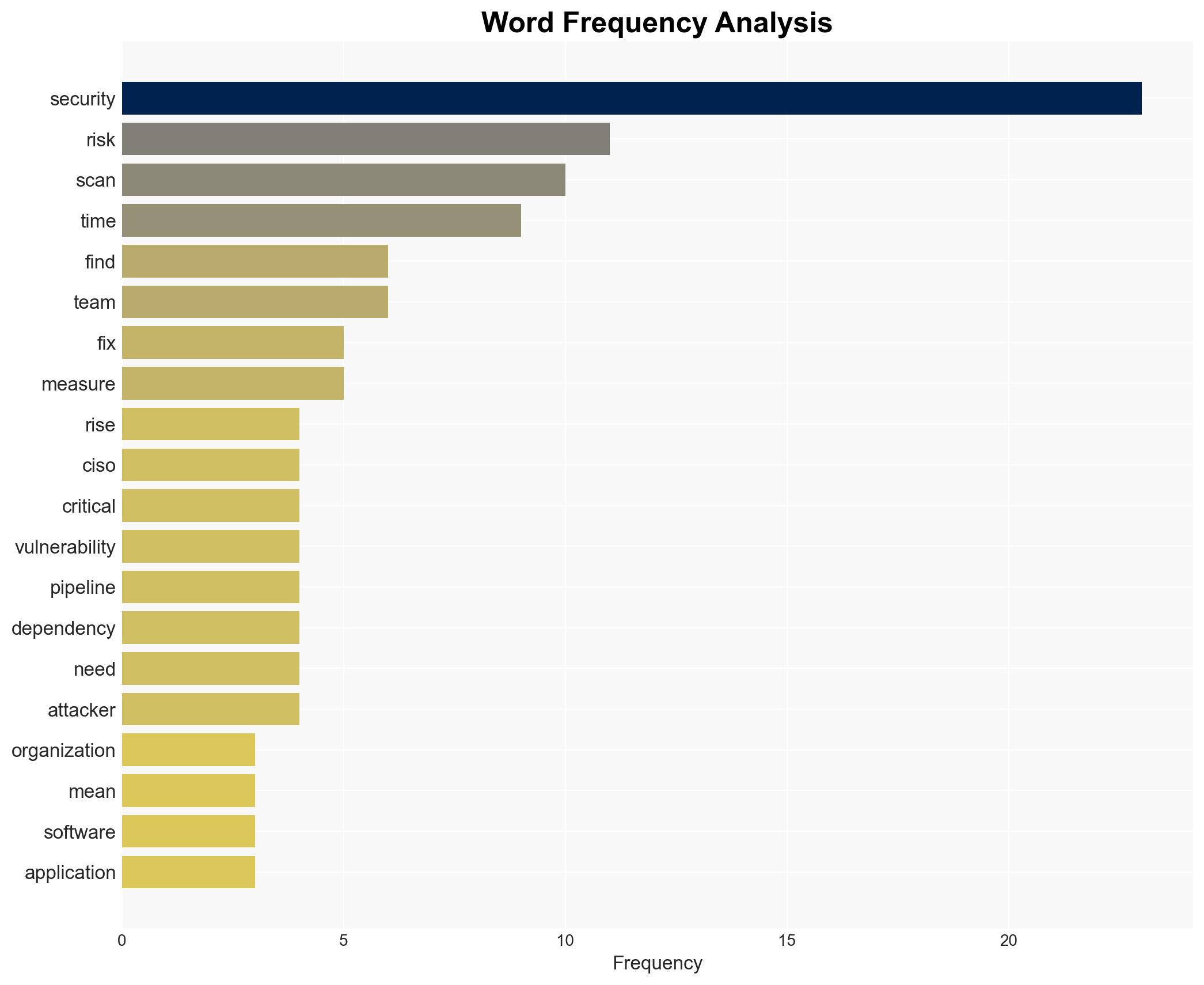
The reliance on traditional security metrics is leading to a false sense of security among CISOs, potentially increasing vulnerability to cyberattacks. The most likely hypothesis is that current metrics fail to measure true security efficacy, leaving critical vulnerabilities unaddressed. This affects organizations with significant security debt and outdated risk management strategies. Overall confidence in this judgment is moderate.
2. Competing Hypotheses
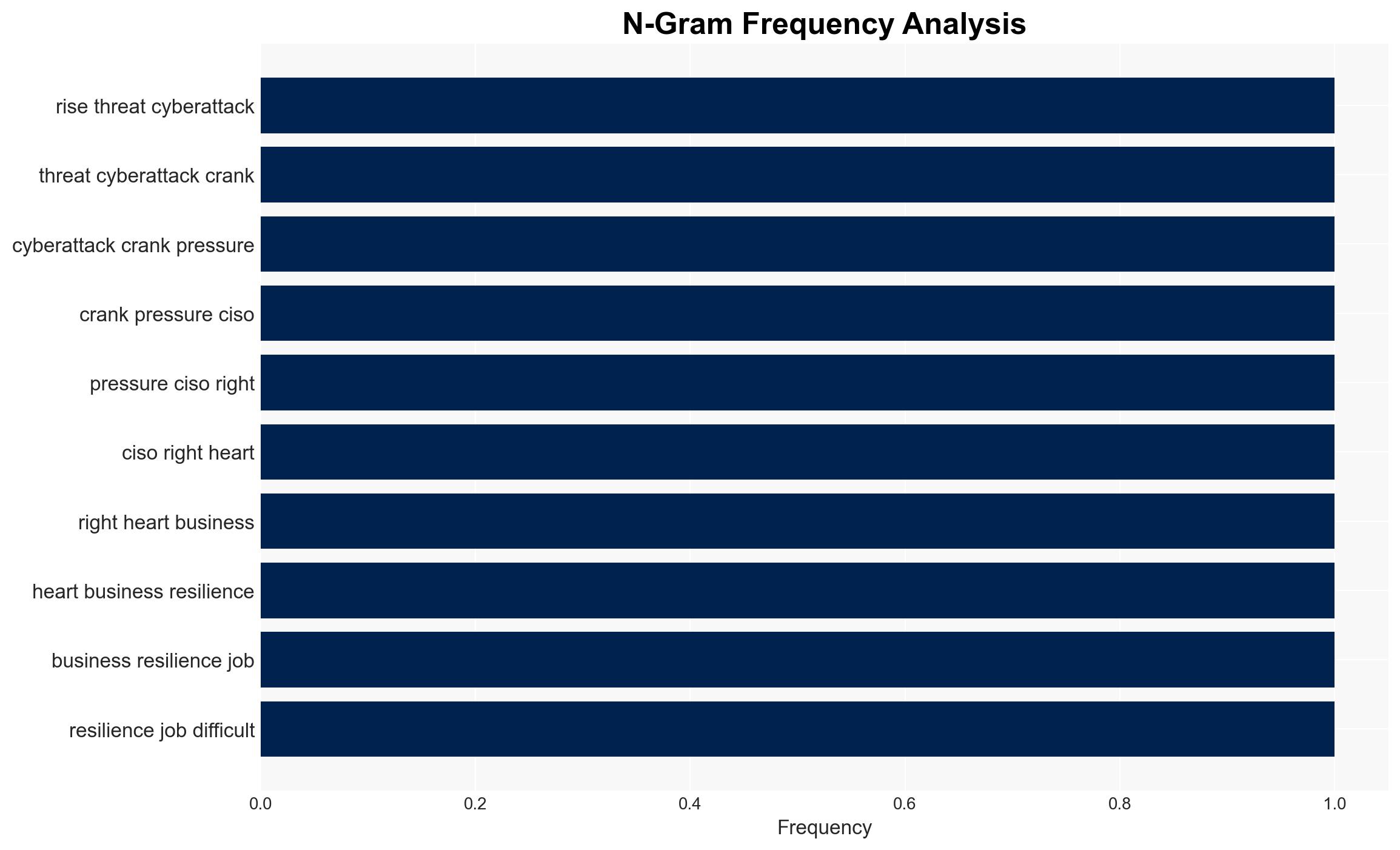
- Hypothesis A: Traditional security metrics create a false sense of security because they emphasize volume over efficacy, leading to unresolved critical vulnerabilities. Evidence includes the persistence of security debt and the ineffectiveness of high scan volumes in preventing breaches. Key uncertainties involve the extent to which organizations are aware of these shortcomings.
- Hypothesis B: Organizations are aware of the limitations of traditional metrics but lack the resources or strategic direction to implement more effective measures. Supporting evidence includes the rising average time to remediate vulnerabilities. Contradicting evidence is the continued emphasis on volume-based KPIs.
- Assessment: Hypothesis A is currently better supported due to the widespread use of traditional KPIs and the documented rise in security debt. Indicators that could shift this judgment include evidence of strategic shifts in organizational security practices or resource allocation.
3. Key Assumptions and Red Flags
- Assumptions: Organizations prioritize traditional metrics due to historical precedence; CISOs have limited influence over strategic shifts; security debt is a widespread issue.
- Information Gaps: Specific organizational case studies demonstrating successful transitions to more effective metrics; data on the impact of unresolved vulnerabilities on actual breach incidents.
- Bias & Deception Risks: Confirmation bias in security teams focusing on metrics that show progress; potential manipulation of KPI data to appease stakeholders.
4. Implications and Strategic Risks
The continued reliance on inadequate security metrics could exacerbate vulnerabilities and lead to increased cyberattack success rates. This development may interact with broader dynamics by influencing organizational risk management strategies and stakeholder perceptions.
- Political / Geopolitical: Increased cyber vulnerabilities could be exploited by state actors, potentially escalating geopolitical tensions.
- Security / Counter-Terrorism: Enhanced risk of cyberattacks could impact national security infrastructure and critical sectors.
- Cyber / Information Space: Potential for increased cyber espionage and data breaches, affecting information integrity and privacy.
- Economic / Social: Financial losses and reputational damage from breaches could impact economic stability and public trust in digital systems.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive review of current security metrics; prioritize addressing critical vulnerabilities over volume-based metrics.
- Medium-Term Posture (1–12 months): Develop and implement a strategic plan to transition to efficacy-based security metrics; invest in training and resources for security teams.
- Scenario Outlook:
- Best: Organizations successfully transition to effective metrics, reducing vulnerabilities and breach incidents.
- Worst: Continued reliance on traditional metrics leads to significant breaches and economic damage.
- Most-Likely: Gradual shift to improved metrics with intermittent breaches highlighting ongoing vulnerabilities.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
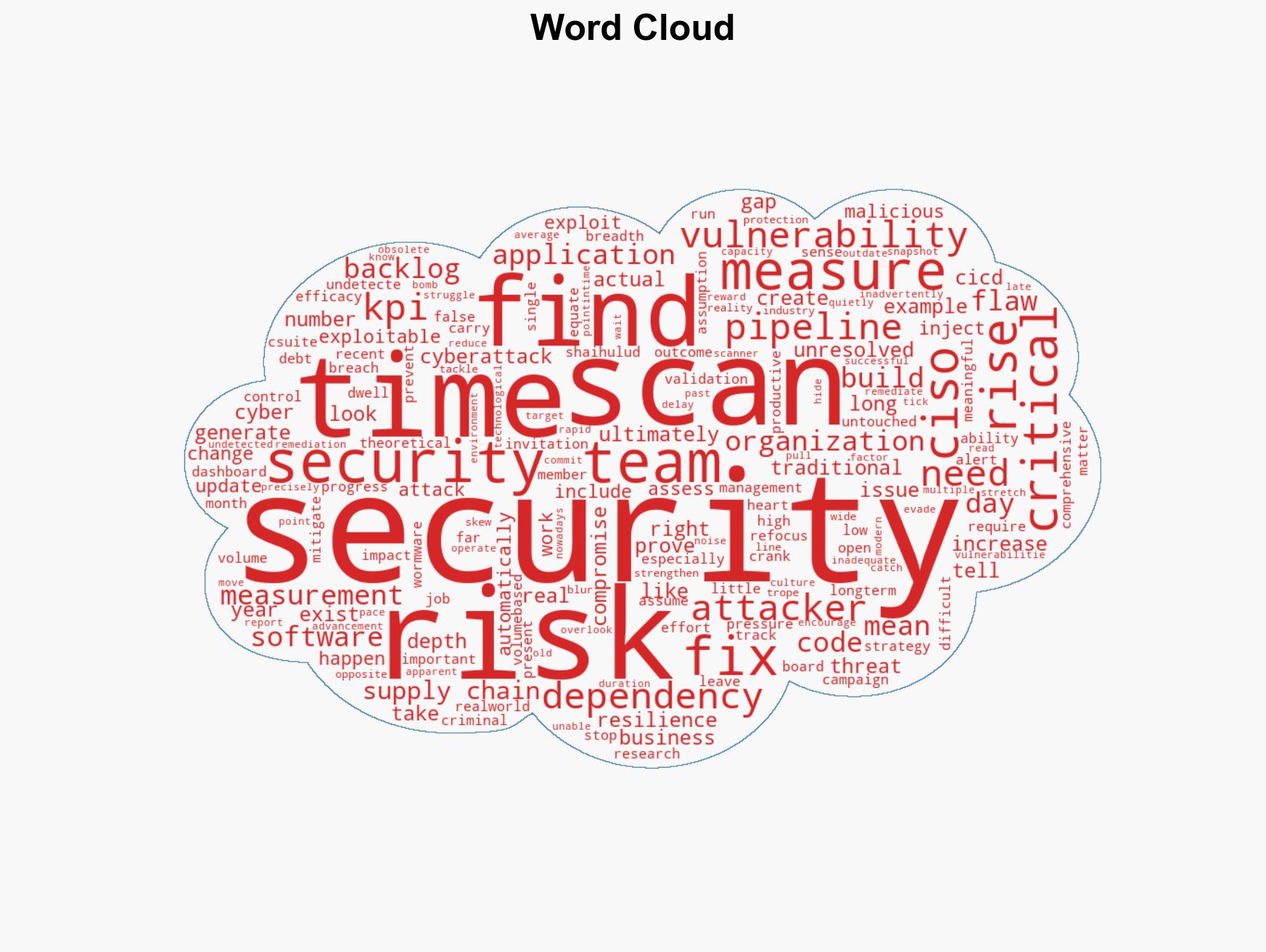
cybersecurity, risk management, security metrics, vulnerability management, cyber threats, organizational strategy, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us