US Treasury targets individuals and firms linked to North Korea’s IT worker fraud scheme funding weapons prog…
Published on: 2026-03-13
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: US Treasury sanctions enablers of North Korea IT worker fraud ring
1. BLUF (Bottom Line Up Front)
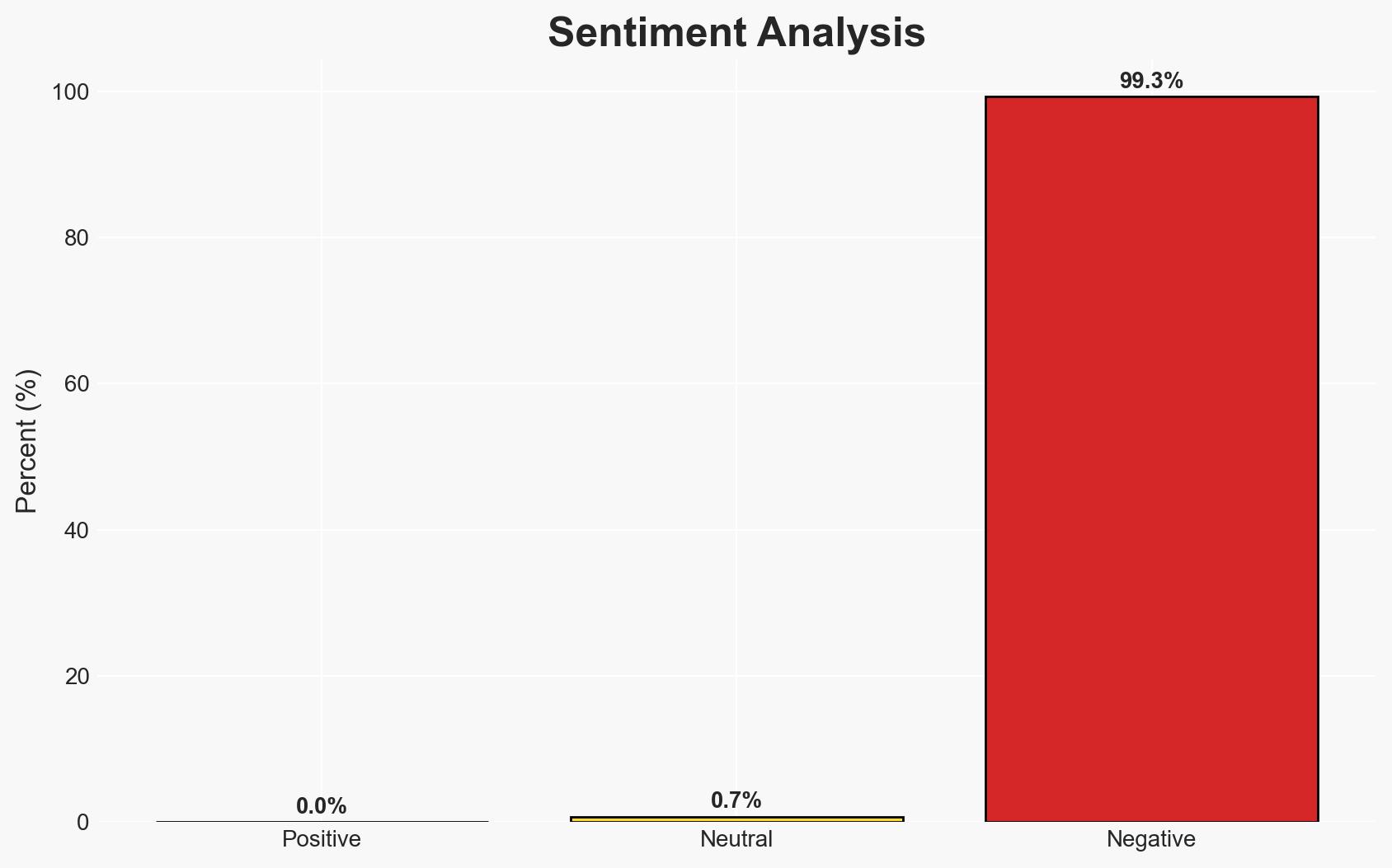
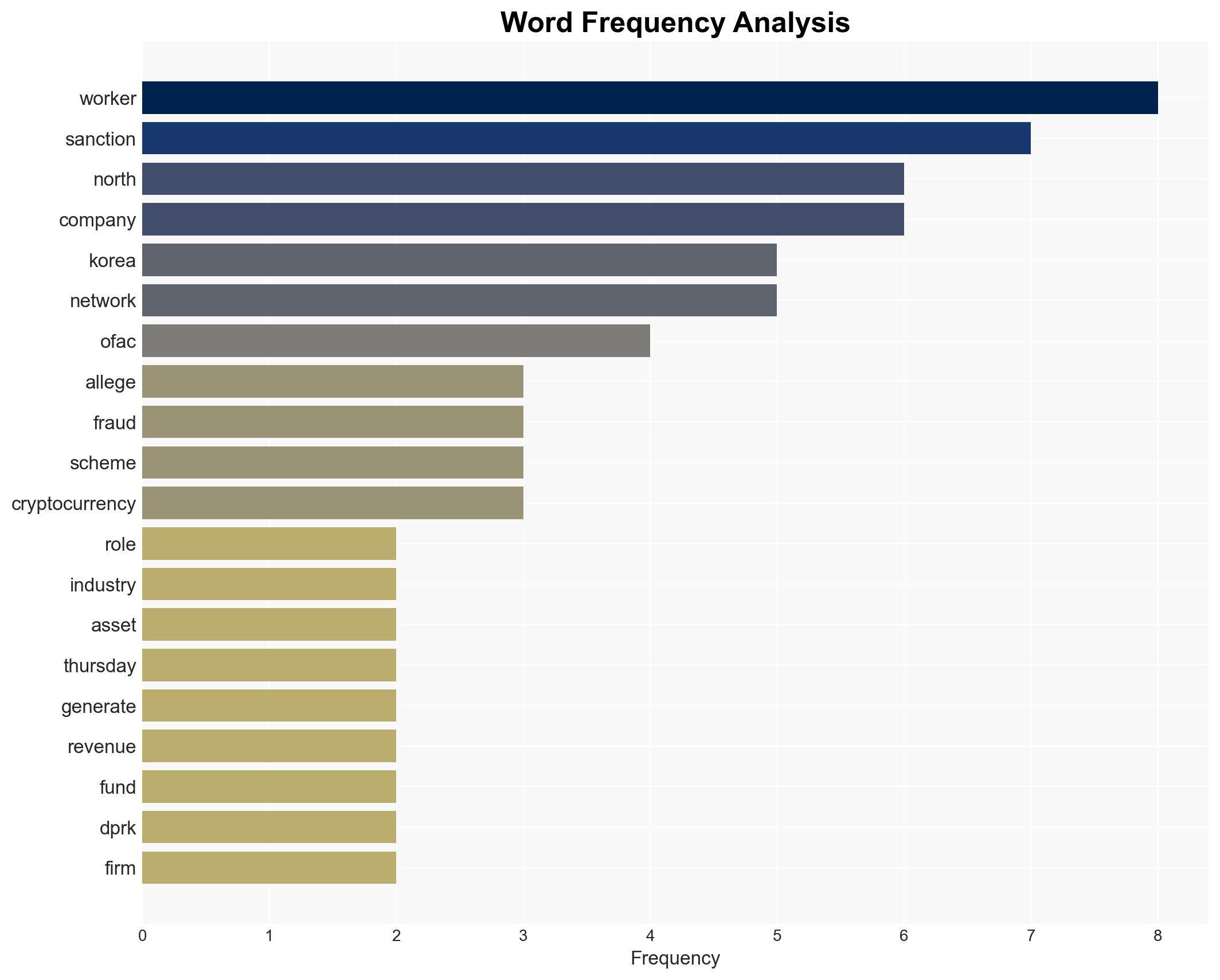
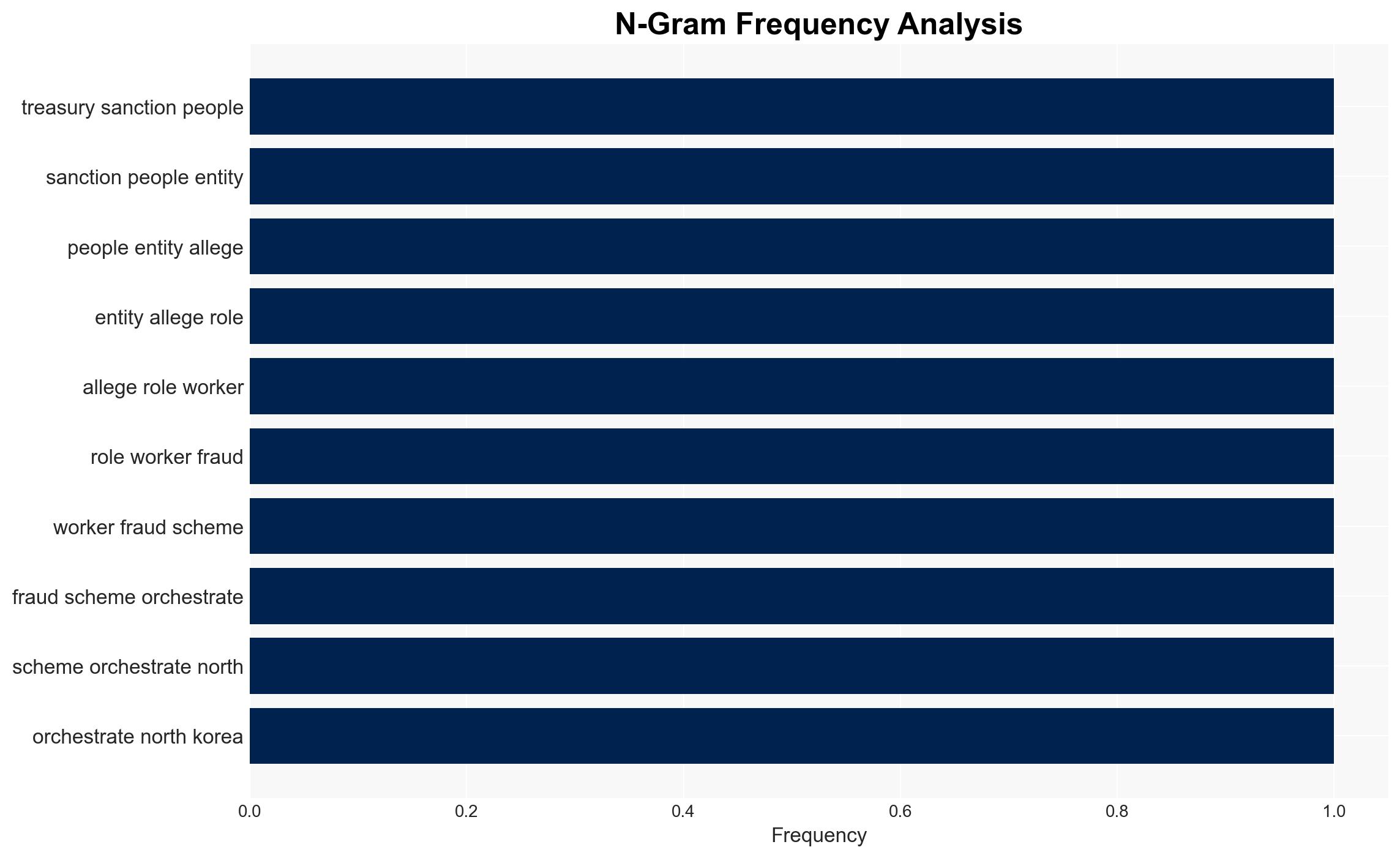
The US Treasury’s sanctions on individuals and entities linked to North Korea’s IT worker fraud scheme are intended to disrupt revenue streams funding the DPRK’s weapons program. This action highlights the sophistication and global reach of North Korean cyber operations. The sanctions are likely to impact the targeted entities’ operations significantly, with moderate confidence in the effectiveness of these measures due to potential adaptive responses from North Korean networks.
2. Competing Hypotheses
- Hypothesis A: The sanctions will significantly disrupt North Korea’s ability to generate revenue through IT worker fraud, thereby weakening its weapons program funding. Supporting evidence includes the freezing of assets and prohibition of US financial interactions. However, uncertainties remain regarding North Korea’s ability to adapt and find alternative revenue streams.
- Hypothesis B: North Korea will adapt to the sanctions by shifting its operations to less regulated environments or employing more sophisticated evasion tactics, thus maintaining its revenue streams. This is supported by North Korea’s historical resilience and adaptability in circumventing international sanctions.
- Assessment: Hypothesis B is currently better supported due to North Korea’s demonstrated ability to adapt to sanctions and continue its operations. Key indicators that could shift this judgment include evidence of significant operational disruptions or a lack of adaptation by North Korean networks.
3. Key Assumptions and Red Flags
- Assumptions: North Korea relies heavily on IT worker fraud for revenue; sanctions will be enforced effectively; targeted entities have significant roles in the fraud network.
- Information Gaps: Detailed understanding of North Korea’s alternative revenue streams and the full scope of its global IT operations.
- Bias & Deception Risks: Potential bias in underestimating North Korea’s adaptability; risk of deception in the identities and roles of sanctioned individuals and entities.
4. Implications and Strategic Risks
The sanctions could lead to short-term disruptions in North Korean operations but may drive the regime to develop more sophisticated evasion tactics. This could result in increased cyber threats and geopolitical tensions.
- Political / Geopolitical: Potential escalation in US-DPRK tensions; increased diplomatic efforts to address North Korean cyber activities.
- Security / Counter-Terrorism: Heightened threat of retaliatory cyber operations by North Korea against US and allied interests.
- Cyber / Information Space: Possible increase in cyber espionage and malware deployment as North Korea seeks alternative revenue and intelligence sources.
- Economic / Social: Limited direct economic impact but potential for increased scrutiny on cryptocurrency transactions globally.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of cryptocurrency transactions; increase collaboration with international partners to track and disrupt North Korean cyber activities.
- Medium-Term Posture (1–12 months): Develop resilience measures for critical infrastructure; strengthen partnerships with private sector entities to improve threat intelligence sharing.
- Scenario Outlook:
- Best: North Korean operations are significantly disrupted, leading to decreased funding for its weapons program.
- Worst: North Korea successfully adapts, increasing cyber threats and geopolitical tensions.
- Most-Likely: North Korea adapts partially, maintaining some revenue streams while facing increased international scrutiny.
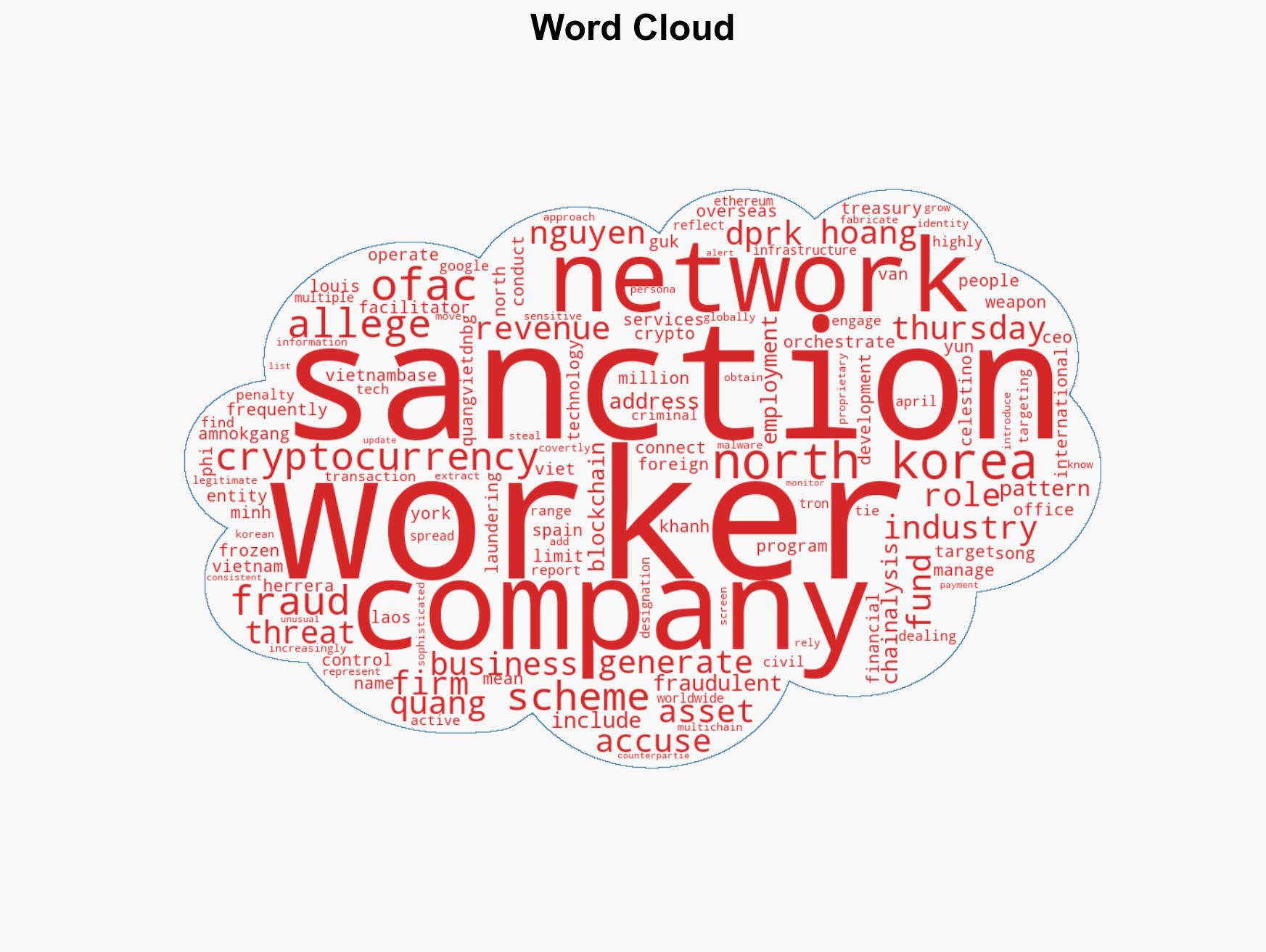
6. Key Individuals and Entities
- Amnokgang Technology Development Company
- Nguyen Quang Viet
- Do Phi Khanh
- Hoang Van Nguyen
- Yun Song Guk
- Hoang Minh Quang
- York Louis Celestino Herrera
7. Thematic Tags
cybersecurity, sanctions, North Korea, cyber-fraud, cryptocurrency, international security, IT worker schemes, geopolitical tensions
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us