Trio-Tech International re-evaluates ransomware incident as significant after data breach revelation
Published on: 2026-03-23
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
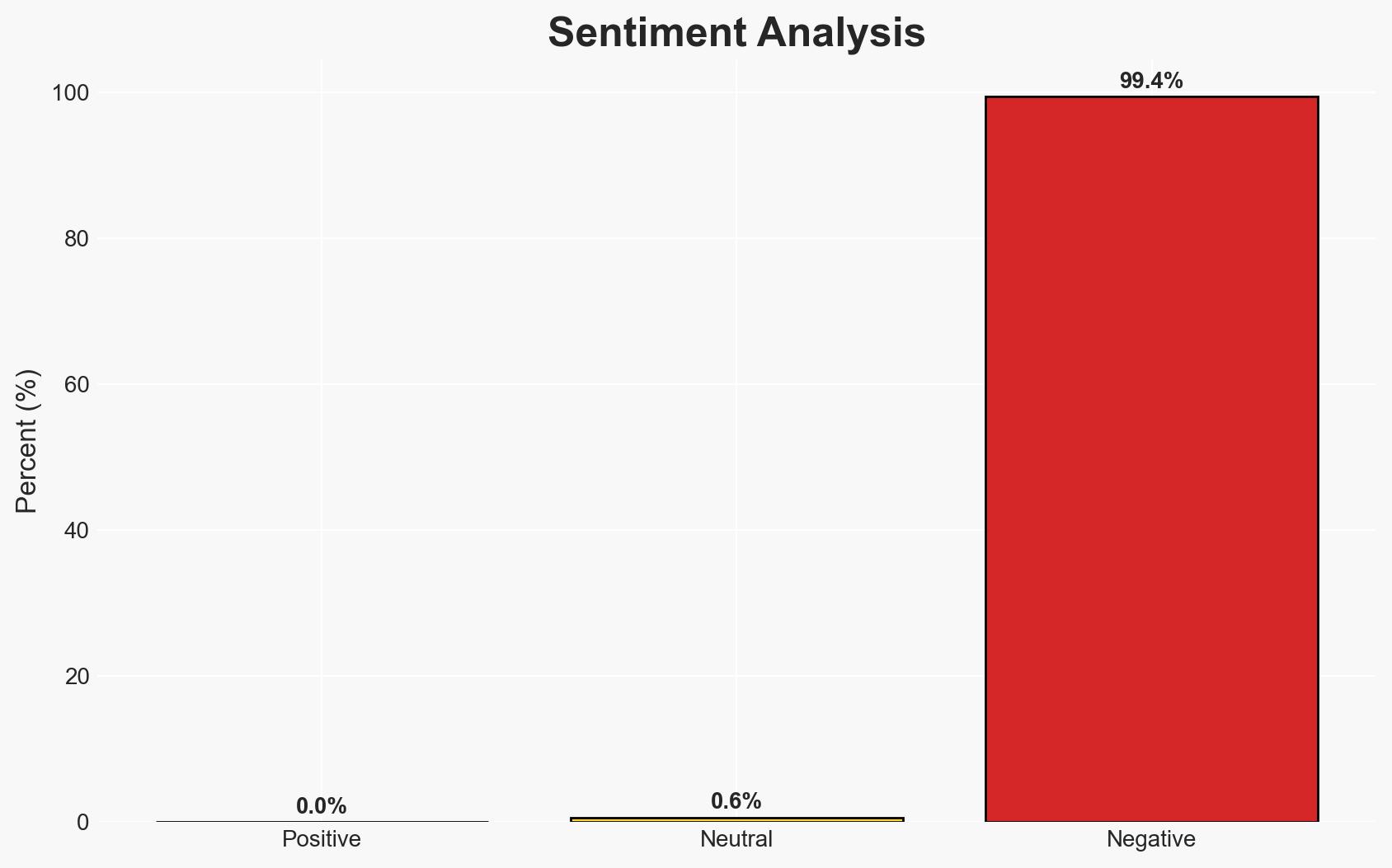
Intelligence Report: US chip testing firm shrugged off ransomware hit as minor – then came the data leak
1. BLUF (Bottom Line Up Front)
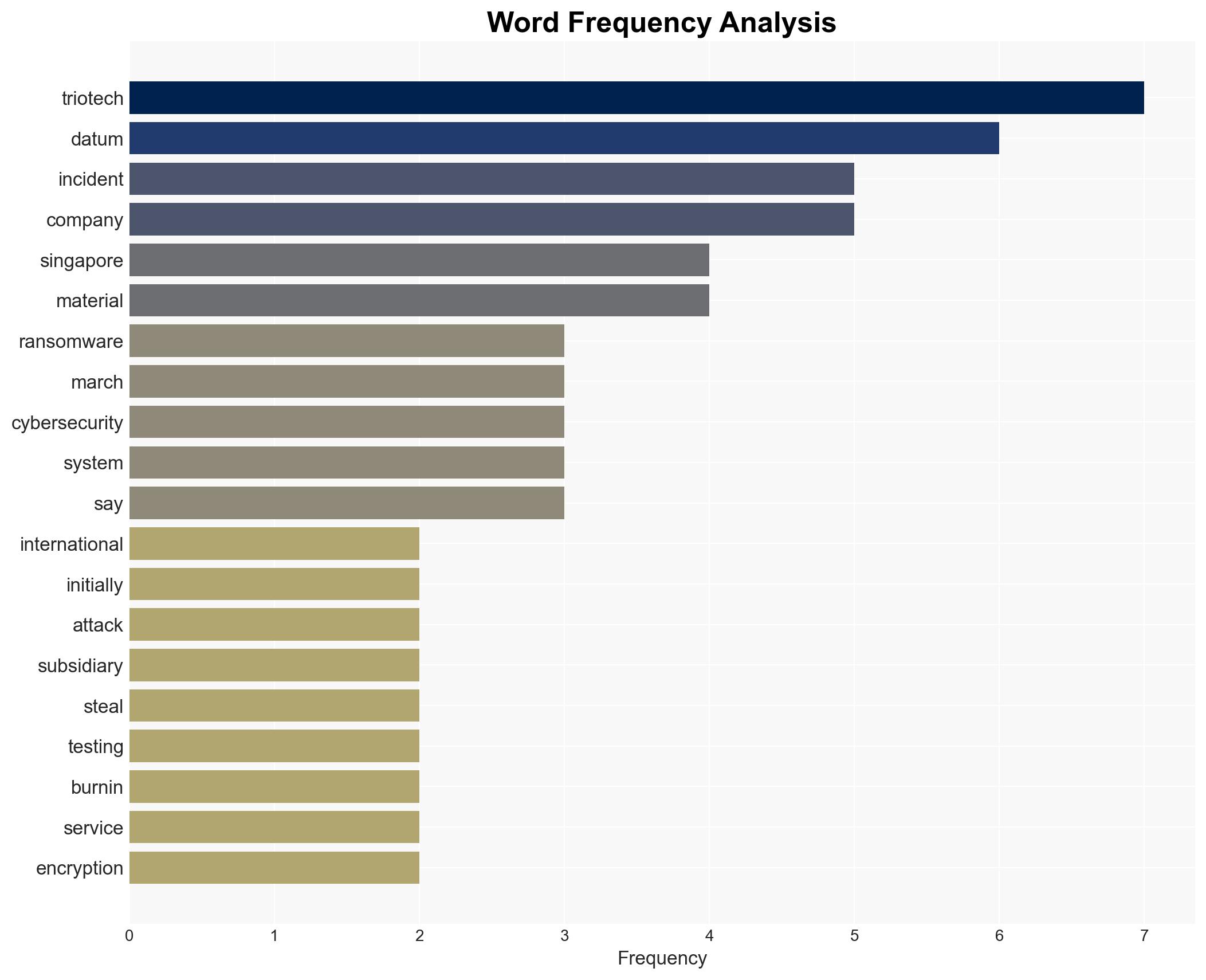
Trio-Tech International’s initial assessment of a ransomware attack on its Singapore subsidiary as immaterial was reversed following a data leak, indicating a significant cybersecurity event. The incident affects the company’s operations across multiple regions and sectors, with moderate confidence in the assessment that the financial impact may be understated. The situation remains fluid with potential for further developments.
2. Competing Hypotheses
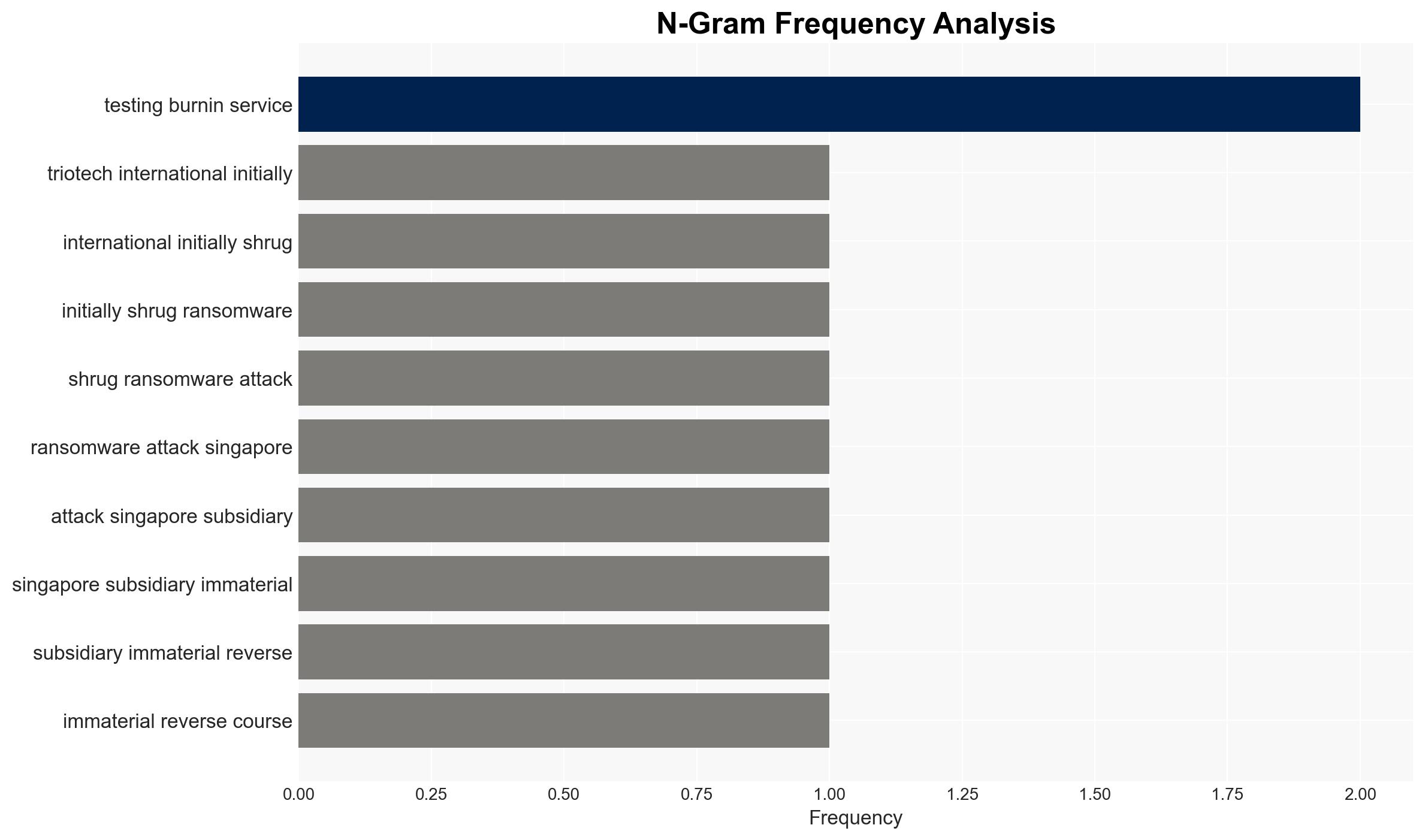
- Hypothesis A: The ransomware attack was primarily aimed at disrupting operations, with data theft being a secondary consequence. This is supported by the initial encryption of files and the company’s initial assessment of immaterial impact. However, the subsequent data leak contradicts this, suggesting a more complex intent.
- Hypothesis B: The primary intent of the attack was data theft, using ransomware as a diversion or pressure tactic. The escalation from encryption to data disclosure supports this, as does the lack of immediate operational disruption. However, the absence of a ransom demand or group claiming responsibility leaves this uncertain.
- Assessment: Hypothesis B is currently better supported due to the data leak’s timing and impact, suggesting premeditated data theft. Key indicators that could shift this judgment include identification of the responsible group or a ransom demand.
3. Key Assumptions and Red Flags
- Assumptions: The attackers had prior knowledge of Trio-Tech’s data value; the company’s cybersecurity measures were insufficient; the financial impact is currently underestimated.
- Information Gaps: Identity of the attackers; specific data compromised; any ransom demands made or payments executed.
- Bias & Deception Risks: Trio-Tech’s public statements may downplay the incident to protect stock value; lack of claims by known groups could indicate a new or evolving threat actor.
4. Implications and Strategic Risks
The incident could evolve into a broader cybersecurity threat, impacting Trio-Tech’s reputation and client trust. It may also signal vulnerabilities in similar firms, prompting industry-wide scrutiny.
- Political / Geopolitical: Potential regulatory scrutiny and international cooperation in cybersecurity enforcement.
- Security / Counter-Terrorism: Increased risk of similar attacks on critical infrastructure and technology sectors.
- Cyber / Information Space: Possible rise in ransomware attacks combining data theft, necessitating enhanced cybersecurity protocols.
- Economic / Social: Potential financial losses for Trio-Tech and its clients, with broader implications for the semiconductor supply chain.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of Trio-Tech’s network for further breaches; engage with cybersecurity experts to assess vulnerabilities; increase communication with affected stakeholders.
- Medium-Term Posture (1–12 months): Develop resilience measures, including staff training and system upgrades; strengthen partnerships with cybersecurity firms and law enforcement.
- Scenario Outlook:
- Best: Rapid containment and resolution with minimal financial impact.
- Worst: Prolonged data exposure leading to significant financial and reputational damage.
- Most-Likely: Moderate financial impact with increased cybersecurity measures and industry awareness.
6. Key Individuals and Entities
- Trio-Tech International
- Singapore subsidiary of Trio-Tech
- Law enforcement in Singapore
- Cyber insurance provider (unnamed)
7. Thematic Tags
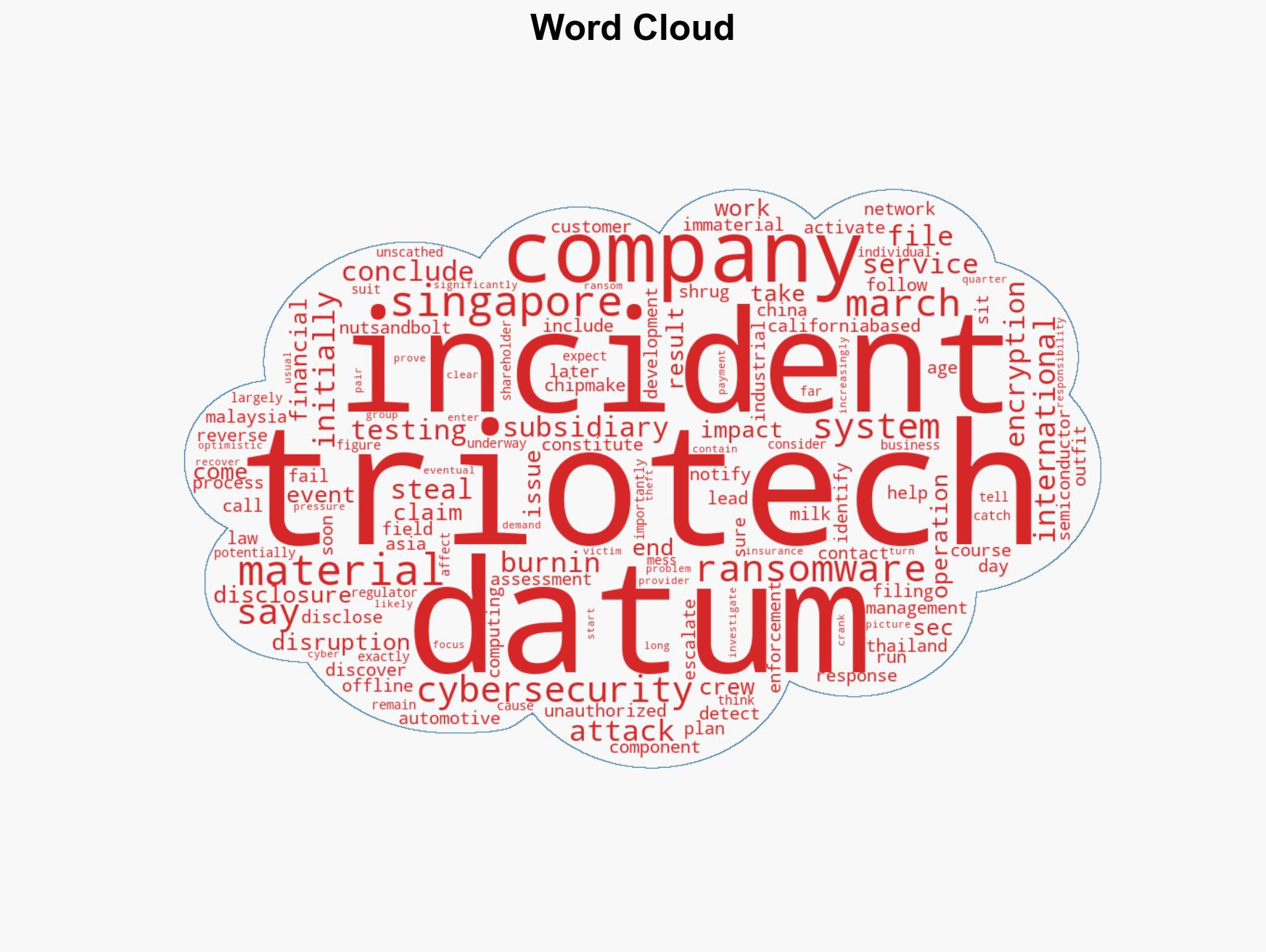
cybersecurity, ransomware, data breach, semiconductor industry, international operations, risk management, cyber insurance
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us