UK Users Bypass Imgur’s Geo-Block by Implementing Network-Level Solutions
Published on: 2025-11-28
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Imgur Geo-Blocked the UK So I Geo-Unblocked My Network
1. BLUF (Bottom Line Up Front)
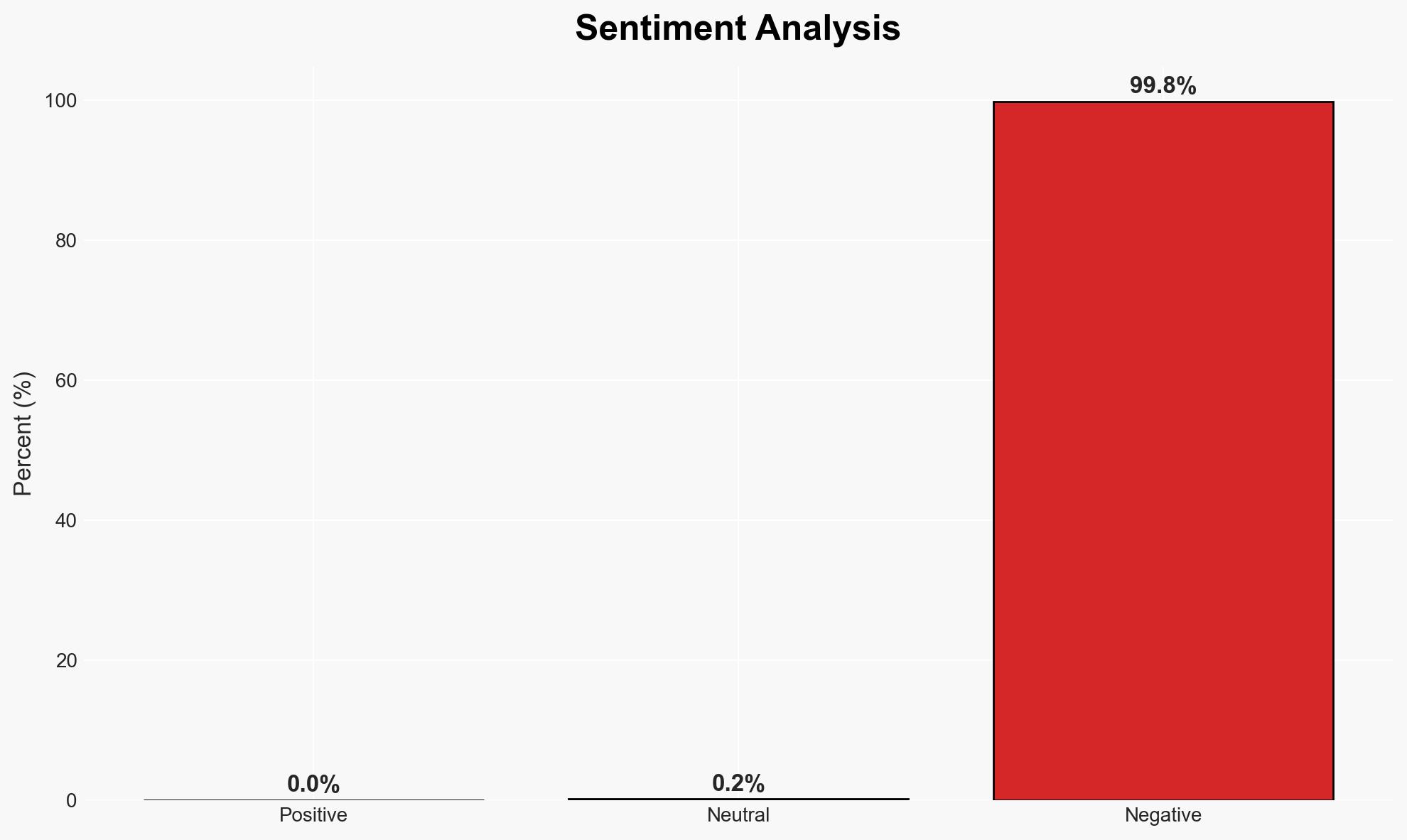
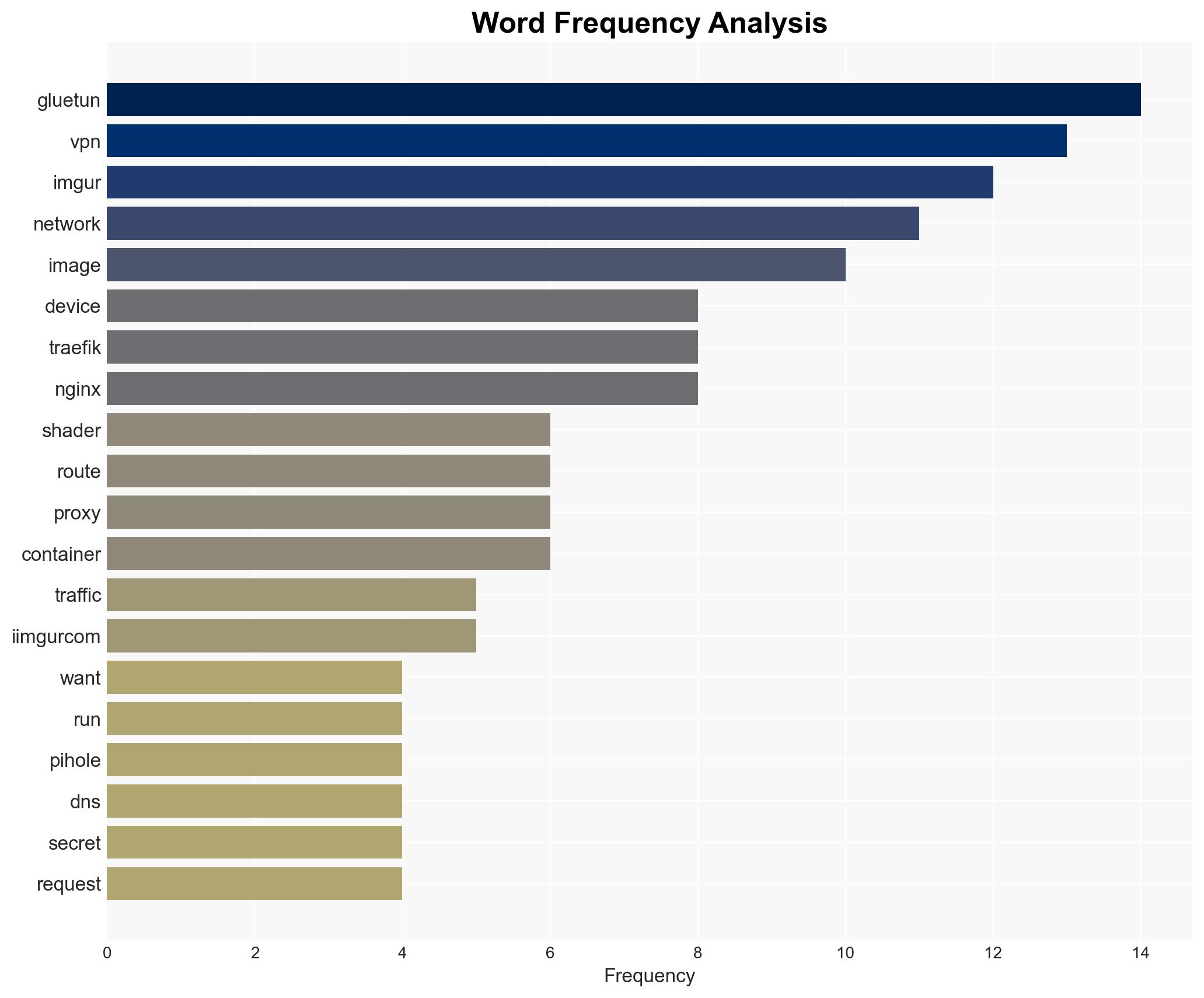
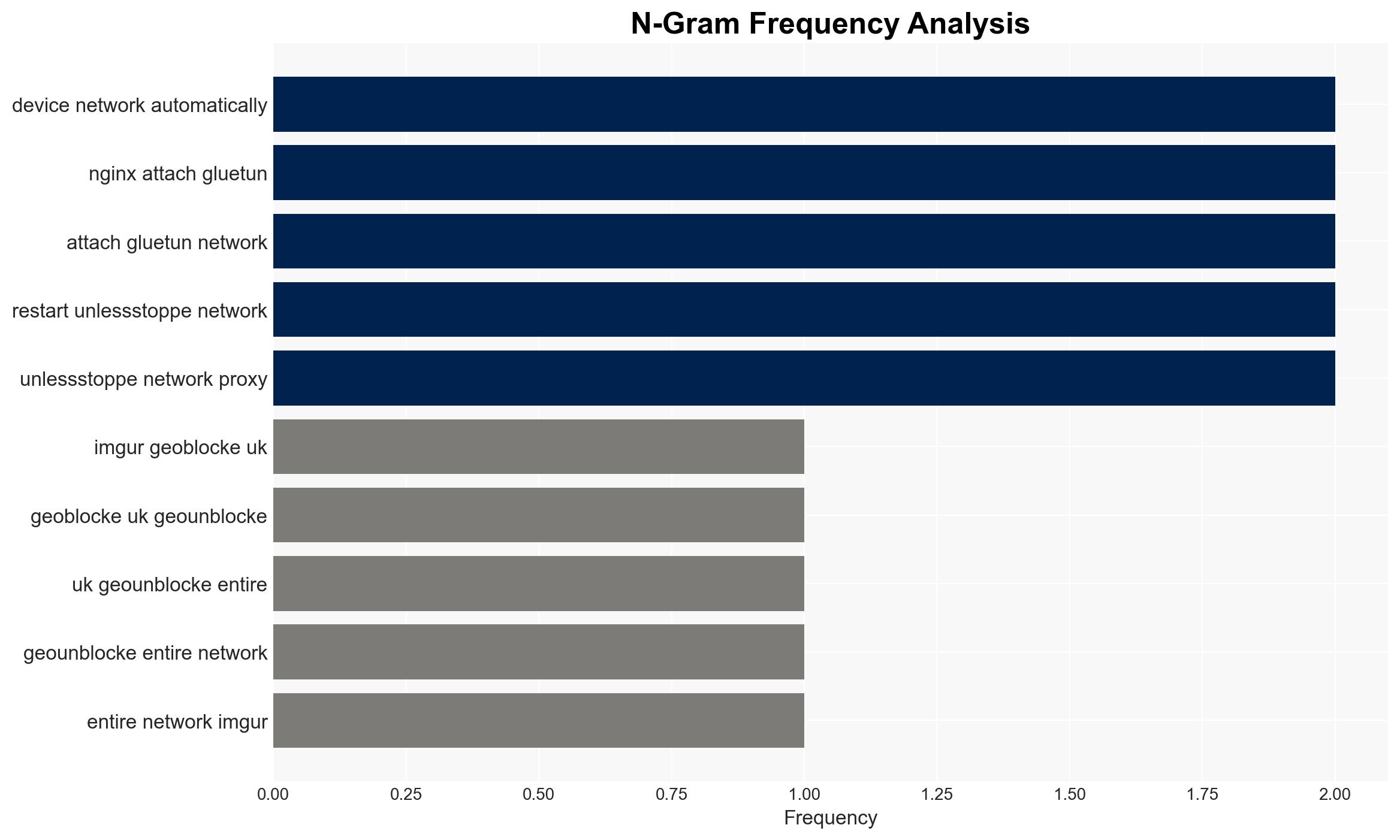
Imgur’s decision to geo-block users in the UK has led to innovative technical workarounds by affected users, potentially undermining the effectiveness of such restrictions. The use of VPNs and network-level configurations to bypass geo-blocking could have broader implications for digital policy enforcement and user privacy. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: Imgur’s geo-blocking is primarily a business decision aimed at compliance with regional regulations or cost management. This is supported by the lack of direct engagement with UK users and the broader trend of digital platforms adjusting services regionally. However, specific regulatory pressures are not detailed in the snippet.
- Hypothesis B: The geo-blocking is a strategic move to test user responses and adaptability to restrictions, potentially informing future policy or service adjustments. This is contradicted by the lack of explicit communication from Imgur regarding experimental objectives.
- Assessment: Hypothesis A is currently better supported due to the commonality of regional service adjustments in the tech industry, though further data on Imgur’s strategic objectives could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Users have the technical capability to implement network-level workarounds; Imgur’s decision is not explicitly tied to specific UK regulations; VPN use will remain a viable method for circumventing geo-blocks.
- Information Gaps: Specific reasons for Imgur’s geo-blocking decision; data on the prevalence of VPN use among UK users; potential legal or regulatory responses to such circumventions.
- Bias & Deception Risks: Potential bias in interpreting user motivations as purely technical rather than also privacy-driven; lack of direct statements from Imgur increases reliance on user-reported experiences.
4. Implications and Strategic Risks
The development of user-driven solutions to bypass geo-blocking could influence future digital policy enforcement and user privacy strategies. This may lead to increased scrutiny on VPN services and network-level configurations.
- Political / Geopolitical: Potential for increased regulatory scrutiny on digital platforms and VPN services within the UK.
- Security / Counter-Terrorism: Minimal direct impact, though increased VPN use could complicate monitoring efforts.
- Cyber / Information Space: Highlights the adaptability of users to circumvent digital restrictions, potentially informing future cyber policy and enforcement strategies.
- Economic / Social: Could affect user engagement with platforms like Imgur, influencing their business models and regional strategies.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor user adaptation strategies and VPN usage trends; engage with digital platforms to understand the rationale behind geo-blocking decisions.
- Medium-Term Posture (1–12 months): Develop partnerships with tech companies to explore balanced regulatory frameworks; enhance capabilities to track and analyze VPN traffic without infringing on privacy.
- Scenario Outlook:
- Best: Platforms and regulators collaborate to create user-friendly compliance solutions.
- Worst: Increased regulatory crackdowns on VPN services, leading to user privacy concerns.
- Most-Likely: Continued user adaptation to geo-blocking, prompting incremental policy adjustments.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
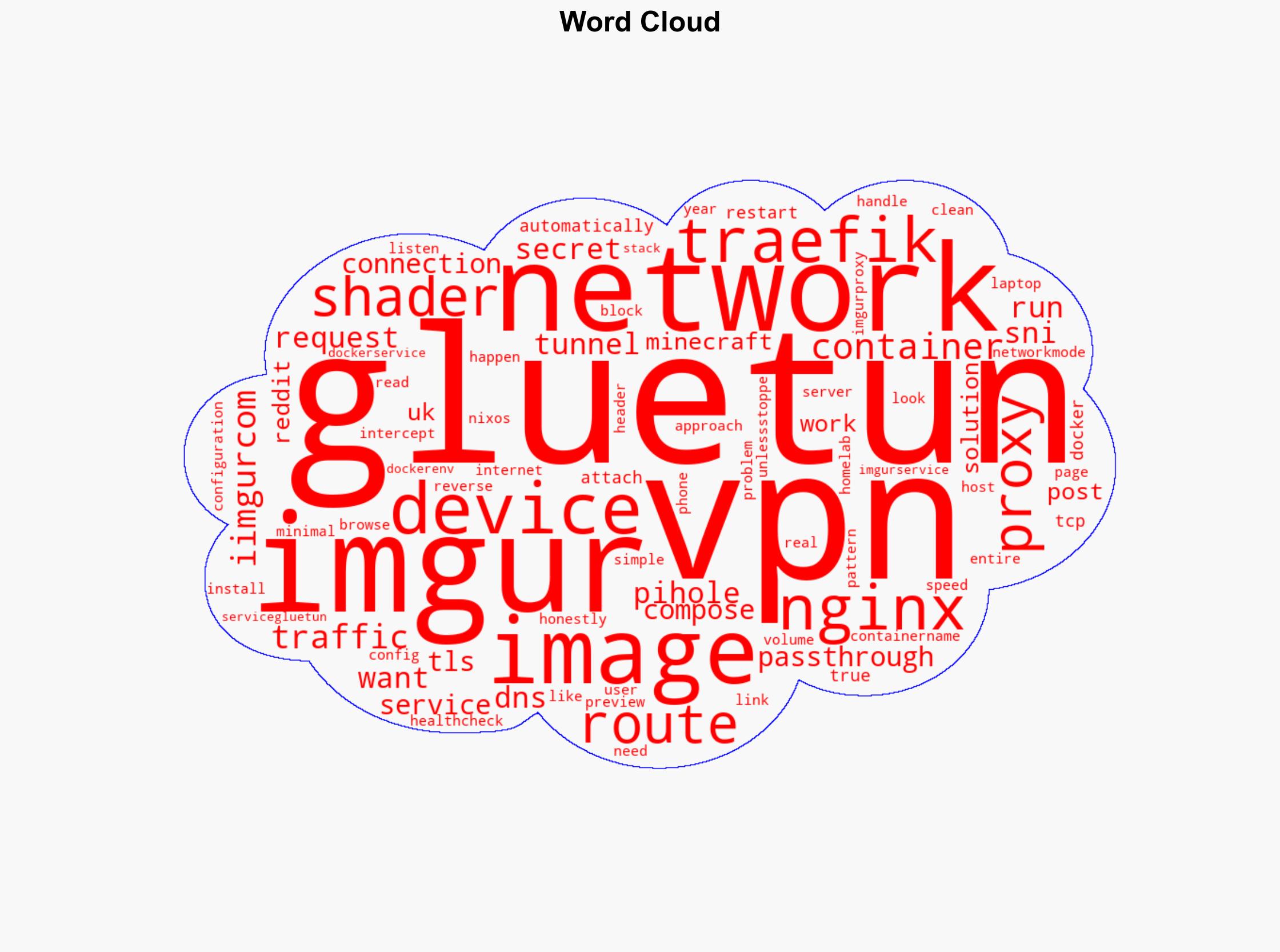
Cybersecurity, geo-blocking, VPN, digital policy, user privacy, regulatory compliance, network security, tech industry
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us