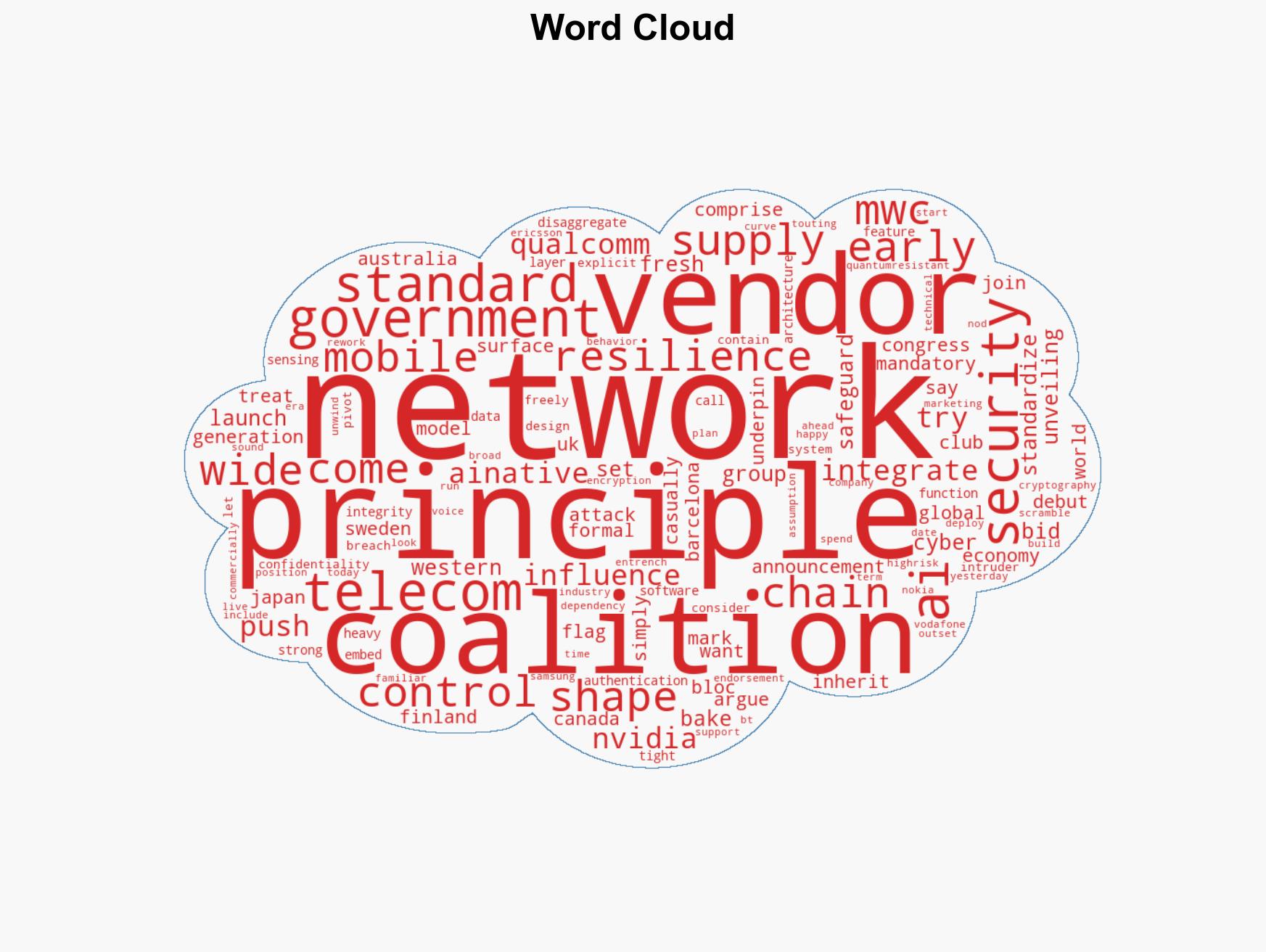
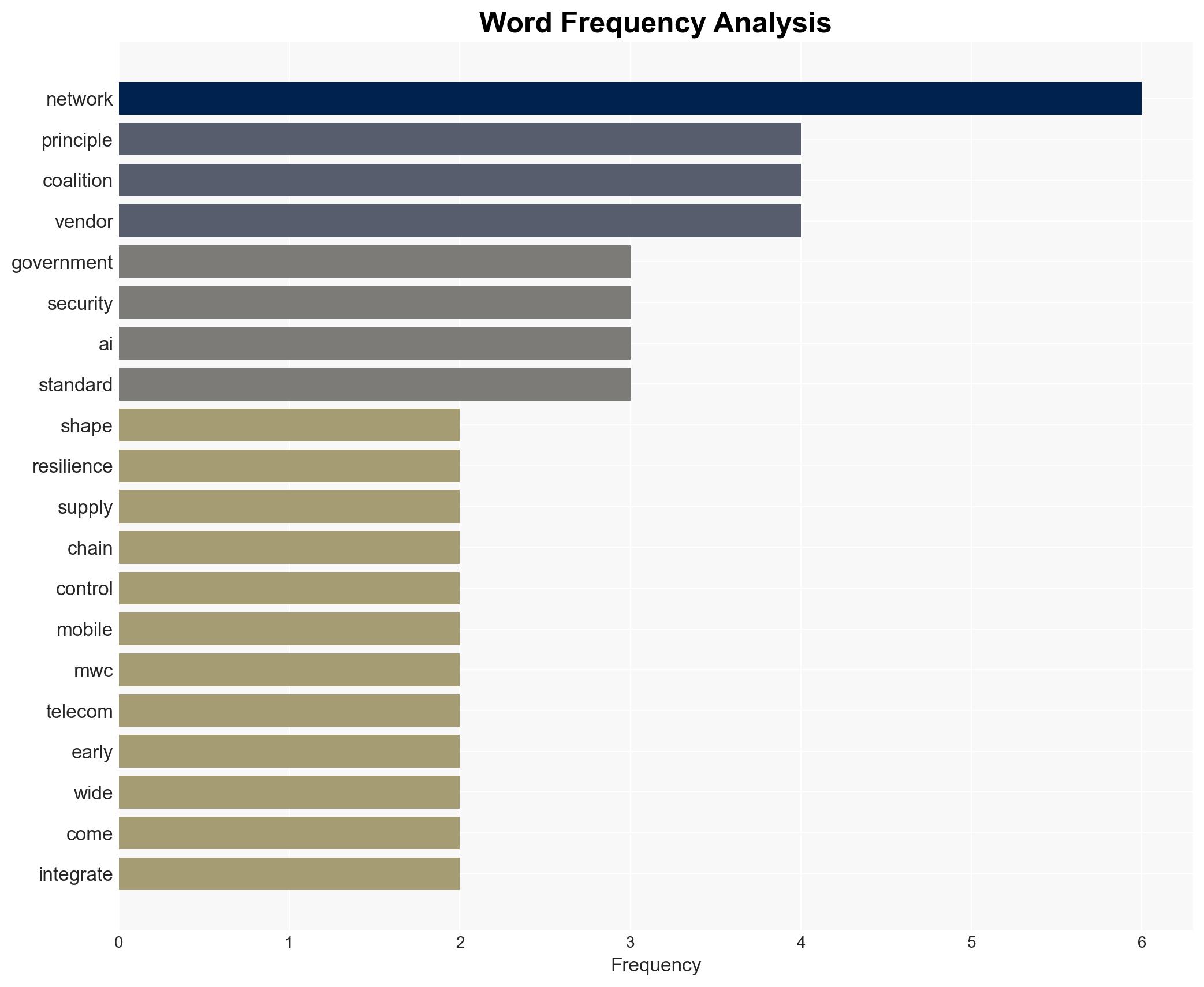
Western nations aim to influence 6G development with security principles ahead of standardization
Published on: 2026-03-03
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
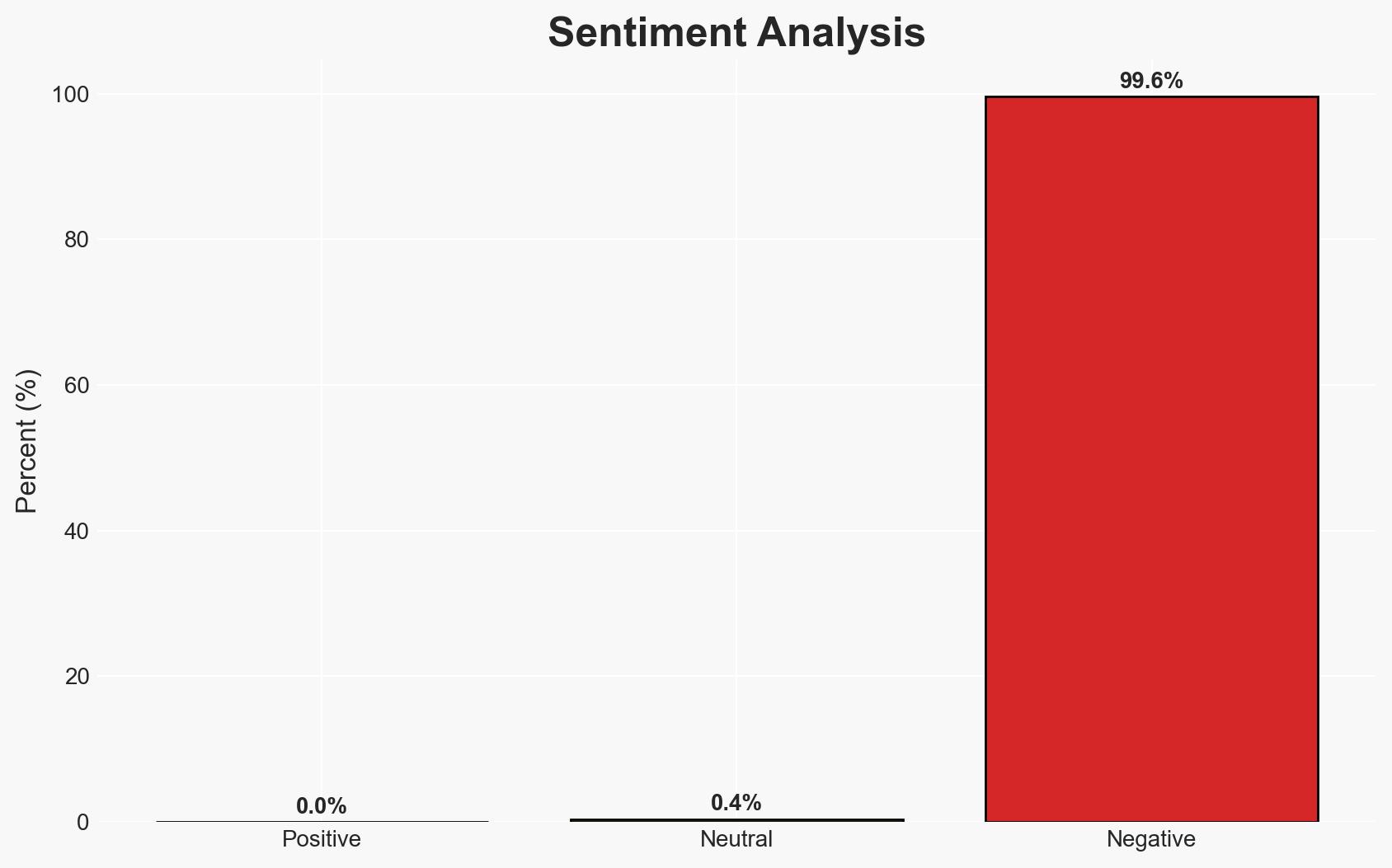
Intelligence Report: Western governments seek to lock down 6G before it even exists
1. BLUF (Bottom Line Up Front)
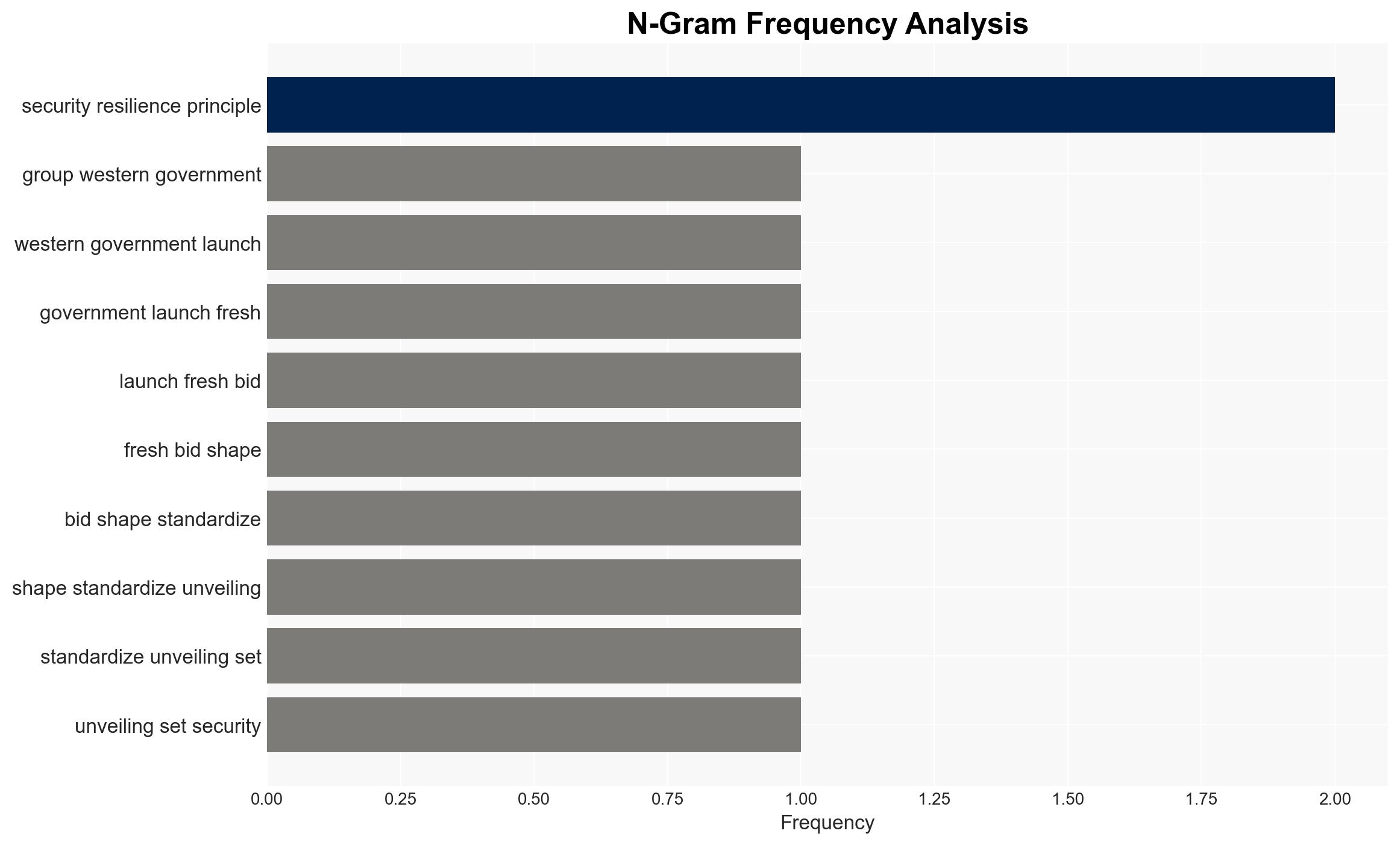
Western governments are proactively attempting to influence 6G development by establishing security and resilience principles, aiming to integrate supply chain controls and cyber safeguards early in the process. This initiative, while non-binding, seeks to preemptively address security concerns associated with 6G’s anticipated technological advancements. The effort is supported by major industry players, indicating a cooperative stance. Overall confidence in this assessment is moderate due to the early stage of 6G development and the lack of binding commitments.
2. Competing Hypotheses
- Hypothesis A: Western governments are genuinely committed to securing 6G networks by influencing standards early to avoid past mistakes with 5G. This is supported by the coalition’s proactive stance and industry support, but contradicted by the lack of enforcement mechanisms.
- Hypothesis B: The initiative is primarily a strategic move to maintain geopolitical influence over 6G standards and limit the role of non-Western vendors. This is supported by the coalition’s composition and historical context but lacks explicit evidence of exclusionary tactics.
- Assessment: Hypothesis A is currently better supported due to the coalition’s focus on security principles and industry alignment. However, indicators such as exclusionary practices or geopolitical tensions could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: 6G will be foundational to future economic and technological landscapes; industry support will translate into compliance; current encryption standards will become obsolete by the 2030s.
- Information Gaps: Specific details on how these principles will influence 6G standards bodies and the timeline for 6G deployment.
- Bias & Deception Risks: Potential bias in reporting due to Western-centric perspectives; risk of strategic deception by industry players to align superficially with principles while pursuing independent agendas.
4. Implications and Strategic Risks
This development could set a precedent for early-stage standardization efforts in future technologies, potentially leading to more secure and resilient networks. However, it may also intensify geopolitical competition over technology leadership.
- Political / Geopolitical: Potential for increased tensions with non-Western countries excluded from the coalition, particularly China.
- Security / Counter-Terrorism: Enhanced security measures could reduce vulnerabilities but may also drive adversaries to develop alternative technologies.
- Cyber / Information Space: Early integration of quantum-resistant cryptography could mitigate future cyber threats but requires ongoing research and adaptation.
- Economic / Social: Successful implementation could bolster economic stability and technological leadership, but failure to achieve consensus could fragment global telecom markets.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor developments in 6G standardization efforts and industry responses; engage with coalition members to clarify enforcement mechanisms.
- Medium-Term Posture (1–12 months): Develop partnerships with industry leaders to ensure alignment with security principles; invest in research on quantum-resistant technologies.
- Scenario Outlook: Best: Broad adoption of principles leads to secure 6G networks. Worst: Geopolitical rifts lead to fragmented standards. Most-Likely: Gradual alignment with principles amid ongoing negotiations.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, telecommunications, 6G, geopolitical strategy, technology standards, quantum cryptography, supply chain security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us