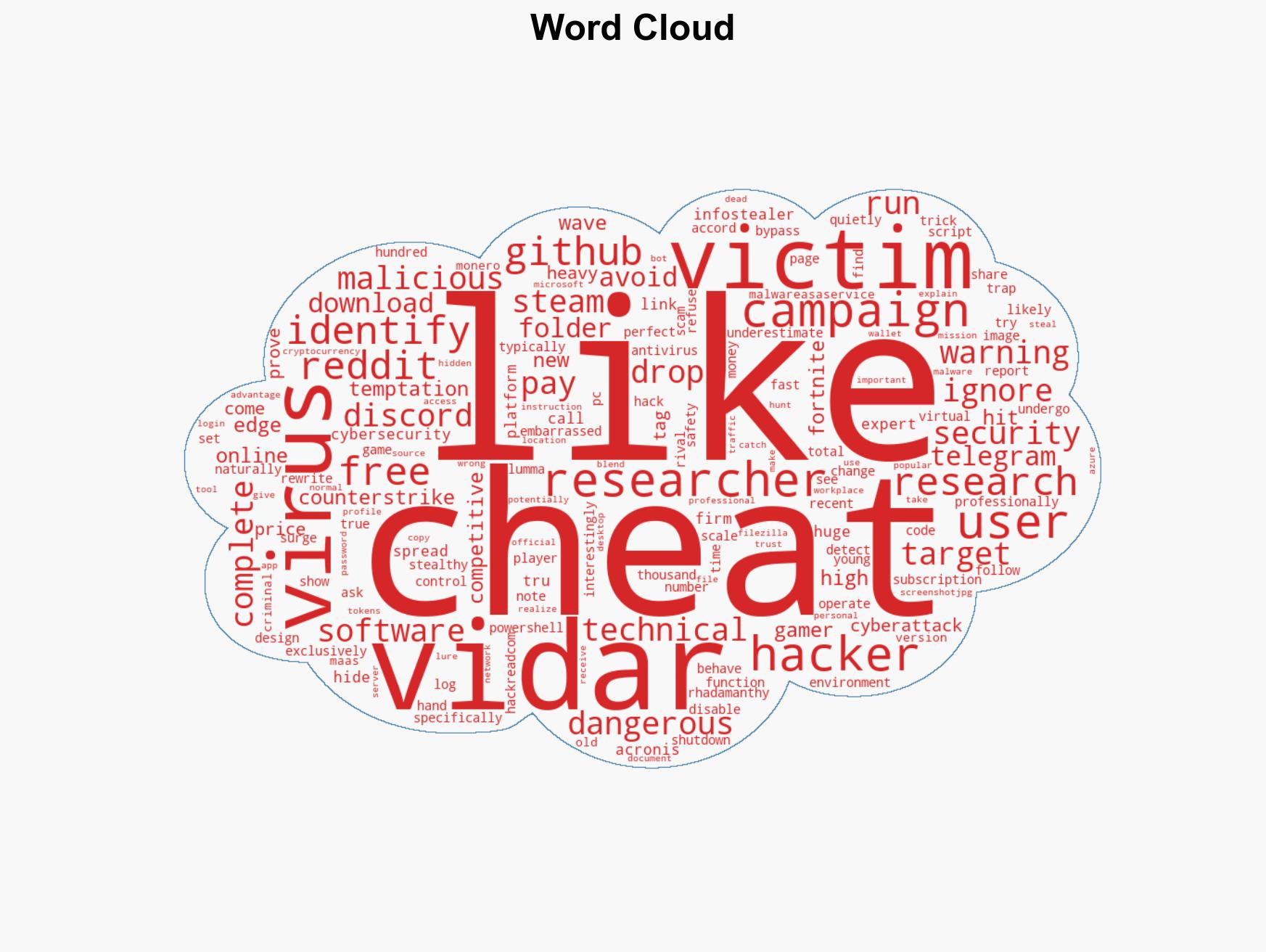
Vidar 2.0 Infostealer Targets Gamers with Malicious Game Cheat Links on GitHub and Reddit
Published on: 2026-03-17
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: New Vidar 20 Infostealer Spreads via Fake Game Cheats on GitHub Reddit
1. BLUF (Bottom Line Up Front)
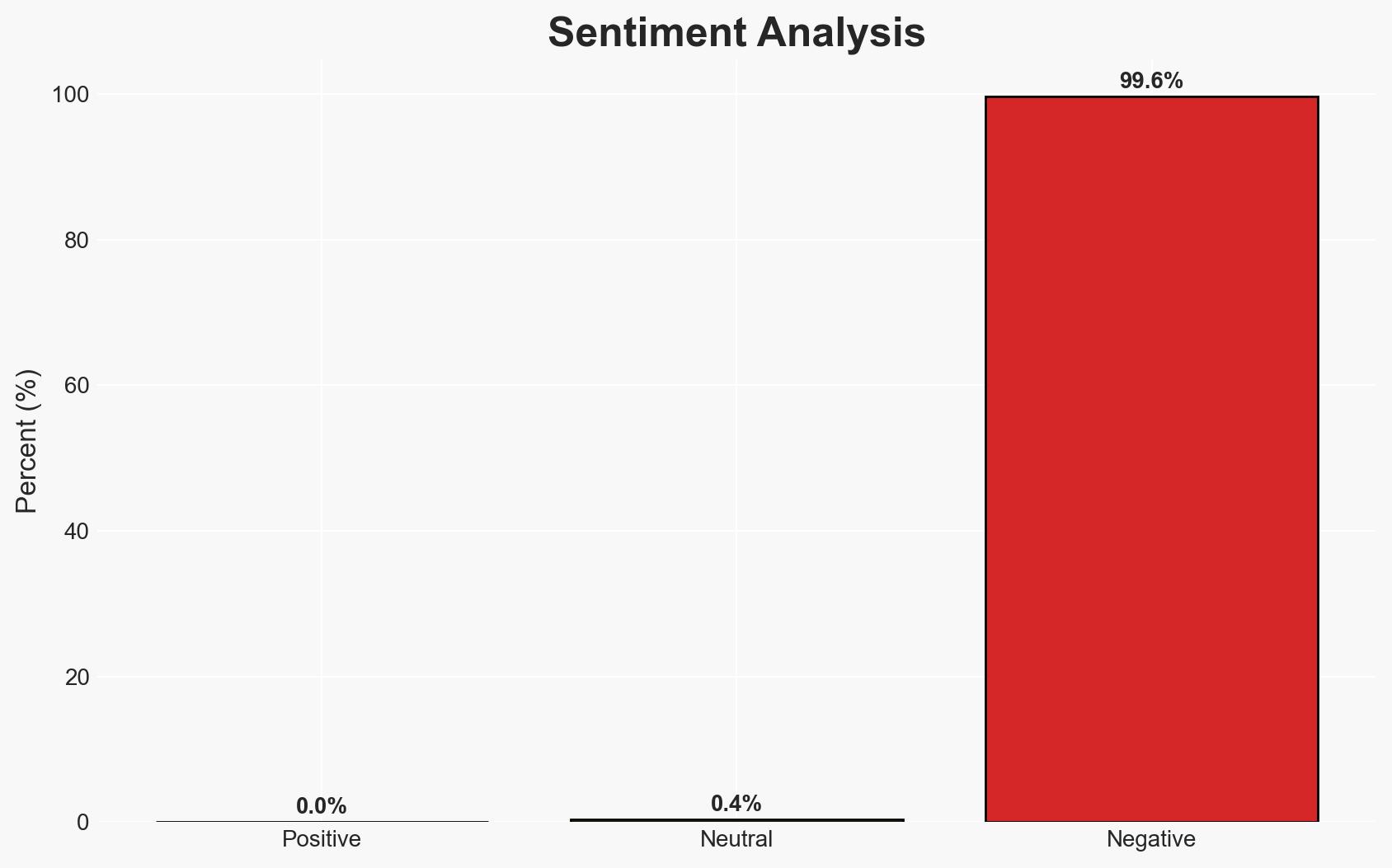
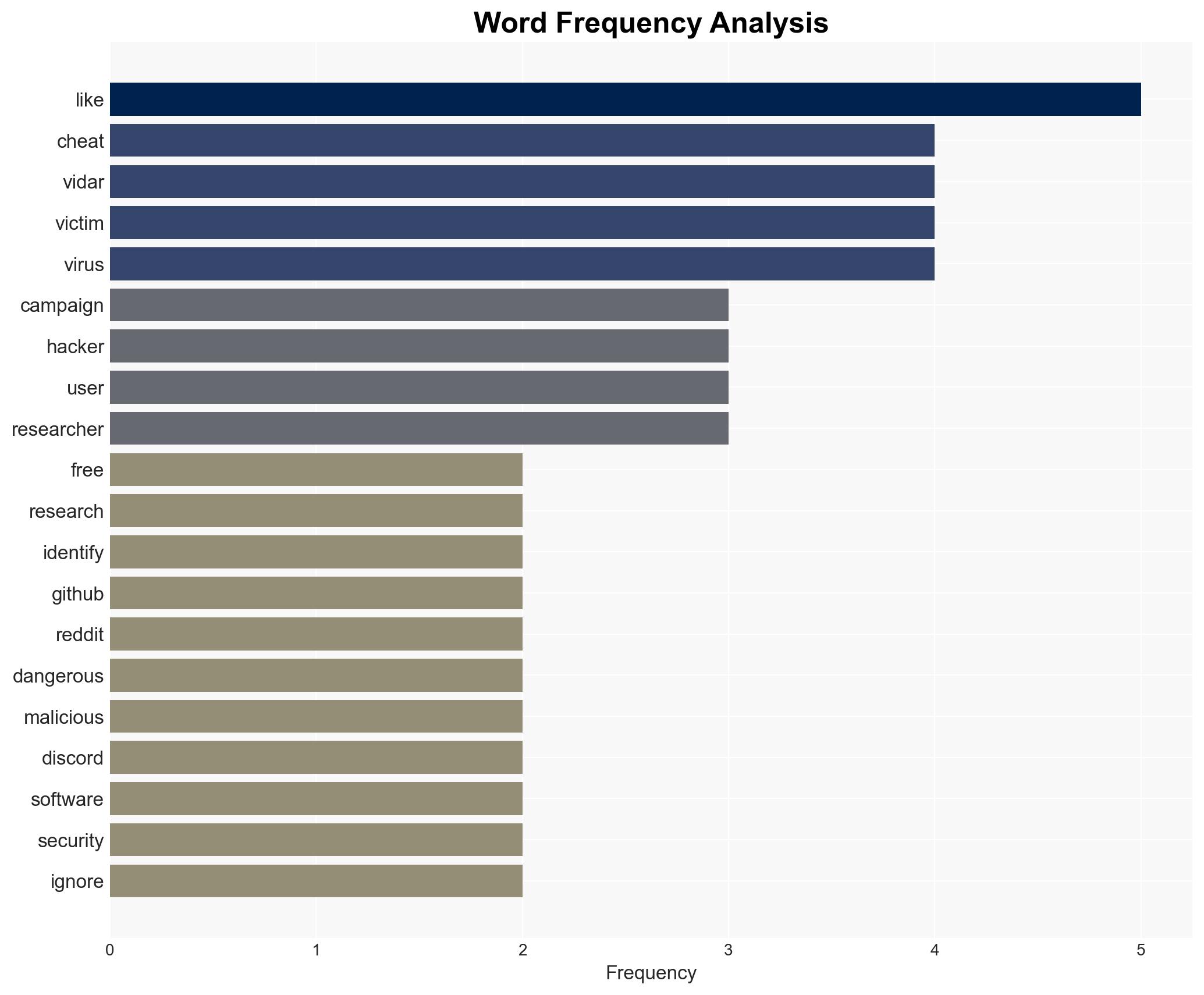
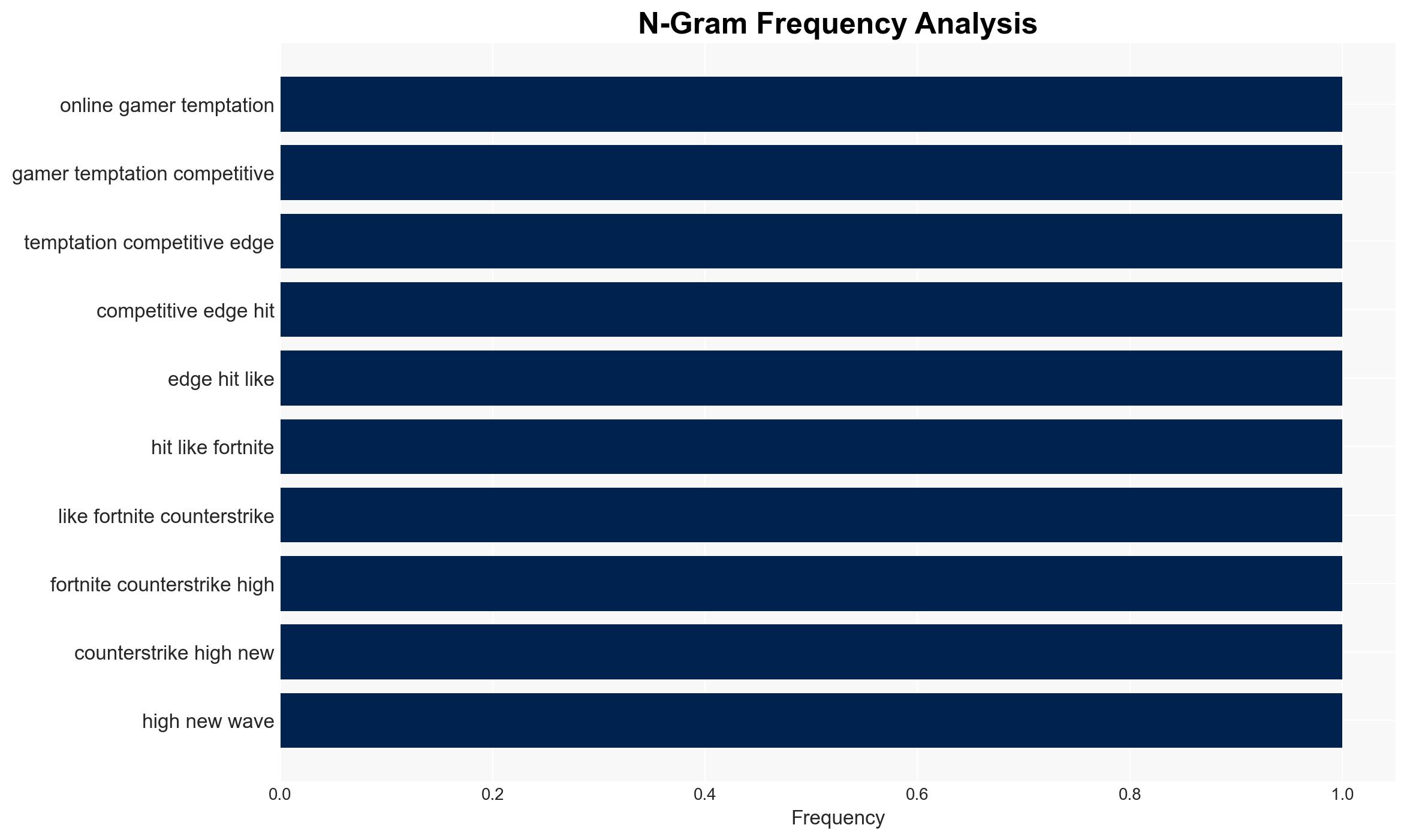
The Vidar 2.0 infostealer is spreading through fake game cheats on platforms like GitHub and Reddit, targeting younger gamers. This campaign exploits users’ desire for free advantages, leading to significant data breaches. The malware’s technical sophistication and stealth make it a potent threat, with moderate confidence in the assessment that its prevalence is underestimated.
2. Competing Hypotheses
- Hypothesis A: The Vidar 2.0 campaign is primarily opportunistic, exploiting the shutdown of rival malware to capture a larger market share. This is supported by the timing of the surge and the use of common platforms like GitHub and Reddit. However, the true scale of the campaign remains uncertain.
- Hypothesis B: The campaign is part of a coordinated effort by a sophisticated threat actor to establish dominance in the Malware-as-a-Service market. The complete technical rewrite and advanced evasion techniques suggest a strategic intent beyond opportunism.
- Assessment: Hypothesis A is currently better supported due to the opportunistic nature of the campaign and the use of widely accessible platforms. Key indicators that could shift this judgment include evidence of centralized command structures or links to known threat actor groups.
3. Key Assumptions and Red Flags
- Assumptions: The campaign is primarily targeting younger gamers; the technical rewrite of Vidar 2.0 enhances its stealth capabilities; the use of GitHub and Reddit is primarily for distribution.
- Information Gaps: Exact number of affected users; detailed profiles of the threat actors; comprehensive analysis of the malware’s code changes.
- Bias & Deception Risks: Potential bias in underestimating the scale due to reliance on reported cases; deception risk from malware’s evasion techniques, which could mislead analysts about its capabilities.
4. Implications and Strategic Risks
The Vidar 2.0 campaign could lead to increased data breaches and financial losses among gamers, with potential spillover into professional environments if workplace credentials are compromised.
- Political / Geopolitical: Limited direct implications, but potential for increased scrutiny on platforms like GitHub and Reddit.
- Security / Counter-Terrorism: Heightened threat environment for cybersecurity, particularly in gaming and associated sectors.
- Cyber / Information Space: Increased sophistication in malware distribution and evasion tactics, potentially setting new standards for future campaigns.
- Economic / Social: Potential economic impact on individuals and businesses through data theft; social impact on trust in online platforms.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of GitHub and Reddit for malicious activities; increase awareness campaigns targeting younger gamers about the risks of downloading cheats.
- Medium-Term Posture (1–12 months): Develop partnerships with gaming companies to improve security measures; invest in research to better understand and counteract evolving malware tactics.
- Scenario Outlook:
- Best: Successful mitigation efforts reduce the campaign’s impact, with improved detection and prevention measures.
- Worst: The campaign expands, leading to widespread data breaches and financial losses.
- Most-Likely: Continued sporadic incidents with gradual improvements in detection and response capabilities.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, malware, gaming, information security, Malware-as-a-Service, online platforms, data breach
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us