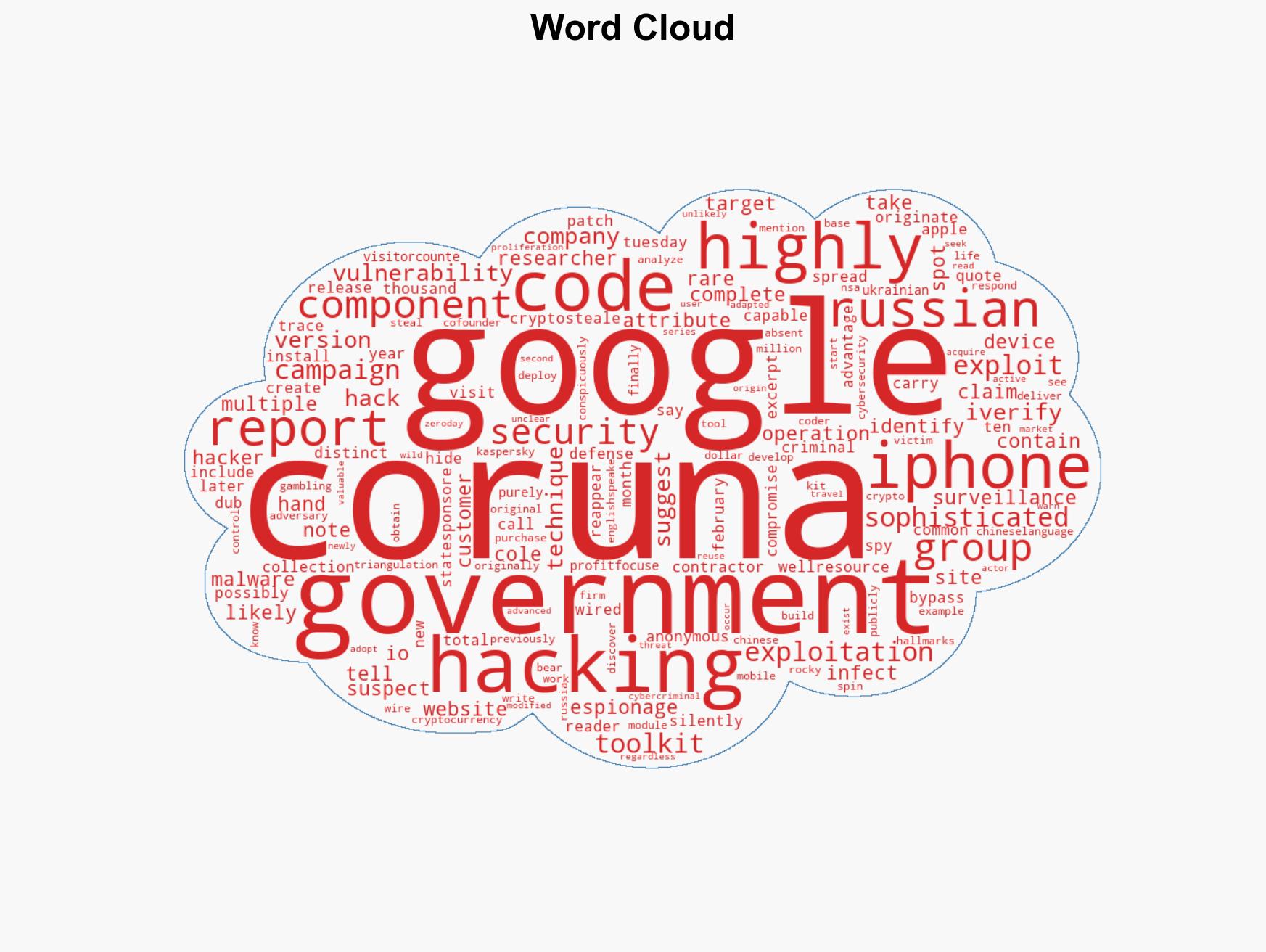
US-Originated iPhone Hacking Toolkit “Coruna” Now in Possession of Foreign Spies and Cybercriminals
Published on: 2026-03-04
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: A Possible US Government iPhone-Hacking Toolkit Is Now In the Hands of Foreign Spies Criminals
1. BLUF (Bottom Line Up Front)
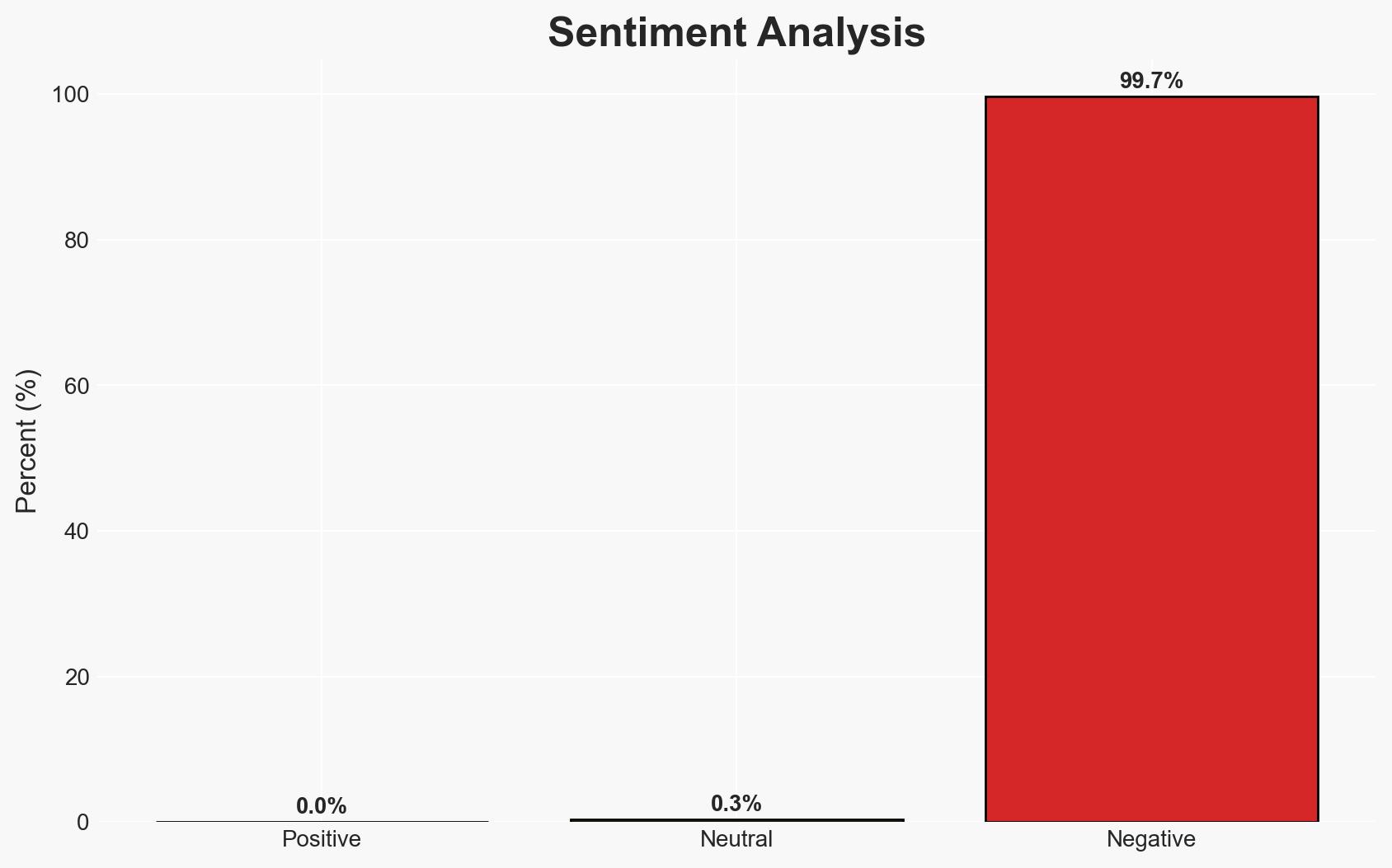
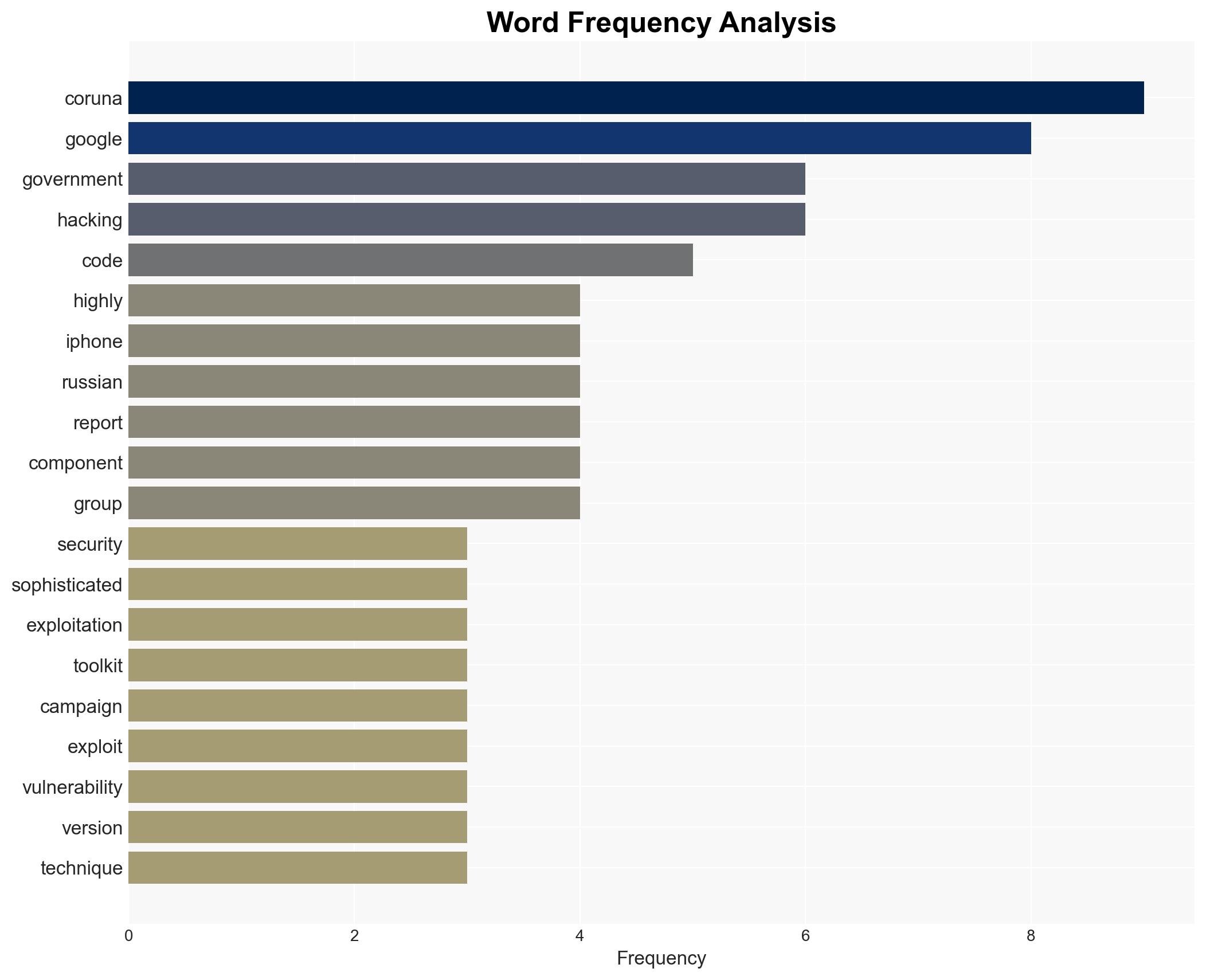
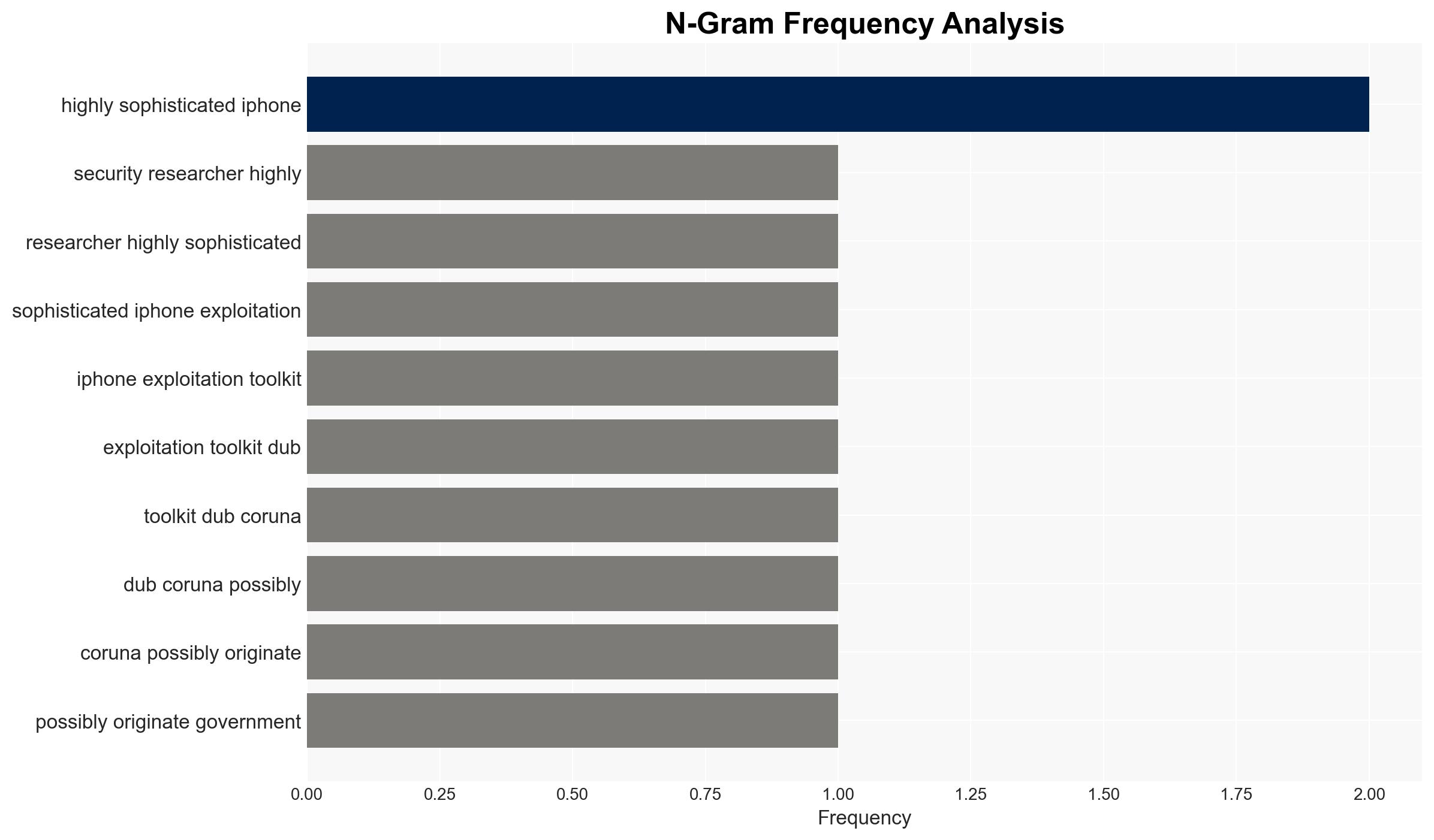
The iPhone exploitation toolkit “Coruna,” potentially originating from a U.S. government contractor, has been used by both state-sponsored and criminal entities, including suspected Russian espionage and crypto-stealing campaigns. This development poses significant cybersecurity threats, with moderate confidence in the assessment that the toolkit’s proliferation could lead to increased cyber operations against U.S. interests and allies.
2. Competing Hypotheses
- Hypothesis A: Coruna was developed by or for the U.S. government and has been leaked or sold, leading to its use by foreign adversaries and criminal groups. Supporting evidence includes the sophistication of the toolkit and its components’ similarities to known U.S. government tools. Key uncertainties involve the original intent and control mechanisms for the toolkit.
- Hypothesis B: Coruna was developed independently by a non-state actor or foreign government and falsely attributed to the U.S. to mislead and create geopolitical tension. Supporting evidence includes the lack of direct attribution to the U.S. government and the toolkit’s use in operations against U.S. interests. Contradicting evidence includes the toolkit’s English-language coding and high development cost.
- Assessment: Hypothesis A is currently better supported due to the toolkit’s sophistication and coding characteristics, which align with known U.S. government cyber capabilities. Indicators that could shift this judgment include credible attribution to a non-U.S. entity or evidence of deliberate misinformation campaigns.
3. Key Assumptions and Red Flags
- Assumptions: The toolkit’s sophistication implies state-level resources; the U.S. government has not publicly acknowledged involvement; the toolkit’s proliferation was unintended.
- Information Gaps: The identity of the original “customer” and the exact circumstances of the toolkit’s proliferation are unknown.
- Bias & Deception Risks: Potential confirmation bias in attributing the toolkit to the U.S. based on coding language; risk of deception by adversaries to implicate the U.S. government.
4. Implications and Strategic Risks
The spread of Coruna could lead to increased cyber threats against U.S. and allied interests, potentially escalating geopolitical tensions and undermining trust in U.S. cybersecurity capabilities.
- Political / Geopolitical: Possible diplomatic fallout if the toolkit is confirmed to originate from the U.S., impacting international relations.
- Security / Counter-Terrorism: Enhanced capabilities for adversaries to conduct espionage and cyber-attacks, increasing the threat landscape.
- Cyber / Information Space: Potential for widespread exploitation of iOS vulnerabilities, undermining public trust in digital security.
- Economic / Social: Economic impacts from cyber theft and potential disruptions to critical infrastructure.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase monitoring of cyber activities linked to Coruna, engage with allies to share threat intelligence, and enhance public-private partnerships for cybersecurity resilience.
- Medium-Term Posture (1–12 months): Develop capabilities to detect and neutralize similar tools, strengthen international cyber norms, and invest in cybersecurity education and infrastructure.
- Scenario Outlook:
- Best: Effective containment and neutralization of Coruna, leading to improved cybersecurity collaboration.
- Worst: Escalation of cyber-attacks using Coruna, resulting in significant geopolitical tensions and economic damage.
- Most-Likely: Continued sporadic use of Coruna by various actors, with moderate impact on security and economic sectors.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, espionage, cybercrime, U.S. government, iOS vulnerabilities, geopolitical tensions, cyber operations
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us