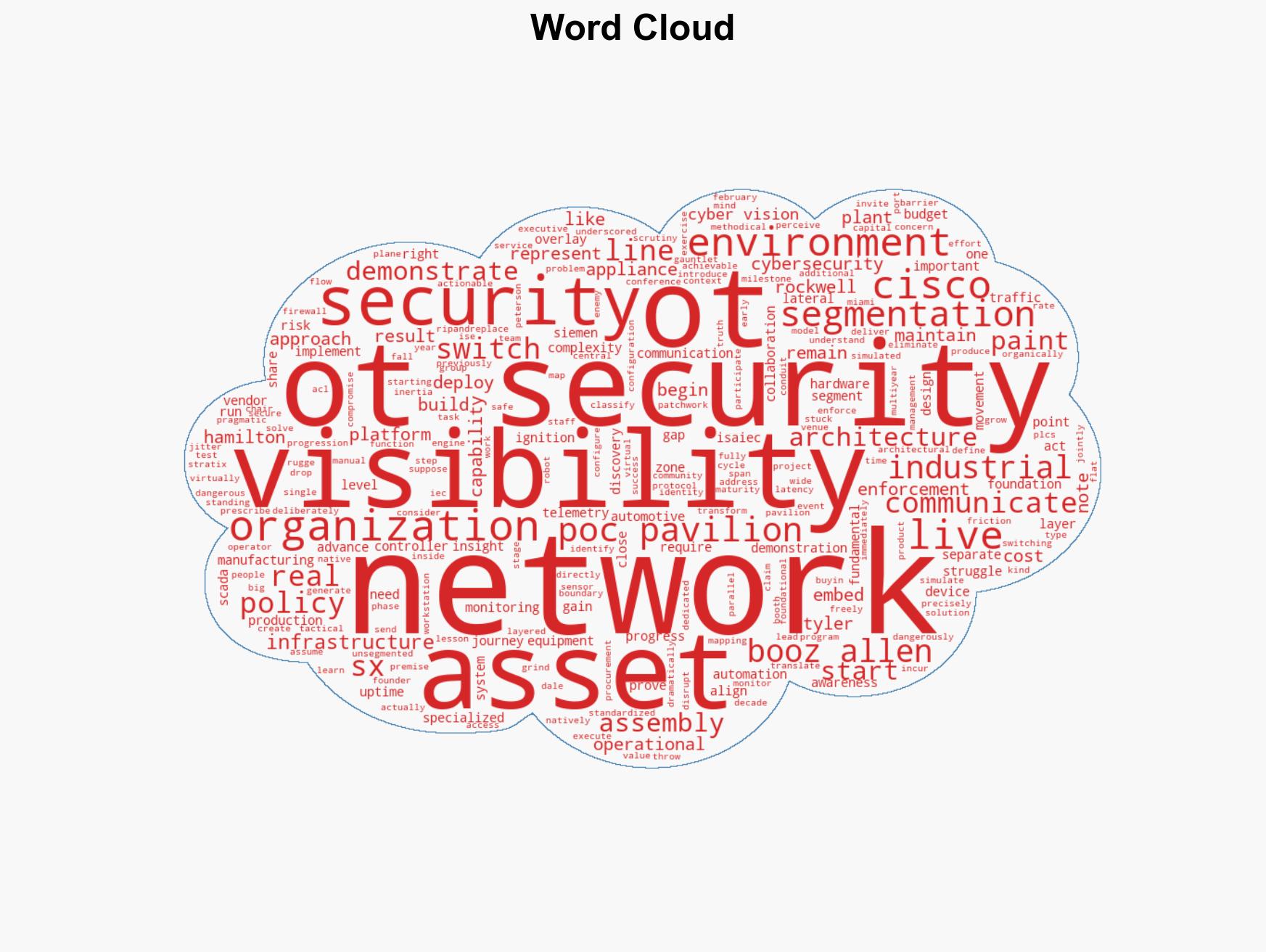
Visibility-Driven Segmentation Transforms the Foundation of OT Security Strategies
Published on: 2026-04-01
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: How Visibility-Driven Segmentation is Redefining the OT Security Starting Line
1. BLUF (Bottom Line Up Front)
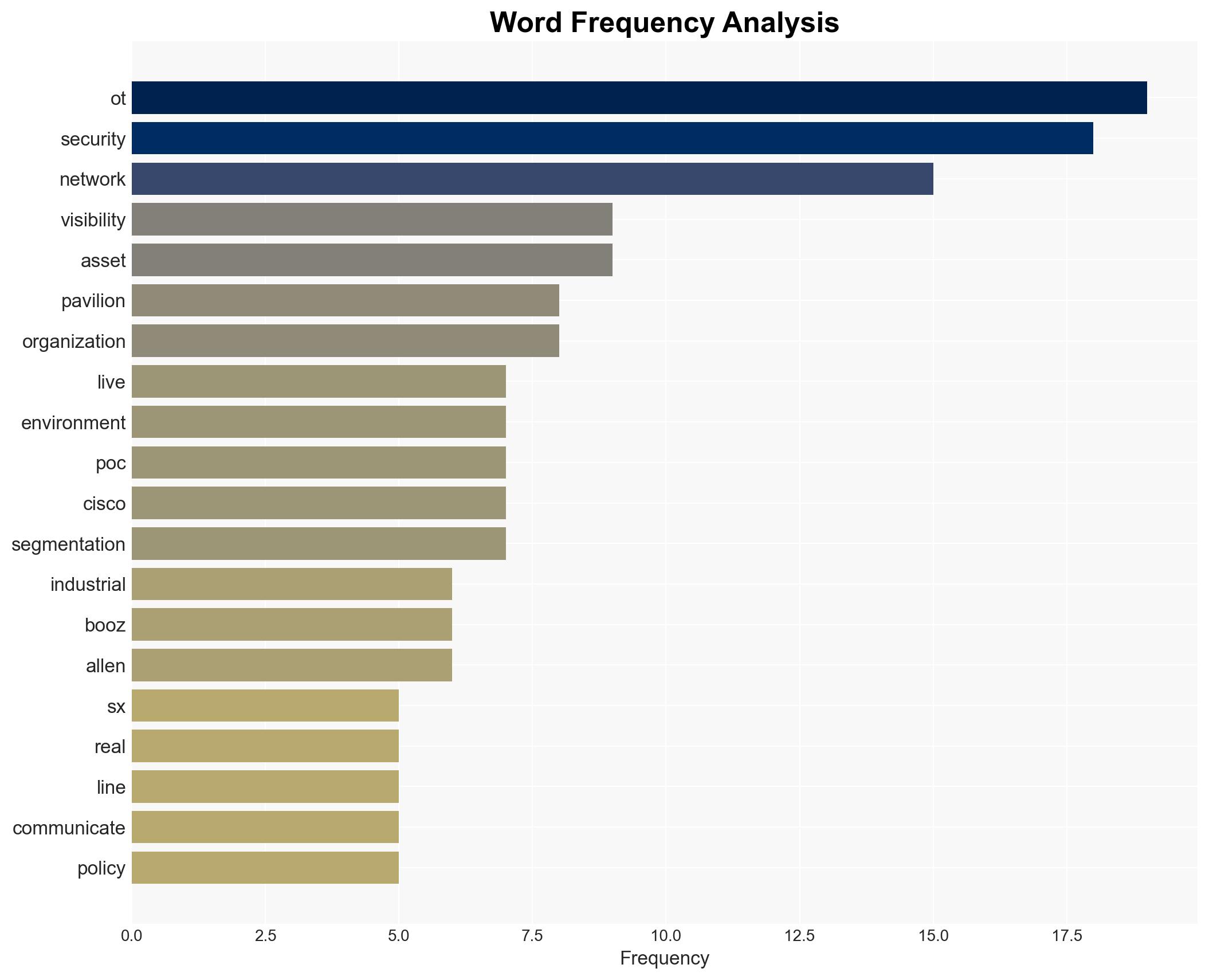
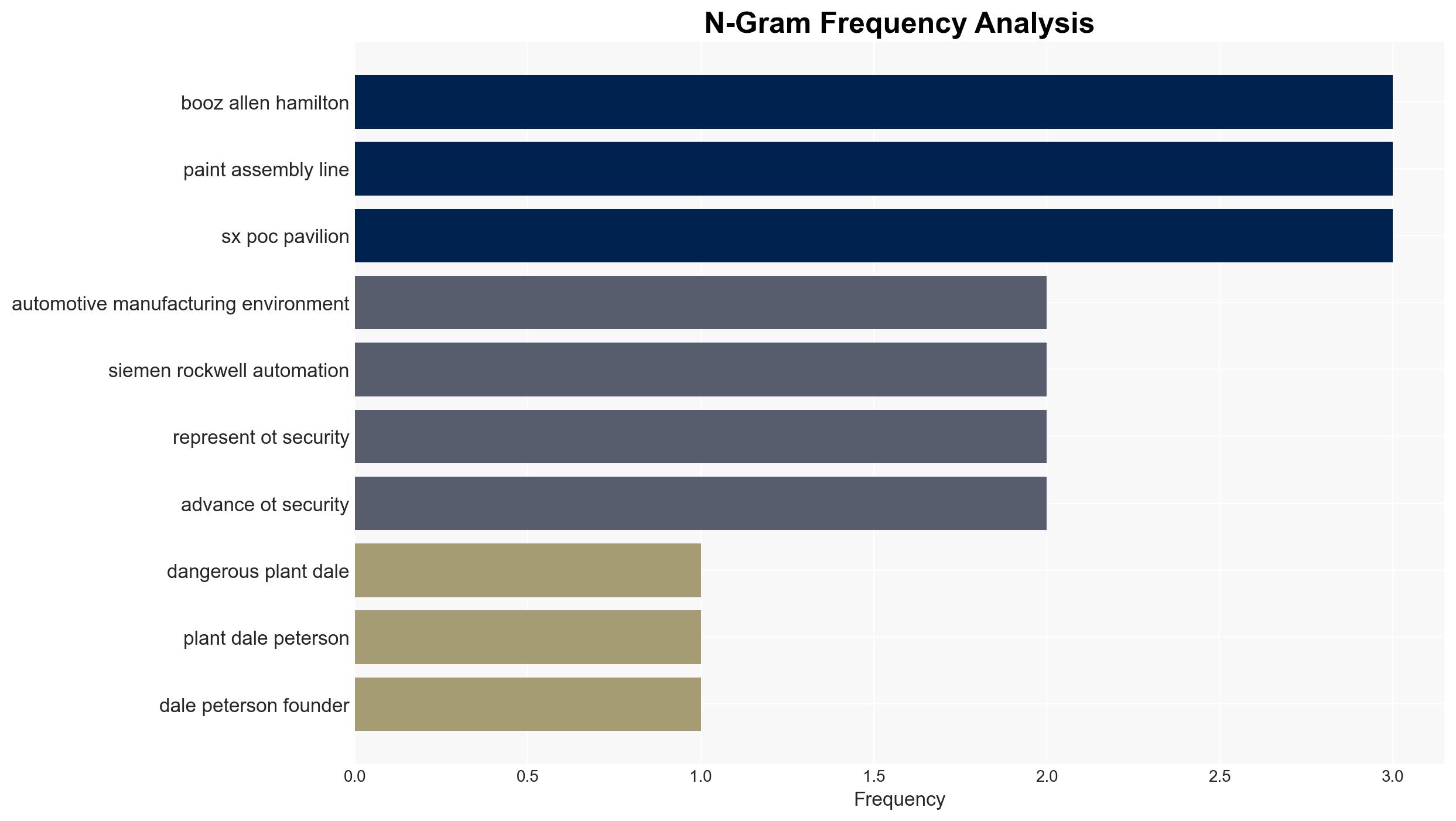
The integration of visibility-driven segmentation in OT environments is reshaping industrial cybersecurity by addressing the critical gap in asset visibility. The approach demonstrated at the S4x26 conference highlights the necessity of understanding network components before implementing security measures. This development primarily affects industrial operators and cybersecurity vendors, with moderate confidence in its potential to enhance OT security frameworks.
2. Competing Hypotheses
- Hypothesis A: Visibility-driven segmentation will significantly improve OT security by enabling precise asset identification and communication flow mapping, thus reducing lateral movement risks. This hypothesis is supported by the successful demonstration at S4x26 and the immediate actionable results observed.
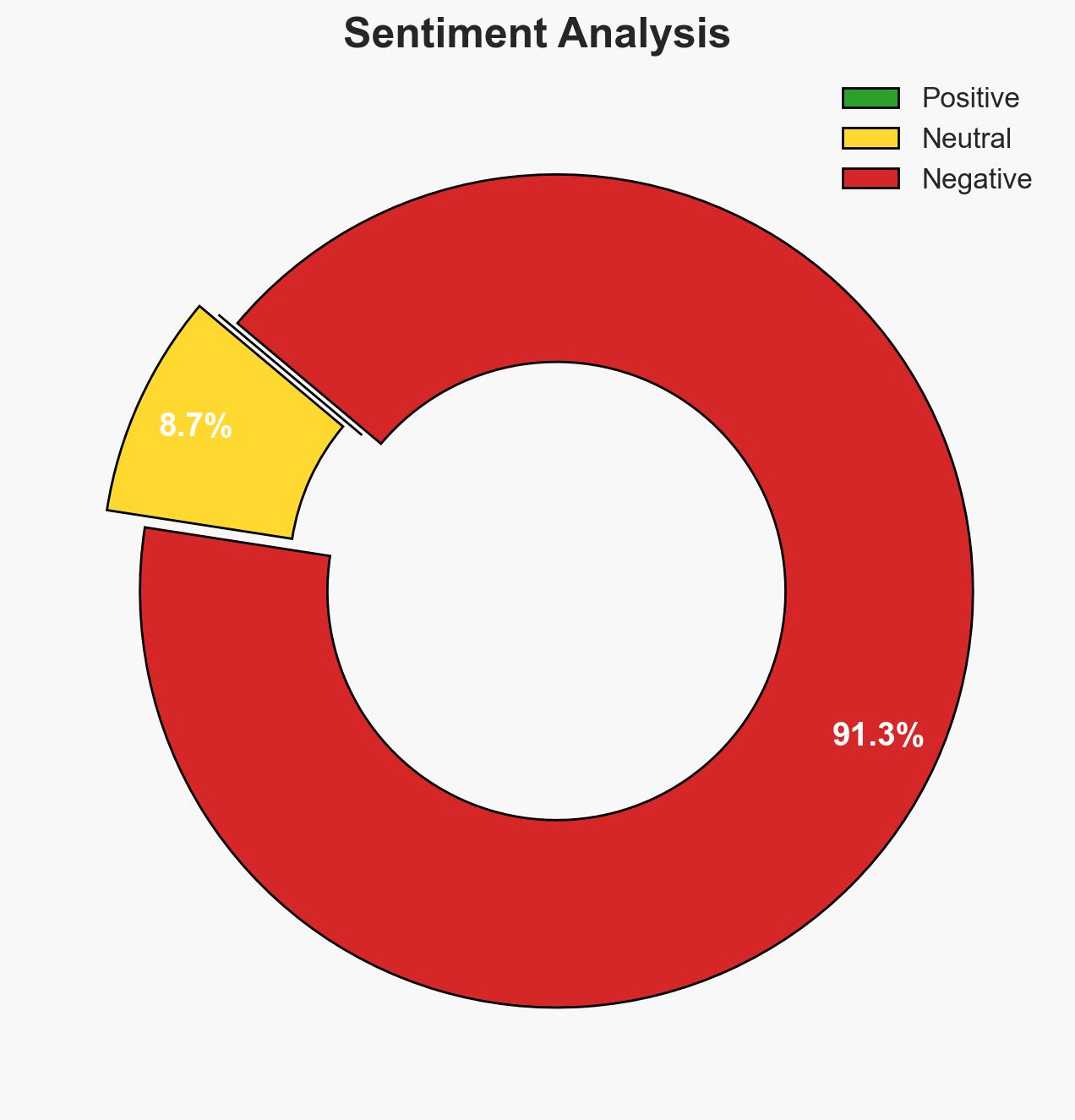
- Hypothesis B: The complexity and cost of implementing visibility-driven segmentation may deter widespread adoption, limiting its impact on overall OT security. This is supported by the historical inertia in OT security adoption due to perceived costs and operational disruptions.
- Assessment: Hypothesis A is currently better supported due to the practical demonstration of benefits and the phased approach that minimizes disruption. However, ongoing monitoring of adoption rates and cost-benefit analyses could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Organizations are willing to invest in visibility tools; the technology will scale effectively across diverse OT environments; existing network infrastructures can support the integration of new visibility solutions.
- Information Gaps: Data on the long-term cost-effectiveness of visibility-driven segmentation; specific case studies of implementation in varied industrial settings; feedback from operators on integration challenges.
- Bias & Deception Risks: Potential bias from vendors promoting their solutions; lack of independent verification of demonstration results; possible underreporting of integration challenges by early adopters.
4. Implications and Strategic Risks
The adoption of visibility-driven segmentation could lead to a paradigm shift in OT security, influencing broader cybersecurity practices and policies. However, the transition may face resistance due to cost and complexity concerns.
- Political / Geopolitical: Potential for increased regulatory scrutiny and policy development around industrial cybersecurity standards.
- Security / Counter-Terrorism: Enhanced security postures could deter cyber threats targeting critical infrastructure, reducing vulnerabilities to state and non-state actors.
- Cyber / Information Space: Improved visibility may lead to better threat intelligence and incident response capabilities, impacting the broader cybersecurity landscape.
- Economic / Social: Successful implementation could drive economic efficiencies and enhance trust in industrial operations, though initial investments may strain smaller operators.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Encourage pilot programs for visibility-driven segmentation; gather data on initial implementation challenges and successes.
- Medium-Term Posture (1–12 months): Develop partnerships with technology providers to facilitate knowledge sharing; invest in training for OT security personnel.
- Scenario Outlook:
- Best: Widespread adoption leads to significant reductions in OT security incidents.
- Worst: High costs and integration challenges stall adoption, leaving vulnerabilities unaddressed.
- Most-Likely: Gradual adoption with mixed results, leading to incremental improvements in OT security.
6. Key Individuals and Entities
- Dale Peterson, founder and program chair of S4
- Booz Allen Hamilton
- Cisco
- Siemens
- Rockwell Automation
7. Thematic Tags
cybersecurity, OT security, industrial cybersecurity, network segmentation, asset visibility, cybersecurity innovation, critical infrastructure protection
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us