Vulnerabilities in Amazon Bedrock LangSmith and SGLang Allow Data Theft and Remote Code Execution Risks
Published on: 2026-03-17
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: AI Flaws in Amazon Bedrock LangSmith and SGLang Enable Data Exfiltration and RCE
1. BLUF (Bottom Line Up Front)
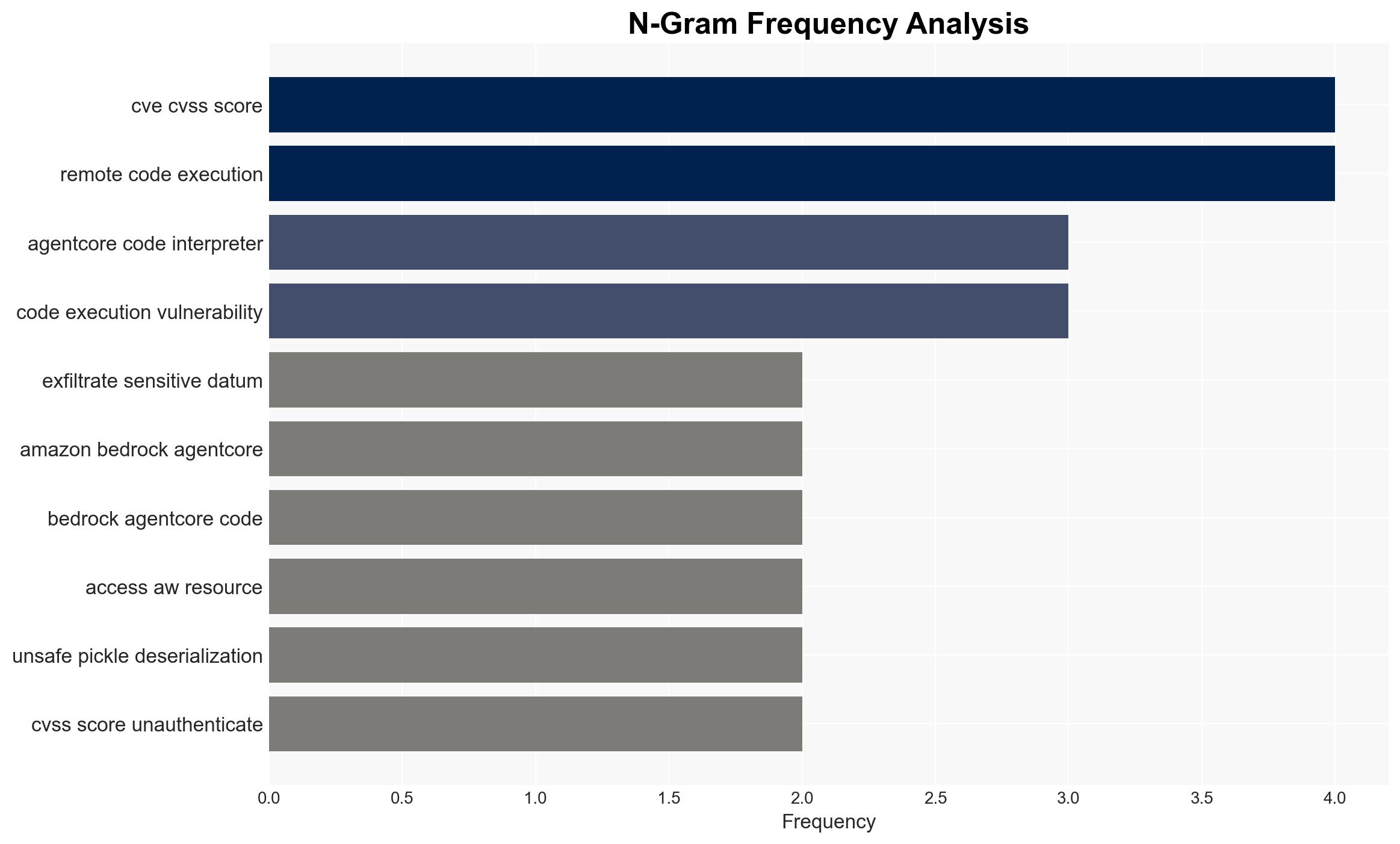
The recent disclosure of vulnerabilities in Amazon Bedrock’s AI code execution environments presents a significant cybersecurity risk, allowing potential data exfiltration and remote code execution (RCE) via DNS queries. This affects organizations using Amazon Bedrock’s sandbox mode, with potential impacts on data integrity and security. Overall, there is moderate confidence in the assessment due to the lack of a CVE identifier and Amazon’s classification of the issue as intended functionality.
2. Competing Hypotheses
- Hypothesis A: The vulnerability in Amazon Bedrock’s sandbox mode is an unintended flaw that can be exploited for data exfiltration and RCE. Evidence supporting this includes the ability to bypass network isolation controls and establish command-and-control channels. However, Amazon’s response suggests this is intended functionality, which contradicts this hypothesis.
- Hypothesis B: The functionality allowing DNS queries is an intentional design choice by Amazon, aimed at maintaining certain operational capabilities, albeit with security trade-offs. This is supported by Amazon’s recommendation to use VPC mode for complete isolation and the lack of a CVE identifier. The contradiction lies in the potential security risks posed by this design.
- Assessment: Hypothesis B is currently better supported, given Amazon’s classification of the issue as intended functionality and their guidance on using VPC mode for enhanced security. Key indicators that could shift this judgment include any future security incidents exploiting this vulnerability or changes in Amazon’s security posture.
3. Key Assumptions and Red Flags
- Assumptions: The sandbox mode’s DNS query capability is not widely exploited; Amazon’s security recommendations are effectively communicated and implemented; organizations have the capability to transition to VPC mode.
- Information Gaps: Detailed technical specifications of the sandbox mode’s DNS handling; extent of current exploitation in the wild; Amazon’s internal risk assessment and decision-making process.
- Bias & Deception Risks: Potential bias in Amazon’s public statements minimizing the security risk; cognitive bias in underestimating the likelihood of exploitation due to lack of reported incidents.
4. Implications and Strategic Risks
This development could lead to increased scrutiny of AI execution environments and their security configurations. Organizations may face operational disruptions if vulnerabilities are exploited, leading to broader security concerns.
- Political / Geopolitical: Potential for international regulatory scrutiny on AI security practices, impacting cross-border data flows.
- Security / Counter-Terrorism: Increased risk of cyber-attacks leveraging AI vulnerabilities, potentially targeting critical infrastructure.
- Cyber / Information Space: Heightened focus on securing AI environments against data exfiltration and RCE, influencing cybersecurity strategies.
- Economic / Social: Potential financial losses from data breaches and reputational damage, affecting consumer trust in AI services.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Organizations should audit their use of Amazon Bedrock’s sandbox mode, implement DNS firewalls, and transition critical workloads to VPC mode.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms for continuous monitoring and threat intelligence sharing; invest in staff training on AI security best practices.
- Scenario Outlook: Best: Rapid adoption of VPC mode mitigates risks; Worst: Exploitation leads to significant data breaches; Most-Likely: Gradual transition with isolated incidents prompting further security enhancements.
6. Key Individuals and Entities
- Amazon Bedrock
- BeyondTrust
- Kinnaird McQuade, Chief Security Architect at BeyondTrust
- Jason Soroko, Senior Fellow
7. Thematic Tags
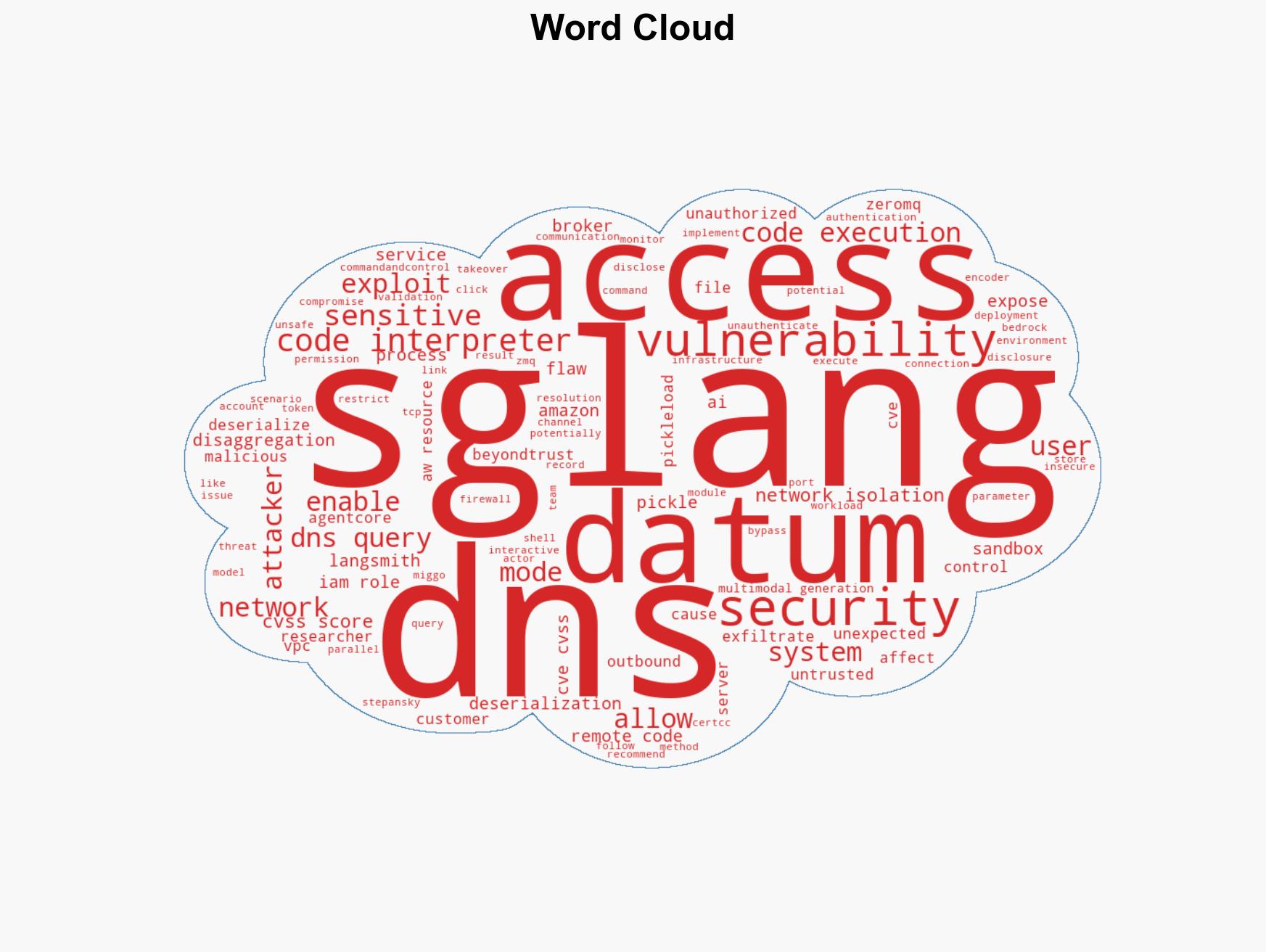
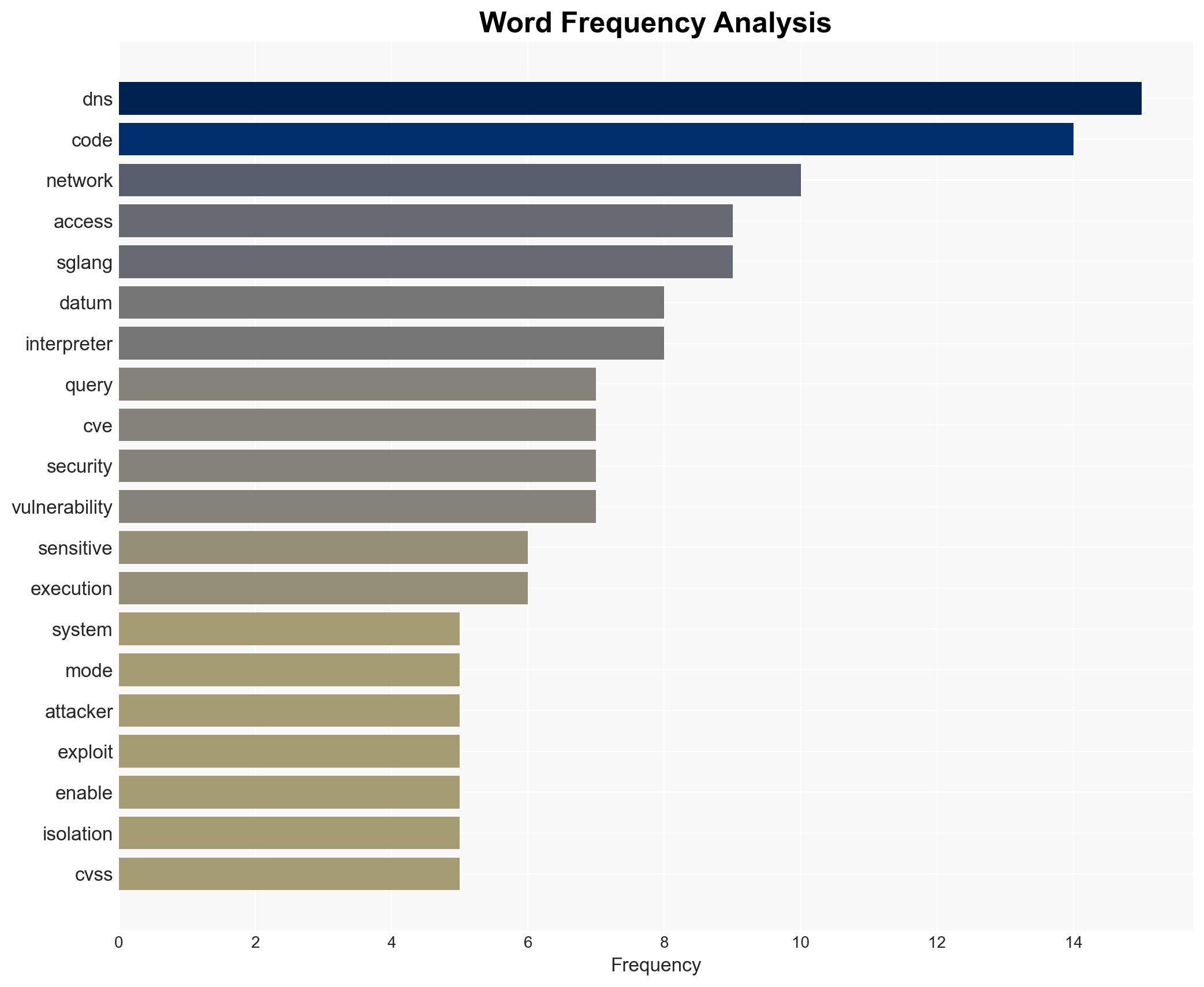
cybersecurity, AI vulnerabilities, data exfiltration, remote code execution, Amazon Bedrock, DNS queries, network isolation
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us