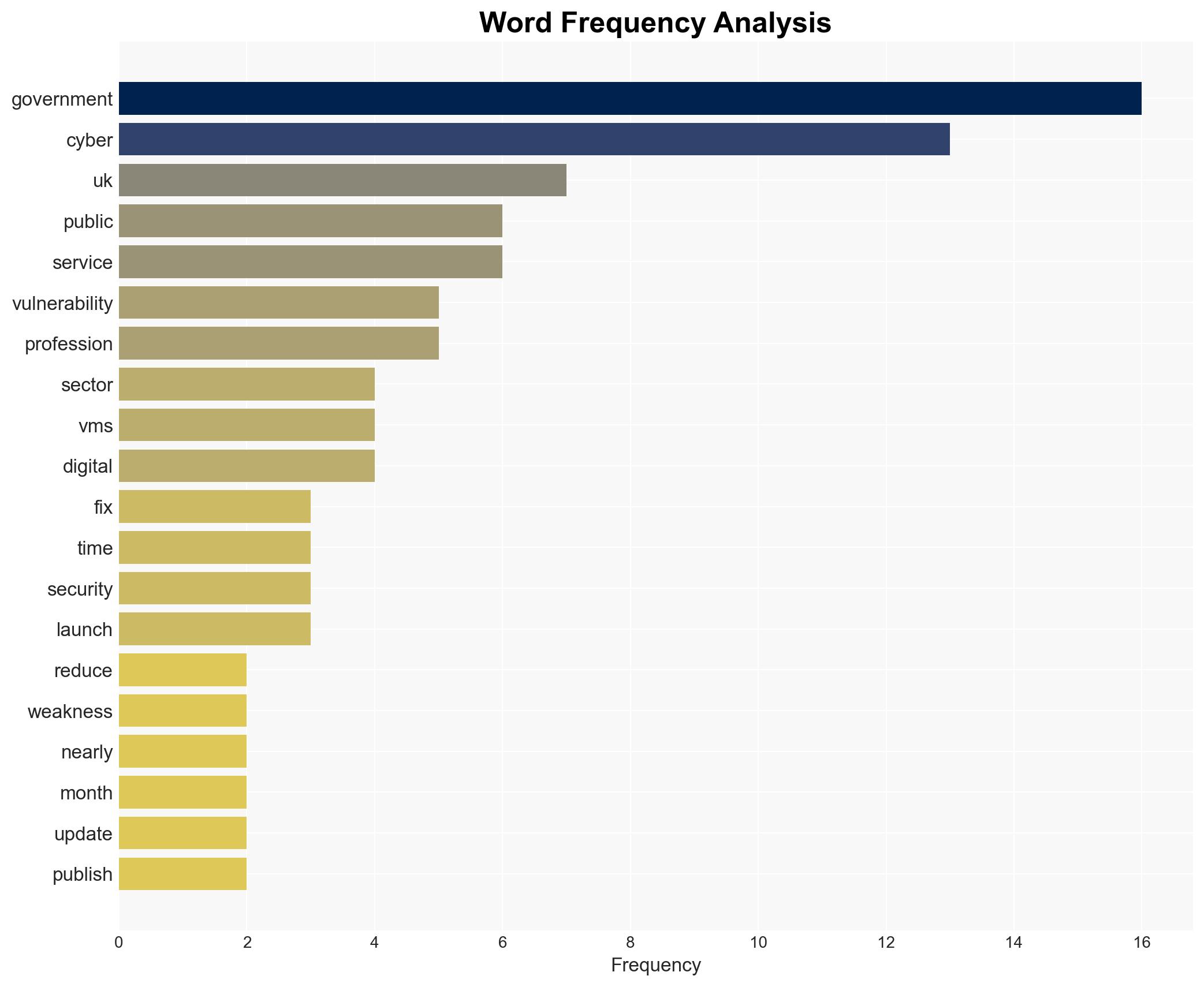
UK Government Reduces Critical Cyber Vulnerabilities by 75% and Speeds Fix Times by 87%
Published on: 2026-02-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: UK Vulnerability Monitoring Service Cuts Unresolved Security Flaws by 75
1. BLUF (Bottom Line Up Front)
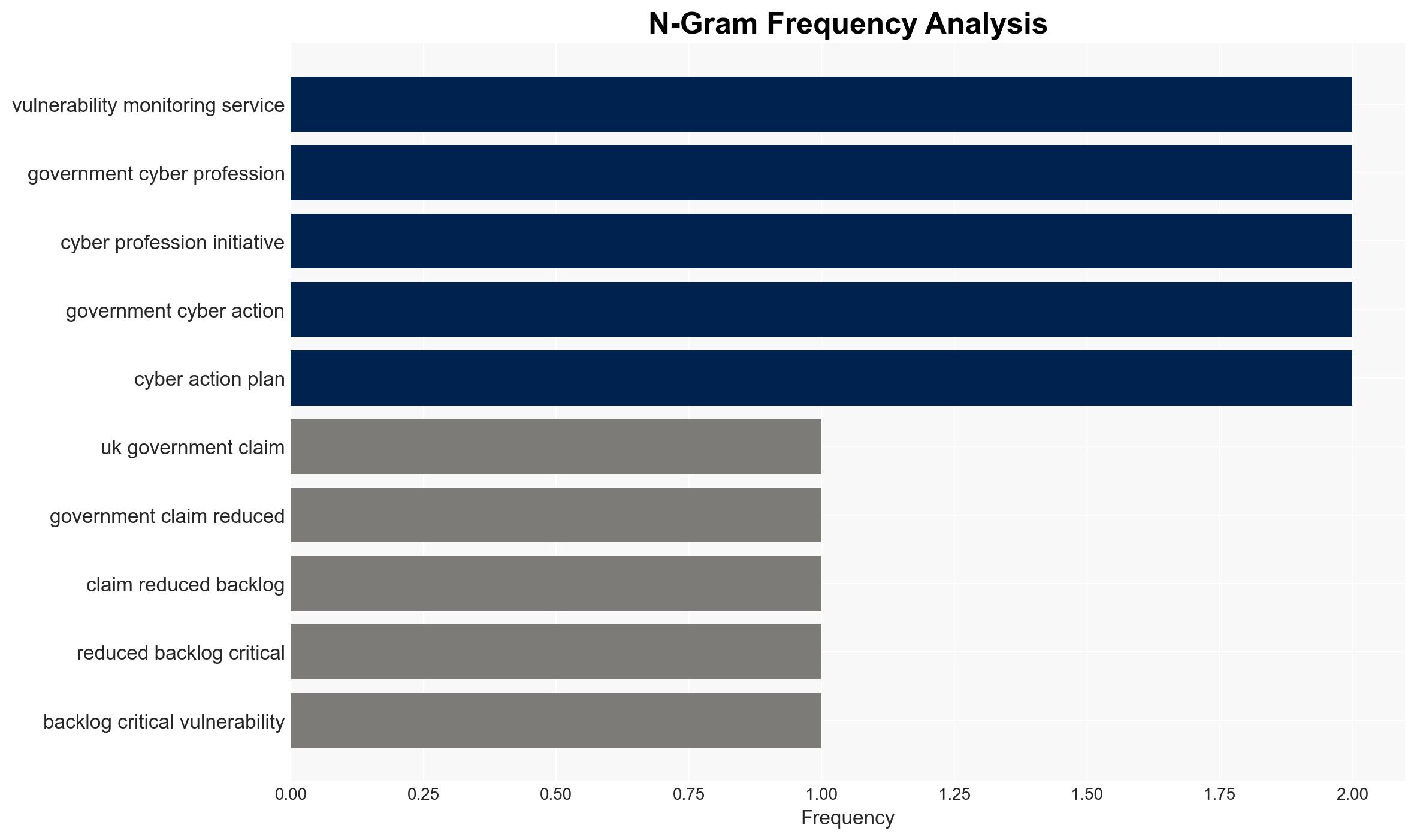
The UK government has significantly reduced its backlog of critical cyber vulnerabilities by 75% and decreased fix times by 87% through the implementation of a new Vulnerability Monitoring Service (VMS). This development enhances the resilience of public sector digital infrastructure against cyber threats. The initiative is likely to improve national security and public trust in digital services. Overall confidence in this assessment is moderate due to potential information gaps and the nascent stage of the initiative.
2. Competing Hypotheses
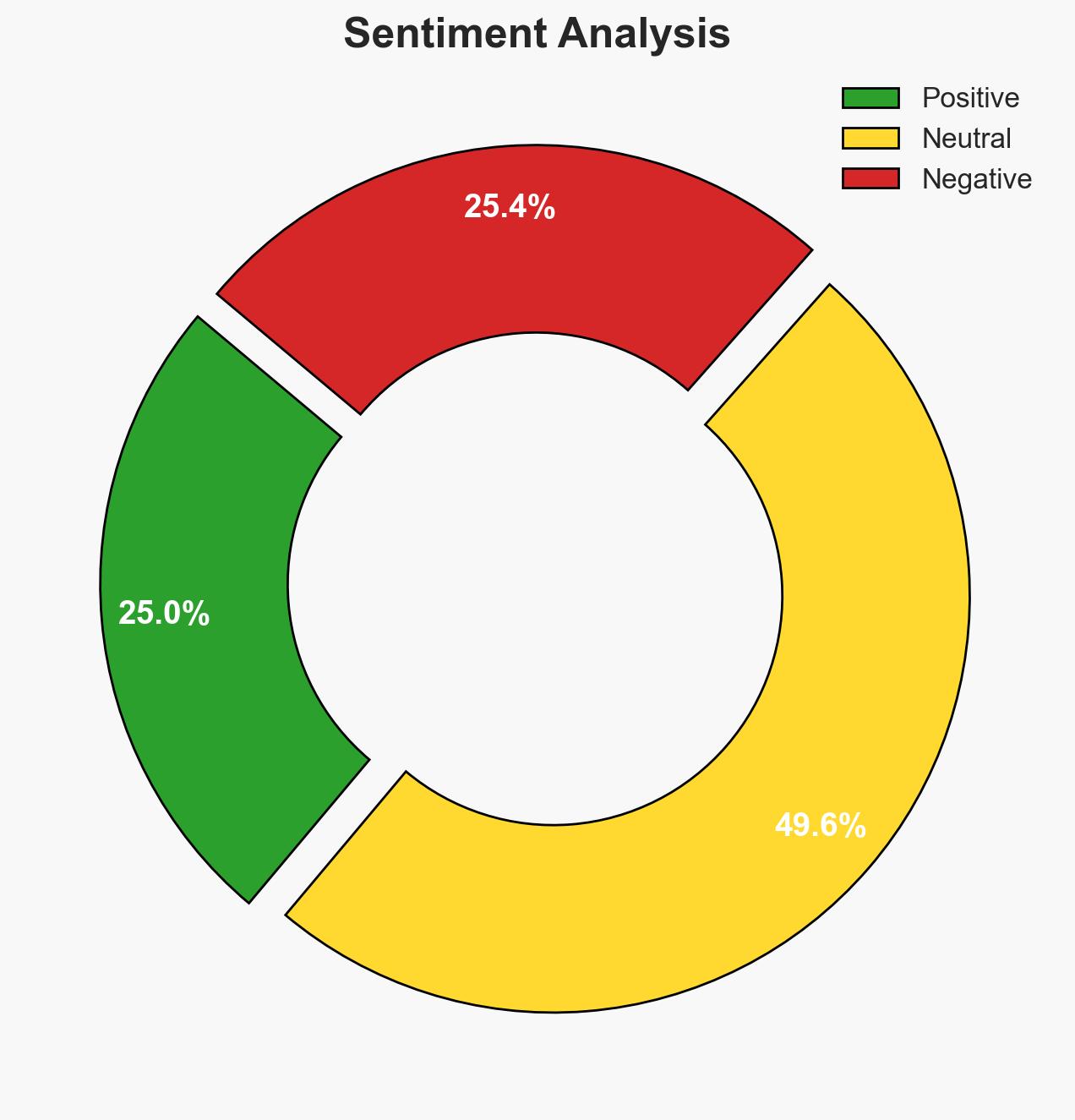
- Hypothesis A: The VMS has genuinely improved the UK government’s ability to manage cyber vulnerabilities, as evidenced by the reported reductions in backlog and fix times. However, the lack of independent verification and potential reporting bias are key uncertainties.
- Hypothesis B: The reported improvements are overstated, potentially due to political motivations to demonstrate progress in cyber defense. The absence of third-party validation and the possibility of selective reporting support this hypothesis.
- Assessment: Hypothesis A is currently better supported by the available evidence, given the detailed reporting of specific metrics and the alignment with broader government digital strategies. Future independent audits or third-party evaluations could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The VMS metrics are accurately reported; the reduction in vulnerabilities correlates with increased security; the VMS will continue to operate effectively.
- Information Gaps: Independent verification of the VMS’s effectiveness; detailed methodology of vulnerability assessments; long-term sustainability of the initiative.
- Bias & Deception Risks: Potential for confirmation bias in government reporting; lack of transparency in data collection and analysis; political bias influencing public communications.
4. Implications and Strategic Risks
This development could lead to enhanced public sector cyber resilience, but it also raises questions about the sustainability and transparency of the initiative. The success of the VMS may set a precedent for other nations, influencing global cyber defense strategies.
- Political / Geopolitical: Strengthened cyber defenses may enhance the UK’s international standing and influence in cybersecurity policy discussions.
- Security / Counter-Terrorism: Improved vulnerability management reduces the risk of cyber-attacks on critical infrastructure, potentially deterring state and non-state actors.
- Cyber / Information Space: The initiative may prompt adversaries to develop more sophisticated cyber tactics, leading to an arms race in cyber capabilities.
- Economic / Social: Enhanced digital security could boost public confidence in online services, fostering economic growth and digital innovation.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct an independent audit of the VMS; increase transparency in reporting; engage with international partners for knowledge sharing.
- Medium-Term Posture (1–12 months): Develop partnerships with private sector cybersecurity firms; invest in continuous training and recruitment of cyber professionals; monitor adversary responses to the VMS.
- Scenario Outlook:
- Best: Sustained reduction in vulnerabilities leads to a robust national cyber defense framework.
- Worst: Over-reliance on initial success leads to complacency and increased vulnerability to sophisticated attacks.
- Most-Likely: Continued improvements in cyber resilience with periodic challenges from evolving threats.
6. Key Individuals and Entities
- Ian Murray, Minister for Digital Government
- Department for Science, Innovation and Technology (DSIT)
- UK National Cyber Security Centre (NCSC)
- UK Cyber Security Council
7. Thematic Tags
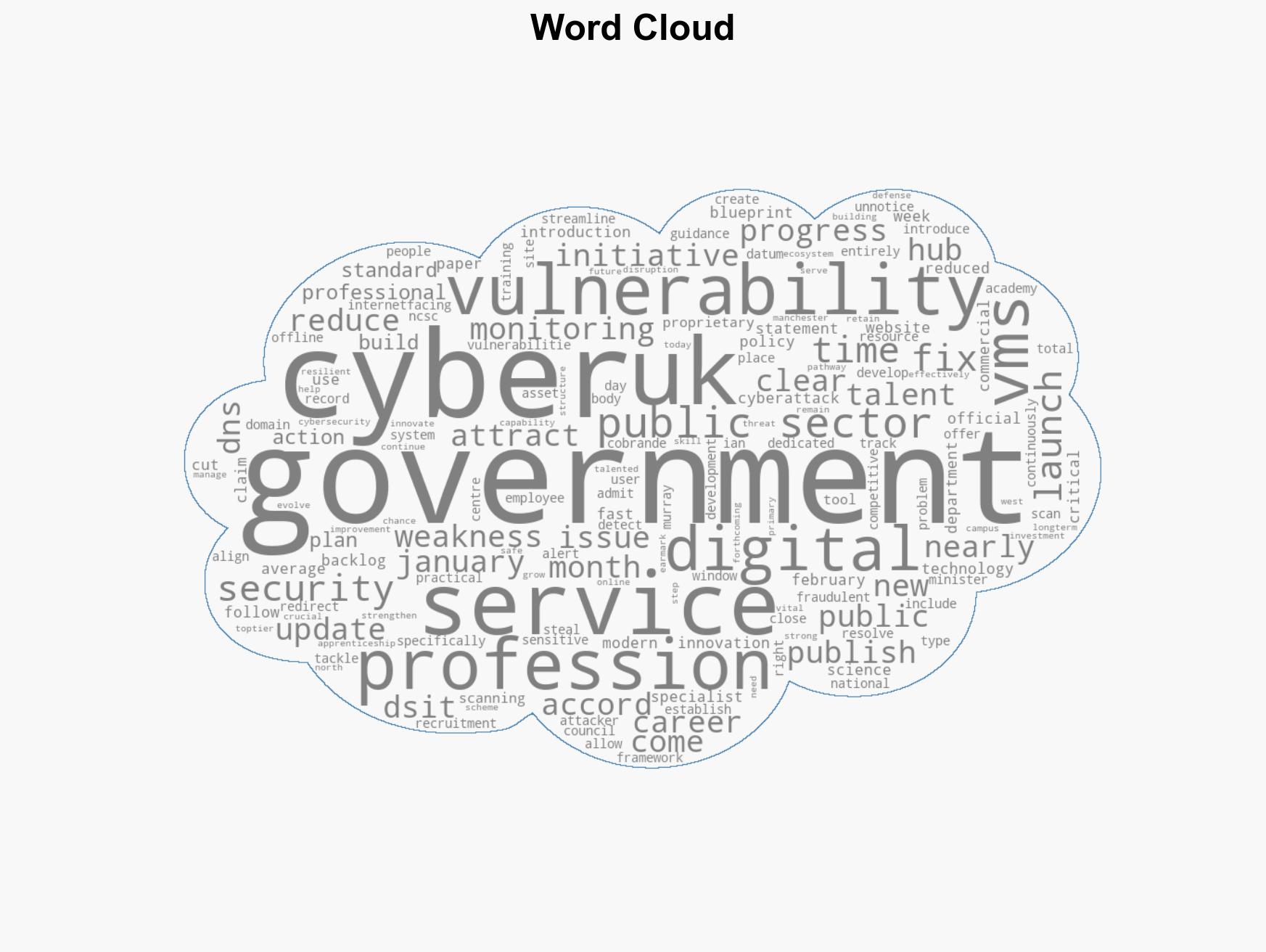
cybersecurity, public sector, vulnerability management, digital government, cyber defense, national security, cyber talent development
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us