US CISA adds Cisco Smart Licensing Utility flaw to its Known Exploited Vulnerabilities catalog – Securityaffairs.com
Published on: 2025-03-31
Intelligence Report: US CISA adds Cisco Smart Licensing Utility flaw to its Known Exploited Vulnerabilities catalog – Securityaffairs.com
1. BLUF (Bottom Line Up Front)
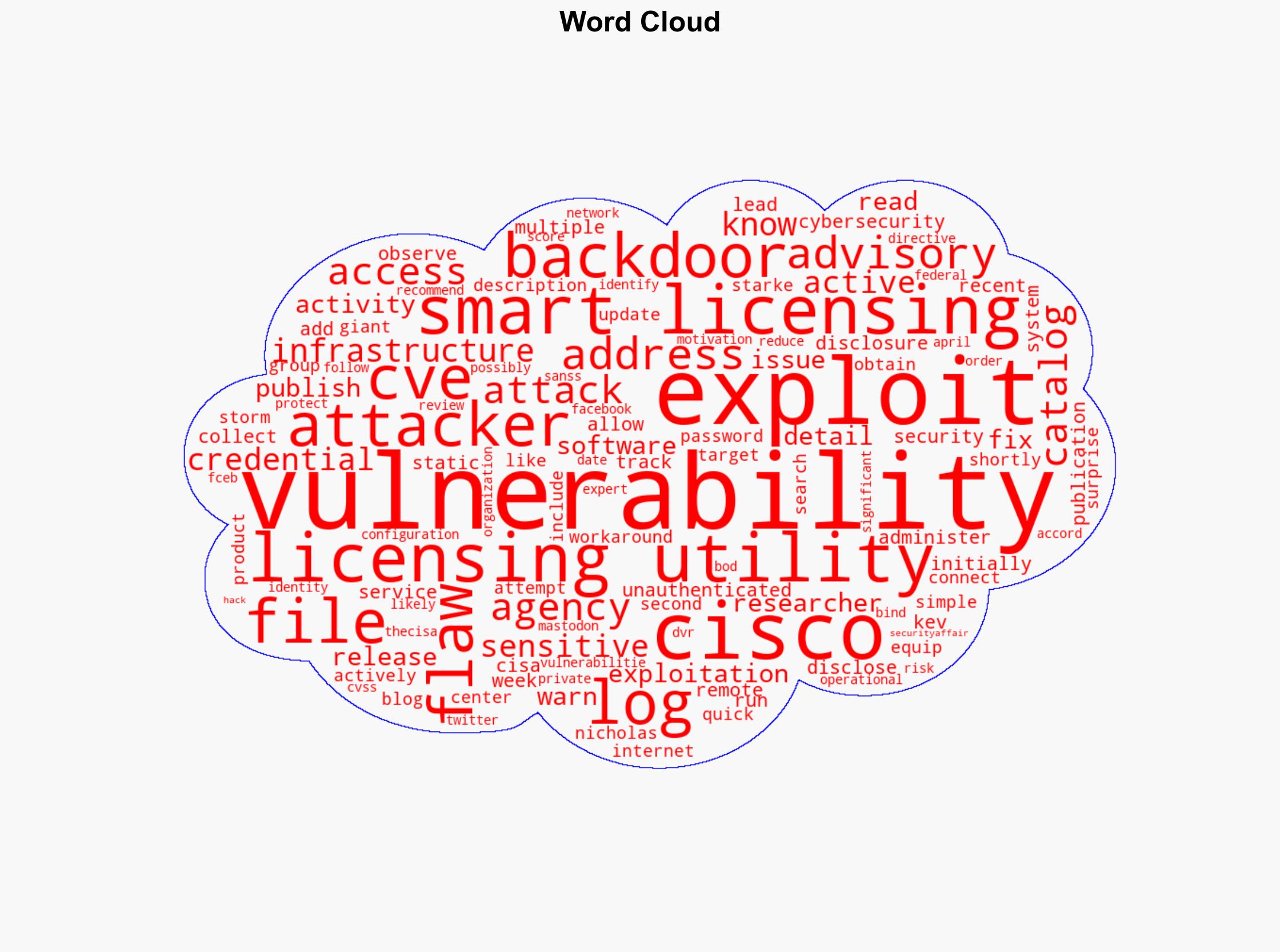
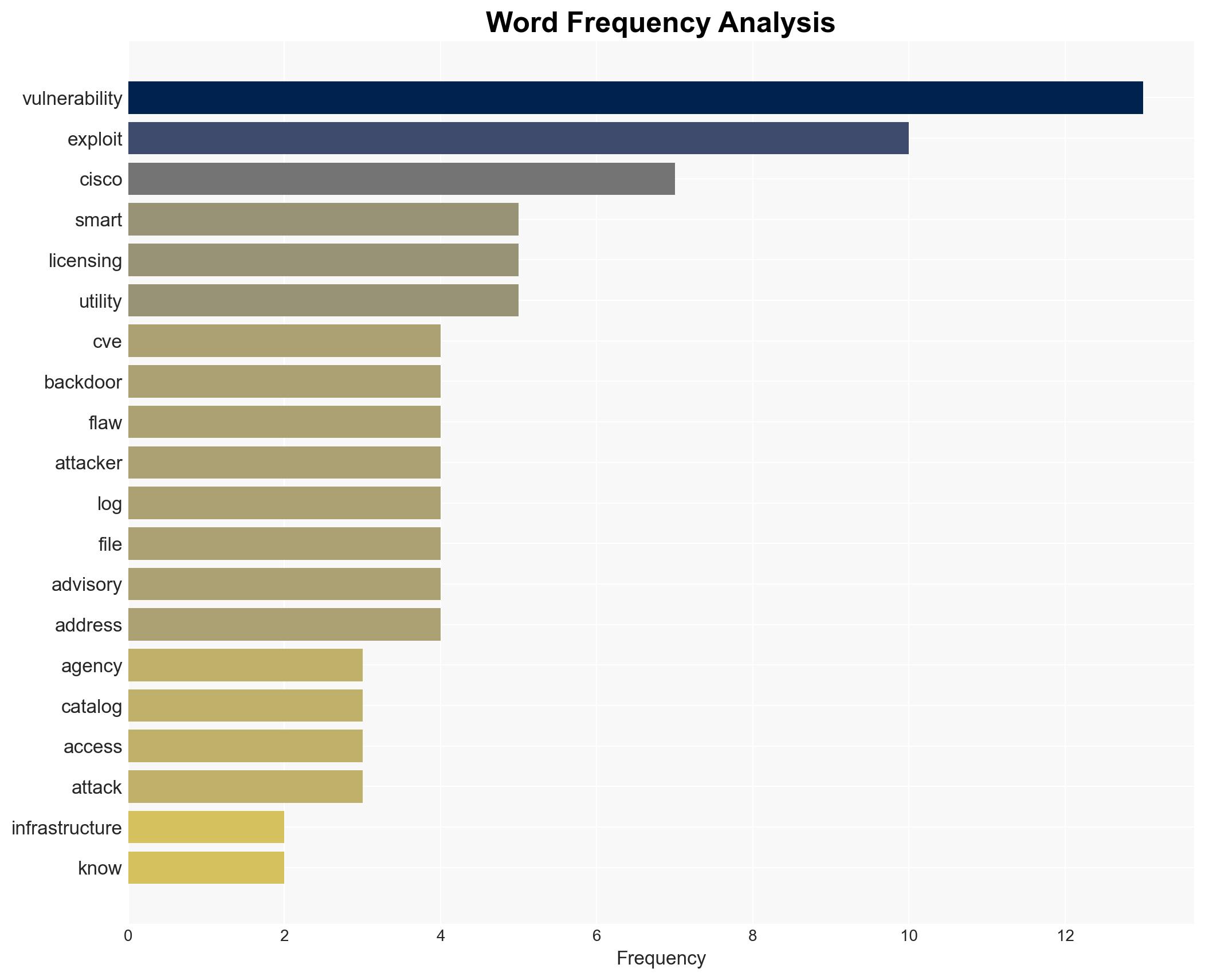
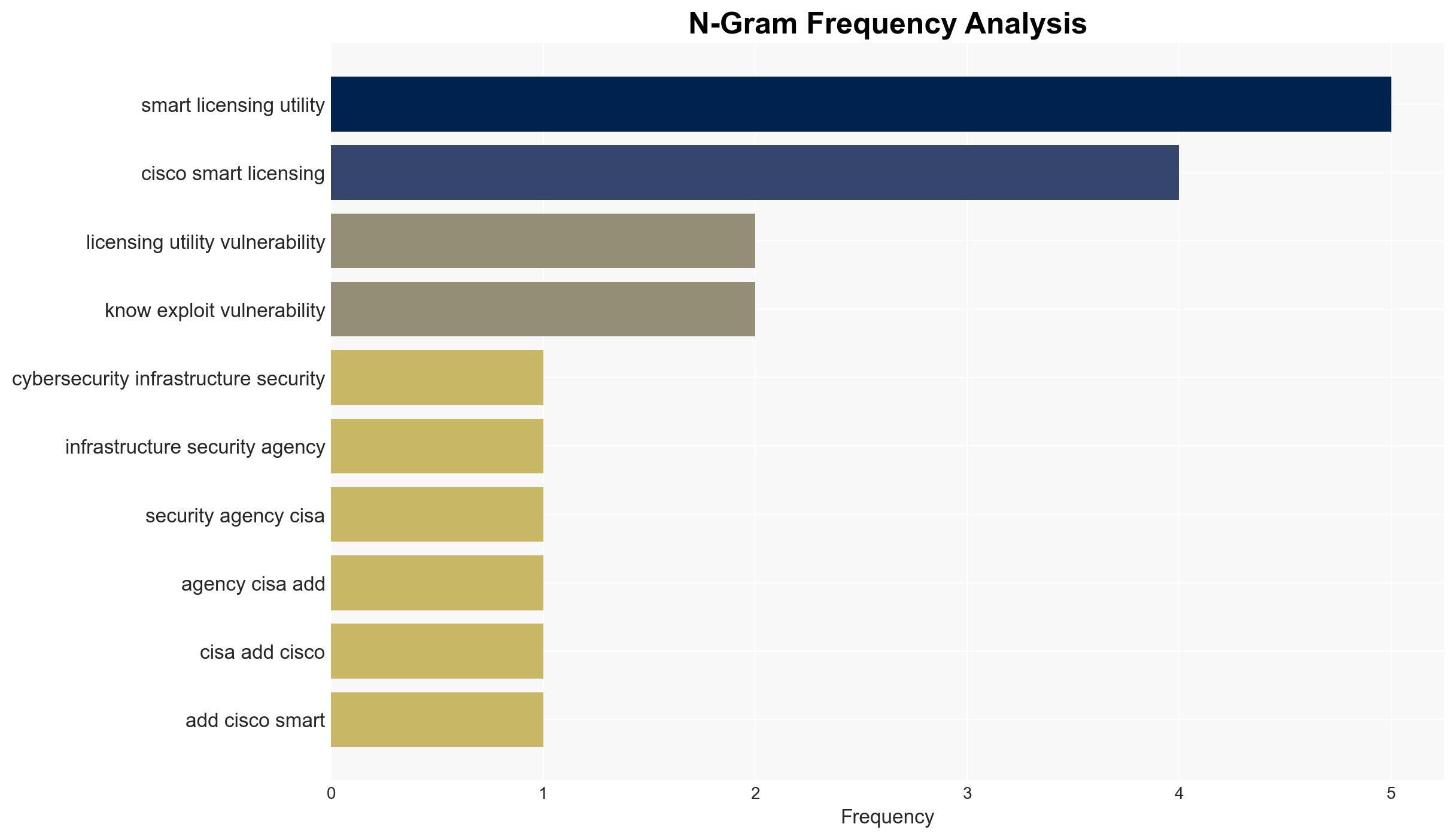
The US Cybersecurity and Infrastructure Security Agency (CISA) has identified a critical vulnerability in Cisco’s Smart Licensing Utility, tracked as CVE, and added it to its Known Exploited Vulnerabilities (KEV) catalog. This vulnerability, involving a static credential backdoor, allows unauthorized remote access to sensitive log files. Active exploitation has been observed, prompting immediate action to mitigate risks. Stakeholders are advised to implement the latest software updates and follow CISA’s directives to protect their networks.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
The vulnerability in Cisco’s Smart Licensing Utility is significant due to its potential to allow unauthorized access to sensitive information. The flaw was disclosed by Cisco, and active exploitation has been reported. The vulnerability can be exploited by remote attackers to collect sensitive data and administer the affected systems. The advisory from Cisco and subsequent warnings from researchers highlight the urgency of addressing this flaw. The exploitation of this vulnerability is likely to increase, given its inclusion in the KEV catalog and the publication of exploit details.
3. Implications and Strategic Risks
The exploitation of this vulnerability poses several risks, including:
- National Security: Potential unauthorized access to critical infrastructure systems.
- Regional Stability: Increased cyber threats could destabilize regional networks and operations.
- Economic Interests: Organizations may face financial losses due to data breaches and system downtimes.
The vulnerability’s exploitation could lead to significant disruptions if not addressed promptly, affecting both public and private sector entities.
4. Recommendations and Outlook
Recommendations:
- Implement the latest software updates provided by Cisco to address the vulnerability.
- Conduct a thorough review of network configurations and access controls to prevent unauthorized access.
- Enhance monitoring and incident response capabilities to detect and mitigate exploitation attempts.
Outlook:
Best-case scenario: Rapid implementation of patches and security measures mitigates the vulnerability, preventing further exploitation.
Worst-case scenario: Delayed response leads to widespread exploitation, resulting in significant data breaches and operational disruptions.
Most likely scenario: A mixed response with varying levels of mitigation success, leading to some exploitation but overall containment of major incidents.
5. Key Individuals and Entities
The report mentions Nicholas Starke as a researcher who published a blog post about the vulnerability. The Internet Storm Center is also noted for warning about active exploitation attempts. These entities play a crucial role in disseminating information and raising awareness about the vulnerability.