Trump’s Authority Key in Defining Response to Cyber Warfare Escalation
Published on: 2026-03-25
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Only Trump can decide when cyberwar turns into real war
1. BLUF (Bottom Line Up Front)
The determination of when a cyberattack warrants a kinetic military response remains ambiguous, with significant discretion afforded to the U.S. President. This lack of a well-defined threshold poses risks of inconsistent responses to cyber threats. The current environment is characterized by increased cyber threats and a potentially under-resourced defense posture. Overall confidence in this assessment is moderate, given the limited clarity on decision-making criteria.
2. Competing Hypotheses
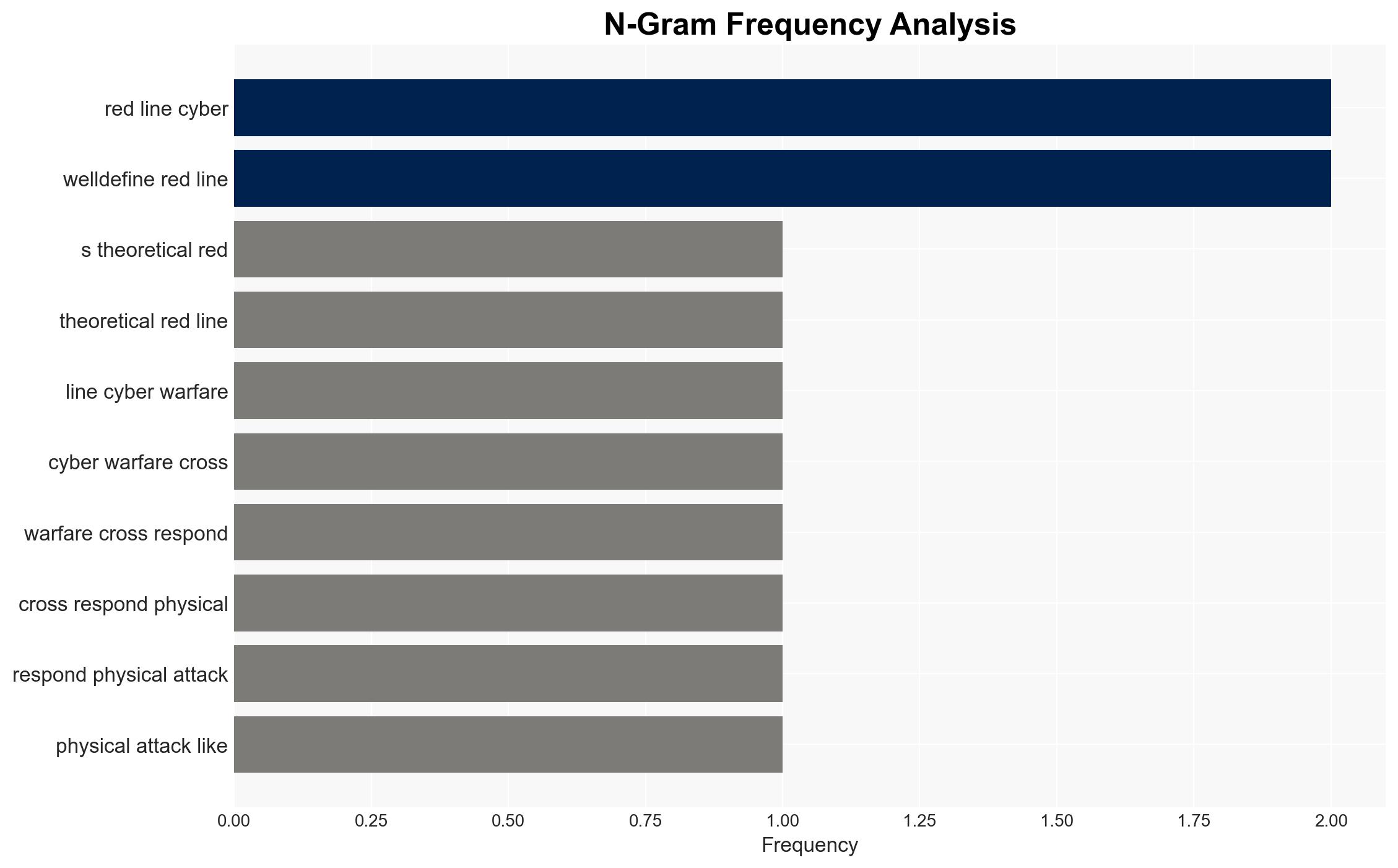
- Hypothesis A: The absence of a defined red line for cyberattacks allows for strategic flexibility, enabling tailored responses to diverse threats. This is supported by the argument for presidential discretion in determining responses. However, it lacks clear criteria, which could lead to unpredictable outcomes.
- Hypothesis B: A lack of defined criteria for cyber responses increases the risk of inconsistent and potentially escalatory actions, as evidenced by past incidents like the Sony hack. This hypothesis is supported by calls for minimum standards for response, such as loss of life or infrastructure damage.
- Assessment: Hypothesis B is currently better supported due to historical precedents and the potential for misinterpretation of cyber incidents as acts of war. Key indicators that could shift this judgment include the establishment of clearer guidelines or a significant cyber incident prompting a kinetic response.
3. Key Assumptions and Red Flags
- Assumptions: The U.S. President will continue to have significant discretion in cyber response decisions; cyber threats will persist and potentially escalate; international norms on cyber warfare remain underdeveloped.
- Information Gaps: Specific criteria used by the President to determine a kinetic response to cyber incidents; current status and capabilities of U.S. cyber defense infrastructure.
- Bias & Deception Risks: Potential bias in favor of military solutions over diplomatic or cyber-specific responses; risk of adversaries exploiting ambiguity to test U.S. thresholds.
4. Implications and Strategic Risks
Ambiguity in cyber response thresholds could lead to strategic miscalculations and unintended escalation in international conflicts. The evolving cyber threat landscape necessitates adaptive and coherent policy frameworks.
- Political / Geopolitical: Potential for strained alliances if U.S. responses are perceived as disproportionate or inconsistent.
- Security / Counter-Terrorism: Increased vulnerability to cyber threats could embolden adversaries, impacting national security.
- Cyber / Information Space: Ongoing cyber intrusions could degrade public trust in digital infrastructures and government capabilities.
- Economic / Social: Persistent cyber threats could lead to economic disruptions and societal unease, particularly if critical infrastructure is targeted.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive review of current cyber defense capabilities and establish interim guidelines for cyber response thresholds.
- Medium-Term Posture (1–12 months): Develop international partnerships to establish norms for cyber warfare and invest in cyber resilience and workforce development.
- Scenario Outlook:
- Best Case: Establishment of clear guidelines and international norms reduces the risk of escalation (trigger: successful diplomatic engagement).
- Worst Case: A significant cyberattack prompts an uncalibrated military response, escalating into broader conflict (trigger: major cyber incident targeting critical infrastructure).
- Most Likely: Continued ambiguity with incremental improvements in cyber defense and policy (trigger: ongoing cyber incidents without clear resolution).
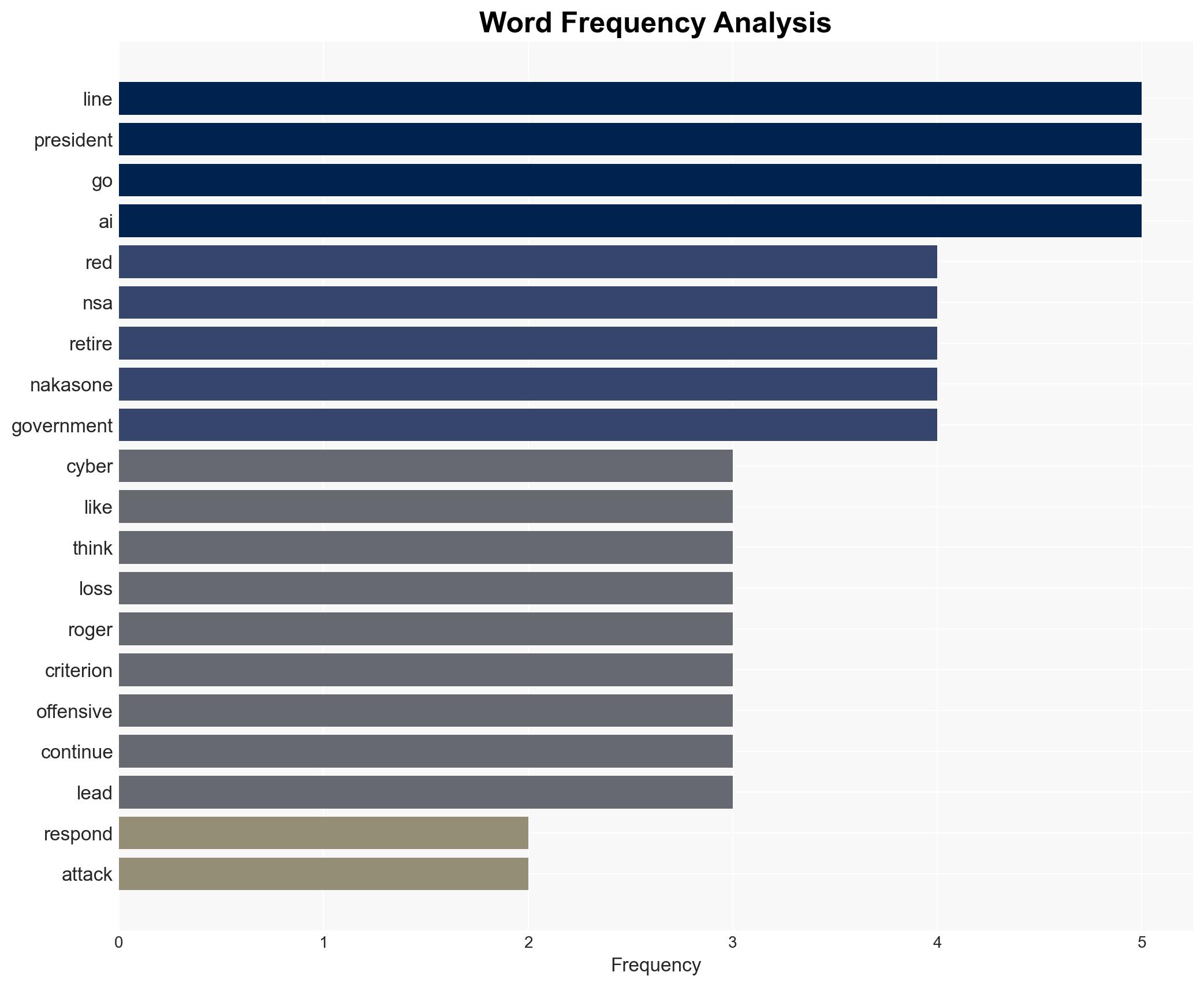
6. Key Individuals and Entities
- Donald Trump (U.S. President)
- Paul Nakasone (Former NSA Director)
- Mike Rogers (Former NSA Director)
- U.S. Cyber Command
- Chinese Government (Volt and Salt Typhoon)
- North Korean State Actors
7. Thematic Tags
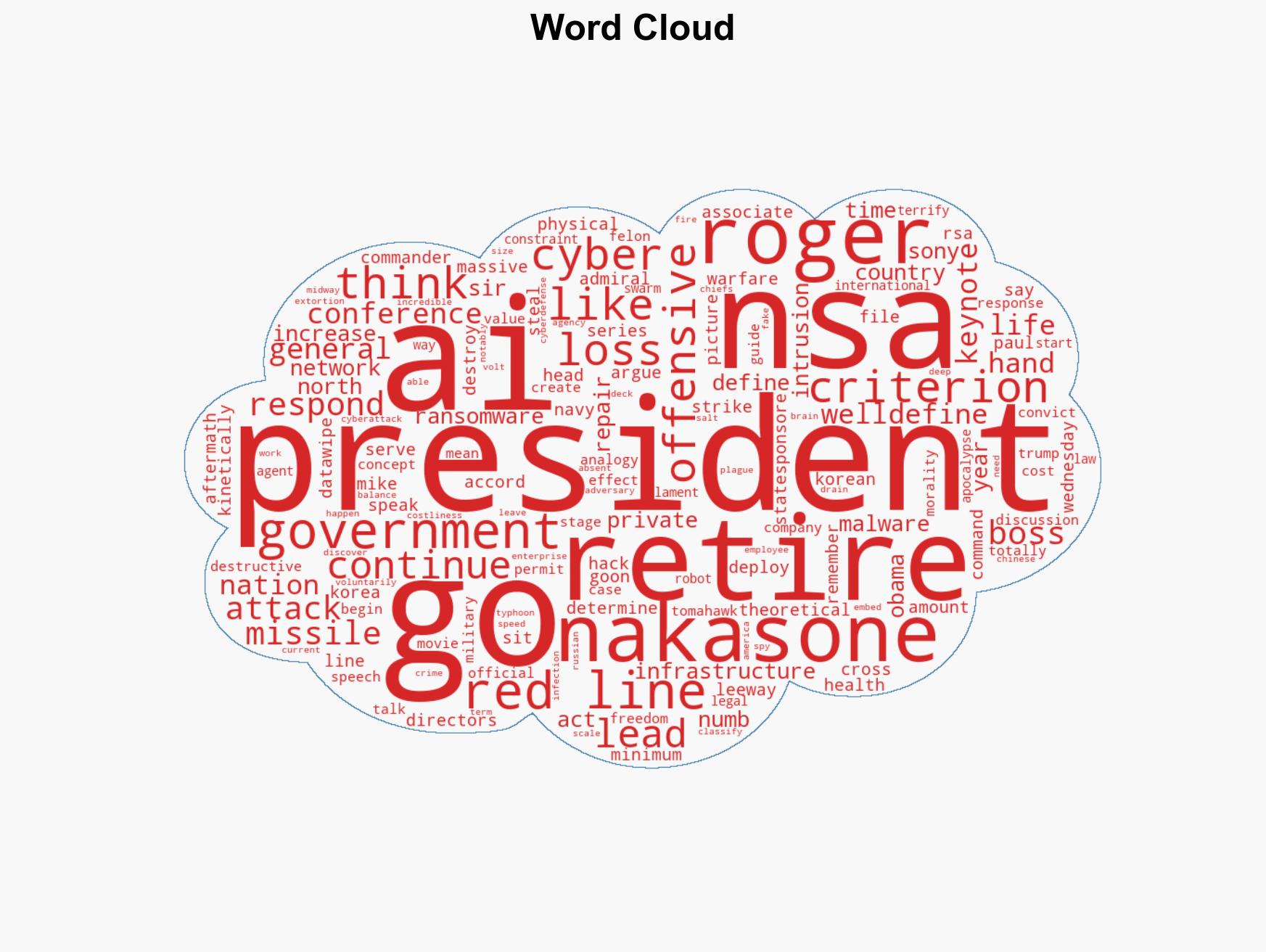
cybersecurity, cyber warfare, kinetic response, national security, cyber defense, international norms, strategic ambiguity, presidential discretion
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us