Trump’s Cyber Strategy: A Shift Toward Global Cyber Resilience and Risk-Based Security Governance
Published on: 2026-03-09
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: President Trump’s Cyber Strategy for America What It Means for the US and Why It Matters Globally
1. BLUF (Bottom Line Up Front)
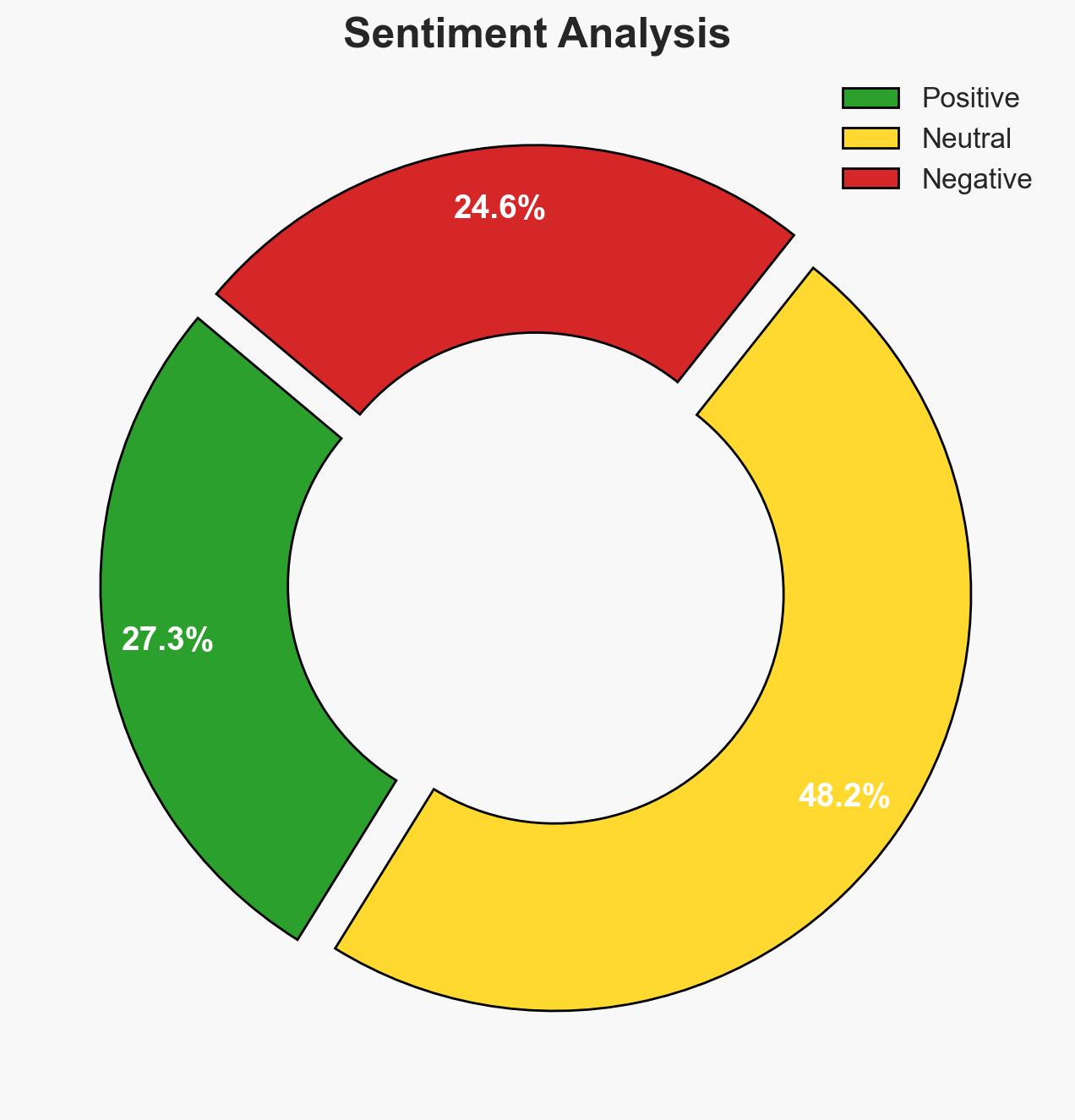
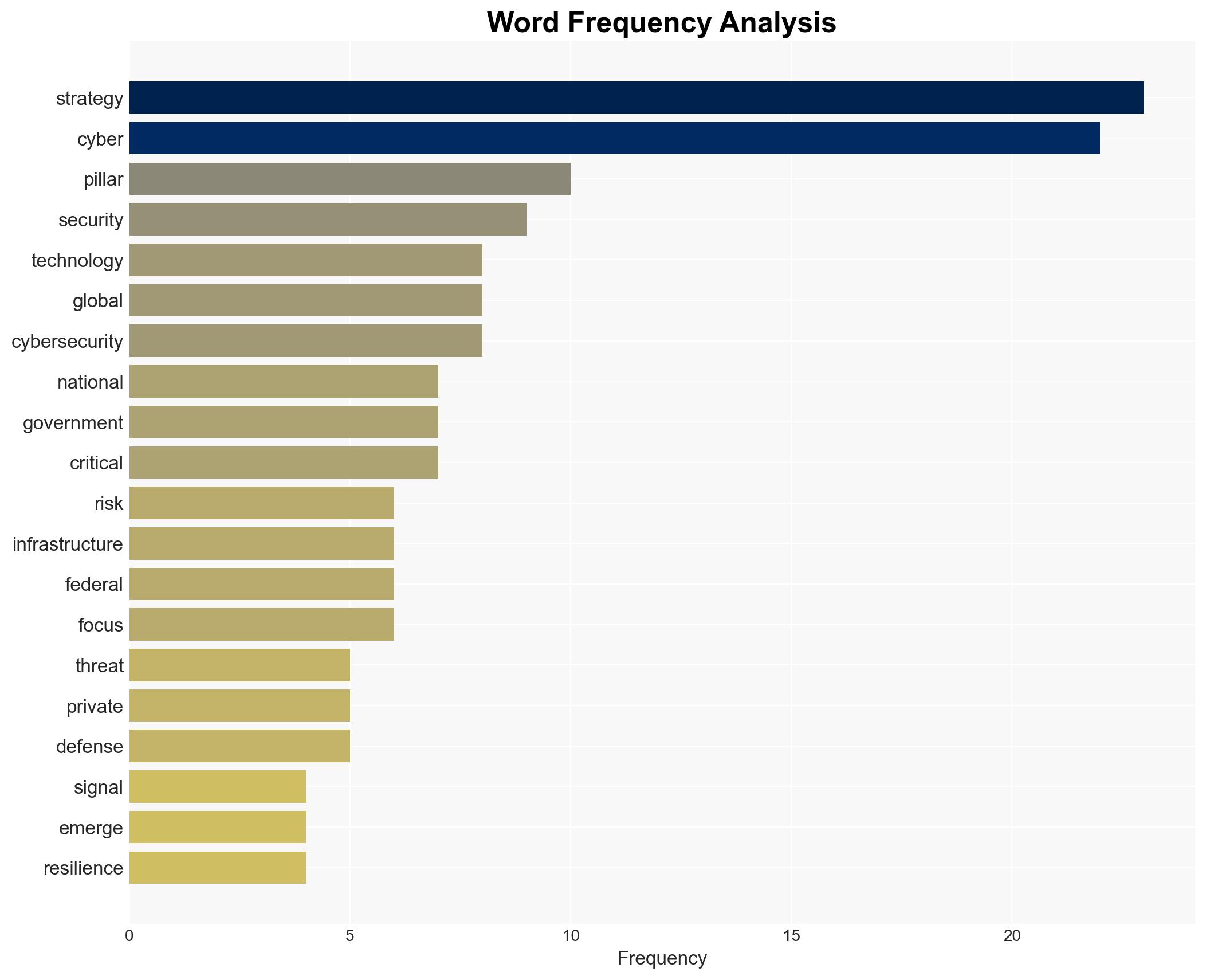
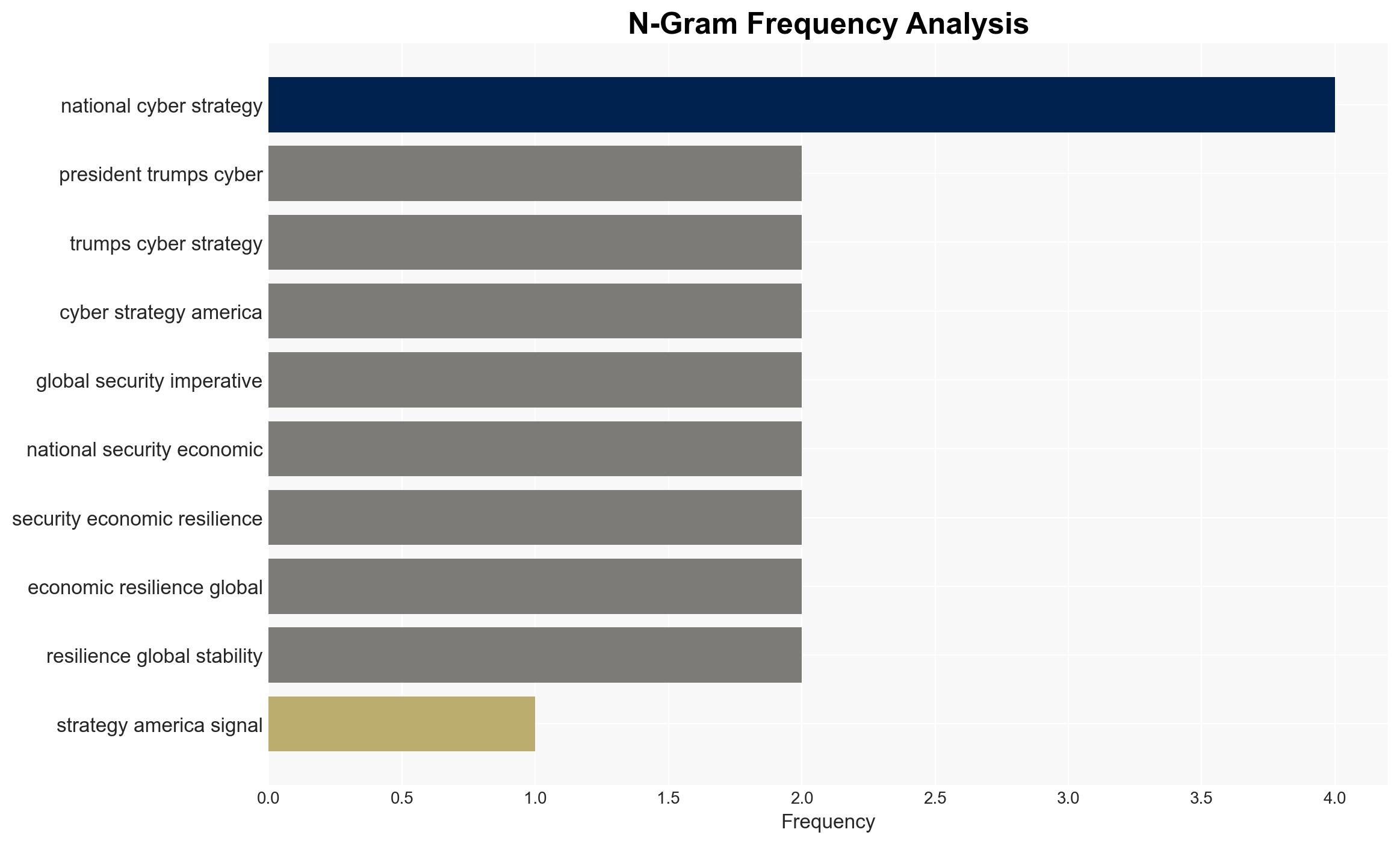
President Trump’s Cyber Strategy represents a significant shift towards risk-based cybersecurity governance, emphasizing global cooperation and secure-by-design principles for emerging technologies. This strategy is likely to influence international cybersecurity norms and expectations, impacting both public and private sectors. Overall, there is moderate confidence in the strategy’s potential to enhance U.S. and global cyber resilience.
2. Competing Hypotheses
- Hypothesis A: The strategy will effectively consolidate U.S. cybersecurity efforts, leading to improved national and global cyber resilience. This is supported by the strategy’s focus on risk-based governance and secure-by-design principles. However, the short length of the document and lack of detailed implementation plans are uncertainties.
- Hypothesis B: The strategy may fail to achieve its objectives due to insufficient detail and potential resistance from stakeholders accustomed to existing compliance frameworks. The concise nature of the document and the need for broad cooperation are potential weaknesses.
- Assessment: Hypothesis A is currently better supported due to the strategy’s alignment with evolving cyber threats and its emphasis on global cooperation. Key indicators that could shift this judgment include the effectiveness of subsequent implementation plans and stakeholder buy-in.
3. Key Assumptions and Red Flags
- Assumptions: The strategy will be followed by detailed implementation plans; stakeholders will align with the new risk-based approach; global partners will cooperate with U.S. initiatives; secure-by-design principles can be effectively integrated into emerging technologies.
- Information Gaps: Specific details on implementation timelines and resource allocation; clarity on how the strategy will address existing cybersecurity challenges; stakeholder response and commitment levels.
- Bias & Deception Risks: Potential over-reliance on U.S. perspectives; underestimation of resistance from entrenched interests; possible misrepresentation of strategy effectiveness by adversaries.
4. Implications and Strategic Risks
The strategy’s focus on risk-based governance and global cooperation could reshape international cybersecurity norms, but its success depends on effective implementation and stakeholder engagement.
- Political / Geopolitical: Potential for increased U.S. influence in setting global cybersecurity standards; risk of geopolitical tensions if perceived as U.S.-centric.
- Security / Counter-Terrorism: Enhanced resilience against cyber threats could reduce vulnerabilities to cyber-terrorism; however, adversaries may adapt tactics in response.
- Cyber / Information Space: Emphasis on secure-by-design could drive innovation in cybersecurity technologies; potential for increased cyber operations as adversaries test U.S. defenses.
- Economic / Social: Improved cybersecurity could bolster economic stability and protect critical infrastructure; however, transition costs and resistance from industry could pose challenges.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor stakeholder reactions and initial implementation steps; engage with international partners to gauge cooperation levels.
- Medium-Term Posture (1–12 months): Develop partnerships to support secure-by-design initiatives; enhance capabilities for risk-based governance and threat detection.
- Scenario Outlook:
- Best: Successful implementation leads to enhanced global cyber resilience and reduced threat levels.
- Worst: Strategy fails to gain traction, leading to fragmented cybersecurity efforts and increased vulnerabilities.
- Most-Likely: Gradual improvement in cybersecurity posture with ongoing challenges in stakeholder alignment and implementation.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
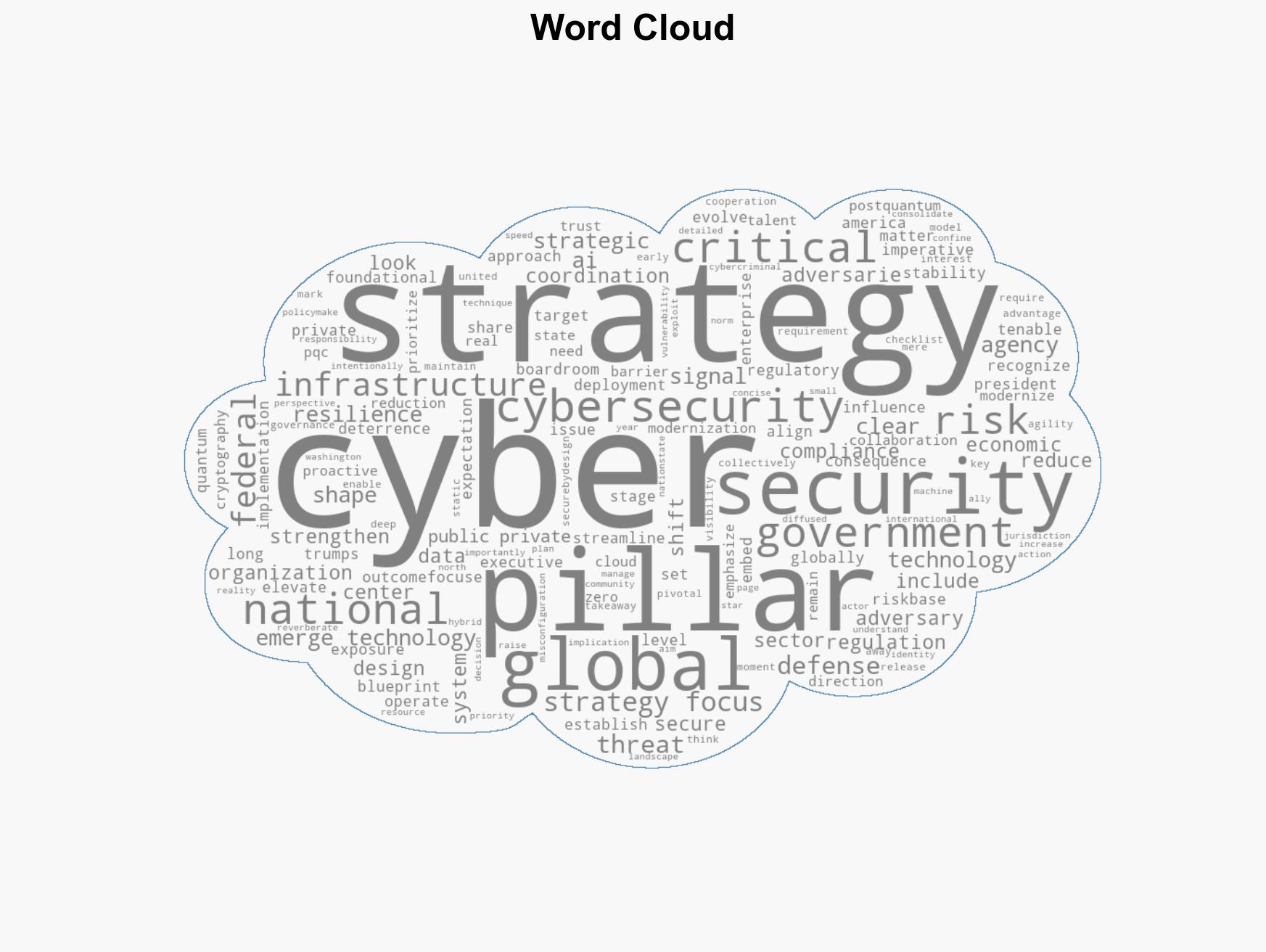
cybersecurity, cybersecurity strategy, risk-based governance, global cooperation, secure-by-design, national security, cyber resilience, emerging technologies
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model hostile behavior to identify vulnerabilities.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us