U.S. Defense Grants Linked to Researchers Tied to Chinese Government and Military Entities
Published on: 2026-02-23
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
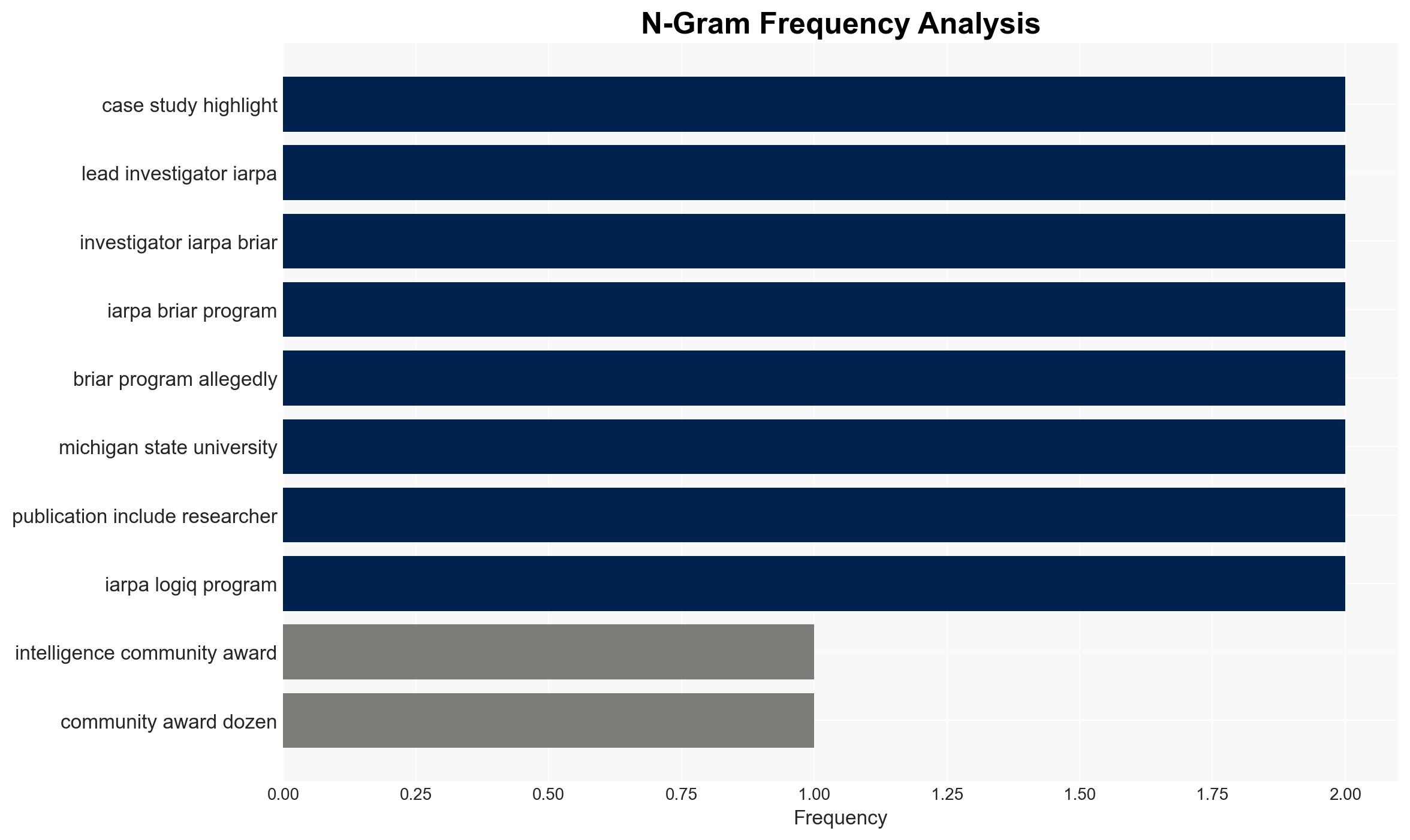
Intelligence Report: EXCLUSIVE US Intel Funded Projects Riddled With Chinese Govt-Linked Researchers
1. BLUF (Bottom Line Up Front)
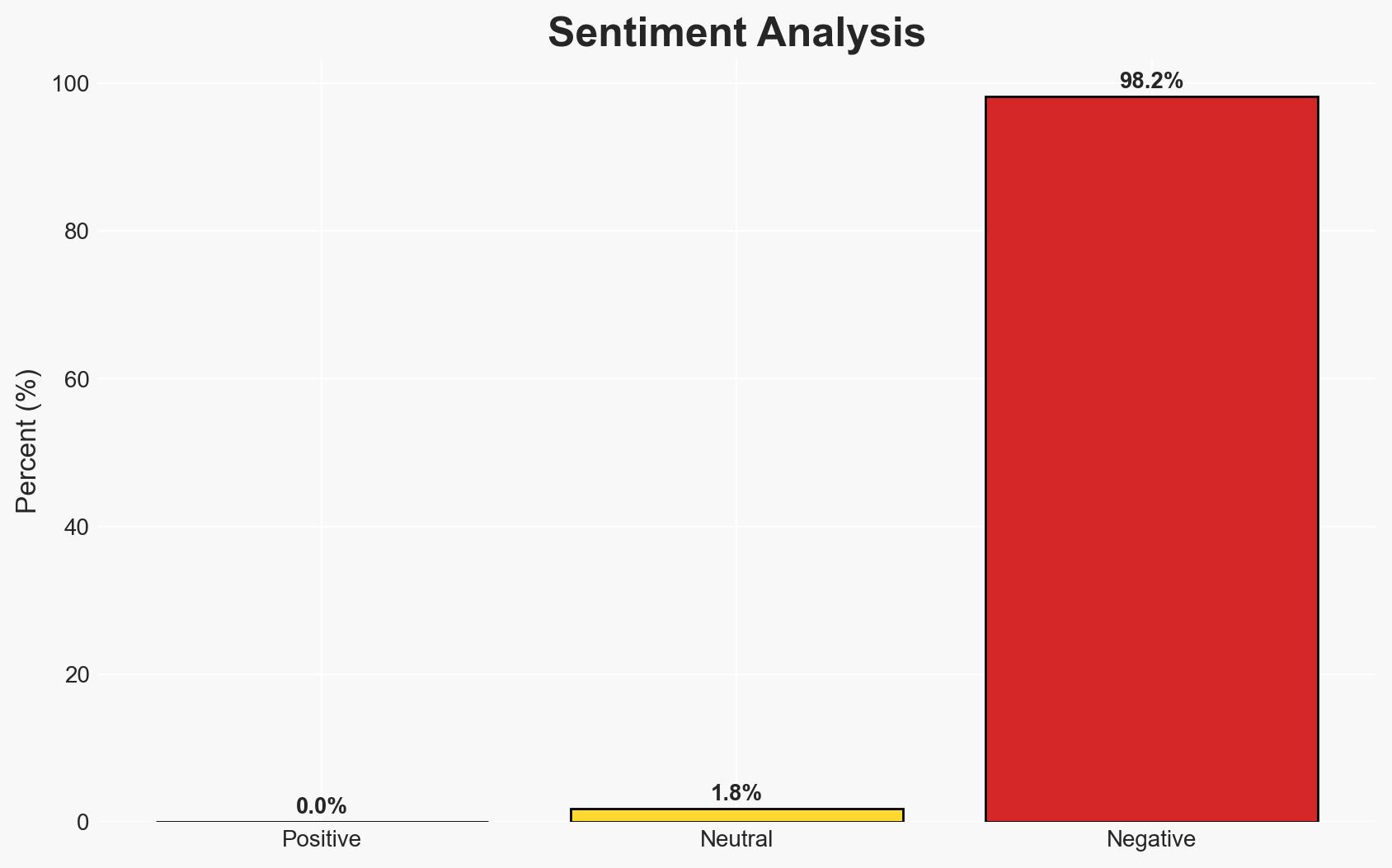
The involvement of Chinese government-linked researchers in U.S. intelligence-funded projects poses a significant risk of technology transfer to a potential adversary, potentially undermining U.S. national security. The most likely hypothesis is that these collaborations are part of a deliberate Chinese strategy to acquire sensitive U.S. defense technologies. This assessment is made with moderate confidence due to incomplete data on the extent of these collaborations and their impact.
2. Competing Hypotheses
- Hypothesis A: The presence of Chinese-affiliated researchers in U.S. defense projects is part of a strategic effort by China to acquire sensitive technologies and methodologies. Supporting evidence includes the simultaneous involvement of these researchers in Chinese government-tied institutions and the specific targeting of high-value projects. Key uncertainties include the level of oversight and the extent of data transfer.
- Hypothesis B: The involvement of these researchers is coincidental or due to oversight failures in vetting processes, rather than a coordinated effort by China. Contradicting evidence includes the structured nature of the collaborations and the specific alignment with Chinese strategic interests.
- Assessment: Hypothesis A is currently better supported due to the pattern of involvement in strategically significant projects and the alignment with known Chinese intelligence objectives. Indicators that could shift this judgment include evidence of systemic vetting failures or additional data showing benign intentions.
3. Key Assumptions and Red Flags
- Assumptions: The Chinese government has strategic interests in acquiring U.S. defense technologies; U.S. vetting processes are insufficient to detect all foreign affiliations; Chinese researchers have access to sensitive project data.
- Information Gaps: The full extent of data and technology transfer; specific details of the collaborations and their outcomes; responses from ODNI and IARPA.
- Bias & Deception Risks: Potential source bias from the report’s authors; risk of Chinese disinformation or obfuscation regarding the true nature of the collaborations.
4. Implications and Strategic Risks
This development could exacerbate U.S.-China tensions and impact global technological leadership dynamics. It may lead to increased scrutiny and restrictions on international research collaborations.
- Political / Geopolitical: Potential for diplomatic friction and policy shifts towards stricter research collaboration regulations.
- Security / Counter-Terrorism: Increased risk of compromised defense technologies impacting U.S. military capabilities.
- Cyber / Information Space: Potential for cyber-espionage activities to exploit research data and methodologies.
- Economic / Social: Possible impacts on academic and research institution funding and international partnerships.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive review of current and past research collaborations; enhance vetting processes for foreign affiliations.
- Medium-Term Posture (1–12 months): Develop stronger inter-agency collaboration to monitor and mitigate foreign influence in sensitive research areas; establish clearer guidelines for international research partnerships.
- Scenario Outlook:
- Best: Strengthened vetting processes prevent further technology transfer.
- Worst: Continued technology leakage leads to significant strategic disadvantages.
- Most-Likely: Incremental improvements in oversight reduce but do not eliminate risks.
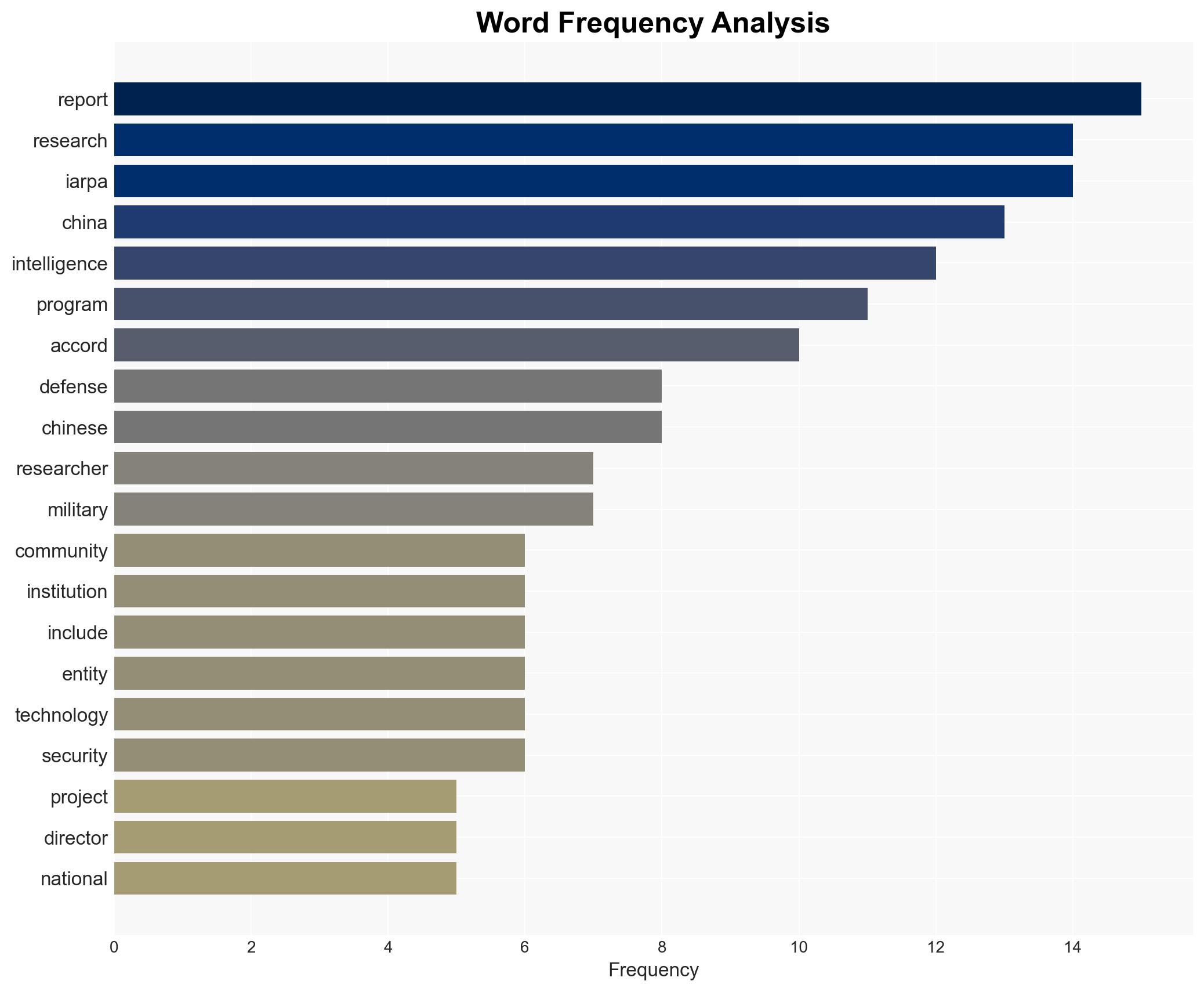
6. Key Individuals and Entities
- Intelligence Advanced Research Projects Activity (IARPA)
- Office of the Director of National Intelligence (ODNI)
- Parallax Advanced Research
- People’s Liberation Army (PLA)
- Michigan State University faculty member (unnamed)
7. Thematic Tags
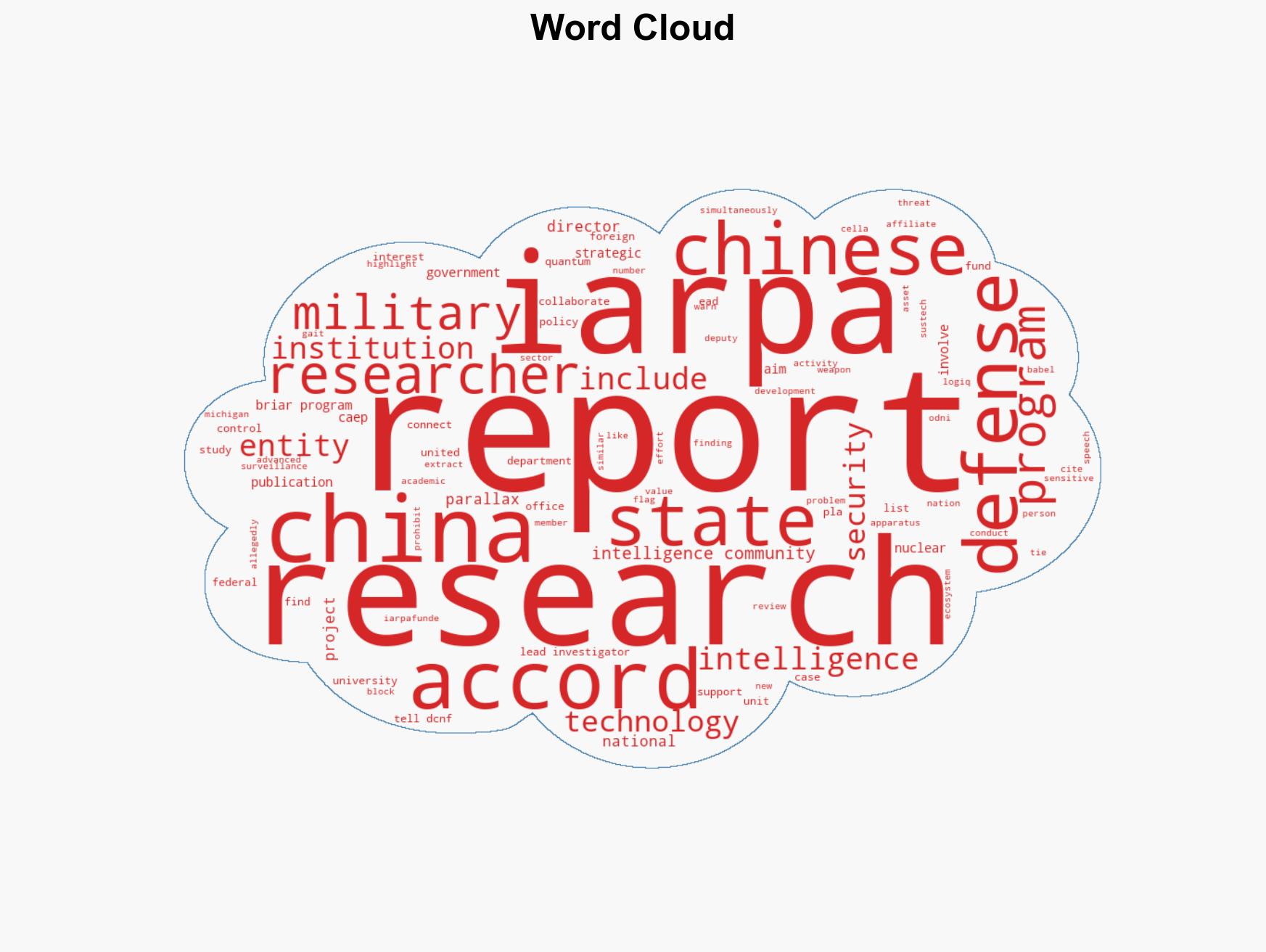
national security threats, counter-intelligence, technology transfer, research collaboration, national security, Chinese espionage, defense research, intelligence oversight
Structured Analytic Techniques Applied
- Cognitive Bias Stress Test: Expose and correct potential biases in assessments through red-teaming and structured challenge.
- Bayesian Scenario Modeling: Use probabilistic forecasting for conflict trajectories or escalation likelihood.
- Network Influence Mapping: Map relationships between state and non-state actors for impact estimation.
- Adversarial Threat Simulation: Model hostile behavior to identify vulnerabilities.
Explore more:
National Security Threats Briefs ·
Daily Summary ·
Support us