US Treasury designates Russian broker for acquiring stolen zero-day exploits from former US defense contracto…
Published on: 2026-02-25
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
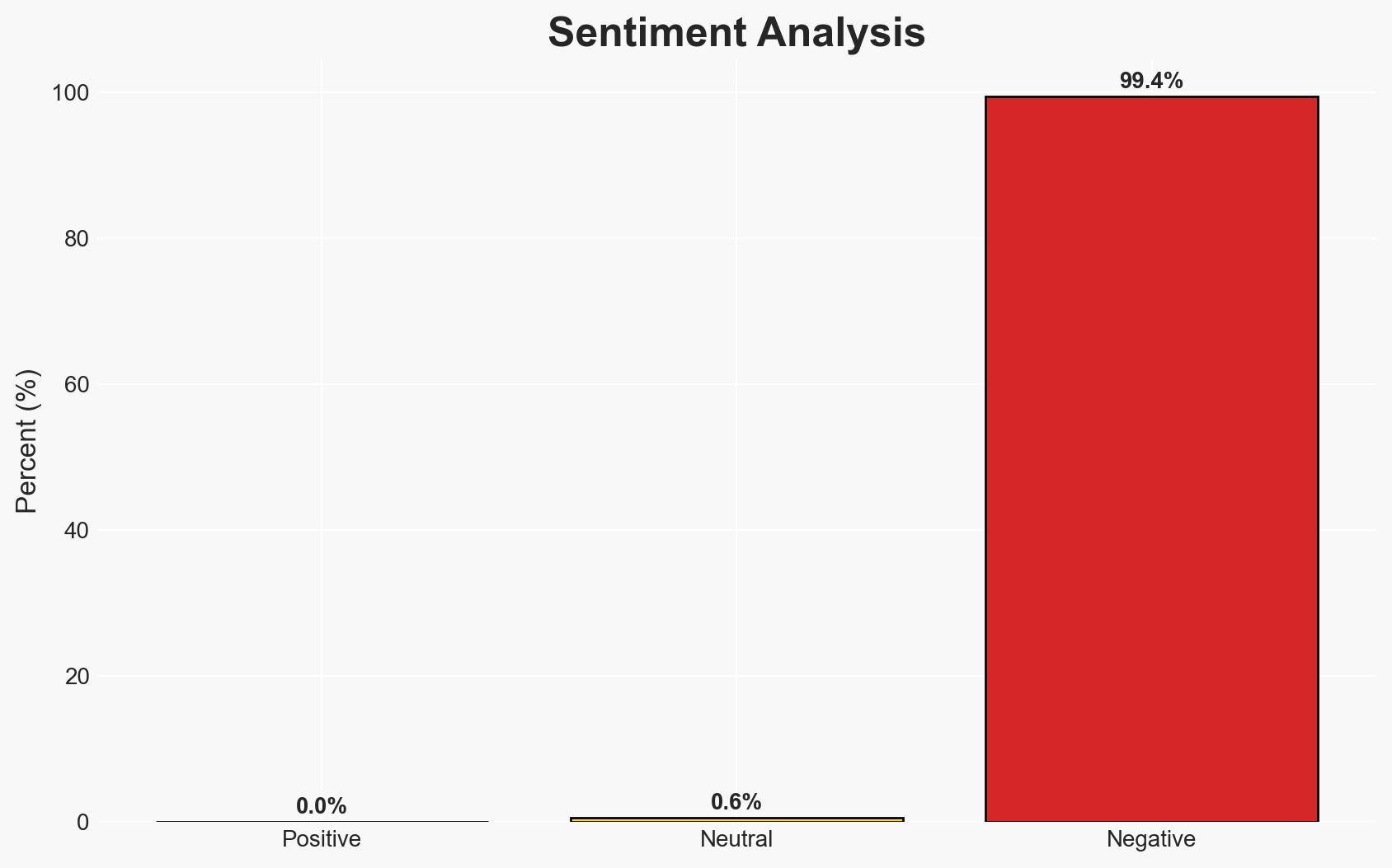
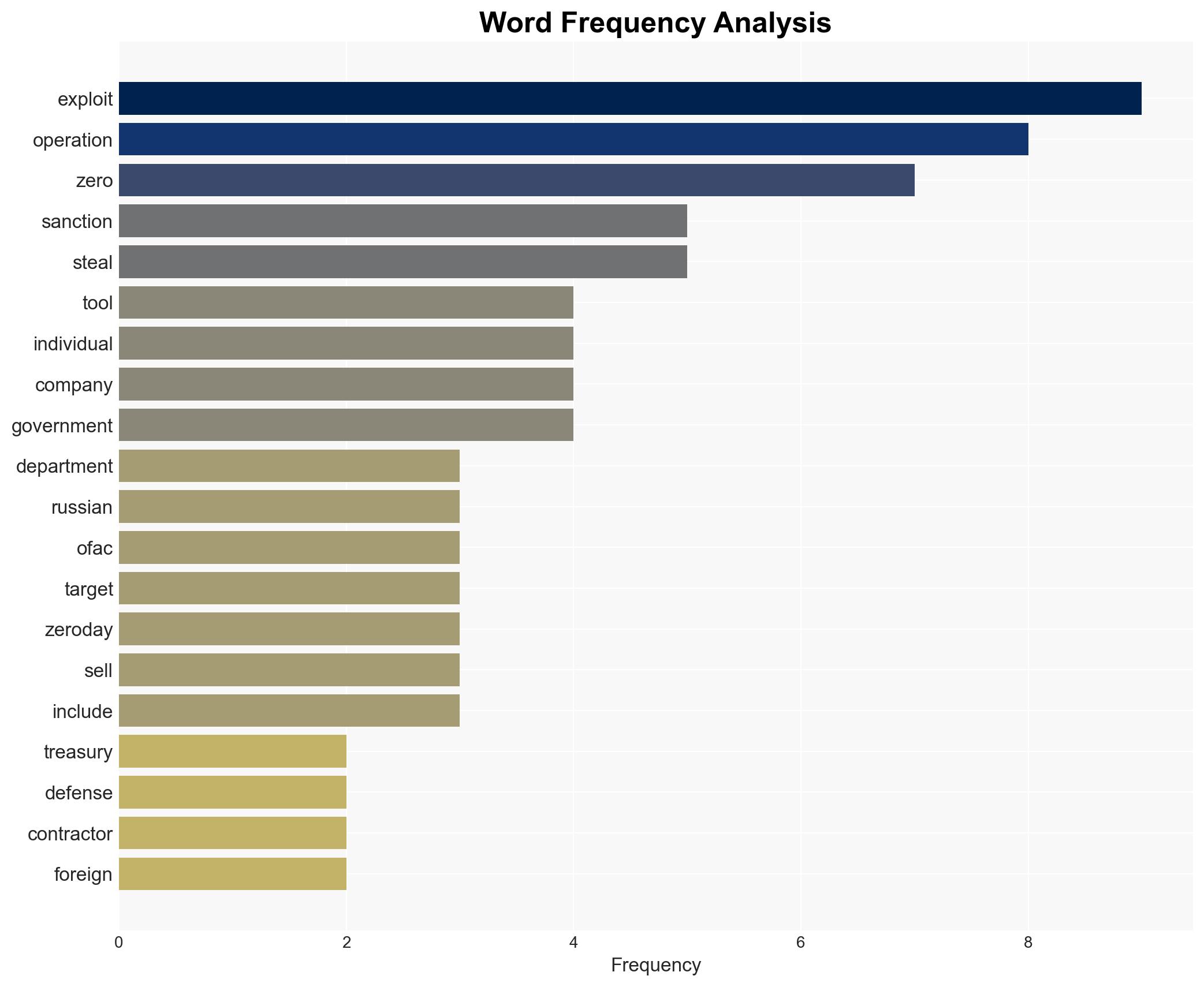
Intelligence Report: US sanctions Russian broker for buying stolen zero-day exploits
1. BLUF (Bottom Line Up Front)
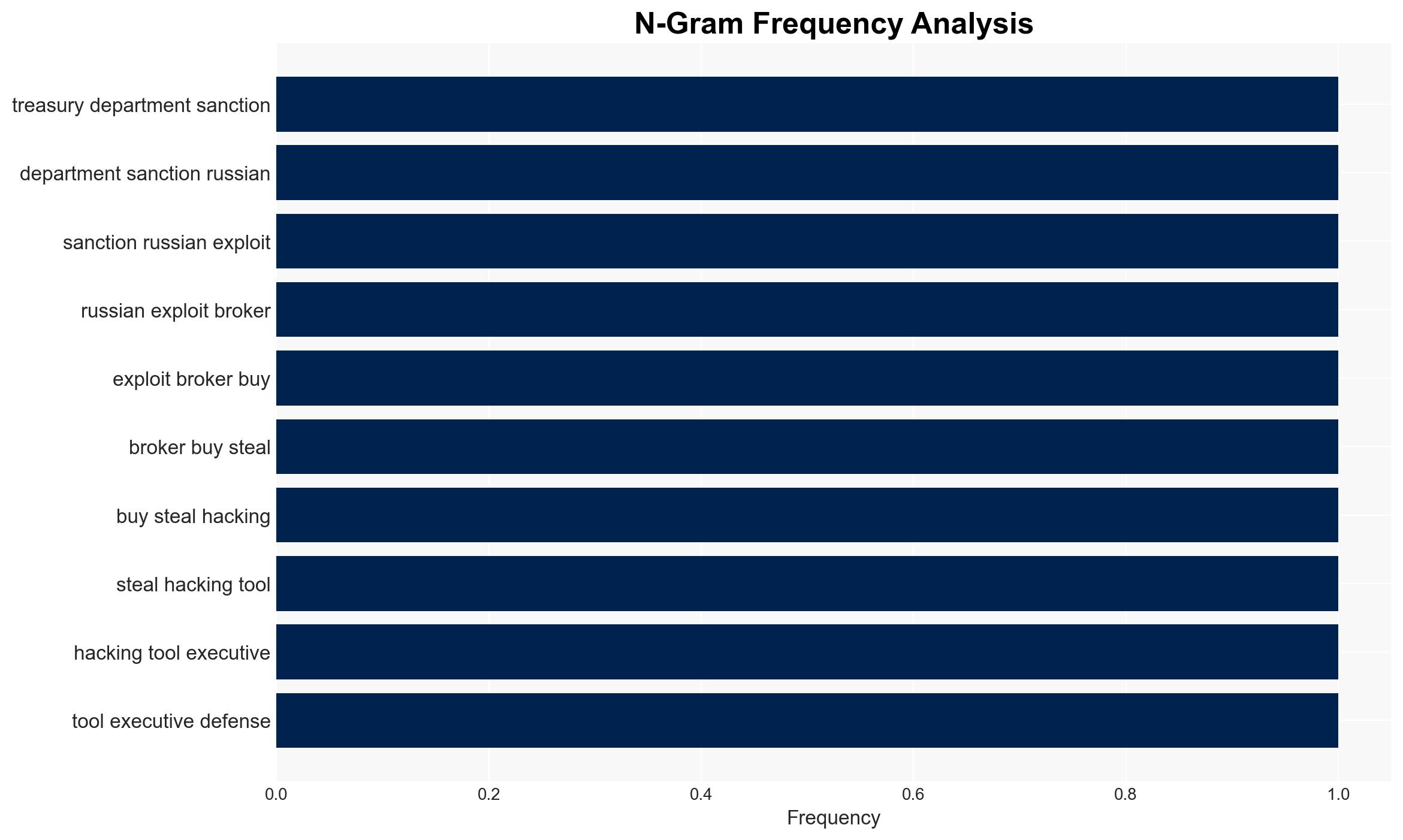
The U.S. Treasury Department has sanctioned Russian entities and individuals for acquiring stolen zero-day exploits, highlighting a significant breach in cybersecurity involving U.S. defense technologies. This action underscores the ongoing cyber threat posed by foreign adversaries leveraging stolen intellectual property. The sanctions aim to deter further exploitation and signal a robust U.S. response. Overall confidence in this assessment is moderate, given the complexity of cyber operations and potential undisclosed actors involved.
2. Competing Hypotheses
- Hypothesis A: The sanctions will effectively deter further acquisition and use of stolen exploits by Russian entities. Supporting evidence includes the freezing of U.S.-held assets and the legal ramifications for associated individuals. However, the effectiveness is uncertain due to potential undisclosed networks and alternative funding mechanisms.
- Hypothesis B: The sanctions will have limited impact, and Russian entities will continue to acquire and utilize stolen exploits through alternative channels. This is supported by the adaptability of cybercriminal networks and the potential for continued covert operations. Contradicting evidence includes the immediate disruption of known entities and individuals.
- Assessment: Hypothesis B is currently better supported due to the historical resilience and adaptability of cybercriminal networks. Indicators such as continued exploit acquisition or new entities emerging could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The sanctioned entities are primary actors in the exploit market; sanctions will disrupt their operations; other nations will support U.S. sanctions; cybercriminal networks are adaptable but not invulnerable.
- Information Gaps: The full extent of Operation Zero’s network and client base; potential undisclosed collaborators or alternative funding sources.
- Bias & Deception Risks: Potential underestimation of the resilience of cybercriminal networks; reliance on open-source data that may omit covert operations; possible misinformation from sanctioned entities.
4. Implications and Strategic Risks
This development could escalate tensions between the U.S. and Russia, impacting diplomatic relations and cybersecurity policies. It may also prompt other nations to reassess their cybersecurity strategies and alliances.
- Political / Geopolitical: Potential for increased diplomatic strain between the U.S. and Russia, influencing broader geopolitical alignments.
- Security / Counter-Terrorism: Heightened threat environment as cybercriminal networks seek alternative methods to acquire exploits.
- Cyber / Information Space: Increased focus on cybersecurity defenses and potential retaliatory cyber operations by affected entities.
- Economic / Social: Potential economic impacts on sanctioned entities and ripple effects on global cybersecurity markets.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of sanctioned entities, increase intelligence-sharing with allies, and bolster cybersecurity defenses.
- Medium-Term Posture (1–12 months): Develop resilience measures, strengthen international partnerships, and invest in cybersecurity capability development.
- Scenario Outlook:
- Best: Sanctions effectively disrupt operations, leading to reduced cyber threats.
- Worst: Sanctioned entities adapt and continue operations, escalating cyber threats.
- Most-Likely: Partial disruption with ongoing attempts to circumvent sanctions; continued vigilance required.
6. Key Individuals and Entities
- Sergey Sergeyevich Zelenyuk
- Matrix LLC (Operation Zero)
- Peter Williams
- Special Technology Services LLC
- Oleg Vyacheslavovich Kucherov
- Advance Security Solutions
7. Thematic Tags
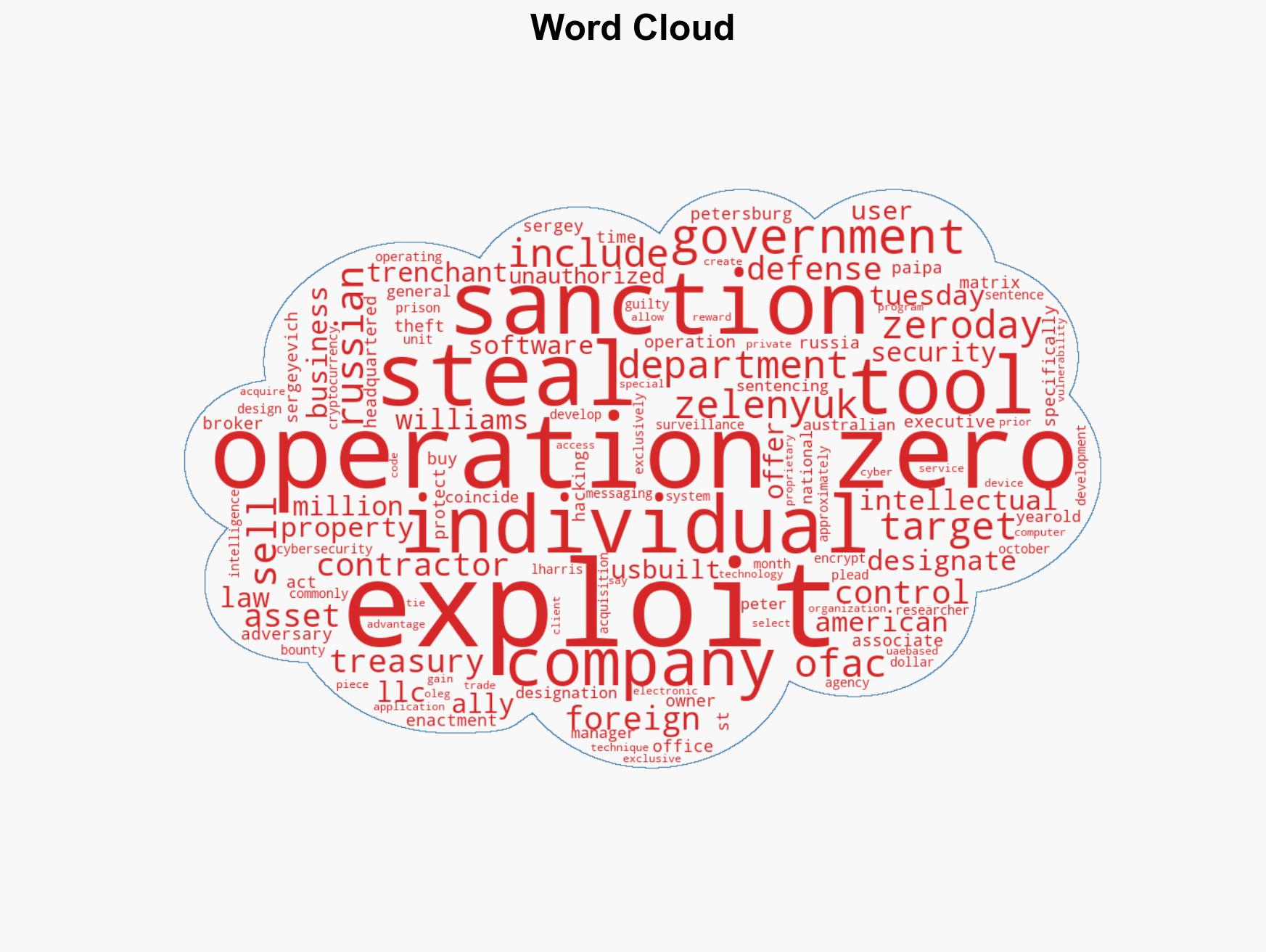
cybersecurity, sanctions, cyber-espionage, intellectual property theft, U.S.-Russia relations, zero-day exploits, international security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us