US CISA adds Apache Tomcat flaw to its Known Exploited Vulnerabilities catalog – Securityaffairs.com
Published on: 2025-04-02
Intelligence Report: US CISA adds Apache Tomcat flaw to its Known Exploited Vulnerabilities catalog – Securityaffairs.com
1. BLUF (Bottom Line Up Front)
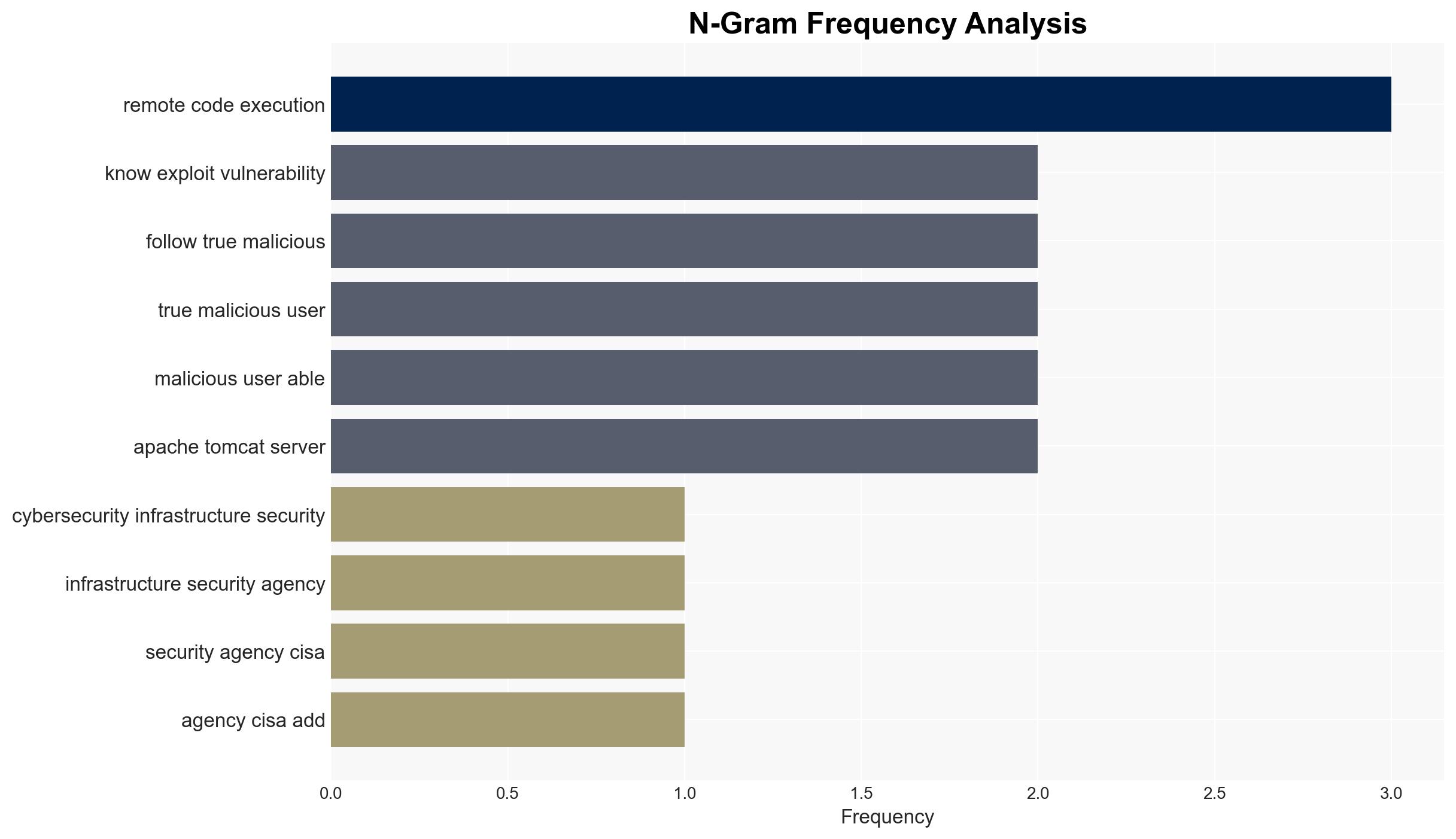
The US Cybersecurity and Infrastructure Security Agency (CISA) has added a critical Apache Tomcat vulnerability, tracked as CVE, to its Known Exploited Vulnerabilities catalog. This vulnerability allows remote code execution under specific conditions and has been actively exploited shortly after a proof-of-concept was released. Immediate mitigation actions are recommended to prevent potential breaches.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
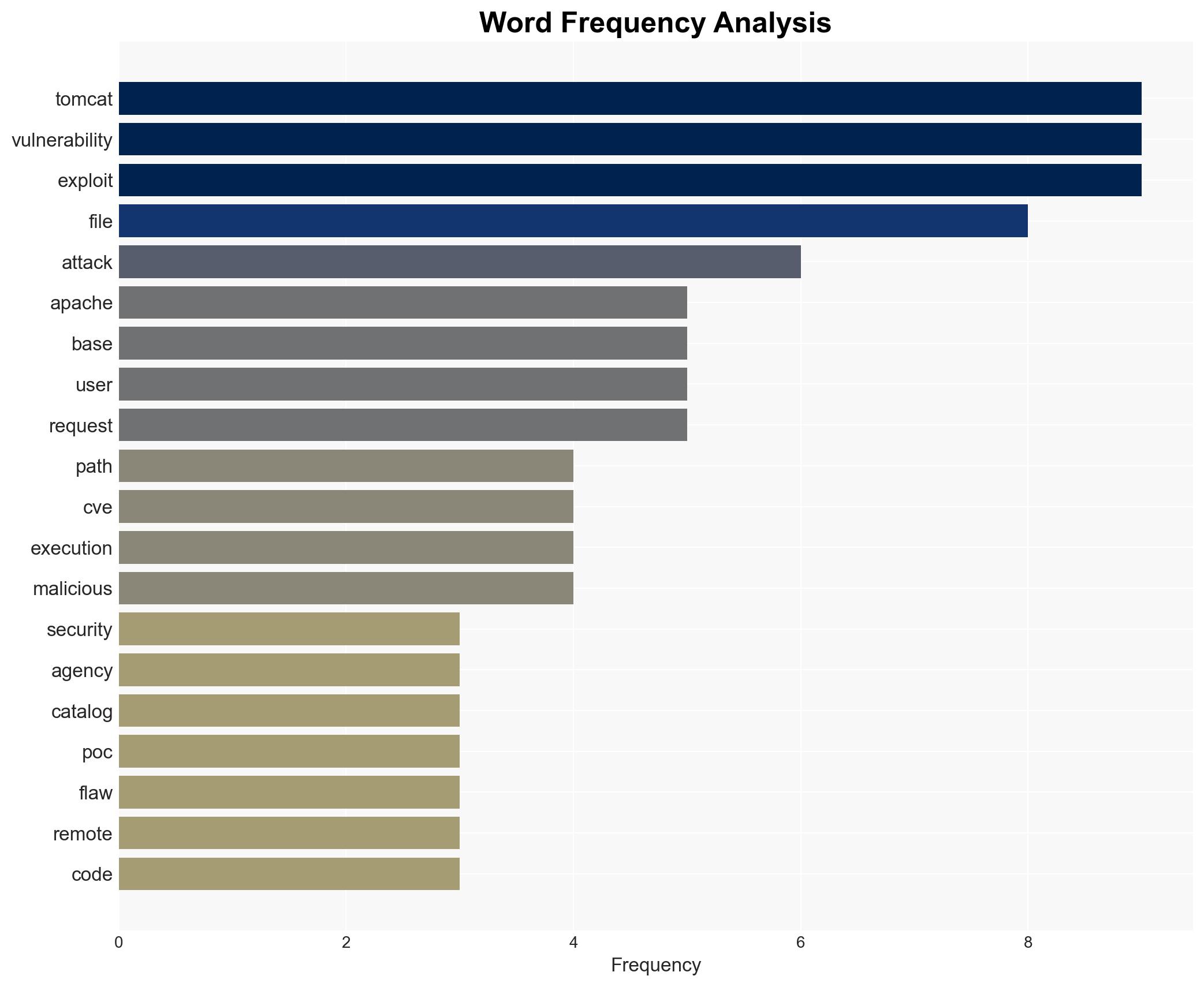
The Apache Tomcat vulnerability, identified as a path equivalence flaw, enables remote code execution when certain conditions are met. It affects multiple versions of Apache Tomcat and requires write-enabled default servlet and partial support for specific file handling. The vulnerability was actively exploited soon after a proof-of-concept was published online by a user known as isee. The attack involves uploading a malicious Java session file to trigger deserialization, bypassing traditional security filters due to base encoding, making detection challenging.
3. Implications and Strategic Risks
The exploitation of this vulnerability poses significant risks to national security and economic interests. The ability to execute remote code on affected servers can lead to unauthorized access to sensitive information, disruption of services, and potential control over critical infrastructure. The rapid exploitation following the proof-of-concept release highlights the need for timely vulnerability management and patching.
4. Recommendations and Outlook
Recommendations:
- Organizations should immediately update affected Apache Tomcat versions to mitigate the vulnerability.
- Implement enhanced monitoring and detection mechanisms to identify and respond to exploitation attempts.
- Review and strengthen web application firewall (WAF) configurations to better detect encoded attack patterns.
- Encourage private organizations to align with CISA’s directives to reduce exposure to known vulnerabilities.
Outlook:
In the best-case scenario, rapid patching and improved detection measures will minimize the impact of this vulnerability. In the worst-case scenario, continued exploitation could lead to widespread breaches and significant operational disruptions. The most likely outcome involves a moderate level of exploitation with increased awareness and mitigation efforts reducing the overall risk.
5. Key Individuals and Entities
The report mentions the following significant individuals and entities:
- isee – User who published the proof-of-concept online.
- Wallarm researchers – Confirmed active exploitation and provided advisory details.
- CISA – Added the vulnerability to its Known Exploited Vulnerabilities catalog.