University of Mississippi Medical Center resumes operations after nine-day ransomware disruption
Published on: 2026-03-04
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Mississippi medical center reopens clinics hit by ransomware attack
1. BLUF (Bottom Line Up Front)
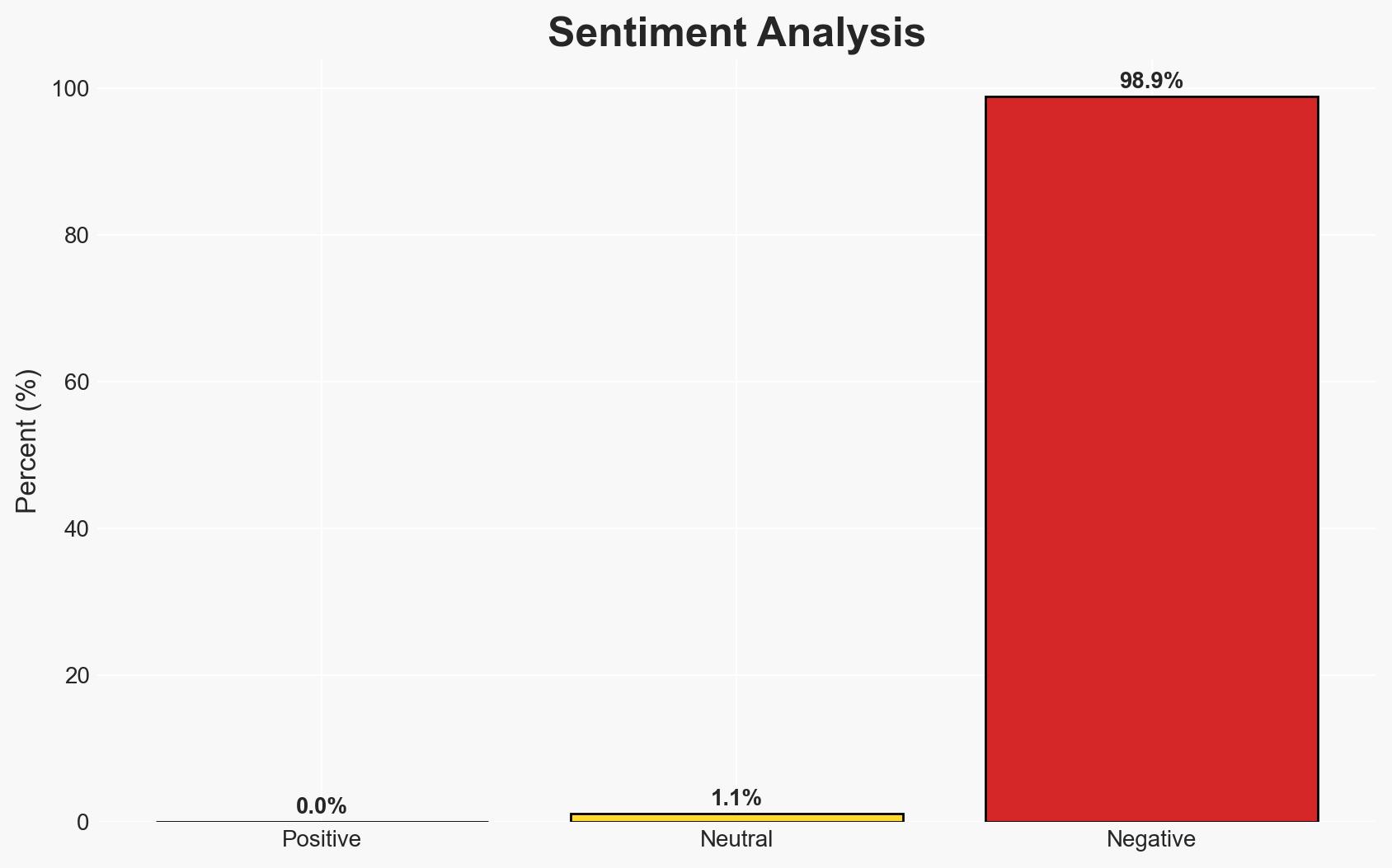
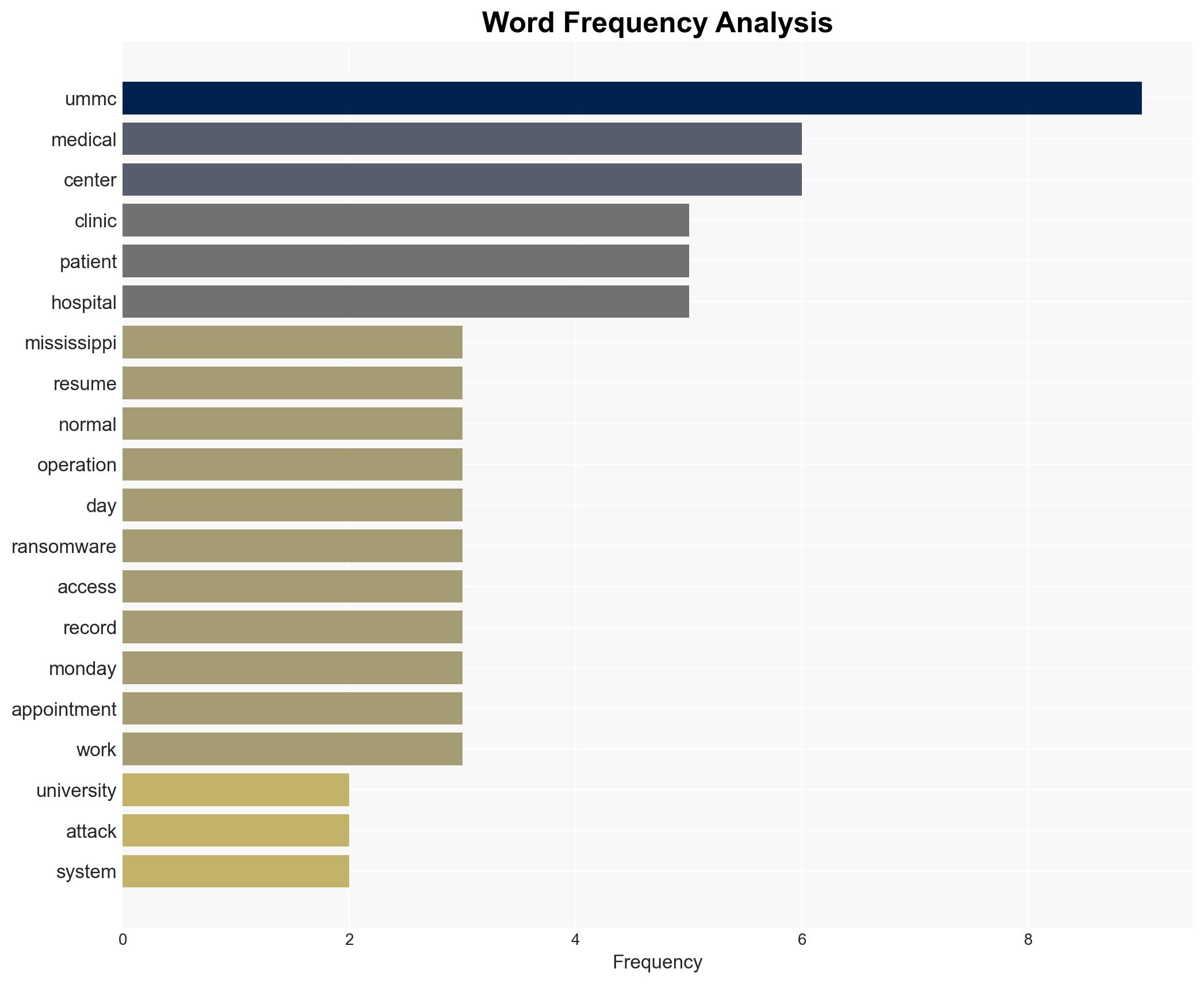
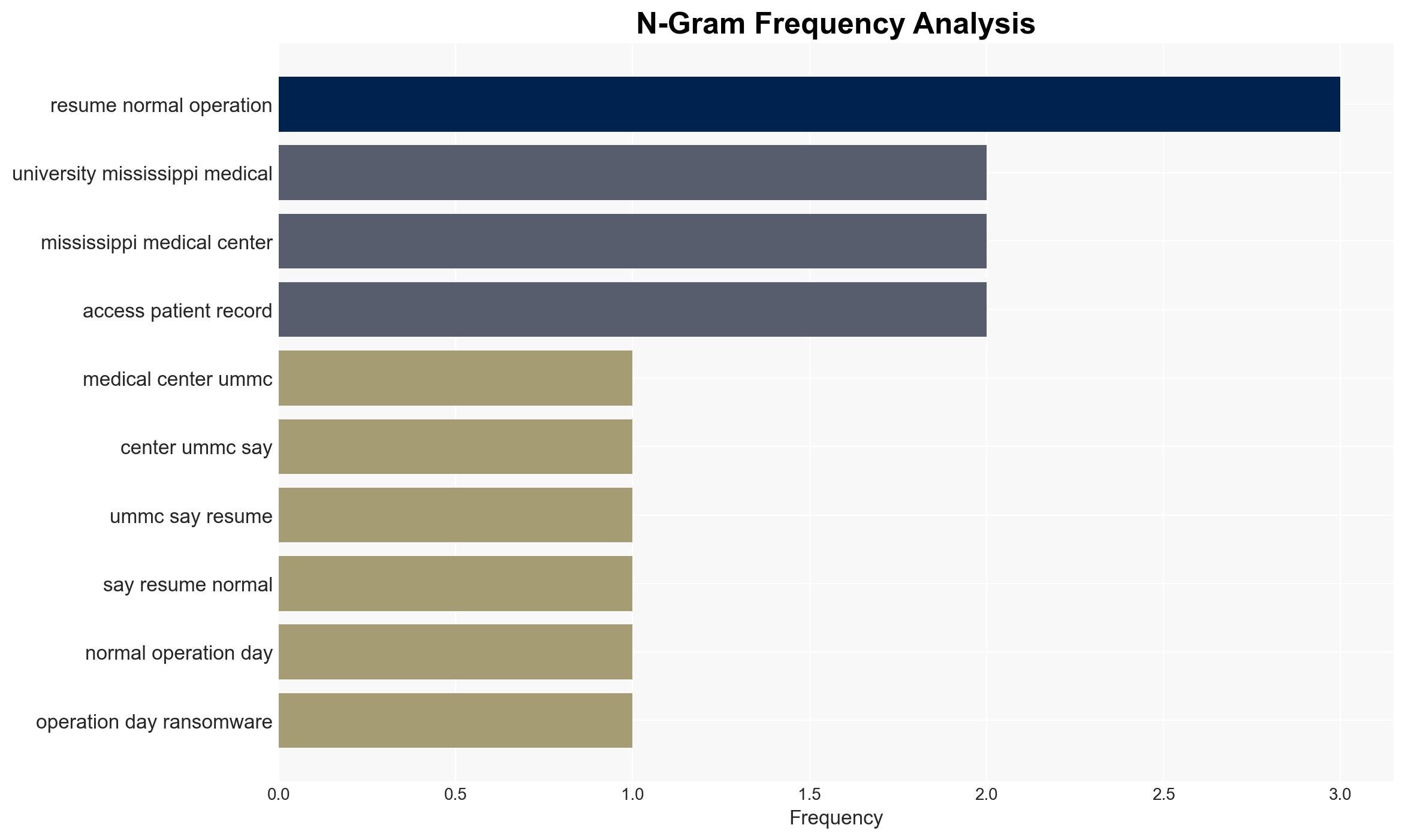
The University of Mississippi Medical Center (UMMC) has resumed normal operations following a ransomware attack that disrupted services for nine days. The attack significantly impacted patient care, but UMMC has restored access to electronic medical records and resumed clinic operations. The incident underscores vulnerabilities in healthcare IT systems. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The ransomware attack was opportunistic, targeting UMMC due to its large size and critical role in Mississippi’s healthcare system. Supporting evidence includes the lack of a claimed responsibility, suggesting the attackers are still negotiating. Key uncertainties include the attackers’ identity and specific motivations.
- Hypothesis B: The attack was a targeted operation by a sophisticated group aiming to exploit healthcare vulnerabilities for financial gain. The attackers’ communication with UMMC and the involvement of federal agencies support this. However, the absence of a public ransom demand contradicts this hypothesis.
- Assessment: Hypothesis A is currently better supported due to the lack of specific targeting indicators and the opportunistic nature of many ransomware attacks. Key indicators that could shift this judgment include the emergence of a ransom demand or attribution to a known threat actor.
3. Key Assumptions and Red Flags
- Assumptions: UMMC’s IT systems were not adequately protected against ransomware; the attack was financially motivated; the attackers are not state-sponsored.
- Information Gaps: Identity of the attackers, specific vulnerabilities exploited, and whether a ransom was paid.
- Bias & Deception Risks: Potential bias in UMMC’s public statements to minimize reputational damage; possible deception by attackers regarding their intentions.
4. Implications and Strategic Risks
This incident highlights the persistent threat of ransomware to critical infrastructure, particularly in the healthcare sector. The situation could evolve with further attacks or increased regulatory scrutiny.
- Political / Geopolitical: Potential for increased government intervention in cybersecurity standards for healthcare.
- Security / Counter-Terrorism: Heightened awareness and preparedness against cyber threats in critical sectors.
- Cyber / Information Space: Increased focus on healthcare cybersecurity vulnerabilities; potential for copycat attacks.
- Economic / Social: Disruption to healthcare services could affect public trust and economic stability in the region.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a thorough forensic investigation, enhance cybersecurity measures, and engage with federal agencies for support.
- Medium-Term Posture (1–12 months): Develop resilience measures, invest in cybersecurity training, and establish partnerships with cybersecurity firms.
- Scenario Outlook:
- Best: No further incidents; improved cybersecurity posture.
- Worst: Recurrence of attacks; significant operational disruptions.
- Most-Likely: Incremental improvements in cybersecurity; occasional minor disruptions.
6. Key Individuals and Entities
- LouAnn Woodward, Dean of the School of Medicine at UMMC
- University of Mississippi Medical Center (UMMC)
- FBI
- U.S. Cybersecurity and Infrastructure Security Agency (CISA)
7. Thematic Tags
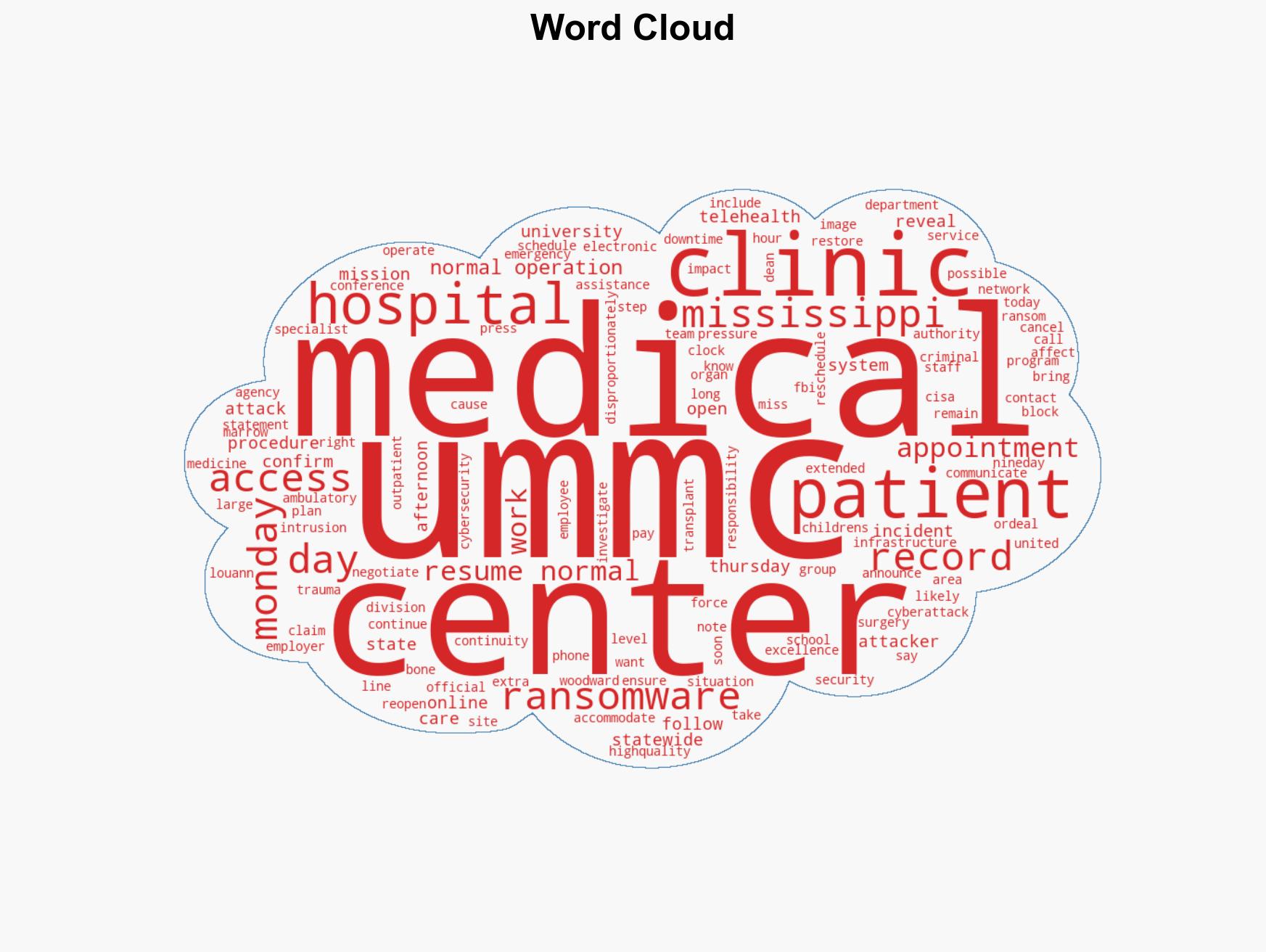
cybersecurity, ransomware, healthcare cybersecurity, critical infrastructure, cyber resilience, federal investigation, patient care disruption
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us