University of Mississippi Medical Center Remains Inaccessible Following Recent Ransomware Incident
Published on: 2026-02-23
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: University of Mississippi Medical Center Still Offline After Ransomware Attack
1. BLUF (Bottom Line Up Front)
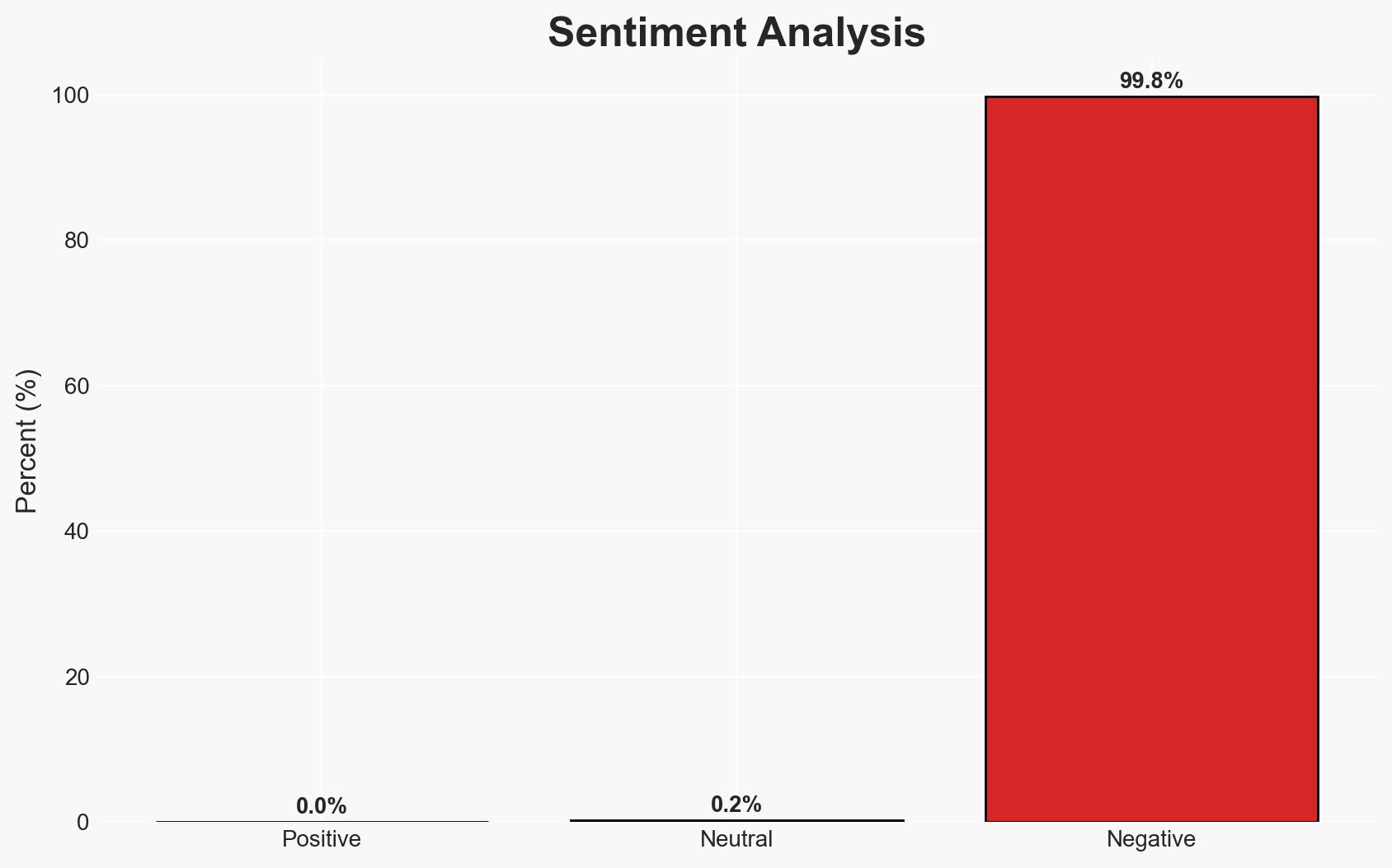
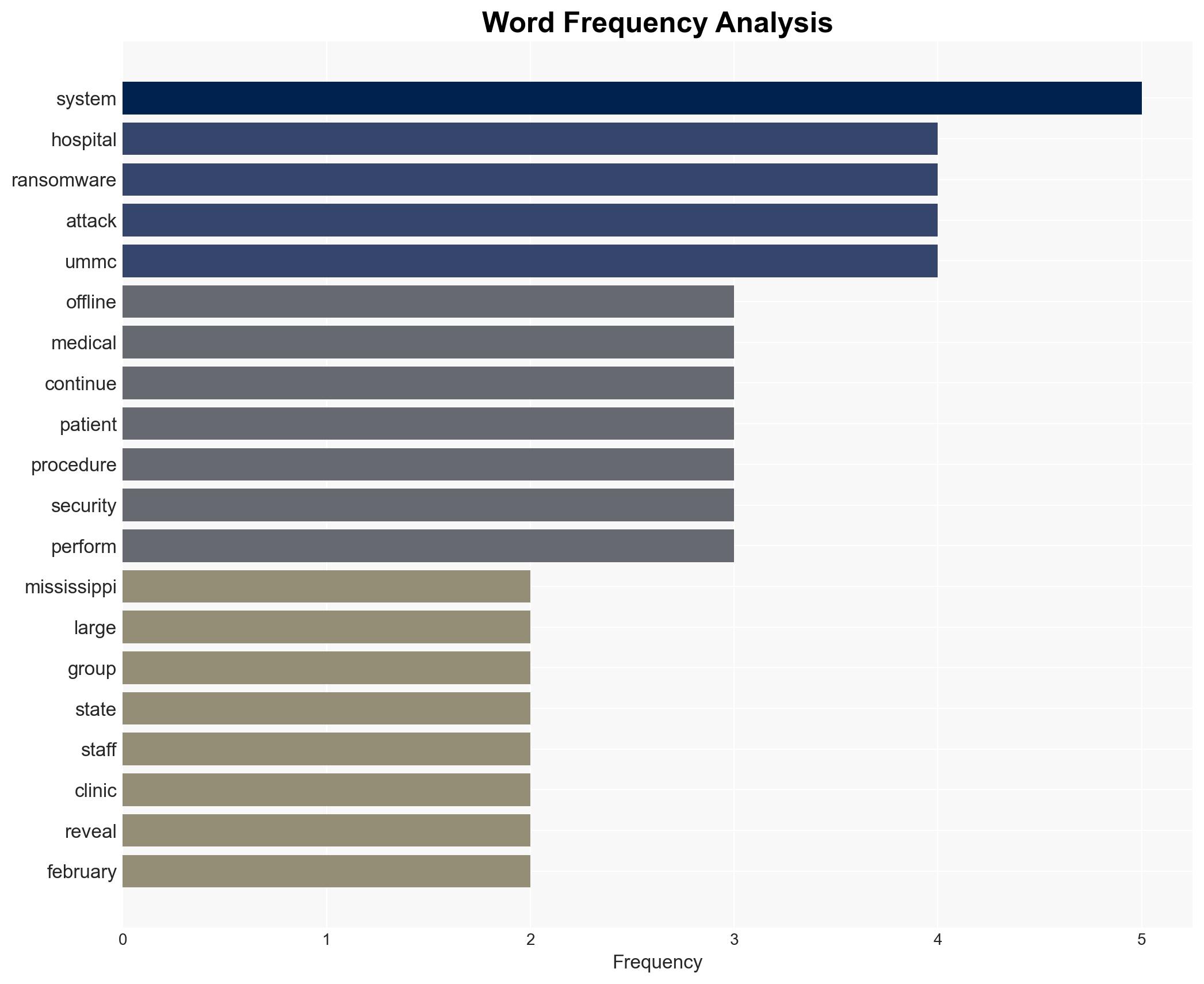
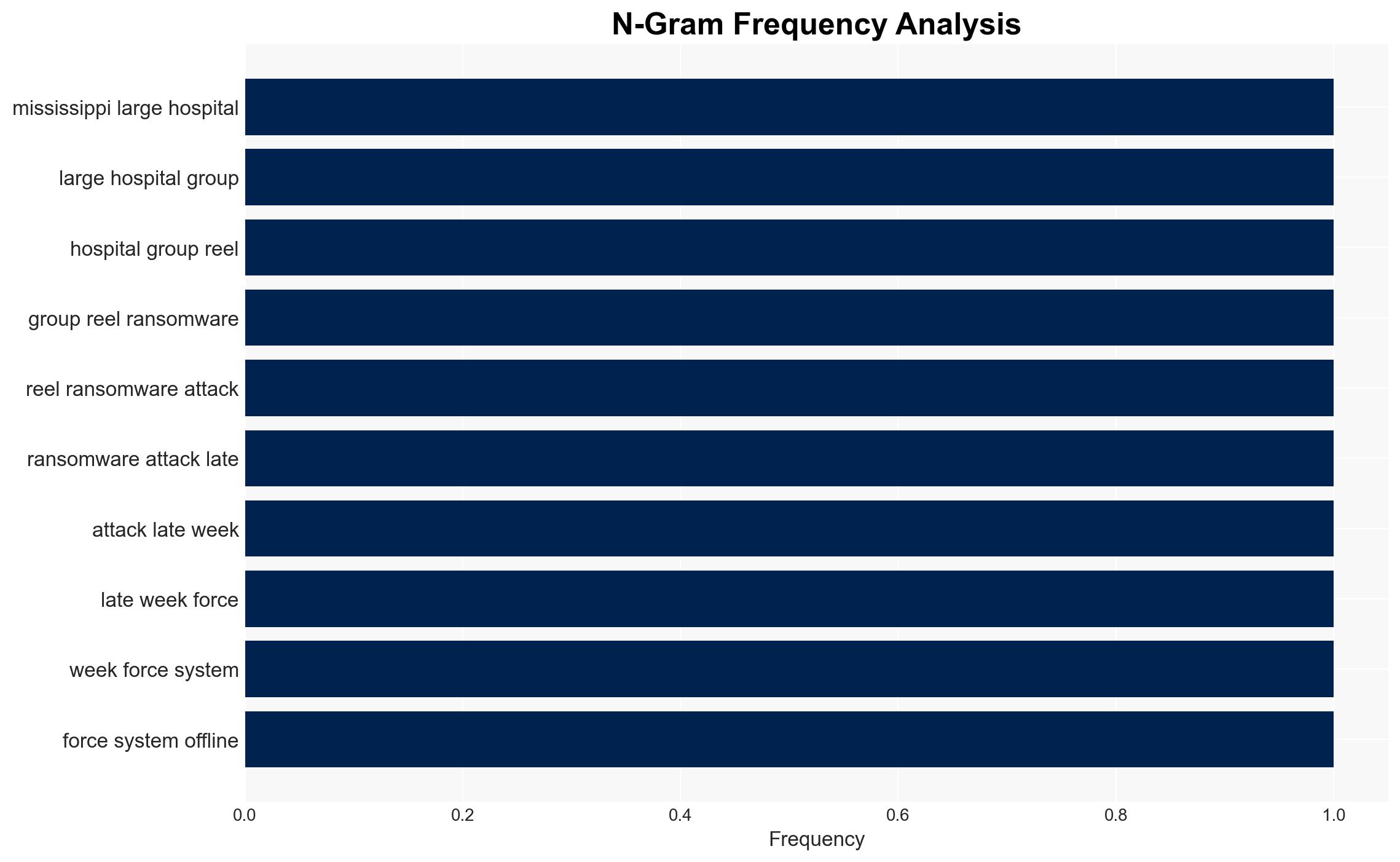
The University of Mississippi Medical Center (UMMC) remains offline following a significant ransomware attack, impacting healthcare services across multiple facilities. The attack has forced the use of manual procedures, affecting patient care and operational continuity. The involvement of DHS and the FBI suggests a serious cyber threat, with moderate confidence in the hypothesis that a financially motivated cybercriminal group is responsible.
2. Competing Hypotheses
- Hypothesis A: The ransomware attack on UMMC is conducted by a financially motivated cybercriminal group seeking ransom payments. This is supported by the typical modus operandi of ransomware attacks targeting large institutions for financial gain. However, the lack of confirmed ransom demands introduces uncertainty.
- Hypothesis B: The attack could be part of a broader campaign by a state-sponsored actor aiming to disrupt critical infrastructure. This is less supported due to the absence of geopolitical tensions directly involving UMMC, but cannot be entirely ruled out without further evidence.
- Assessment: Hypothesis A is currently better supported due to the typical financial motivations associated with ransomware attacks on healthcare institutions. Confirmation of ransom demands or communication from the attackers would strengthen this hypothesis.
3. Key Assumptions and Red Flags
- Assumptions: The attack is financially motivated; UMMC’s IT systems are vulnerable to ransomware; the attackers are external to UMMC.
- Information Gaps: Identity of the attackers, specific vulnerabilities exploited, and whether any data has been exfiltrated.
- Bias & Deception Risks: Potential bias in assuming financial motivation without direct evidence; risk of deception if attackers provide false claims about data theft.
4. Implications and Strategic Risks
The ransomware attack on UMMC could have cascading effects on healthcare delivery, patient safety, and public trust in healthcare institutions. It highlights vulnerabilities in critical infrastructure and the need for enhanced cybersecurity measures.
- Political / Geopolitical: Potential for increased regulatory scrutiny and policy discussions on healthcare cybersecurity.
- Security / Counter-Terrorism: Increased risk of similar attacks on other healthcare facilities, necessitating heightened security measures.
- Cyber / Information Space: Potential for increased cyber threat activity targeting healthcare, necessitating improved defenses and incident response capabilities.
- Economic / Social: Disruption of healthcare services could lead to economic losses and decreased public confidence in healthcare systems.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of UMMC’s network for further threats, engage with cybersecurity experts to restore systems, and communicate transparently with stakeholders.
- Medium-Term Posture (1–12 months): Develop and implement comprehensive cybersecurity strategies, including regular penetration testing and employee training on cyber hygiene.
- Scenario Outlook:
- Best: Systems restored with minimal data loss; improved cybersecurity measures prevent future incidents.
- Worst: Prolonged disruption and data breach lead to significant financial and reputational damage.
- Most-Likely: Gradual restoration of services with increased cybersecurity awareness and resilience.
6. Key Individuals and Entities
- University of Mississippi Medical Center (UMMC)
- Department of Homeland Security (DHS)
- Federal Bureau of Investigation (FBI)
- Steven Swift, MD at Suzu Labs
- Michael Centrella, Head of Public Policy at SecurityScorecard
7. Thematic Tags
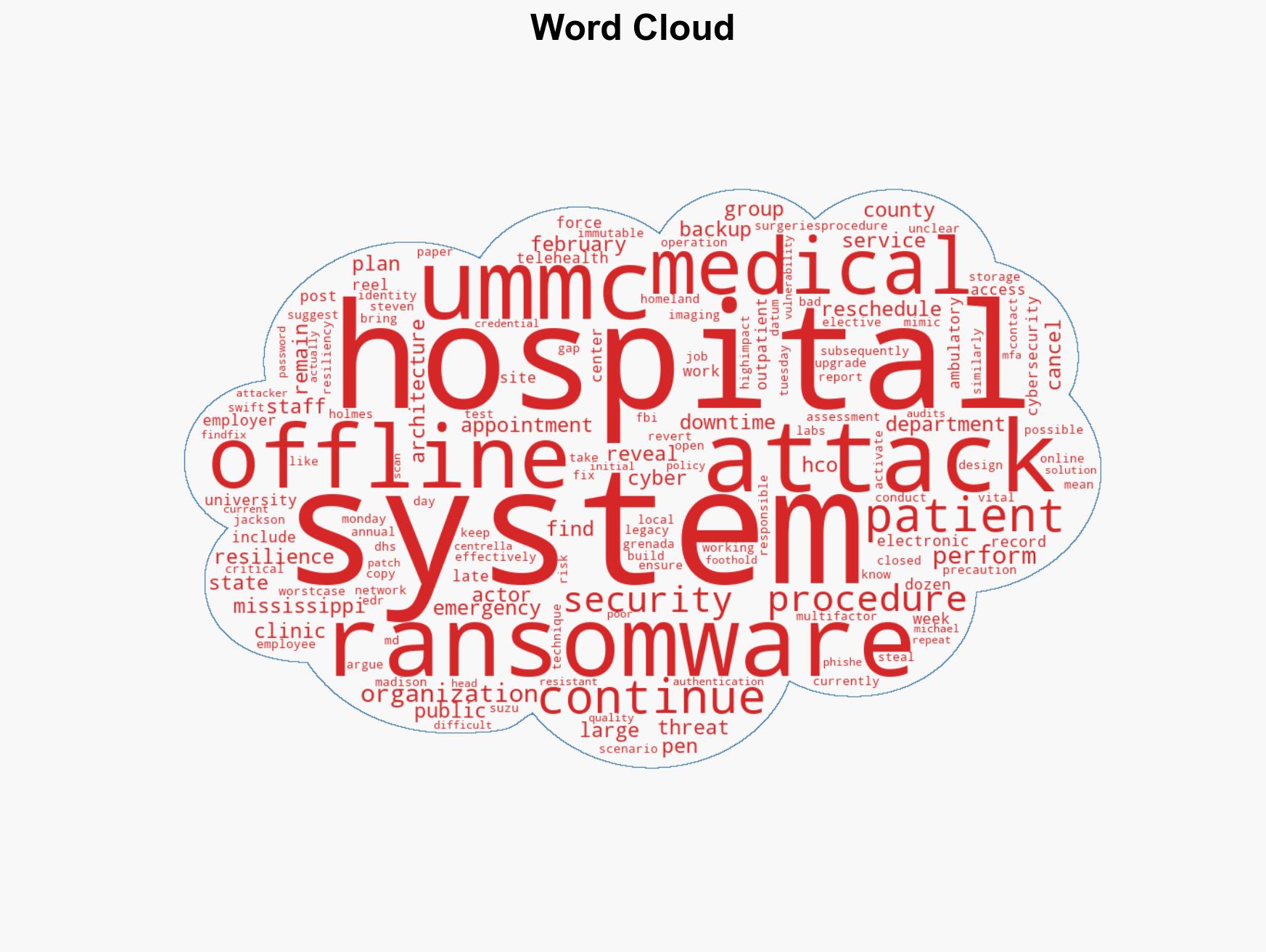
cybersecurity, ransomware, healthcare cybersecurity, critical infrastructure, cyber resilience, public trust, operational continuity
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us